Entry Level Cybersecurity Jobs 2026:
Your Complete Guide to Starting a Cleared Career
Most guides give you the same generic list. This one shows you the fastest path to six figures — through the cleared cybersecurity market.
The 2026 Market — Why Now Is the Time
The cybersecurity talent shortage has become one of the defining economic facts of the tech industry. The Bureau of Labor Statistics projects 33% growth in information security analyst roles through 2034 — roughly 175,000 professionals currently employed in the field, with demand consistently outstripping supply.
But the headline number that matters for your career decision is this: CyberSeek estimates over 500,000 unfilled cybersecurity positions in the United States right now. That gap isn’t closing — it’s widening as AI-powered attacks, cloud migration complexity, and federal spending on cyber defense all accelerate simultaneously.
Three macro forces are driving this demand with no signs of reversal:
- AI-powered threats: Attackers are deploying generative AI for phishing, code generation, and automated vulnerability scanning — defense organizations need analysts who can counter these at scale.
- Cloud migration complexity: Federal agencies moving to hybrid cloud architectures under CMMC 2.0 and FedRAMP need security professionals who understand both legacy and cloud-native environments.
- Regulatory pressure: CMMC 2.0 certification requirements now affect 300,000+ defense contractors, creating massive demand for GRC and compliance professionals at every level.
The practical implication: this is one of the few fields where a motivated person can, in 12–18 months, go from zero cybersecurity experience to a $80–100K+ position with job security that rivals any profession. The cleared market amplifies this — a Secret clearance alone adds $10–20K to your base salary, and the process can begin before you’ve accumulated significant experience.
Browse current cleared cybersecurity jobs to see what employers are hiring for right now.
8 Best Entry-Level Cybersecurity Roles
Not all entry-level cybersecurity jobs are created equal. The roles below represent the best combination of low barrier to entry, high salary ceiling, and strong demand in the cleared market. Each listing shows both national market rates and cleared/government contractor rates — the gap is significant and worth targeting.
Breaking In With No Experience
The question “how do I get into cybersecurity with no experience?” has a concrete, actionable answer. Here’s the exact path that works — structured as a 6–18 month staircase that ends at a cleared position paying $80–100K+.
Step 1: Build Your IT Foundation (Months 1–3)
CompTIA A+ and Network+ are not glamorous, but they are the baseline. Security concepts are 10× easier to grasp when you understand how networks, operating systems, and hardware actually work. A+ proves you can troubleshoot. Network+ proves you understand TCP/IP, routing, and the infrastructure security lives on top of. Together they take 2–3 months to prep and pass.
Step 2: Get Security+ — This Is Non-Negotiable (Months 3–5)
At $404, CompTIA Security+ is the single best investment you can make in your cybersecurity career. It’s DoD 8140 mandatory — meaning every federal agency and cleared defense contractor is legally required to have it for baseline security roles. Two to three months of focused study. Pass this and you’re immediately eligible for dozens of entry-level cleared positions.
Step 3: Build a Home Lab (Months 4–6)
Paper certifications only get you so far. Employers at cleared contractors want to see that you’ve actually done things. Set up VirtualBox with Windows and Linux VMs. Install Splunk Free and ingest some logs. Run Wireshark and analyze real traffic. Try a beginner CTF on HackTheBox or TryHackMe. Document everything in a GitHub repository or write-ups — this becomes your portfolio.
Step 4: Get Real Experience (Months 5–12)
The fastest path is often lateral: get a help desk or IT support role at a company with security operations. You gain professional experience while being in proximity to the security team. Alternatively: participate in CTF competitions, contribute to bug bounty programs, or volunteer for a nonprofit’s IT/security needs. The goal is to have something in the “experience” section that isn’t just “studied at home.”
Step 5: Target Cleared Positions — The Fast Track to $100K+ (Months 6–18)
With Security+ and any demonstrable experience, start applying to cleared positions at defense contractors like Leidos, SAIC, Booz Allen, ManTech, and Peraton. Be explicit in your cover letter that you’re willing to undergo the clearance process. The contractor will sponsor you — they absorb the cost of the investigation in exchange for your commitment. A Secret clearance takes 3–6 months on average and immediately boosts your earning potential by $10–20K per year.
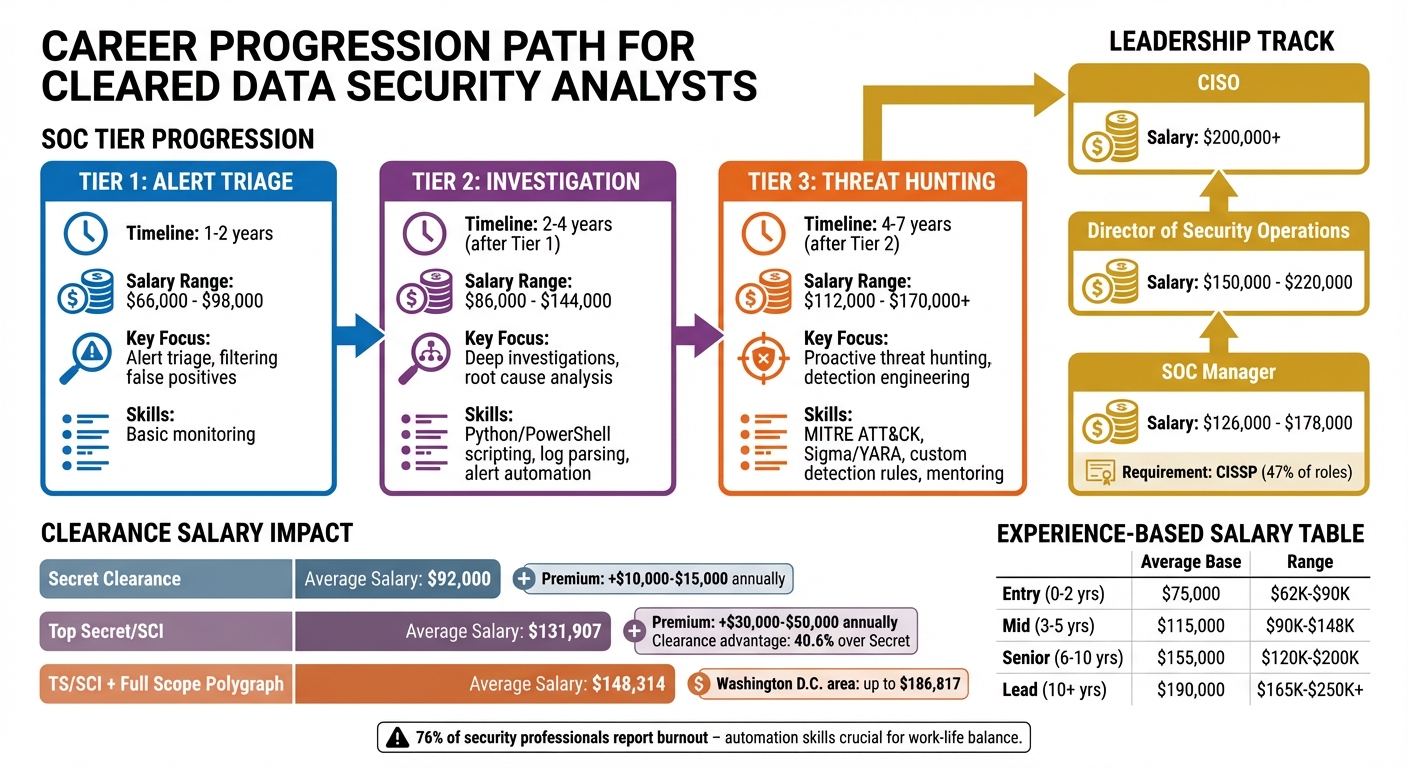
The Cleared Career Advantage
Security clearances are the most underappreciated salary multiplier in the American labor market. Each level of clearance is, essentially, a guaranteed raise — not a one-time bonus, but a structural premium baked into your compensation for every position you hold in the cleared market.
For deeper context on the cleared market, read our analysis of TS/SCI salary premiums, what to expect from the security clearance interview process, and whether upgrading from Secret to Top Secret is worth it at your career stage.
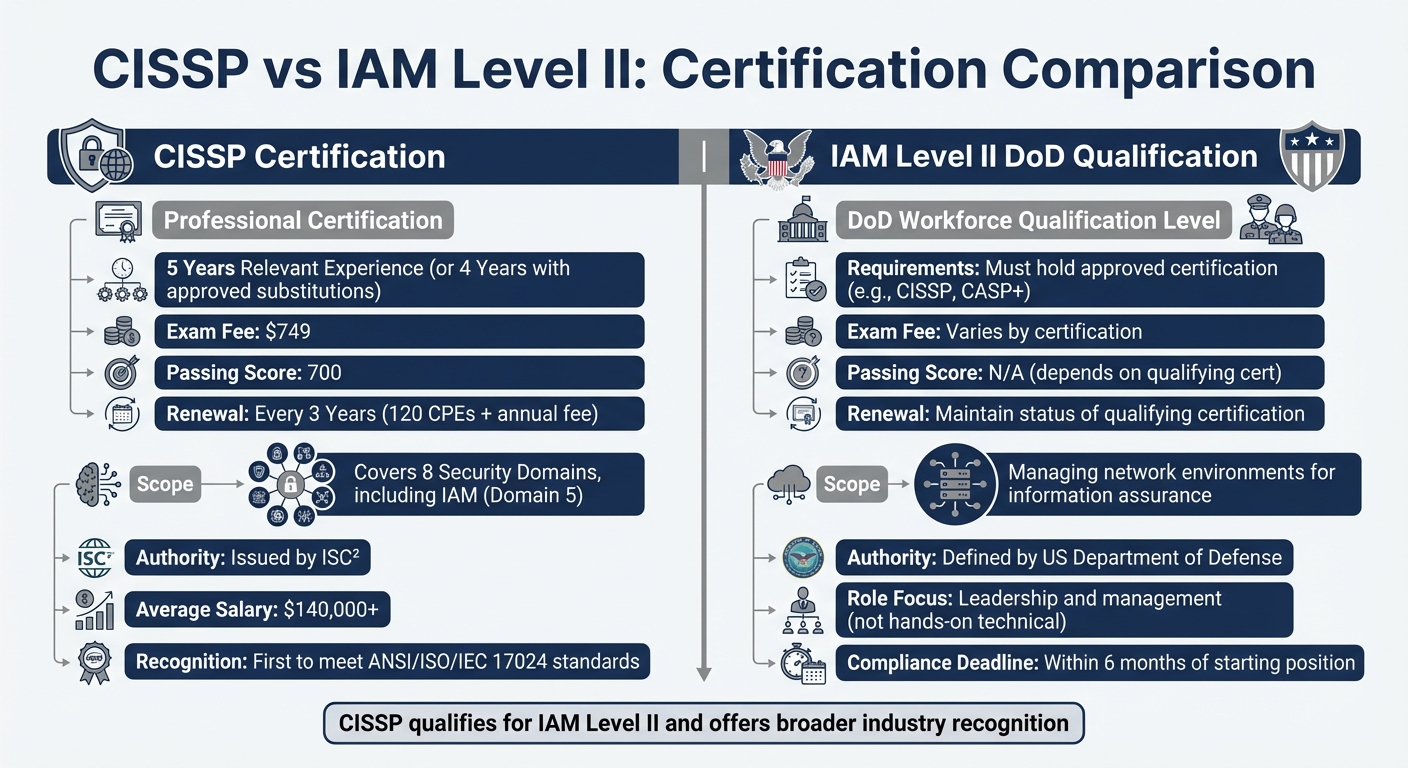
Essential Certifications for Entry-Level Jobs
Certifications in cybersecurity serve two distinct purposes: demonstrating competence to employers, and satisfying DoD 8140 regulatory requirements for government and contractor positions. Understanding the difference helps you prioritize.
| Certification | Cost | Study Time | Salary Impact | DoD 8140 | Best For |
|---|---|---|---|---|---|
| ⭐ Security+ | $404 | 2–3 months | +$10–15K | REQUIRED | Everyone |
| CySA+ | $404 | 3–4 months | +$8–12K | CSSP | Blue Team / SOC |
| PenTest+ | $404 | 2–4 months | +$8–12K | CDA | Red Team |
| CEH | $1,199 | 3–4 months | +$12–18K | CDA | DoD Pen Testing |
| GSEC | $2,499 | 4–5 months | +$15–20K | YES | Premium Entry |
One note on GSEC: the $2,499 price tag is steep for a first cert, but GIAC certifications carry significant weight in the cleared market and employer reimbursement is common once you’re hired. If your employer will pay for it, GSEC over Security+ is a meaningful credential. Read our complete cybersecurity certifications guide for full certification roadmaps by career track.
Entry-Level Cybersecurity Salary Breakdown
The following salary data is based on PayScale 2026 reporting combined with cleared market analysis. The “With TS/SCI” column represents realistic compensation at major defense contractors in top cleared markets — these are not outliers, they’re what the market currently pays.
Salary by Role — National vs. Cleared
| Role | Entry-Level | National Avg | With Secret | With TS/SCI |
|---|---|---|---|---|
| Cyber Security Analyst | $70,828 | $83,525 | $93K–$110K | $105K–$130K |
| Penetration Tester | $72,823 | $102,472 | $100K–$125K | $115K–$150K |
| Security Engineer | $76,332 | $103,573 | $105K–$135K | $120K–$155K |
| Incident Response Analyst | $55,000 | $68,400 | $75K–$95K | $85K–$115K |
| Digital Forensics Analyst | $58,000 | $74,991 | $80K–$100K | $90K–$130K |
| Malware Analyst | $72,000 | $92,880 | $95K–$120K | $110K–$145K |
| SOC Analyst (Tier 1) | $60,000 | $74,000 | $80K–$95K | $95K–$115K |
| GRC Analyst | $62,000 | $77,500 | $82K–$100K | $95K–$125K |
Salary by Location — The Four Cleared Cyber Hubs
Location is one of the most powerful salary levers in the cleared market — arguably more impactful than experience level for the first 3–5 years of your career.
DC Metro
San Antonio, TX
Colorado Springs, CO
Augusta, GA
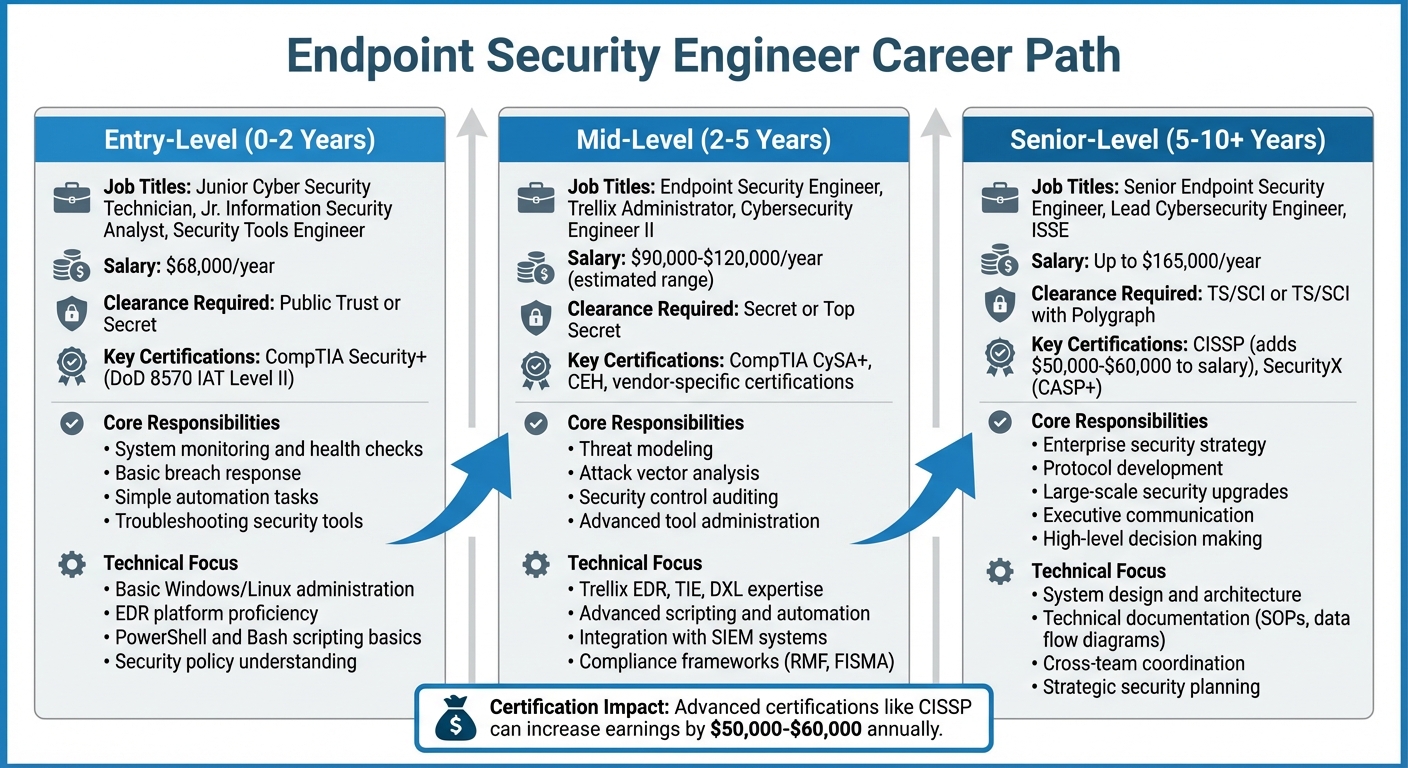
Career Path Progression
Understanding the full arc of a cybersecurity career helps you make smarter early decisions. The choices you make in years 0–2 (which role, which certs, cleared vs. uncleared) compound significantly by years 5–10.
Years 0–2: Foundation Phase ($60K–$85K uncleared / $80K–$115K cleared)
🛡 Blue Team / Defensive
🔴 Red Team / Offensive
Years 2–5: Specialization Phase ($100K–$140K cleared)
The choices you made in the foundation phase start to compound. Blue teamers move into SOC Tier 2/3, incident response lead, or threat hunting roles. Offensive security professionals pursue OSCP, red team operations, and exploit development. GRC analysts become compliance managers and ISSOs supporting classified programs.
Years 5+: Senior Leadership ($150K–$280K)
| Senior Role | Salary Range | Clearance Typical |
|---|---|---|
| Security Architect | $150K–$200K | TS/SCI |
| CISO / Deputy CISO | $180K–$280K | TS/SCI |
| Director, Cyber Operations | $160K–$230K | TS/SCI |
| VP Cybersecurity | $200K–$280K | TS/SCI |
| Principal Security Engineer | $165K–$225K | TS/SCI + Poly |
| Red Team Lead | $150K–$200K | TS/SCI |
For detailed roadmaps by track, see our career path guides: SOC Analyst Career Path · Penetration Tester Career Path · GRC Analyst Career Path
Frequently Asked Questions
Yes — and cybersecurity is one of the more accessible technical fields for career changers, specifically because demand so heavily outstrips supply. The two roles most accessible with no direct experience are SOC Analyst Tier 1 and GRC Analyst. Both primarily require Security+ (a certification you can earn in 2–3 months of study) and demonstrable interest in the field. The key is to treat certifications and a home lab as your substitute for experience. Build a lab, document it, practice with real tools like Splunk and Wireshark, and compete in a few CTFs. Defense contractors — who are constantly under pressure to fill positions — will look at motivated candidates with certifications and demonstrated initiative over experienced candidates who don’t have the drive.
CompTIA Security+ — without qualification. At $404, it’s mandatory for every DoD-cleared position under DoD 8140, recognized by virtually every employer in the field, and covers exactly the breadth of knowledge you need at the entry level: network security, cryptography, identity management, risk management, and threat analysis. After Security+, your next cert depends on your track: CySA+ for blue team/SOC, PenTest+ or eJPT for offensive security, CISA for GRC and compliance.
Entry-level cybersecurity salaries range significantly based on role, location, and whether the position is cleared. For uncleared commercial positions, expect $55,000–$85,000 for most entry-level roles. For cleared entry-level positions, add $10,000–$25,000 to those figures immediately. A SOC Analyst with a Secret clearance at a Northern Virginia contractor is typically looking at $80,000–$95,000 at career entry. With a TS/SCI, the same role jumps to $95,000–$115,000. PayScale 2026 data shows entry-level Cyber Security Analysts earning $70,828 nationally, rising to $105,000–$130,000 with a TS/SCI clearance.
No — but it helps, and it depends on the employer and role. The cybersecurity industry has moved significantly toward certifications as the primary credential signal, partly because the university system produces too few graduates relative to demand and partly because certifications are better proxies for actual job-readiness than a four-year degree. For cleared positions specifically: the federal government and most defense contractors officially accept DoD 8140-qualifying certifications as equivalent to degree requirements for many roles. A Security+ + CySA+ combination can get you into roles that would otherwise require a bachelor’s in computer science. The degree matters more as you progress toward senior and leadership roles.
With focused effort and zero background in tech: 6–12 months to your first position. This assumes you’re dedicating meaningful study time (1–2 hours daily minimum), following the structured path in Section 3, and targeting entry-level roles at cleared contractors specifically. The timeline breaks down roughly as: 2–3 months for foundational certs (A+, Network+), 2–3 months for Security+ prep and exam, 1–2 months building a lab and applying. If you already have an IT background, compress this to 3–6 months. The cleared path adds time after hiring: expect 3–6 months for a Secret clearance to come through. But the job offer comes first — you don’t need the clearance to start, just the willingness to go through the process.
Ready to Launch Your Cybersecurity Career?
Everything you need to go from zero to a six-figure cleared position — career guides, cert roadmaps, and active job listings in one place.
CyberSecJobs.com is the cybersecurity career resource of ClearedJobs.Net, a veteran-owned company serving the security-cleared community since 2001.