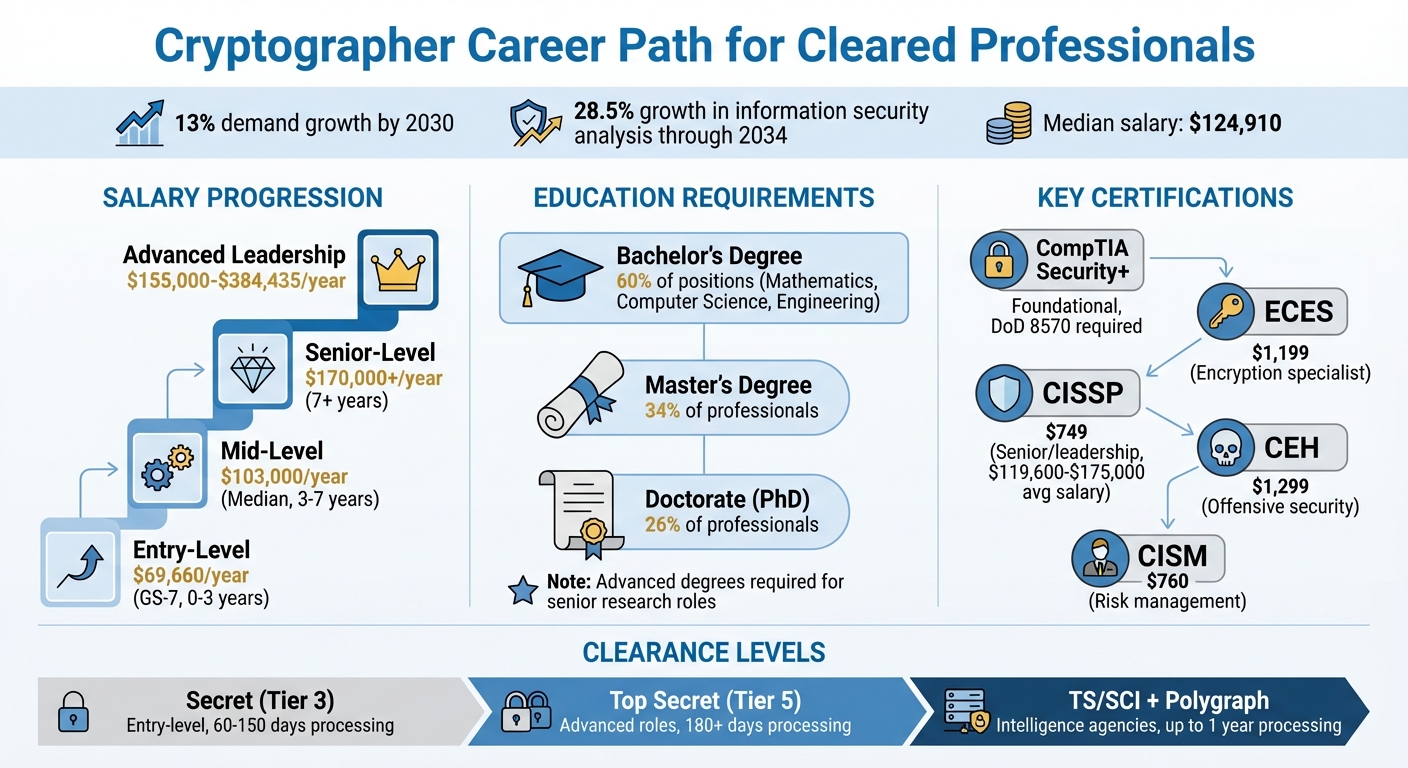
Cryptographers with security clearances are essential for protecting national security data and countering adversaries. They work in agencies like the NSA and DoD, focusing on encryption, cryptanalysis, and secure systems design. Median salary for these roles is $103,000, with demand projected to grow by 13% by 2030. Most professionals hold advanced degrees (34% Master’s, 26% Doctorate) and require U.S. security clearances, which can take up to a year to obtain.
Key Takeaways:
- Skills Needed: Advanced mathematics, programming (C, C++, Python, Rust), and cryptographic protocols.
- Education: Bachelor’s in Mathematics, Computer Science, or Engineering; advanced degrees for senior roles.
- Certifications: ECES, CISSP, CEH, and Security+.
- Career Progression: Entry-level roles start at $69,660; senior positions can exceed $170,000.
- Clearance Levels: Secret (Tier 3) for entry-level; Top Secret/SCI (Tier 5) for advanced roles.
Professionals must navigate security clearance processes, continuous vetting, and specialized training to succeed. Opportunities are concentrated in intelligence agencies, federal contractors, and research labs.
Cryptographer Career Path: Salary Progression and Education Requirements
How to get a Security Clearance With No Experience
What Cleared Cryptographers Do
Cleared cryptographers juggle two key responsibilities: safeguarding classified information and tackling encryption systems used by adversaries. Their work is essential for both securing government communications and gaining critical intelligence.
Protecting Classified Data
One major part of the job is creating encryption systems that shield sensitive information. Cryptographers develop complex algorithms and digital keys, embedding them into both software and hardware to keep data safe during transmission and storage. They also evaluate existing security setups, identifying and fixing vulnerabilities that could be exploited by hackers or foreign entities. This proactive approach ensures that classified data stays out of the wrong hands.
Conducting Cryptanalysis
Cryptanalysts, often the same professionals handling encryption, focus on dismantling the encryption systems of foreign governments or criminal networks. As a National Security Agency spokesperson puts it, "Cryptanalysts at NSA find ways to get around those protections so that the United States has the information it needs for national security" [4]. This process involves spotting mathematical flaws or programming mistakes in encryption methods. It’s a highly creative and analytical task that often requires thinking outside the box. Their findings not only support intelligence efforts but also help strengthen the security of future systems.
Collaborating in Secure Systems Design
Beyond encryption and decryption, cryptographers work with multidisciplinary teams to create secure systems from the ground up. They team up with software developers, IT specialists, and government agencies to build protocols tailored for classified environments. Security Architects play a key role, crafting frameworks and policies that safeguard critical assets. Whether it’s debugging software, designing new cryptanalysis tools, or monitoring data flows, these professionals ensure security measures are deeply integrated into system designs. Collaboration like this not only enhances system security but also provides a pathway for cryptographers to move into strategic leadership roles within their field.
Required Skills and Qualifications
Excelling in cleared cryptography requires a mix of specialized knowledge and practical expertise. With the U.S. Bureau of Labor Statistics forecasting a 31.5% growth in security analyst jobs over the next decade [5], this is an ideal time to develop the skills needed for a career in this field.
Mathematics and Algorithms
Cryptography is deeply rooted in applied mathematics. Key areas like number theory underpin algorithms such as RSA, focusing on concepts like integers, prime numbers, and modular arithmetic. Abstract algebra, especially group theory and finite fields, is critical for mastering Elliptic Curve Cryptography (ECC). Probability and statistics also play a role in assessing system vulnerabilities and the likelihood of key compromise. As The Crypto Recruiters explain:
A flawed implementation of a perfect algorithm is just as insecure as a flawed algorithm. The code is where the theory meets reality, and even a tiny mistake can create a catastrophic vulnerability [5].
Programming Languages
Turning mathematical theory into secure, functional systems requires strong programming skills. Languages like C and C++ are essential for performance-critical applications, low-level hardware security, and building cryptographic libraries. Python is widely used for tasks like rapid prototyping and security analysis, thanks to libraries like PyCryptodome. Meanwhile, Rust is gaining traction in the security field for its memory safety features, and the industry is increasingly embracing memory-safe languages like Rust and Go. Hands-on experience, such as participating in Capture The Flag (CTF) competitions or contributing to open-source projects, can showcase your abilities to potential employers.
Clearance-Specific Knowledge
Working in classified environments demands expertise in security protocols, including end-to-end encryption, Public Key Infrastructure (PKI), and both symmetric and asymmetric cryptography. A deep understanding of computer architecture is also vital for defending against side-channel attacks, where adversaries exploit physical signals like power usage or electromagnetic emissions to access sensitive data. Adopting an adversarial mindset is equally important – anticipating attack strategies helps safeguard national security and meet the rigorous operational demands of classified work.
Education and Certifications
Educational Pathways
To step into a career in cryptography, a bachelor’s degree in Mathematics, Computer Science, or Electrical Engineering is typically required. Mathematics degrees are especially valued because they cover key areas like number theory, abstract algebra, and discrete mathematics – subjects that form the backbone of modern encryption algorithms. On the other hand, Computer Science and Electrical Engineering programs equip students with the programming skills and hardware knowledge essential for implementing cryptographic systems and defending against threats like side-channel attacks.
For those aiming for senior research roles, particularly with organizations like the NSA or NIST, a Master’s or PhD in Cryptography, Theoretical Computer Science, or Applied Mathematics is often necessary. These advanced degrees allow professionals to focus on developing new algorithms, conducting cryptanalysis, or contributing to post-quantum cryptography research. Coursework in Linear Algebra, Number Theory, Probability, and Complexity Theory is crucial for excelling in these roles. Additionally, internships at government agencies such as the NSA, NIST, or national labs can provide valuable experience in classified environments early in one’s career.
Specialized institutions like the National Intelligence University (NIU) and the National Cryptologic School (NCS) offer classified education specifically designed for cleared professionals [9]. The NCS, part of the National Cryptologic University, provides training in cryptology at over 20 university campuses and cryptologic centers [9]. For military personnel and NSA civilians, the Accelerated Degree Program (ADP) offers college credit for NCU coursework and military training through partner institutions [9].
This solid academic groundwork is often complemented by certifications that validate expertise in cryptography and related fields.
Key Certifications for Cleared Cryptographers
Certifications not only validate your skills but are often required for cleared positions under DoD 8570/8140 mandates. One standout option is the EC-Council Certified Encryption Specialist (ECES), which focuses on the practical use of symmetric and asymmetric algorithms, hashing, and PKI. The ECES certification is particularly valuable for those seeking hands-on cryptographic knowledge, with the exam priced at around $1,199 [7].
The CompTIA Security+ certification is a foundational requirement for many cleared roles, offering baseline security knowledge that aligns with DoD 8570 compliance.
For senior or leadership positions, the Certified Information Systems Security Professional (CISSP) is a must. This ANSI-accredited and DoD-approved certification covers cryptography within a broader security framework and is highly regarded for management and architecture roles. The exam costs $749 [1], and CISSP-certified professionals in the U.S. report average salaries between $119,600 and $175,000 [7].
The Certified Ethical Hacker (CEH) certification is geared toward offensive security and penetration testing roles, especially in government sectors. This certification comes with an exam fee of approximately $1,299 [7].
Finally, the Certified Information Security Manager (CISM) takes a risk management approach to cryptography. This certification costs $760, or $575 for ISACA members [1], and is particularly useful for professionals focusing on security governance and risk management.
Security Clearance Requirements
Types of Security Clearances
Cryptographers working with classified information need clearances aligned with the sensitivity of the data they manage. For many entry-level roles in cryptography or network defense, a Secret (Tier 3) clearance is typical. This level covers information that could cause "serious damage" to national security if exposed. Processing times for this clearance generally range from 60 to 150 days [2].
For more advanced positions, such as cryptanalysis or vulnerability research, a Top Secret (Tier 5) clearance is required. This clearance level protects information that, if compromised, could cause "exceptionally grave damage" to national security. Many cryptographers working for intelligence agencies also need access to Sensitive Compartmented Information (SCI). SCI access allows clearance holders to work with specific intelligence sources and methods. When combined with a polygraph examination, processing times for SCI can stretch to 180 days or longer, sometimes exceeding a year [2].
Under the Trusted Workforce 2.0 (TW 2.0) framework, which became operational in 2026, the federal government has adopted a "clear once, trusted everywhere" policy. This approach aims to streamline clearance reciprocity across agencies. Additionally, Continuous Vetting (CV) has replaced the older system of periodic reinvestigations. CV involves ongoing monitoring of criminal records, credit activity, and foreign travel throughout the duration of a clearance [2].
Once the appropriate clearance is identified, the process moves forward with extensive background investigations.
Eligibility and Background Checks
To qualify for a security clearance, applicants must be U.S. citizens and demonstrate unwavering loyalty to the United States. Importantly, individuals cannot apply for a clearance on their own; sponsorship by a federal agency or an authorized cleared contractor is required, typically following a conditional job offer [2] [10]. Applications are submitted through the eApp platform, which has replaced the older e-QIP system. The eApp platform uses logic-based questioning and real-time error detection to streamline the process [2].
The Defense Counterintelligence and Security Agency (DCSA) handles over 95% of federal background investigations [2]. These investigations cover a 10-year span of personal history. For cryptographic positions, adjudicators may also examine your online activity, such as GitHub projects, professional forum contributions, and collaborations with international researchers, to ensure compliance with security standards [2]. Since financial issues are a leading cause of clearance denials, resolving credit problems in advance is critical [2].
"Any falsification on the SF-86, however minor, can be fatal. Be candid." – Kevin James, Cybersecurity Writer [2]
To expedite the process, prepare a detailed 10-year record of your addresses, employment, and education. Be thorough when documenting foreign contacts, including names, nationalities, and the nature of each relationship. If you have any potentially disqualifying factors – like past drug use or financial troubles – disclose them upfront and provide evidence of how you’ve addressed the issues [2].
Understanding these steps is essential for anyone pursuing a career in cleared cryptography.
sbb-itb-bf7aa6b
How to Find Cleared Cryptographer Jobs
Once you’ve met the qualifications and clearance requirements, the next step is landing a role that aligns with your expertise.
Optimizing Your Job Search
Finding the right cryptographer job takes some strategy. Start by building a detailed profile on Cybersecjobs.com and uploading your resume to their database. This allows recruiters from direct-hire employers to find you for sensitive or unlisted positions that aren’t publicly advertised [11].
Make sure your profile and resume highlight your clearance level (e.g., Secret, TS/SCI), technical expertise like Post-Quantum Cryptography (PQC), PKI, RMF, ASIC/FPGA, and DCID 6/4, and certifications such as CompTIA Security+, CISSP, or CEH. Including these keywords can help you rank higher in recruiter searches and align with job filters.
Leverage advanced search tools and set up Boolean alerts to zero in on roles that fit your qualifications. For example, you could use a search string like:
("Cryptography" OR "Cryptanalyst") AND ("TS/SCI" OR "Top Secret") AND ("Remote" OR "Hybrid").
Enable your profile’s searchability so recruiters can find you. If privacy is a concern, consider using an alias until you’ve established contact.
Focus on quality over quantity when applying. Cleared job requirements – like specific clearance levels, polygraph types, and location – are typically non-negotiable. Applying to positions outside your eligibility wastes time. Instead, target major federal contractors known for cryptography work, such as Booz Allen Hamilton, Leidos, Northrop Grumman, MITRE, and ManTech.
Participating in Cleared Job Fairs
While a strong online presence is essential, attending job fairs can give you a competitive edge.
Cleared job fairs provide direct access to hiring managers from top defense contractors and government agencies [11]. These events often feature roles that aren’t publicly advertised due to their sensitivity. Many platforms offer both in-person and virtual hiring events, including those tailored to specific regions. For example, virtual events might connect local professionals with defense and intelligence companies in their area [12].
Prepare by bringing multiple resumes that clearly outline your clearance and skills. Research the participating employers in advance so you can discuss your qualifications confidently. Be ready to talk about your clearance level, polygraph eligibility, and flexibility regarding relocation or working on-site in secure facilities (SCIFs). Keep in mind that most national security cryptography roles require in-person work rather than remote arrangements.
Career Progression for Cleared Cryptographers
A career in cleared cryptography unfolds through a series of well-defined stages. Recognizing these milestones can help you chart a clear path for growth and professional development.
Entry-Level Roles
The journey typically begins with roles like Cryptanalyst, Junior Security Analyst, or Cryptography Engineer I during the first three years. At the NSA, for example, entry-level positions often start at the GS-7 grade level. In these roles, you’ll focus on tasks such as implementing cryptographic protocols, managing encryption keys, and supporting senior team members. According to the Bureau of Labor Statistics, employment in related fields like information security analysis is projected to grow by 28.5% through 2034, making this an opportune time to enter the field [4]. Entry-level salaries start at around $69,660 per year, with the median salary for the profession reaching $124,910 [4].
Early in your career, gaining hands-on experience with cryptographic tools and earning certifications like CISSP or EC-Council Certified Encryption Specialist (CES) can give you a competitive edge. Programs like the NSA’s CADP offer a structured three-year plan that includes rotations across five different offices, technical mentorship, and formal training to accelerate your growth. These foundational years are crucial for building the skills needed to take on more complex responsibilities.
Mid-Level and Senior Roles
As you gain experience, you’ll transition into roles requiring greater independence and strategic thinking. Between three and seven years into your career, you might step into positions like Cryptography Engineer or Security Consultant. These roles involve taking ownership of projects, designing advanced cryptographic solutions, conducting security reviews, and mentoring junior team members. Instead of simply following established protocols, you’ll contribute to creating new ones.
By the seven-year mark and beyond, you’ll be prepared for roles like Senior Cryptographer, Security Architect, or Team Lead. At this stage, your focus shifts from hands-on implementation to strategic planning. You’ll design complex security architectures, establish organizational policies, and guide the technical direction of your team. Compensation for senior roles often approaches $170,000, including bonuses [5]. Specializing in areas like post-quantum cryptography (PQC), blockchain security, or hardware-based cryptographic solutions can further accelerate your career progression.
Advanced Leadership Roles
Advanced roles build on your technical expertise and leadership experience, focusing on shaping the broader security strategy. Positions like Principal Cryptographer, Chief Information Security Officer (CISO), or Distinguished Research Scientist involve high-level decision-making, resource management, and influencing industry practices. In these roles, your responsibilities extend beyond solving cryptographic challenges to setting strategic priorities and ensuring the efficient allocation of resources.
Resources for Career Development
Advancing as a cleared cryptographer means staying committed to learning and building connections in the field. Below are some key resources to help you grow your skills and expand your professional network.
Training Programs and Certifications
The National Cryptologic School (NCS) offers advanced cryptology training tailored for cleared professionals looking to deepen their expertise [9]. For those with a solid foundation, the Advanced Crypto Course (ACC) from the Department of Defense provides further specialized training [8]. Additionally, the National Intelligence University (NIU) offers classified bachelor’s and master’s degree programs, allowing you to earn credentials while working directly with sensitive material [9].
If you’re an NSA civilian employee, you can take advantage of the After-hours college program, which supports job-related courses at accredited universities [9]. For employees with at least a year of experience, the Advanced Studies Program provides the opportunity to attend college for up to four semesters with full salary and tuition covered [9]. The NSA also collaborates with institutions like the Naval Postgraduate School and National Defense University, offering tuition-free degrees in intelligence-related fields [9]. For hands-on experience, the NSA Codebreaker Challenge delivers cryptographic problem-solving exercises paired with study resources [16].
While formal education is vital, connecting with professional networks can further enhance your career.
Professional Organizations
Joining professional organizations can open doors to networking and additional learning. ISC2 (International Information System Security Certification Consortium) provides courses on cutting-edge topics like Quantum Computing, Zero Trust Strategy, and AI Security. Local chapters often host networking events, and members gain access to free Express Courses covering topics like data protection and application security [13].
The National Cryptologic Foundation (NCF) organizes events that bring together industry leaders and government experts. For instance, on March 17, 2026, the NCF hosted a session titled "Convening to Act: Accelerating U.S. Post-Quantum Cryptography Adoption: From Standards to Deployment", focusing on strategies for implementing Quantum-Resistant Cryptography [14]. Meanwhile, the International Institute of Cryptology (i2OC) offers certifications, publishes research, and provides a global network for professionals dedicated to securing digital communications [15].
Cybersecjobs.com Career Resources
For cleared professionals navigating the cryptography job market, Cybersecjobs.com offers tailored tools to simplify your search. The platform allows you to use job search filters specific to security clearance levels, helping you quickly find roles requiring Top Secret, TS/SCI, or Polygraph clearances. You can also upload your resume, set up job alerts for cryptographer positions, and access career resources designed for the cleared community.
Additionally, Cybersecjobs.com hosts job fairs, connecting you directly with employers who need cleared cryptographers. This direct connection streamlines the hiring process and eliminates unnecessary steps. For more government-focused tools, the NSA’s Job Exploration Tool (JET) can help match your skills and education to positions within the Intelligence Community [17].
Conclusion
A career as a cleared cryptographer requires a strong foundation in mathematics and programming. Proficiency in languages like Python, C, C++, and Rust is especially important for developing secure systems [3][6]. Jobs in related fields are expected to grow steadily, with average salaries around $121,000. Senior-level roles can bring in $155,000 to $165,000 annually, showcasing the profession’s financial rewards and stability [6][19].
While about 60% of cybersecurity job postings from May 2024 to April 2025 are expected to require a four-year degree, advancing to high-level cryptography roles often calls for a master’s or PhD [6]. Certifications such as CISSP or ECES further validate expertise and can pave the way to leadership positions. In some cases, senior cryptography roles may offer salaries as high as $384,435 [20]. As William Emmanuel Yu points out:
Most of the time, certifications are geared towards using cryptography instead of building and proving them. For the latter, I suggest you get a graduate degree [21].
Beyond certifications, obtaining security clearances is crucial for roles within agencies like the NSA, CIA, and FBI. These clearances not only expand career opportunities but also significantly impact earning potential [18][19]. With the field rapidly evolving to address challenges like post-quantum cryptography and quantum computing, staying ahead through continuous learning and skill development is non-negotiable.
FAQs
How do I get sponsored for a security clearance?
To be sponsored for a security clearance, the first step is landing a job with an employer that requires access to classified information and is authorized to sponsor you. Without sponsorship, it’s impossible to obtain a clearance independently.
Once hired, your employer will handle the necessary paperwork, such as submitting the SF-86 form, and will initiate the background investigation. This thorough process examines your personal, financial, and professional history and can take several months to complete.
Can I become a cryptographer without a master’s or PhD?
Yes, a bachelor’s degree is usually enough to start a career as a cryptographer. That said, many senior or specialized positions in the field tend to favor candidates with advanced degrees like a master’s or PhD.
What can I do now to speed up the clearance process?
To move through the security clearance process more quickly, make sure all your background information is thorough and accurate – even small mistakes can lead to delays. Practice responsible behavior, keep your finances in good order, and steer clear of situations that might cause concern. Staying organized is key: submit any requested documents promptly and keep an eye on updates, such as the Trusted Workforce 2.0 initiative, to help you handle the process more smoothly.
