Malware analysts with security clearances are in high demand, playing a critical role in national security by dissecting malicious software to understand its intent and mechanics. This guide outlines the skills, tools, certifications, and career strategies needed to excel in this field.
Key Takeaways:
- Skills Required: Expertise in C/C++, Assembly, and Python, alongside knowledge of Windows, Linux, Android, and iOS platforms.
- Core Methods: Static analysis (examining file properties) and dynamic analysis (running malware in controlled environments).
- Top Tools: Ghidra, IDA Pro, Binary Ninja, Wireshark, x64dbg, and Process Monitor.
- Certifications: GREM (most relevant), CEH, CySA+, GCFA, and OSCP, depending on your career stage.
- Job Market: Cleared malware analysts earn $145k–$215k annually, with a 35% job growth expected by 2030.
- Career Path: Transitioning from reverse engineering to senior roles involves mastering malware attribution, memory forensics, and automation.
With demand for cleared malware analysts surging, this guide equips you with actionable steps to advance your career in this specialized, high-paying field.
Required Skills for Cleared Malware Analysts
Technical Skills
To excel as a cleared malware analyst, proficiency in low-level programming is a must. This includes expertise in C/C++ and Assembly (for both x86 and x64 architectures). These skills allow analysts to dissect malware at its core. Additionally, Python scripting plays a key role in automating repetitive tasks and creating custom tools for analysis.
While understanding Windows internals remains critical – given that Windows is still the primary target for most malware – analysts must now broaden their expertise. Increasingly, threats are targeting Linux, Android, and iOS platforms. Mobile threats, in particular, have led to a demand for specialists familiar with Android device tampering and anti-removal techniques. This shift reflects the growing need for cross-platform and mobile threat expertise, as highlighted in many job postings today [1].
Malware Analysis Methods
Analyzing malware effectively requires mastering two core methods: static analysis and dynamic analysis.
- Static analysis involves examining a file’s properties – such as headers, embedded strings, and metadata – without running the code. Tools like PEiD and BinText are commonly used to gather initial insights.
- Dynamic analysis, on the other hand, focuses on executing malware in a controlled environment, such as a sandbox like Cuckoo or Any.Run. This method helps analysts observe real-time behaviors, including registry changes and network activity.
However, modern malware often incorporates techniques like debugger detection and obfuscation to avoid scrutiny. Analysts must counter these anti-analysis measures and rely on resources like the MITRE ATT&CK framework to map observed behaviors to known adversary tactics, techniques, and procedures (TTPs). This approach not only enhances threat intelligence but also aids in attribution.
Analytical and Problem-Solving Abilities
Reverse engineering is at the heart of malware analysis, offering a unique perspective on cyber threats. As J.W. McKiddy, a GREM-certified expert, puts it:
"Where incident response often looks outward at effects and outcomes, malware reverse engineering looks inward at intent and mechanics" [5].
This inward focus sharpens critical thinking, helping analysts uncover not just what happened, but also how and why an attack occurred. Whether performing static or dynamic analysis, this mindset is essential for uncovering hidden threats.
Attention to detail is non-negotiable in this field. Even a single byte can drastically change a malware sample’s behavior [1]. Analysts must de-obfuscate complex code, extract Indicators of Compromise (IOCs), and connect technical findings to broader threat intelligence. This capability allows organizations to move beyond reactive, signature-based defenses to proactive strategies built on a deep understanding of adversary methods [4].
With ransomware incidents spiking by 46% in September 2025 and the average data breach costing $4.4 million, these analytical skills are more than just technical requirements – they directly influence an organization’s ability to defend itself against evolving threats [1].
Tools for Reverse Engineering Malware
Reverse Engineering Software
Ghidra, a free and open-source tool, has become a go-to choice for malware analysis since its release in 2019. Marco Figueroa, Principal Threat Researcher at SentinelOne, highlights its rise:
"IDA Pro long set the industry standard until Ghidra’s emergence in 2019. Since then Ghidra’s popularity has grown exponentially due to it being a free open-source tool that was developed and is still maintained by the NSA" [12].
Ghidra’s ability to transform raw assembly into C-like pseudocode makes it easier to understand complex binaries. It also supports collaborative binary analysis, which is invaluable for teams working on threat intelligence [7].
IDA Pro continues to be the gold standard for professional reverse engineering. Its Hex-Rays decompiler and vast plugin ecosystem make it incredibly powerful, though its high licensing fees can be a barrier [11]. For those looking for a middle ground, Binary Ninja offers a sleek interface, strong performance, and automation-friendly APIs, making it an appealing option between free tools and IDA Pro [9].
For dynamic analysis, x64dbg has taken over from OllyDbg as the preferred debugger. It provides a straightforward interface for stepping through code and tracking memory changes in real time [6]. By running malware in a sandboxed environment, x64dbg can bypass packers and observe runtime behavior. Neil Fox, an Incident Response Specialist, explains:
"A disassembly tool such as Ghidra doesn’t run the code, it maps out the assembly code of the malware and enables code navigation without affecting the analysis environment" [6].
Network and System Monitoring Software
While reverse engineering tools focus on dissecting malware binaries, network and system monitoring software reveals how malware operates in real-world scenarios.
Wireshark is the go-to tool for analyzing network traffic. It helps detect C2 (Command and Control) communication, data exfiltration, and payload downloads [8]. For a safer environment, analysts often use FakeNet-NG or INetSim to mimic internet services in a controlled lab, tricking malware into exposing its network behavior without risking actual connectivity.
On the system side, Process Monitor (ProcMon) from Microsoft Sysinternals is indispensable. It provides real-time tracking of file system, registry, and process activity, helping analysts identify the traces malware leaves behind [8]. For quick triage, PEStudio is another essential tool. It flags suspicious imports, strings, and indicators of compromise, offering valuable insights before executing the malware.
How to Learn Malware Analysis & Reverse Engineering | Complete Roadmap
Certifications for Cleared Malware Analysts
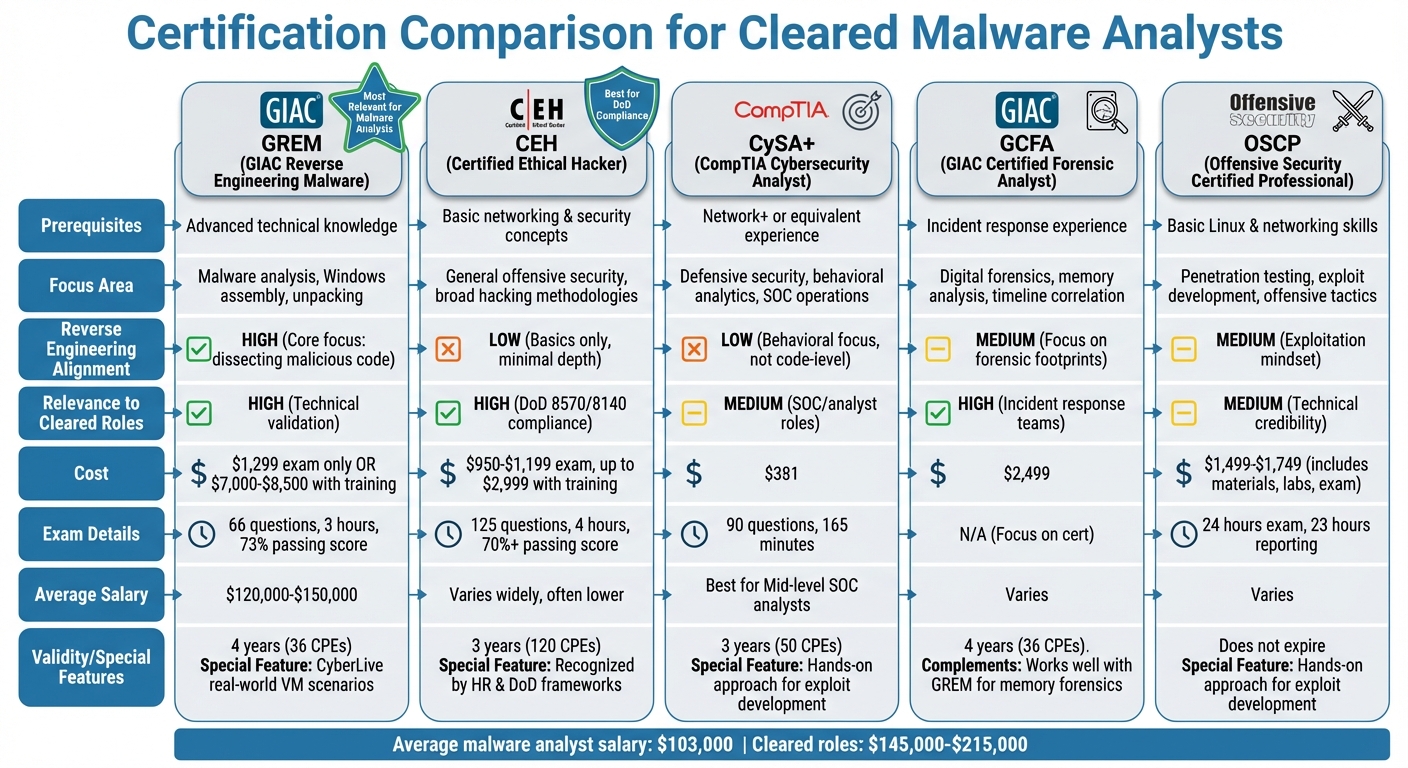
Malware Analyst Certification Comparison Guide: GREM, CEH, CySA+, GCFA, and OSCP
Recommended Certifications
If you’re aiming to excel as a cleared malware analyst, certifications can play a big role in showcasing your expertise. Here are some of the most respected options:
GIAC Reverse Engineering Malware (GREM) is often seen as the top certification for malware analysts. It proves you can break down malicious code, bypass anti-analysis techniques, and understand how malware works on Windows and web platforms [3]. The exam consists of 66 questions, lasts three hours, and requires a passing score of 73% [3]. A standout feature is the "CyberLive" component, where you’re tasked with solving real-world problems in a virtual machine environment [3]. The cost? Around $1,299 for the exam alone, or $7,000–$8,500 if bundled with SANS training (FOR610) [3]. GREM-certified professionals often earn between $120,000 and $150,000 annually [10].
Certified Ethical Hacker (CEH) is another popular choice, especially for meeting DoD 8570/8140 requirements [10]. As Programs.com highlights:
"CEH is recognized by HR departments, DoD 8570/8140 frameworks, and Fortune 500 employers. It gets résumés past filters" [10].
The exam costs between $950 and $1,199, with training packages reaching up to $2,999. While CEH is not specifically focused on reverse engineering, it’s a good credential for meeting cleared job requirements [10].
CompTIA CySA+ is a mid-level certification that focuses on defensive security and incident response. Priced at $381, it’s ideal for SOC analysts who want to demonstrate skills in behavioral analysis without diving into deep code-level analysis.
GIAC Certified Forensic Analyst (GCFA) complements GREM by focusing on memory forensics and timeline reconstruction. This certification, priced at about $2,499, helps analysts track the traces malware leaves behind.
Offensive Security Certified Professional (OSCP), while not malware-specific, is highly respected for proving problem-solving abilities and an exploitation mindset. The cost ranges from $1,499 to $1,749, including course materials, labs, and the exam. OSCP’s hands-on approach is great for sharpening skills in exploit development [4].
For GIAC certifications, keep in mind they’re valid for four years. Renewing them requires 36 Continuing Professional Education (CPE) credits [4].
Certification Comparison
Here’s a quick breakdown of how these certifications stack up:
| Certification | Prerequisites | Focus Area | Reverse Engineering Alignment | Relevance to Cleared Roles |
|---|---|---|---|---|
| GREM | Advanced technical knowledge | Malware analysis, Windows assembly, unpacking | High (core focus on dissecting malicious code) | High (technical validation) |
| CEH | Basic networking and security concepts | General offensive security, broad hacking methodologies | Low (basics only, minimal reverse engineering depth) | High (DoD 8570 compliance) |
| CySA+ | Network+ or equivalent experience | Defensive security, behavioral analytics, SOC operations | Low (behavioral focus, not at the code level) | Medium (SOC/analyst roles) |
| GCFA | Incident response experience | Digital forensics, memory analysis, timeline correlation | Medium (focus on forensic footprints) | High (incident response teams) |
| OSCP | Basic Linux and networking skills | Penetration testing, exploit development, offensive tactics | Medium (exploitation mindset) | Medium (technical credibility) |
Building Your Certification Path
Your choice of certifications should match your career stage and goals. Many professionals start with foundational credentials like Security+ or CEH for entry-level cleared roles. From there, OSCP is a great way to deepen your technical skills, while GREM offers a specialized focus on malware analysis.
If you’re planning to take a GIAC exam, remember they’re open-book. A well-organized, alphabetized index of course materials can be a lifesaver during the test. Beyond certifications, setting up a malware lab is a great way to boost your practical skills. Tools like REMnux, Ghidra, and x64dbg let you analyze real-world malware samples in a controlled environment.
With the right certifications and hands-on experience, you’ll be well-prepared to tackle specialized roles in malware analysis.
sbb-itb-bf7aa6b
Finding Cleared Malware Analyst Jobs
Using Cleared Cyber Security Jobs
Cleared Cyber Security Jobs offers a range of tools specifically designed for professionals with security clearances. Their IntelliSearch™ system matches your uploaded resume with job opportunities based on your clearance level, technical skills, and preferred locations. You can refine your search using filters for clearance types (Secret, TS, TS/SCI), polygraph requirements (CI, Full Scope), and regions where cleared roles are concentrated. Additionally, personalized email alerts ensure you stay updated on new openings. Since employers often use titles like "Malware Analyst" and "Reverse Engineer" interchangeably in job postings [1], searching for both terms can broaden your options.
The platform is exclusively for U.S. citizens with active security clearances, creating a competitive environment among equally qualified candidates. With a direct-hire model, you’ll connect directly with hiring managers at government contractors, defense agencies, and cybersecurity firms. These features make it easier to find specialized roles and advance your career as a cleared malware analyst.
Salary Ranges and Market Trends
The demand for cleared malware analysts is reflected in both job availability and competitive salaries. These roles typically pay significantly more than non-cleared positions. While the average malware analyst earns around $103,000 annually, cleared roles command salaries ranging from $145,000 to $215,000. Entry-level positions start at approximately $73,000, with substantial increases after seven years of experience. In cities like San Jose and San Francisco, salaries exceed the national average by 26.1% and 24.8%, respectively.
The cybersecurity field is expected to grow by 35% through 2030, driven by increasing cyber threats and expanding attack surfaces. To stand out, emphasize your expertise in automating malware triage using Python scripts, a highly sought-after skill in job listings. Industries like manufacturing, professional services, and public administration are particularly active in hiring for these roles [1]. These trends highlight the importance of staying ahead in a growing and competitive job market.
Job Seeker and Employer Plans
Cleared Cyber Security Jobs offers tailored plans to meet the needs of both job seekers and employers.
| Feature | Job Seeker Plan | Employer Plan |
|---|---|---|
| Cost | Free | Custom Pricing |
| Job Search | Advanced filters (Clearance, Polygraph, Location) | Access to the cleared candidate database |
| Alerts | Personalized email alerts (Daily/Weekly) | New candidate notifications |
| Profile | Resume upload and IntelliSearch™ matching | Job posting and branding tools |
| Visibility | Control over which employers see your profile | Direct messaging to cleared professionals |
The job seeker plan provides free access to advanced search tools, resume uploads, and personalized alerts, making it easier to find roles that match your skills and preferences. On the employer side, government contractors, defense agencies, and other organizations benefit from flexible pricing packages, access to a specialized candidate database, and direct communication tools. Both plans include features like advanced filters and direct messaging, ensuring a streamlined experience for connecting top talent with the right opportunities.
Moving from Reverse Engineer to Senior Malware Analyst
Gaining Experience
The path to becoming a senior malware analyst depends heavily on your educational background. For instance, individuals with a bachelor’s degree typically need over 12 years of experience, while those holding a PhD may require around 8 years. On the other hand, an associate’s degree often necessitates 14+ years, and a high school diploma or GED could mean around 16 years of hands-on experience [1].
To step into a senior role, you’ll need to master several advanced skills. These include malware attribution, automating triage processes using Python, conducting memory forensics with tools like Volatility or Rekall, and performing in-depth network analysis with Wireshark. Platforms such as MISP, VirusTotal, and YARA are key for fine-tuning your attribution techniques, while expertise in countering sophisticated malware tactics like polymorphism and anti-debugging is crucial. Additionally, documenting your findings on platforms like GitHub can demonstrate your technical depth and organizational skills [1]. For professionals with security clearances, these technical capabilities play a direct role in supporting national security missions.
If you’re looking to speed up your career progression, structured training programs can help you bridge the gap between technical expertise and leadership skills.
Career Development Resources
For cleared professionals aiming to advance into high-level roles such as TS/SCI positions, specialized training programs and resources can be game-changers. Cleared Cyber Security Jobs offers tailored career guidance to help you stay ahead of evolving skill demands and market trends.
Structured training programs are an excellent way to fast-track your growth. For example, InfosecTrain provides 32-hour live instructor-led sessions with added career guidance, mentorship, and access to peer-to-peer learning communities via Telegram [13]. Another standout option is Kaspersky’s Targeted Malware Reverse Engineering course, which includes 100 hours of virtual lab time and instruction from their Global Research and Analysis Team (GReAT). This program dives deep into real-world APT cases like Lazarus and LuckyMouse [14]. Plus, these courses often offer CPE credits through partnerships with ISACA and ISC2, allowing you to maintain professional certifications while sharpening your skills [15].
These resources not only enhance your technical abilities but also position you for leadership roles in the malware analysis field.
Conclusion
Breaking into the field of cleared malware analysis requires a solid grasp of x86/x64 assembly, expertise in tools like IDA Pro and Ghidra, and a firm understanding of static and dynamic analysis techniques. On top of that, earning technical certifications and building a personal lab setup – using tools like REMnux and isolated Windows environments – can help you practice with real-world malware samples and sharpen your skills [1][10].
Certifications play a big role in career advancement. For example, GREM-certified professionals report an average salary of about $124,000, significantly higher than the industry average of $103,000. This highlights the importance of credentials like GREM for those aiming to move into senior positions [1][2]. While the CEH certification is useful for clearing HR filters at the entry level, employers seeking advanced threat analysis skills look for certifications that demonstrate deeper expertise, like GREM [10].
The demand for cleared malware analysts is growing rapidly, fueled by the rise in malware threats and the need for advanced analysis. Employers are increasingly looking for professionals who can shift from reactive "what happened" investigations to proactive "how and why" research [1][4][5]. When searching for roles, keep an eye out for job titles like "Malware Analyst" and "Reverse Engineer", as these often overlap in both responsibilities and salary potential [1].
Platforms like Cleared Cyber Security Jobs make the job search easier by offering tools like resume uploads, job alerts, and direct connections to employers who value your security clearance and technical background. To stand out, consider showcasing your work on GitHub and pursuing targeted training to prepare for leadership roles [1][10]. These steps can help position you as a sought-after expert in national security and malware analysis.
FAQs
What clearance do I need to become a malware analyst?
To land a role as a malware analyst in the cleared cybersecurity sector, you’ll usually need a TS/SCI clearance. This high-level clearance is essential for positions that deal with sensitive or classified data.
How do I build a safe malware analysis lab at home?
To set up a secure malware analysis lab at home, start by using virtual machines (VMs) to keep your main system safe. VMs provide the isolation needed to analyze malware without risking your host computer. Make sure to configure network containment to prevent malware from spreading beyond the lab. Taking snapshots of your VMs is also essential – it allows you to quickly reset your environment if something goes wrong.
Store malware samples in password-protected archives to prevent accidental execution or unauthorized access. Equip your lab with powerful analysis tools like IDA Pro or Ghidra to dissect and understand malware behavior.
Security should always be your top priority. Keep networks isolated, handle all samples with care, and never execute malware directly on your host system. These precautions help reduce risks and ensure your analysis setup remains safe and effective.
Which certification should I get first for cleared malware roles?
The GREM certification is a strong foundation for those pursuing cleared roles in malware analysis. It confirms essential skills in analyzing and reverse-engineering malware, earning widespread respect in the cybersecurity community. Tailored for professionals in this niche, it’s an excellent step for anyone aiming to grow their career in the cleared cybersecurity field.
