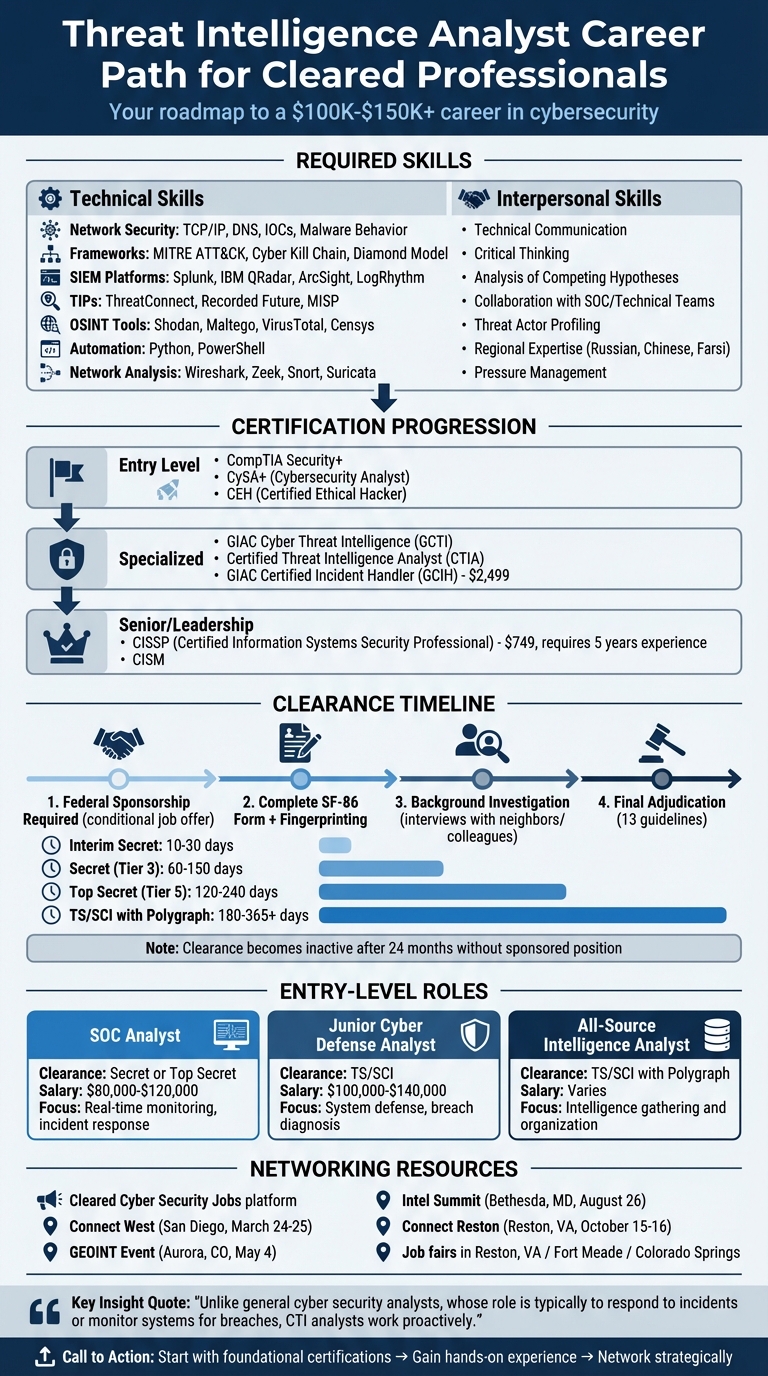
Threat Intelligence Analysts are critical in identifying and stopping cyber threats before they become attacks. For professionals with security clearances (Secret, TS/SCI, or Polygraph), this role offers access to classified data, high-impact responsibilities, and salaries ranging from $100,000 to $130,000 or more. Here’s what you need to know:
- Skills Required: Analysts need technical expertise in tools like Splunk, MITRE ATT&CK, and Python, alongside strong communication and critical thinking abilities.
- Certifications: Start with Security+ or CySA+ and advance to GCTI, CEH, or CISSP for senior positions.
- Clearance Process: A federal sponsor is required, and the process includes background checks and continuous monitoring.
- Entry-Level Roles: Positions like SOC Analyst or Junior Cyber Defense Analyst offer starting points, often requiring a Secret or Top Secret clearance.
- Networking: Platforms like Cleared Cyber Security Jobs and job fairs in areas like Reston, VA, connect professionals with top employers.
With growing demand for cleared cybersecurity experts, this career path combines technical skills, certifications, and networking for long-term success.
Threat Intelligence Analyst Career Path: Skills, Certifications, and Clearance Timeline
How to Become a CTI Analyst: Zero to Hero (The Ultimate Beginner’s Guide)
sbb-itb-bf7aa6b
Required Skills for Cleared Threat Intelligence Analysts
Cleared Threat Intelligence Analysts need a mix of technical expertise and strong interpersonal abilities. On the technical side, you’ll need to master tools and frameworks for detecting and analyzing threats. On the interpersonal side, it’s all about breaking down complex findings into clear, actionable insights for decision-makers at every level. Let’s dive into the key technical tools and soft skills that help analysts thrive in cleared environments.
Technical Skills: Tools and Platforms
Start with the basics of network security – understanding TCP/IP, DNS, indicators of compromise (IOCs), and malware behavior is non-negotiable. Familiarize yourself with intelligence frameworks like MITRE ATT&CK, the Cyber Kill Chain, and the Diamond Model to map out how adversaries operate.
Proficiency with SIEM platforms such as Splunk, IBM QRadar, ArcSight, or LogRhythm is critical for analyzing logs and spotting patterns. You’ll also need to work with Threat Intelligence Platforms (TIPs) like ThreatConnect, Recorded Future, or MISP, as well as OSINT tools like Shodan, Maltego, VirusTotal, and Censys for reconnaissance and research. For malware analysis, tools like Cuckoo, Any.Run, and Hybrid Analysis are invaluable.
To streamline workflows, learn automation tools like Python or PowerShell for parsing and analyzing data. Tools like Wireshark, Zeek, Snort, and Suricata are essential for network analysis. If you’re just starting out, free and open-source platforms like Gephi, MISP, or OpenCTI can help you build foundational skills without hefty costs.
Interpersonal and Analytical Skills
Even the best technical skills fall flat if you can’t communicate your findings effectively. A cleared analyst’s job often involves translating complex technical data into concise, actionable reports. Whether you’re briefing SOC teams on tactical indicators or presenting executives with high-level risk assessments, clarity is key.
Strong critical thinking is another must-have. Analysts need to evaluate intelligence sources to avoid false positives and biases. This requires an investigative mindset – profiling threat actors, understanding their motivations, and piecing together incomplete or conflicting data. Techniques like Analysis of Competing Hypotheses can help you stay objective when assessing threats.
Collaboration is at the heart of success in cleared environments. You’ll work closely with technical, operational, and strategic teams, coordinate with outside agencies, and engage in threat-sharing communities like FIRST or ISACs. You also need to stay calm under pressure, especially when handling time-sensitive threats. Bonus points if you develop regional expertise and language skills (e.g., Russian, Chinese, Farsi) – these can make you an even more valuable asset in sensitive environments.
Education, Certifications, and Clearance Requirements
Most roles for Threat Intelligence Analysts call for a bachelor’s degree in fields like Computer Science, Cybersecurity, Information Technology, or similar technical areas. Key coursework often includes network security, cryptography, ethical hacking, and digital forensics. For senior or leadership positions, employers may lean toward candidates with a master’s degree in areas such as Cybersecurity Engineering, Intelligence Studies, or Information Assurance. Interestingly, non-technical backgrounds, like Criminology, Law Enforcement, or Digital Forensics, are also appreciated. In certain cleared environments, extensive experience – over eight years – can sometimes substitute for a formal degree.
If your undergraduate degree isn’t in a technical field, pursuing an online master’s in Information Assurance or Cybersecurity can help bridge the knowledge gap. You can also enhance your skills by joining Capture The Flag (CTF) competitions or engaging in hands-on labs, which showcase your abilities in investigative work and malware analysis. Developing expertise in a specific geographic region can also make you stand out, especially when analyzing regional threat actor activities.
A strong educational foundation is just the start – certifications are the next step to solidify your credentials.
Certifications That Advance Your Career
Certifications are a great way to prove your expertise and stand out in the competitive job market, especially for cleared positions. Entry-level options like CompTIA Security+ and CySA+ (Cybersecurity Analyst) focus on threat detection and data analysis. The Certified Ethical Hacker (CEH) is another popular choice, teaching you to think like an attacker to identify vulnerabilities proactively. For more specialized roles, certifications such as GIAC Cyber Threat Intelligence (GCTI) and Certified Threat Intelligence Analyst (CTIA) are specifically tailored to this field, emphasizing skills like attribution and the intelligence cycle.
If you’re aiming for senior or management roles, the CISSP (Certified Information Systems Security Professional) is widely regarded as the gold standard. It requires five years of professional experience and costs $749 [2]. For those involved in incident investigations, the GIAC Certified Incident Handler (GCIH), priced at $2,499, is highly relevant [2]. A typical progression might look like this: start with foundational credentials like Security+, move to CySA+ for analytical skills, and then pursue specialized certifications like GCTI or CEH. If your focus is technical analysis, CySA+ or GCTI is ideal. For leadership paths, CISSP or CISM certifications are highly recommended [2].
Once you’ve tackled education and certifications, the next hurdle is obtaining and maintaining a security clearance.
Getting and Keeping Your Security Clearance
You can’t apply for a security clearance independently – it requires sponsorship from a federal agency or an authorized defense contractor after receiving a conditional job offer. By 2026, the Trusted Workforce 2.0 (TW 2.0) framework will be the standard, featuring the "eApp" digital platform and emphasizing reciprocity across agencies under the "clear once, trusted everywhere" principle. The clearance process involves completing the SF-86 form, fingerprinting for initial criminal checks (which may lead to an Interim clearance), a comprehensive background investigation – including interviews with neighbors and colleagues – and final adjudication based on 13 established guidelines.
"Falsification on the SF-86, even on a minor point, is often the most easily preventable yet fatal mistake. Candor is paramount." – Kevin James, Cybersecurity Writer, Cybersecurity For Me [3]
Before you receive the eApp link, it’s wise to prepare. Gather a detailed 10-year history of your residences, employment, education, and foreign contacts to ensure accuracy. Pull your credit reports early to address any delinquencies, as financial issues are the top reason for clearance denials or revocations. A documented repayment plan can help mitigate these concerns. Additionally, review your social media for any sensitive content – adjudicators now examine professional online activity, including GitHub contributions, gaming communities, and posts on forums.
Periodic reinvestigations have been replaced by Continuous Vetting (CV), an automated system that monitors criminal arrests, credit anomalies, and foreign travel in real time. To maintain your clearance under CV, promptly self-report major life events – such as arrests, significant debt, or foreign contacts – to your Facility Security Officer (FSO). Keep in mind that a security clearance typically becomes inactive 24 months after leaving a sponsored position. Processing times vary widely: Interim Secret clearances take 10 to 30 days, Secret (Tier 3) clearances take 60 to 150 days, Top Secret (Tier 5) clearances range from 120 to 240 days, and TS/SCI with Polygraph clearances can take 180 to 365+ days [3].
Building Experience in Cleared Cybersecurity
Once you’ve secured a solid education and relevant certifications, the next step is gaining hands-on experience. Working with security tools, analyzing incidents, and understanding adversary tactics are critical skills to develop. Entry-level roles are an excellent starting point, especially for those with – or working toward – a security clearance.
Entry-Level Roles That Lead to Threat Intelligence
Starting your career in roles like Security Operations Center (SOC) Analyst is a common pathway. These analysts monitor network activity in real time, handle security alerts, and respond to incidents. The data they work with often becomes the foundation for cyber threat intelligence (CTI) analysis. Most SOC analyst positions require a Secret or Top Secret clearance and offer salaries between $80,000 and $120,000 annually [4]. Other entry-level roles such as Junior Cyber Defense Analyst and Incident Responder focus on defending systems and diagnosing breaches, providing valuable insight into threat actor behavior. These jobs typically require TS/SCI clearances and pay between $100,000 and $140,000 [4].
For those interested in intelligence gathering, All-Source Intelligence Analyst roles focus on organizing information from various sources, a key component of CTI. Similarly, Target Analyst Reporter (Level 1) positions involve researching and reporting on specific intelligence targets, often in military or agency settings. These roles, which usually demand TS/SCI clearances with polygraphs [1], range from intelligence reporting to technical specialties like Vulnerability Analyst and Junior Malware Analyst. These technical roles focus on identifying exploitable vulnerabilities and dissecting malicious code.
"Unlike general cyber security analysts, whose role is typically to respond to incidents or monitor systems for breaches, CTI analysts work proactively. This means gathering intelligence from open and closed sources to predict and prevent attacks before they happen." – SecurityClearedJobs.com [1]
Veterans often bring valuable experience from military roles in classified communications, risk management, and simulation exercises [4]. To bridge the gap between military and civilian roles, certifications like Security+ or CySA+ can help. Hands-on platforms such as TryHackMe, HackTheBox, and RangeForce are also great tools for showcasing your skills [4].
"When you’ve owned mission-critical systems where the blast radius of a mistake is measured in lives, not log lines, you develop a rare sixth sense for risk that you simply can’t teach in a bootcamp." – Mick Baccio, Global Security Advisor, Splunk [6]
These roles allow you to apply your technical skills and certifications in real-world scenarios, building a strong foundation for a career in threat intelligence. For even more structured learning, government programs can provide valuable hands-on experience in cleared environments.
Internships and Government Programs for Cleared Professionals
Government internships and scholarships offer structured pathways into cleared cybersecurity roles, often with guaranteed employment. Programs like the DoD SMART Scholarship-for-Service cover full tuition for STEM students, provide a stipend, and guarantee Department of Defense employment after graduation [8]. The DIA STOKES Educational Scholarship Program supports high school seniors and college underclassmen with tuition assistance in exchange for an 18-month service commitment for each sponsored academic year [8]. Another option is the DIA Summer Internship Program (SIP), which provides 10 to 12 weeks of hands-on experience in intelligence analysis and STEM fields. This program requires TS/SCI clearance [8].
For active-duty service members, DoD SkillBridge is an excellent opportunity. This program allows transitioning service members to spend their final 180 days in civilian internships with defense contractors or government agencies. For example, in June 2025, CCS Global Tech’s Veterans Cyber Placement Program successfully placed nine veterans with Security+ certifications and TS/SCI clearances into a major DoD project within three weeks. By providing on-the-job Risk Management Framework (RMF) training, the team saved over $600,000 in potential delays and training costs [5]. Similarly, the DHS Intelligence & Analysis (I&A) Internship offers a 10-week summer program focusing on cybersecurity and terrorism intelligence analysis. This program also requires Top Secret/SCI clearance and pays according to General Schedule (GS) grades 3 to 9, depending on education level [7].
When applying for these programs, keep in mind that you’ll need to meet clearance requirements. For example, ensure you’ve been physically present in the U.S. during the academic year before your internship – studying abroad during this time could complicate the process [7]. Veterans can also benefit from training academies like SANS VetSuccess or IBM Veterans Cyber Academy to earn certifications such as Security+, CySA+, or GCTI [4]. An active security clearance is a key asset, saving employers the 6 to 18 months typically required to process new clearances for civilian hires [6].
Networking and Career Resources for Cleared Professionals
Once you’ve gained solid hands-on experience, the next smart move is building a strong professional network. For cleared cybersecurity professionals, this means tapping into platforms and events specifically designed for individuals with active security clearances. These specialized opportunities not only complement your technical skills but also connect you with roles that align with your expertise in threat intelligence.
Using Cleared Cyber Security Jobs to Find Opportunities
Cleared Cyber Security Jobs is a platform tailored to link cleared professionals with hiring managers actively seeking threat intelligence analysts. Here’s how you can make the most of it:
- Upload your resume: Ensure it highlights your core skills and clearance level.
- Set up job alerts: Use keywords and filters to get notified about roles that match your expertise and location preferences.
- Optimize your profile: Make it easy for recruiters to see your qualifications and availability.
- Stay active: Regularly logging in increases your visibility to recruiters.
- Control privacy settings: Keep your identity protected while showcasing your skills.
The platform also lets you track in-demand skills like SIEM expertise, malware analysis, or regional knowledge. For example, as of March 2026, roles like Cyber Threat Intelligence Team Lead at Procession Systems in Reston, VA (Top Secret/Polygraph required) and CTI Lead at SOSi in Ashburn, VA (TS/SCI required) demonstrate the range of opportunities available to cleared professionals.
Attending Job Fairs and Industry Events
Cleared job fairs are a direct gateway to hiring managers from government agencies and defense contractors. These events are especially helpful for military personnel transitioning to civilian roles in the cleared workforce.
"I attended a Cleared Job Fair and was offered a position shortly after. I accepted and moved directly from the military into my current position, without a lapse in employment." – Technical Project Manager, CACI[9]
For 2026, several key events offer excellent networking opportunities:
- Connect West (San Diego, March 24–25): Focuses on Navy and defense innovation.
- GEOINT Event (Aurora, CO, May 4): Targets professionals in geospatial intelligence.
- Intel Summit (Bethesda, MD, August 26): Concentrates on cybersecurity and intelligence community roles.
- Connect Reston (Reston, VA, October 15–16): Provides direct access to employers in cybersecurity and intelligence.
These events allow you to meet hiring managers, ask in-depth questions about team structures and projects, and even participate in on-site interviews. Each interaction is a step toward advancing your career in threat intelligence.
Conclusion
Pursuing a career as a Threat Intelligence Analyst with a security clearance requires a mix of technical skills, recognized certifications, and strategic networking. That clearance sets you apart, opening doors to specialized roles with salaries that can exceed $150,000.
Certifications are key. Credentials like GCTI, CySA+, and CISSP demonstrate your expertise and are especially helpful when transitioning from roles like SOC analyst or incident responder into threat intelligence. Combine these certifications with practical experience using tools and frameworks like MITRE ATT&CK and the Cyber Kill Chain to better understand and profile threat actors.
Experience sharpens your instincts. Starting in entry-level roles, such as security operations or incident response, helps you develop the ability to sift through data and identify actionable intelligence. This hands-on practice builds the intuition needed to anticipate and prevent attacks – something that goes beyond what you can learn from study alone. By blending technical expertise with real-world experience, you create a solid foundation for success.
Once your skills and credentials are in place, networking becomes essential for career growth. Connections open doors. Platforms like Cleared Cyber Security Jobs link you directly to hiring managers looking for cleared professionals. Attending job fairs in hubs like Northern Virginia, Fort Meade, or Colorado Springs allows you to meet with recruiters from top defense contractors and government agencies, often leading to quicker hiring decisions than traditional methods.
FAQs
What does a cleared threat intelligence analyst do day to day?
A cleared threat intelligence analyst plays a crucial role in safeguarding against cyber threats. Their job involves monitoring, analyzing, and responding to potential risks by staying ahead of adversary tactics and maintaining a clear understanding of the threat landscape.
Key responsibilities include:
- Researching emerging threats to understand new risks and vulnerabilities.
- Analyzing threat data to uncover patterns and potential attack methods.
- Sharing intelligence with relevant teams to ensure coordinated responses.
- Recommending mitigation actions to reduce risks and strengthen defenses.
Additionally, they prepare detailed reports to keep leadership informed, enabling better decision-making to protect both organizational and national security from sophisticated cyber adversaries.
Which certification should I get first for threat intelligence?
If you’re just stepping into the world of cybersecurity or making a career shift, Security+ is a great place to start. This certification lays the groundwork by covering essential knowledge and skills, making it an excellent entry point for those new to the field. In fact, some roles even list it as a requirement.
Once you’ve mastered the basics, you can aim higher with advanced certifications like CISSP or explore specialized credentials in threat intelligence to deepen your expertise and open up more career opportunities.
How can I get a security clearance if I don’t have one yet?
To obtain a security clearance, you’ll need to follow the official process established by the U.S. government. This involves filling out the SF-86 form and undergoing a thorough background investigation. The review covers areas like your criminal history, financial responsibility, and loyalty to the United States. Generally, you must have a sponsor – usually an employer or a government agency – connected to a position that requires clearance. Keeping a clean record and showing sound judgment are key factors in maintaining your eligibility.
