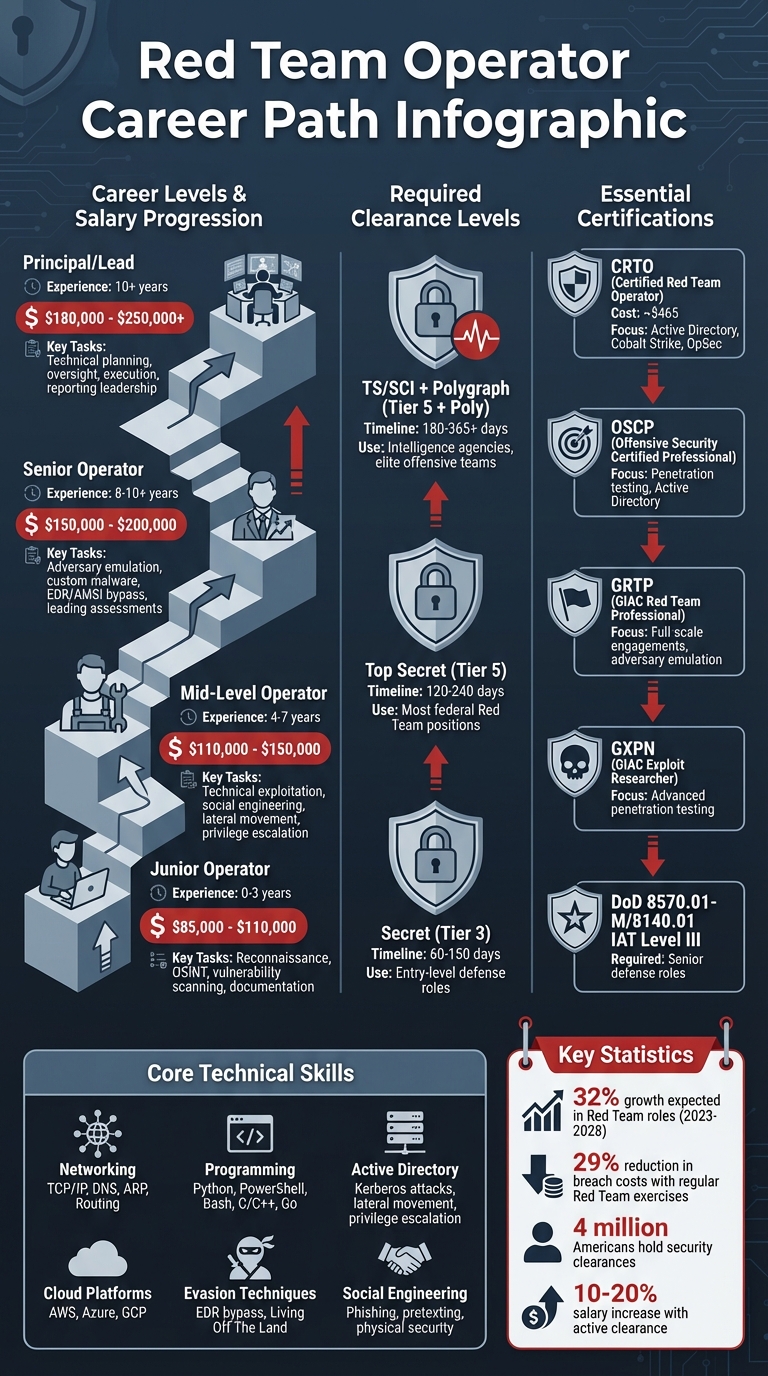
Red Team Operators simulate cyberattacks to identify vulnerabilities and improve security, especially for government and defense sectors. These roles are highly specialized, often requiring security clearances like TS/SCI, advanced technical skills, and certifications such as OSCP and CRTO. Here’s a quick breakdown:
- Clearance Requirements: Most roles need at least Top Secret clearance, often with SCI or Polygraph.
- Skills: Expertise in networking, programming (Python, PowerShell), Active Directory exploitation, and evasion techniques is essential.
- Tools: Common tools include Cobalt Strike, Mimikatz, and BloodHound for tasks like credential theft and lateral movement.
- Certifications: Key certifications include CRTO, OSCP, and GIAC credentials like GRTP and GXPN.
- Career Growth: Salaries range from $85,000 for entry-level roles to $250,000+ for senior positions, with opportunities to specialize in areas like cloud red teaming or malware development.
Demand for Red Team experts is growing (32% increase expected by 2028), making this a lucrative and impactful career path. Keep reading for detailed steps on how to get started and advance in this field.
Red Team Operator Career Path: Skills, Certifications, and Salary Progression
Security Clearance Requirements and Eligibility
Security Clearance Levels Explained
The U.S. government uses three main clearance levels: Confidential, Secret, and Top Secret (TS). These levels reflect the potential harm unauthorized disclosure could cause, ranging from "damage" at the Confidential level to "exceptionally grave damage" at Top Secret[4][5].
For Red Team Operators, Top Secret or Top Secret/Sensitive Compartmented Information (TS/SCI) clearance is often a must[5][8]. These roles involve simulating advanced cyberattacks on classified networks, requiring access to highly sensitive intelligence and operational data. According to a national security law firm, additional compartments like SCI and Special Access Programs (SAP) are often layered on top of a Top Secret clearance to further restrict access[6].
It’s worth noting that SCI and SAP aren’t separate clearance levels. Instead, they are compartments that impose stricter access controls, even for those with Top Secret clearance[5][6]. Many Red Team positions also require polygraph tests, especially when working with intelligence agencies or special operations.
| Clearance Level | Investigation Tier | 2026 Average Timeline | Red Team Relevance |
|---|---|---|---|
| Secret | Tier 3 | 60–150 days | Entry-level defense contractor roles |
| Top Secret | Tier 5 | 120–240 days | Most federal Red Team positions |
| TS/SCI + Polygraph | Tier 5 + Poly | 180–365+ days | Intelligence agencies, elite offensive teams |
How to Obtain and Maintain Security Clearance
To apply for a security clearance, you’ll need a sponsoring agency or contractor to kickstart the process. Your employer submits your application through eApp, which replaced the older e-QIP system in 2026[8]. This process involves filling out Standard Form 86 (SF-86), which asks for 10 years of detailed information about your residence, employment, education, and foreign contacts[8].
The Defense Counterintelligence and Security Agency (DCSA) handles over 95% of federal background checks[8]. For Top Secret clearance, investigators conduct in-depth interviews with neighbors, coworkers, and references to evaluate your reliability and trustworthiness under the "whole-person concept"[8][9]. Cybersecurity writer Kevin James highlights the importance of honesty during this process:
The agencies value candor more than perfection, so providing truthful answers, even about minor indiscretions, proves integrity[10].
The clearance process has shifted to Continuous Vetting (CV) under the Trusted Workforce 2.0 initiative. This system replaces the old periodic reinvestigation cycle, monitoring criminal records, financial data, and travel patterns in real time[8]. To maintain your eligibility, you must self-report major life events like arrests, significant debt, or foreign travel to your Facility Security Officer (FSO)[8][10].
Preparing ahead is key. Compile your 10-year history, run a credit report, and resolve any financial issues – since financial problems are a common reason for clearance denial[8]. For cybersecurity professionals, adjudicators may also review your public-facing online activity, including GitHub contributions and social media, so it’s wise to clean up your digital footprint before applying[8].
These steps not only protect national security but also set the stage for your career growth, as discussed below.
How Security Clearance Impacts Your Red Team Career
Having an active clearance opens doors to more job opportunities and higher earning potential. With over 4 million Americans holding national security clearances, about 85% of them work with the Department of Defense[7]. The clearance requirement creates a smaller talent pool, reducing competition compared to commercial cybersecurity roles and making cleared professionals highly sought after.
A clearance can increase salaries by 10%–20%[7][8]. While the government covers the cost – $5,596 for a Top Secret clearance and $433 for a Secret clearance (2020 rates)[4] – you won’t pay anything out of pocket. This investment underscores the value placed on cleared professionals.
Beyond salary, a clearance grants access to specialized training unavailable elsewhere. Programs like the DCART Operator Training Program provide structured pathways from Apprentice to Senior Operator. Many roles also require compliance with DoD Directive 8570.01-M and certifications like CASP+, CISSP, or GCED[3]. These opportunities accelerate skill development while engaging in missions critical to national security.
Maintaining your clearance involves staying proactive. Although Continuous Vetting automates much of the monitoring, you’ll still need to update your SF-86 every five years[10]. Staying on top of your financial health, foreign contacts, and personal conduct becomes second nature for those committed to a career in the cleared community.
sbb-itb-bf7aa6b
Technical Skills and Tools for Red Team Operators
Required Technical Skills
To thrive as a Red Team Operator, you need a solid grasp of core networking protocols like TCP/IP, DNS, ARP, and routing. This knowledge is essential for analyzing network traffic and crafting packet manipulations to slip past firewalls and intrusion detection systems.
Programming and scripting are equally important. Languages like Python, Bash, and PowerShell are staples for automation, while C, C++, and Go are often used to create custom exploits or malware. Given that many environments operate within Windows domains, understanding Active Directory exploitation is a must. This includes techniques like Kerberos attacks, lateral movement, and privilege escalation.
Modern red teaming relies heavily on advanced evasion techniques. This means bypassing tools like Endpoint Detection and Response (EDR) and antivirus software. One effective method is "Living Off The Land", which involves using legitimate, Microsoft-signed tools to execute code without raising alarms.
Finally, social engineering and physical security skills are vital. Running authorized phishing campaigns, creating pretexting scenarios, and even performing controlled physical break-ins can help assess the human element of security – often the weakest link.
These technical skills lay the groundwork for using the industry-standard tools detailed next.
Common Red Team Tools
Cobalt Strike is the go-to Command and Control (C2) tool for professional red teams. This tool, developed in 2012 and now owned by Fortra, is designed to simulate advanced persistent threats (APTs). Its Malleable C2 profiles allow operators to tweak network traffic to blend in with normal activity. Adjusting elements like user agents and sleep times helps evade detection.
Other popular C2 frameworks include Sliver, an open-source tool written in Go with over 1,000 GitHub forks, as well as PowerShell Empire, Mythic, and Covenant for .NET-based operations. Many operators also set up a "Long-Haul" server for maintaining persistence in case their primary access point is compromised.
Tools for credential theft and privilege escalation are equally critical. Mimikatz is a favorite for extracting plaintext passwords and NTLM hashes from memory. When paired with tools like BloodHound and PowerView, it helps map Active Directory relationships and uncover attack paths. For local privilege escalation, tools like LinPEAS and WinPEAS are invaluable for identifying system vulnerabilities.
| Category | Essential Tools | Primary Use Case |
|---|---|---|
| Command & Control | Cobalt Strike, Sliver, Mythic, Empire | Maintaining access and issuing commands to hosts |
| Credential Access | Mimikatz, Hashcat | Extracting passwords or cracking hashes offline |
| Lateral Movement | Impacket, psexec, BloodHound | Moving across networks to reach high-value targets |
| Reconnaissance | Nmap, Amass, SharpHound | Identifying active hosts, services, and domain paths |
| Persistence | Nishang, Netsh, Scheduled Tasks | Ensuring access survives reboots or password changes |
Reconnaissance tools like Nmap, Amass, and Recon-ng help identify active hosts and services. For mapping Active Directory environments, SharpHound and PowerView are indispensable. Lateral movement often relies on Impacket scripts like psexec.py and wmiexec.py, which allow operators to move between systems using stolen credentials or hashes.
Cloud and Multi-Tenant Environment Skills
In today’s landscape, expertise in cloud and multi-tenant environments is essential. Operators need proficiency with the "Big Three" cloud providers – AWS, Azure, and GCP – as well as secondary platforms like IBM and Oracle Cloud. This involves understanding concepts like Identity and Access Management (IAM), Virtual Private Clouds (VPCs), storage containers, databases, and cloud-native APIs.
Familiarity with Infrastructure as Code (IaC) tools like Terraform, Ansible, and Docker is increasingly important. These tools allow red teamers to simulate how attackers might exploit automated deployment pipelines. Additionally, knowledge of container orchestration platforms like Kubernetes is vital for targeting applications in virtualized environments. Understanding cloud-based CI/CD systems – such as AWS Code Pipeline, Azure DevOps, and GCP Cloud Build – can also help identify vulnerabilities in software supply chains.
For practical cloud red teaming, RedCloud OS is a great starting point. This Debian-based platform comes pre-loaded with tools like Pacu and CloudMapper for AWS, MicroBurst and AzureHound for Azure, and GCPBucketBrute for GCP. Platforms like Ludus allow operators to build automated labs with complex, multi-machine networks using IaC, providing a controlled space to practice techniques like lateral movement and privilege escalation.
Deploying C2 frameworks like Sliver, Mythic, or Cobalt Strike via cloud-hosted redirectors and domain fronting can help mask malicious traffic. Monitoring your own attack "noise" with tools like Elastic can reveal how cloud-native security solutions respond to threats. With demand for Red Team expertise projected to grow by 32% between 2023 and 2028 [1], staying ahead in these areas is critical for success.
Certifications and Training Programs
Required Certifications
The Certified Red Team Operator (CRTO) from Zero-Point Security is a key starting point for anyone entering red teaming. It emphasizes Active Directory tradecraft, Command and Control (C2) frameworks – specifically Cobalt Strike – and operational security to avoid detection [13]. The certification exam spans 48 hours over four days, requiring participants to capture 6 out of 8 flags [14]. At roughly $465, it’s a cost-effective way to gain practical experience with tools like Cobalt Strike [13].
Another highly regarded certification is the Offensive Security Certified Professional (OSCP). This credential provides a solid foundation in penetration testing and Active Directory-related tasks, making it a staple for many red teamers [16]. For professionals working in defense sectors, certifications must comply with DoD 8570.01-M/8140.01 standards, with many senior roles requiring an IAT Level III certification [3]. Additionally, the GIAC Red Team Professional (GRTP) certifies expertise in conducting full-scale engagements, including adversary emulation, setting up C2 infrastructure, and bypassing defense mechanisms [12].
"The opportunity to gain hands-on experience with Cobalt Strike was invaluable, plus the added ‘challenge’ of performing all of the TTPs through Cobalt Strike rather than native PowerShell." – Kyle Gray, Security Researcher [14]
For government-specific roles, internal programs like the Red Team Apprentice Course (RTAC) and Red Team Journeyman Course (RTJC) are often mandatory. These are part of the DCART training pipeline, with positions at locations like Fort Belvoir, VA, explicitly requiring them [3].
These certifications establish a strong foundation, preparing professionals for advanced training programs.
Recommended Training Courses
For those looking to deepen their expertise, Red Team Ops II (RTO II) from Zero-Point Security offers advanced instruction. It focuses on detection-aware red teaming, evading Endpoint Detection and Response (EDR) tools, and creating custom tooling using Cobalt Strike [18]. This course now includes lifetime access and ongoing lab environments through a new platform [18].
GIAC certifications, such as the GXPN (Exploit Researcher and Advanced Penetration Tester) and GPEN (Penetration Tester), are also highly valued, particularly in government contracting roles [3][12]. These certifications are administered via ProctorU or PearsonVUE [12].
To complement formal training, platforms like Hack The Box and TryHackMe provide hands-on lab environments. These allow professionals to refine their skills and maintain practical knowledge [2]. Many training providers now offer browser-based labs using tools like Apache Guacamole, enabling access to expensive software such as Cobalt Strike while ensuring compliance with licensing requirements [17].
Beyond certifications and courses, continuous learning is essential for staying sharp in this fast-moving field.
Keeping Up with Industry Changes
Red teaming evolves quickly, as defenders adopt new detection methods and adversaries craft innovative evasion strategies. To stay ahead, professionals should regularly practice creating portfolio-ready artifacts, such as detailed reports, writeups, and demonstrations, rather than simply collecting certifications or digital badges [15].
Engaging with cybersecurity communities like Red Team Village, r/netsec, TrustedSec, and the Hack The Box blog is an excellent way to stay informed. Attending events like DEF CON, Black Hat, and webinars also helps professionals keep pace with industry trends [2][20]. Monitoring Common Vulnerabilities and Exposures (CVEs) is another critical step to stay aware of emerging attack vectors [20].
"Being able to and knowing how to exploit a vulnerability not only looks good for you, but the impact it has on the business is extremely valuable." – Nick Villa, GPEN [19]
For those in defense or cleared roles, maintaining compliance requires holding the appropriate IAT Level III certification, as previously mentioned [3]. Reviewing job postings – at least 20 or more – can help identify specific skill gaps in areas like Red Team, Web, or Cloud tracks, ensuring that your training aligns with current market demands [15]. This proactive approach to skill development is crucial for staying competitive in high-stakes environments and advancing your career.
Career Progression and Specialization Options
Career Levels and Responsibilities
Advancing in red teaming involves climbing a structured career ladder, with roles and salary ranges clearly defined. Cleared Red Team Operators typically follow a progression from entry-level roles to advanced leadership positions, each with distinct responsibilities.
Junior Operators, those with 0–3 years of experience, earn between $85,000 and $110,000 annually. Their work focuses on tasks like reconnaissance, OSINT (Open Source Intelligence) gathering, vulnerability scanning, and assisting with documentation. Many in these roles come from IT backgrounds or have worked as SOC analysts [1].
Mid-Level Operators, with 4–7 years of experience, see salaries ranging from $110,000 to $150,000 [1]. Their responsibilities expand to include technical exploitation, social engineering, lateral movement, and privilege escalation. Earning certifications like OSCP often marks a turning point for professionals at this stage.
Senior Operators bring 8–10+ years of experience and earn between $150,000 and $200,000 annually [1]. They take on more advanced tasks, such as emulating adversary tactics, creating custom malware, bypassing EDR (Endpoint Detection and Response) and AMSI (Antimalware Scan Interface), and leading major assessments. For those with over a decade of experience, Principal or Lead positions offer salaries of $180,000 to $250,000+ [1]. These roles require a "Technical Lead" mindset, involving oversight of technical planning, execution, and reporting for assessments [3].
Specialization Areas
As red teaming continues to evolve, operators have the opportunity to specialize in distinct areas. One such track is Malware Development and Evasion, which involves creating techniques to bypass antivirus systems and EDR solutions [1][3].
Another growing focus is Cloud Red Teaming, where operators target environments like AWS, Azure, and GCP. This specialization reflects the shift toward cloud-native attack strategies, with demand for expertise in this area increasing. In fact, Red Team roles are expected to grow by 32% between 2023 and 2028 [1][11].
For those interested in industrial systems, Operational Technology (OT) and Critical Infrastructure testing provides a chance to apply red teaming skills to industrial control systems and other non-IT networks [1].
Many cleared positions require candidates to meet specific benchmarks, such as passing aptitude tests or fulfilling "Apprentice" or "Journeyman" criteria outlined in the DCART Handbook [3]. Additionally, these roles often involve travel, with approximately 15% of assignments requiring visits to CONUS and OCONUS locations [3].
Leadership and Mentorship Opportunities
Moving from technical roles into leadership demands a shift in focus, with a greater emphasis on soft skills. Red Team Leads, Technical Program Managers, and Cyber Planners must master communication, emotional intelligence, and the ability to explain complex findings to non-technical audiences [22][23].
"We’re looking for you to be a good fit for the team. More so than the technical knowledge oftentimes, I’m looking for the soft skills that you bring to the team."
– Matt O’Hara, Red Cyber Program Manager, Valiant [24]
Strong leaders embrace a servant leadership style, prioritizing team development through coaching sessions, knowledge sharing, and encouraging participation in activities like capture-the-flag events or CVE reporting [21][25]. They also establish internal processes, develop operational plans with measurable goals (KPIs and KRIs), and manage budgets for tools and certifications. Aspiring leaders can further support their teams by helping junior operators build confidence through public speaking, blogging, or presenting at conferences.
Organizations play a critical role in fostering growth, offering opportunities that balance technical skill development with leadership training. With these pathways in place, the next step is to explore strategies for securing and advancing in cleared Red Team roles.
Job Search Strategies for Cleared Professionals
Using Cleared Job Boards and Resources
Landing a Red Team position that requires security clearance calls for a focused approach. Platforms like Cleared Cyber Security Jobs are designed specifically for professionals with active clearances. These job boards allow you to filter positions by clearance level, location, and technical skills, making it easier to find roles suited to your expertise.
When building your profile, make sure your current clearance level is highlighted on your resume. Employers often prioritize candidates with active and in-scope clearances, as this saves them both time and money by avoiding the need to sponsor new clearances. To stay ahead, set up job alerts using keywords such as "Red Team", "Offensive Security", and "Penetration Testing" paired with your clearance level. These alerts can notify you as soon as new opportunities arise. While job boards are an excellent starting point, a well-rounded strategy also involves expanding your professional network.
Building Your Professional Network
Once you’ve optimized your job board strategy, it’s time to focus on networking. Connecting with others in the cleared community can open doors to opportunities that might not be advertised. Attending cleared job fairs hosted by platforms like Cleared Cyber Security Jobs is a great way to meet hiring managers directly. These events often provide access to decision-makers from defense contractors and government agencies actively looking for cleared Red Team professionals.
In addition to job fairs, consider joining professional organizations related to offensive security and cleared work, such as local ISSA chapters or groups for cleared professionals. Online communities focused on cleared cybersecurity can also offer valuable insights into potential employers and upcoming opportunities. Building relationships with recruiters who specialize in cleared positions can give you a head start on roles that haven’t yet been posted publicly. Since many cleared jobs are filled through referrals, fostering these connections can be key to standing out. Networking, combined with your technical expertise and clearance status, puts you in a strong position to compete in this specialized field. As you expand your network, it’s equally important to carefully evaluate job offers to ensure they align with your goals.
Evaluating Job Offers and Compensation
When assessing offers for Red Team roles, it’s important to look beyond just the paycheck. Consider the travel requirements – how often you’ll need to travel, whether it’s mandatory, and if the company provides per diem or other compensation for extended assignments.
Take a close look at the benefits package. Things like health insurance, retirement plans, and support for professional development can significantly impact the overall value of an offer. Some employers cover costs for certifications, conferences, and training, which can save you thousands of dollars each year. Another factor to weigh is contract stability – positions tied to long-term government contracts often provide more job security compared to those dependent on short-term task orders. Lastly, take time to assess the work environment and team culture. Ask about mentorship opportunities, budgets for tools, and how the company supports the technical growth of its Red Team members. Combining this evaluation with your certifications and practical skills will help you make informed decisions and advance your cleared Red Team career.
Critical Skills For Red Teaming – CyberCast After Dark – Ep.15
Conclusion
Breaking into Red Team operations as a cleared professional takes time, effort, and a dedication to learning. Most elite Red Team operators spend 6 to 10 years honing their skills, starting with foundational IT roles and progressing to adversary emulation specialties [1]. With Red Team roles expected to grow by 32% between 2023 and 2028, and regular exercises shown to reduce breach costs by 29% [1], the demand for skilled professionals in this field is on the rise.
Your security clearance is a major advantage, giving you access to specialized government training programs and high-value contracts. When combined with certifications like OSCP and CRTO, it sets you apart for competitive roles in government and defense sectors [1]. Add hands-on experience with tools like Cobalt Strike and Metasploit, and you’ll be ready for roles offering salaries ranging from $85,000 for entry-level positions to over $250,000 for senior-level leadership [1]. However, technical skills alone won’t cut it – you need to develop an adversarial mindset and the ability to connect technical exploits with real-world business risks.
Keep your skills sharp with hands-on labs, Capture The Flag competitions, and staying current with industry resources. Above all, approach this work responsibly and collaboratively. As Jayson E. Street aptly said:
"The difference between a Red Teamer and a criminal is permission. That permission comes with tremendous responsibility."
- Jayson E. Street, Red Team Expert [1]
FAQs
Can I become a Red Team Operator without a TS/SCI clearance?
Yes, many advanced Red Team Operator roles, particularly those tied to the Department of Defense, do require a TS/SCI clearance. However, there are some entry-level or less sensitive positions that don’t have this requirement. These roles can serve as a stepping stone, allowing you to build experience and work toward qualifying for positions that demand higher clearances.
What should I learn first if I’m new to red teaming?
If you’re just starting with red teaming, it’s important to begin with the basics. Start by strengthening your understanding of Linux and Windows fundamentals, as these operating systems play a key role in red team activities. Once you’re comfortable with these, move on to setting up virtualization environments. These allow you to safely practice tools and techniques without risking real systems.
As you gain confidence, work on developing your exploitation and post-exploitation skills step by step. Remember, mastering the basics is essential before diving into more advanced strategies. Focus on building a solid foundation to ensure long-term success in red teaming.
Which cert matters most for cleared Red Team roles: OSCP or CRTO?
The OSCP is well-regarded for its focus on core penetration testing skills, making it a solid choice for building a strong baseline in offensive security. On the other hand, the CRTO caters specifically to Red Team operations, with a strong emphasis on Active Directory exploitation and tools like Cobalt Strike. For individuals pursuing cleared Red Team roles, the CRTO often proves more applicable, as it mirrors real-world Red Team scenarios and techniques.
