If you’re aiming for a career as a DevSecOps Engineer in the cleared sector, here’s the bottom line: this role is about integrating security into every stage of software development, especially within high-stakes environments like defense and government. With demand growing due to national security needs, cleared professionals with the right skills and certifications are in high demand. Here’s a quick breakdown:
- Key Skills: Automating CI/CD pipelines, Infrastructure as Code (IaC), containerization (Docker/Kubernetes), and advanced security practices like SAST/DAST.
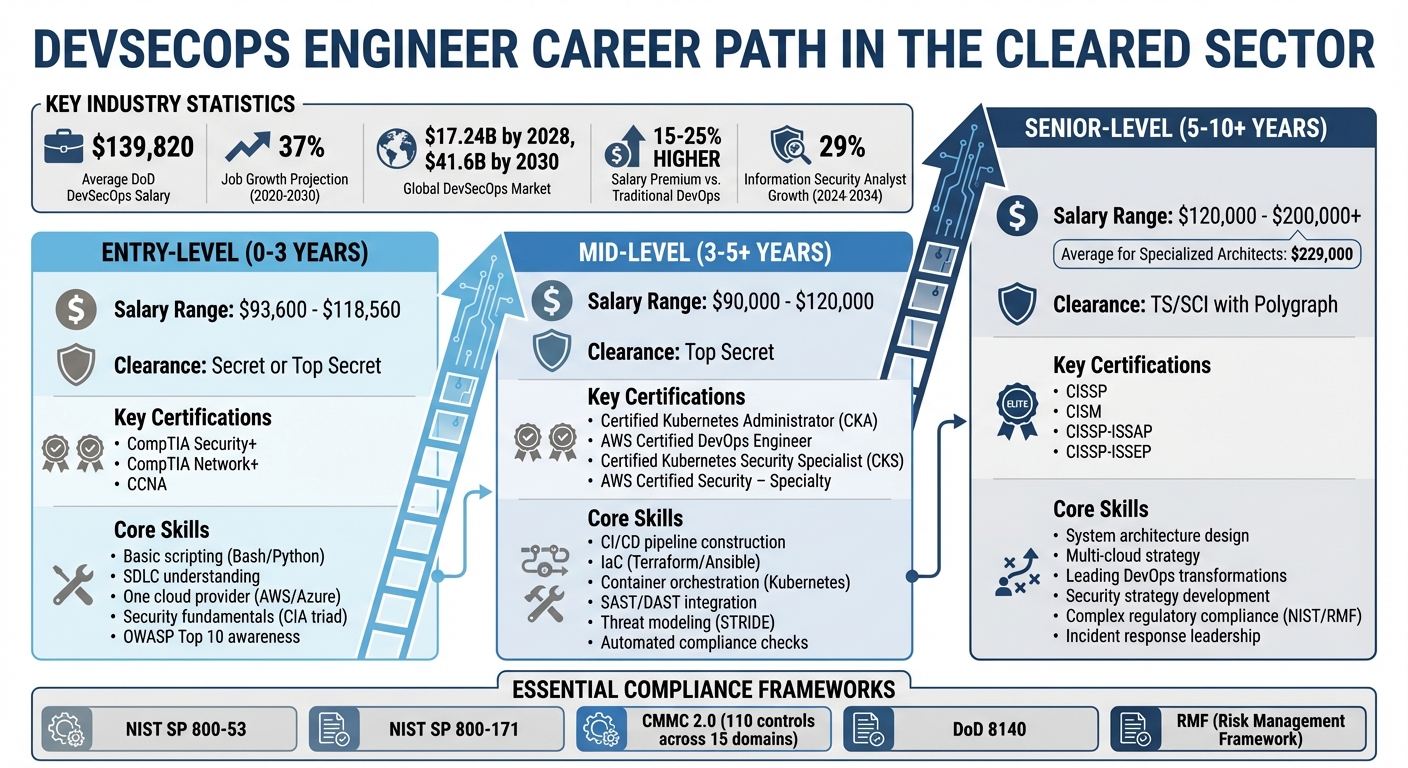
- Certifications: CompTIA Security+ (entry-level), Certified Kubernetes Administrator (CKA), AWS DevOps Engineer, CISSP (senior-level).
- Clearances: Secret, Top Secret (TS), or TS/SCI with polygraph, depending on role sensitivity.
- Salary: Average around $139,820, with senior roles exceeding $200,000.
- Compliance: Mastery of frameworks like NIST SP 800-53, RMF, and CMMC 2.0 is essential.
The field is expanding, with the global DevSecOps market projected to hit $17.24 billion by 2028. To thrive, focus on security automation, continuous learning, and maintaining active clearances.
For more details, including career progression tips and how to stand out in the job market, read on. This guide covers everything from certifications to real-world applications in cleared environments.
DevSecOps Career Progression: Skills, Certifications, and Salaries by Level
DevSecOps in the Cleared Community
What DevSecOps Means in Cleared Roles
In cleared environments, DevSecOps goes beyond the standard "shift left" approach. The Department of Defense (DoD) defines it as the integration of security tools and practices directly into the development pipeline. This involves heavy automation and fostering a shared sense of responsibility among teams. For cleared professionals, this means operating within structured "Software Factories" designed for high-threat, classified missions [3].
A great example is the U.S. Air Force’s Kessel Run. Before 2017, their mission operations heavily relied on manual processes. But after teaming up with Pivotal Labs and embracing DevSecOps principles, they delivered their first product in just three months. By 2025, Kessel Run was deploying 4,000 capabilities annually [3].
Cleared DevSecOps engineers often work in environments that span TS/SCI, Secret, and Unclassified levels. These settings frequently include air-gapped systems and SCIFs, where commercial cloud tools aren’t an option. Instead, they rely exclusively on government-approved platforms like Platform One to ensure security is a constant, built-in process [2][3].
Another critical component of cleared roles is the shift from traditional one-time Authorizations to Operate (ATO) to the continuous model known as Continuous Authorization to Operate (cATO). This approach demands ongoing monitoring of Risk Management Framework (RMF) controls, active cyber defense, and compliance with approved DevSecOps reference designs. Since securing a traditional ATO is often the longest step in federal software development, moving to cATO is a game-changer [3].
These practices are the foundation of the rigorous compliance required in cleared environments.
Compliance and Governance Standards
Cleared DevSecOps roles also demand strict adherence to DoD and industry compliance frameworks. A key directive is DoD 8140, which replaced DoD 8570. This updated framework shifts from a certification-only model to a role-based competency system aligned with the DoD Cyber Workforce Framework (DCWF). The deadline for compliance with these qualifications is February 15, 2026 [4][5].
Another cornerstone is the Cybersecurity Maturity Model Certification (CMMC) 2.0, which governs how defense contractors protect Controlled Unclassified Information (CUI). Most cleared DevSecOps roles align with Level 2 of CMMC 2.0, requiring implementation of 110 specific security controls across 15 domains, such as Access Control and System and Communications Protection. Organizations typically need 12–24 months to prepare for this certification [3].
Daily operations also involve aligning technical activities with standards like NIST SP 800-53 (Security and Privacy Controls) and NIST SP 800-171 (Protecting CUI) [5][3]. Engineers manage Plans of Action and Milestones (POA&M) to track and address vulnerabilities identified during assessments. This level of documentation and continuous monitoring stands in stark contrast to the more flexible security practices often seen in the commercial sector.
| CMMC 2.0 Level | Focus | Primary Requirement |
|---|---|---|
| Level 1 (Foundational) | Basic safeguarding of FCI | FAR Clause 52.204-21 |
| Level 2 (Advanced) | Protecting CUI | NIST SP 800-171 Rev 2 |
| Level 3 (Expert) | High-priority programs | NIST SP 800-172 |
"Digital transformation starts with processes and then moves to skills and technology."
- Lt. Col. Max Reele, Kessel Run [3]
Compliance also extends to securing the software supply chain. Engineers must ensure that all software artifacts come from approved sources. Tools like Platform One’s Iron Bank provide a centralized repository of pre-vetted, hardened container images. This includes components such as Repo One for source code management, Big Bang for CI/CD pipelines, and Iron Bank for hardened containers. These resources help reduce risks associated with unvetted open-source software [2][3].
For cleared professionals, mastering these compliance and governance standards is essential for advancing in DevSecOps roles.
sbb-itb-bf7aa6b
How to Go from Help Desk to DevSecOps Engineer (Step-by-Step Path)
Required Skills and Technical Competencies
Cleared DevSecOps professionals operate in a space where compliance and governance are non-negotiable. To excel, they need a solid mix of technical expertise and security-specific skills.
Core Technical Skills
Cleared DevSecOps engineers must excel in automating CI/CD pipelines using tools like Jenkins, GitLab, or Bitbucket. These tools streamline integration processes while embedding security checks at every stage.
Infrastructure as Code (IaC) expertise is another must-have. Tools like Terraform, AWS CloudFormation, Ansible, Chef, and Puppet help ensure deployments align with strict security standards and provide the audit trails required for achieving an Authority to Operate (ATO).
Containerization (using Docker) and orchestration (via Kubernetes or Docker Swarm) are key skills. Engineers should also have a deep understanding of security services provided by cloud platforms like AWS, Azure, or Google Cloud.
"A DevOps engineer is an IT generalist who should have a wide-ranging knowledge of both development and operations, including coding, infrastructure management, system administration, and DevOps toolchains."
- Tom Hall, DevOps Advocate & Practitioner, Atlassian
Proficiency in programming languages such as Python, Java, Bash, PowerShell, Go, or JavaScript is critical for automating security tasks and responding quickly to vulnerabilities. With the average cost of a data breach sitting at $4.45 million, these skills are more vital than ever [6].
Security-Specific Skills
Beyond general DevOps capabilities, cleared roles require advanced security knowledge. Engineers must codify DISA STIG and FedRAMP baselines into IaC templates, ensuring systems meet hardening requirements and accelerating the ATO process [8].
Policy-as-Code tools like Terraform, CloudFormation, or Packer are essential for maintaining consistent security configurations.
"Configuration automation using policy as code (PaC) can keep IT configurations in a desired state that complies with relevant DISA STIGs."
- Puppet [8]
Security testing is another cornerstone. Engineers use tools for Static Application Security Testing (SAST), Dynamic Application Security Testing (DAST), and Software Composition Analysis (SCA). SAST identifies vulnerabilities like SQL injection early in the development cycle, while DAST uncovers runtime issues such as misconfigurations or cross-site scripting. With supply chain attacks expected to rise 742% by 2026, securing dependencies through SCA is now non-negotiable [7].
Threat modeling frameworks like STRIDE, DREAD, or PASTA allow engineers to proactively identify risks and implement effective controls. Continuous monitoring and drift detection help maintain compliance, even as systems evolve. For example, FedRAMP mandates ongoing monitoring to detect changes in security posture [8]. Automating STIG compliance, as seen in the DoD’s MITRE SAF project, not only speeds up the ATO process but also provides real-time audit evidence [8].
Skills by Career Level
The skills required for cleared DevSecOps roles evolve as professionals advance in their careers.
- Entry-Level: These roles focus on foundational IT skills like basic Bash or Python scripting, understanding the software development lifecycle (SDLC), and familiarity with one cloud provider (e.g., AWS or Azure). Many entry-level engineers transition from system administration, junior development, or security analysis roles. Certifications like CompTIA Security+ help establish a security baseline [1].
- Mid-Level: Engineers at this stage work on containerization (Docker, Kubernetes) and implement IaC tools like Terraform or Ansible. They integrate security testing tools (SAST, DAST, and SCA) into CI/CD pipelines and automate vulnerability scans. Certifications such as Certified Kubernetes Security Specialist (CKS) and AWS Certified Security – Specialty are highly valued. Salaries for mid-level roles typically range from $90,000 to $120,000 [1].
- Senior-Level: Senior engineers focus on architectural design, organization-wide security controls, and policy-as-code implementation. They also translate technical risks into business terms and lead cross-functional teams. Advanced certifications like CISSP or CISM demonstrate expertise in governance, risk management, and security architecture. Salaries for these positions range from $120,000 to $140,000, with leadership roles exceeding $200,000 [1].
| Career Level | Typical Experience | Core Technical Skills | Security-Specific Skills |
|---|---|---|---|
| Entry-Level | 0–3 Years | Basic scripting (Bash/Python), SDLC understanding, familiarity with one cloud provider (AWS/Azure) | Security fundamentals (CIA triad), basic vulnerability scanning, OWASP Top 10 awareness |
| Mid-Level | 3–5+ Years | CI/CD pipeline construction, IaC (Terraform/Ansible), container orchestration (Kubernetes) | SAST/DAST integration, threat modeling (STRIDE), automated compliance checks |
| Senior-Level | 5–10+ Years | System architecture design, multi-cloud strategy, leading DevOps transformations | Security strategy development, complex regulatory compliance (NIST/RMF), incident response leadership |
The demand for these skills is reflected in the market. The global DevSecOps market is expected to soar to $41.6 billion by 2030, up from $3.7 billion in 2021. Job growth for DevSecOps engineers is projected at 37% from 2020 to 2030, with salaries for these roles running 15–25% higher than traditional DevOps positions [9] [10].
This dynamic skill set is the backbone of cleared DevSecOps careers, ensuring professionals meet the rigorous demands of their roles while advancing their careers.
Certifications and Clearance Requirements
For professionals in cleared roles, technical certifications and security clearances aren’t optional – they’re essential for career advancement. These credentials validate both your expertise and trustworthiness, making them critical for success in DevSecOps and related fields.
Required Certifications for Cleared Professionals
The Department of Defense (DoD) uses the DoD 8140 framework to align certifications with specific job functions across four key areas: Cybersecurity, Information Technology, Risk Management, and Systems Development [11]. Your certification needs will depend on your role and career stage.
For entry-level roles, CompTIA Security+ is widely recognized as a baseline certification and must be renewed every three years by earning 50 Continuing Education Units (CEUs) [11]. Many newcomers also pursue CompTIA Network+ or CCNA to build a strong IT foundation.
As you progress, mid-level professionals often add certifications tailored to cloud and DevSecOps. For instance:
- Certified Kubernetes Administrator (CKA): Validates skills in managing containerized environments and costs $375 [12].
- AWS Certified DevOps Engineer – Professional: Focuses on AWS expertise and is priced at $300 [12].
- Microsoft Certified: Azure DevOps Engineer Expert: A more affordable option at $165 [12].
- HashiCorp Certified: Terraform Associate: Ideal for infrastructure automation, costing $70.50 [12].
Senior-level roles typically require certifications in governance and risk management. Credentials like CISSP and CISM are considered top-tier and demand 120 Continuing Professional Education (CPE) credits every three years [11]. These certifications also open doors to lucrative federal roles, such as ISSO positions with salaries ranging from $87,000 to $140,000, and ISSM roles that can reach $180,000 [13].
| Role Area | Entry-Level | Intermediate-Level | Advanced-Level |
|---|---|---|---|
| Cybersecurity | CompTIA Security+, CEH | CISSP, CISM | CISSP-ISSAP, CISSP-ISSEP |
| Information Tech | CompTIA Network+, CCNA | CASP+, GIAC Certs | CISSP, CCIE Security |
| Risk Management | CAP, CompTIA Security+ | CRISC, CISM | CISSP-ISSMP |
| Systems Development | SSCP, CSSLP | CISSP-ISSEP, Certified DevSecOps Engineer | Advanced Systems Security Certifications |
The DoD 8140 framework also ensures certification reciprocity across military branches, making it easier to transition between agencies like the Army, Navy, and Air Force [13].
Security Clearance Levels Explained
Security clearances are separate from certifications and confirm your eligibility to access classified information. These clearances involve thorough background checks conducted by the Defense Counterintelligence and Security Agency (DCSA), which handles the majority of federal investigations [14].
There are three primary clearance levels:
- Secret Clearance: Requires a Tier 3 background check, typically used for entry-level engineering roles. Processing times range from 60 to 150 days [14].
- Top Secret (TS) Clearance: Involves a more detailed Tier 5 investigation, necessary for sensitive national security systems. Processing takes 120 to 240 days [14].
- TS/SCI Clearance: Grants access to highly sensitive intelligence and often includes a polygraph. Processing can take anywhere from 180 to over 365 days [14].
| Clearance Level | Investigation Tier | 2026 Avg. Processing Time |
|---|---|---|
| Secret | Tier 3 | 60 – 150 days |
| Top Secret | Tier 5 | 120 – 240 days |
| TS/SCI (with Polygraph) | Tier 5 | 180 – 365+ days |
Under the Trusted Workforce 2.0 (TW 2.0) framework, the government has introduced a "clear once, trusted everywhere" model to streamline reciprocity between agencies [14]. Additionally, the outdated e-QIP system has been replaced by eApp, a modern platform for submitting SF‑86 forms with built-in error-checking [14].
Maintaining Certifications and Clearances
Keeping your certifications and clearances active requires ongoing effort. For certifications like CompTIA Security+ (50 CEUs) and CISSP/CISM (120 CPEs), renewal is required every three years [11]. Platforms such as Coursera, Udemy, and DoD-approved training repositories can help you earn these credits over time.
Clearance maintenance has shifted to Continuous Vetting (CV), which replaces the traditional 5- or 10-year periodic reinvestigation process. CV systems automatically monitor financial records, criminal databases, and other sources. Alerts are sent to your security office if any issues arise, often by the next business day [14].
Self-reporting is also mandatory. Events like arrests, significant debt, or notable foreign contacts must be reported immediately to your Facility Security Officer (FSO) [14]. Since financial problems are a leading cause of clearance denial, it’s smart to review your credit report annually and address any issues proactively [14].
If you leave a cleared position, your clearance becomes inactive after 24 months without a new sponsor [14]. Reactivation requires a new investigation, which can delay job opportunities. Additionally, adjudicators are now reviewing digital footprints, such as GitHub activity and professional profiles, for signs of sound judgment and operational security (OPSEC) awareness [14]. If you collaborate on open-source projects, document interactions with international researchers carefully to avoid concerns about "Foreign Influence" [14].
It’s also important to note that marijuana remains federally illegal, even in states where it’s been legalized. Any recent or ongoing use can disqualify you from maintaining a clearance in 2026 [14].
Staying on top of certifications and clearances not only helps you remain compliant but also safeguards your career opportunities in this competitive field.
Career Progression for Cleared DevSecOps Professionals
A career in cleared DevSecOps offers a clear path for growth, with salaries that increase as you gain experience and higher-level clearances. Understanding the typical progression stages can help you set practical goals and plan your journey effectively.
Entry-Level Roles and Advancement
Starting out, roles like Junior DevOps Engineer or Security Analyst I typically require at least two years of experience along with a Secret or Top Secret clearance. These positions focus on laying the groundwork with CI/CD pipelines and basic security tools. Salaries for entry-level positions with these clearances range from $93,600 to $118,560 per year.
During your first two to three years, the focus is on technical tasks such as automating deployment processes, implementing basic security measures, and gaining hands-on experience with tools like Kubernetes. Once you demonstrate proficiency with infrastructure-as-code tools like Terraform, moving into mid-level roles becomes a natural next step.
Mid-Level to Senior-Level Positions
As you build on your technical and security expertise, mid-level roles shift toward strategic responsibilities and leadership. Titles at this stage include DevSecOps Engineer, Cloud Security Engineer, or Security Automation Specialist. Salaries vary widely, ranging from $75,850 to $170,000, depending on your clearance level.
In these roles, you’ll take on tasks like designing security architectures, leading automation efforts, and mentoring junior colleagues. Senior roles, on the other hand, often require eight to eleven years of experience and TS/SCI clearances with a polygraph. Positions such as Senior DevSecOps Engineer, Cloud Security Architect, or Security Engineering Manager come with substantial pay increases – specialized architects earn median salaries around $229,000, while senior engineers average $217,000 [18].
At the senior level, responsibilities expand to include strategic planning, cross-department collaboration, and overseeing enterprise-wide security frameworks. With demand for information security analysts projected to grow by 29% between 2024 and 2034 [18], senior-level expertise in DevSecOps will remain highly sought-after.
Lateral Movement and Specializations
Cleared DevSecOps professionals also have the option to pivot laterally into specialized roles, allowing them to expand their skill set while staying relevant in a rapidly changing industry. Common transitions include roles like Site Reliability Engineer (SRE), Application Security (AppSec) Engineer, Compliance Engineer, or emerging fields such as Platform Engineering and AIOps.
Platform Engineering, often seen as the next step in DevOps evolution, involves building internal developer platforms to streamline workflows [17]. AIOps, on the other hand, uses artificial intelligence and machine learning to predict system failures and automate root cause analysis, reducing manual intervention.
"A security strategy that isn’t owned by the engineering teams won’t survive for long and will slowly degrade over time."
– Julien Vehent, Leader of Security Architecture, Mozilla [19]
Transitioning to areas like GitOps, Platform Engineering, or AIOps requires targeted upskilling. For software developers, this might mean gaining operational experience, while IT operations professionals may need to strengthen their coding and security knowledge [15][18]. Adopting a "shift-left" approach – integrating security early in the development process – can also make you invaluable in addressing the growing complexity of cyber threats. With global cyber attacks increasing by 30% in Q2 2024 [16], professionals who can bridge multiple domains will play a critical role in safeguarding systems.
Building a Competitive Profile
Once you’ve mapped out potential career paths, the next step is crafting a standout personal profile. The cleared DevSecOps job market is competitive, and success hinges on demonstrating technical expertise, presenting a polished resume, and effectively showcasing how your past experience aligns with DevSecOps principles. The best candidates combine hands-on skills with a strategic approach to self-presentation.
Hands-On Learning Strategies
Practical experience is key. Start by building a home lab using free tiers from AWS, Azure, or Google Cloud to replicate cleared environments. Work on projects like Cloud Security Posture Audits, IAM policy reviews, and CI/CD pipelines that integrate security tools like SonarQube or Snyk.
For compliance-focused tasks, try automating enforcement with Policy as Code using AWS Config or Azure Policy. Practice secrets management with tools like AWS Secrets Manager or Azure Key Vault to handle encryption and credential rotation. To sharpen your incident response skills, simulate scenarios such as credential compromise or unauthorized access and execute runbooks to address these events. AI chatbots can also serve as virtual mentors, offering step-by-step guidance for setting up environments, installing tools, and applying security controls.
Beyond solo projects, get involved in open-source initiatives, forums, and workshops. These activities not only refine your skills but also keep you updated on emerging industry practices.
Resume Optimization for Cleared Positions
When applying for cleared roles, your resume needs to make an immediate impact. Start by listing your active clearance prominently at the top. For 2026, recruiters are focusing on terms like "Shift Left," "Policy as Code," and "Zero Trust," along with tools like Snyk, Terraform, and Kubernetes. Clearly state your years of experience and use quantifiable achievements to stand out.
"Security is no longer an afterthought. It is the code itself." – ResumeAdapter [20]
Instead of generic phrases, use the PAR method (Problem, Action, Result) to showcase your accomplishments. For example, replace "improved security" with something like: "Configured SonarQube quality gates to automatically block builds with critical vulnerabilities, reducing MTTR by 25%" [20][22]. A technical skills matrix at the top of your resume can help recruiters and applicant tracking systems quickly identify your expertise in programming languages, platforms, and security tools.
While it’s essential to highlight your clearance, avoid sharing sensitive details such as classified project names or specific budgets. Stick to a clean, simple design with standard fonts to ensure your resume is easily processed by electronic systems. It’s worth noting that 55.6% of DevSecOps job ads come from the Finance & Banking sector, followed by Education (21.2%) and Healthcare (13.2%) [22].
"Keep subjective self-descriptions out of your summary section. I’m looking at you, Results-Oriented Team Players." – Bill Branstetter, 9th Way Insignia [21]
Leveraging Transferable Experience
Your background in system administration, networking, and virtualization can be a strong asset for protecting critical systems. Pair these skills with programming languages like Python, Java, C++, or Go, and enhance automation capabilities with shell scripting tools such as Bash, AWK, or sed.
Veterans should emphasize their existing clearances and experience in compliance-driven environments. If you’re transitioning from DevOps, focus on securing Terraform scripts with tools like Checkov or integrating security scanners into Jenkins or GitLab pipelines [20].
A well-rounded profile should also highlight proficiency in vulnerability management (SAST/DAST/SCA), Identity and Access Management (IAM), and compliance frameworks such as NIST 800-53, RMF, and STIGs. Expertise with containerization tools like Docker and Kubernetes, along with runtime security tools like Falco or image scanners such as Trivy, is increasingly sought after. Additionally, cloud security knowledge – using services like AWS GuardDuty or Azure Sentinel – can give you a competitive edge.
As of April 2025, the average salary for a DevSecOps Engineer at the Department of Defense is approximately $139,820, with typical ranges between $124,668 and $156,963 [2]. However, the hiring process can be lengthy. Over 700,000 applicants are currently waiting for federal background checks, and top-level security clearances can take more than 450 days to process. One defense contractor noted losing 20% to 30% of placements because candidates accepted other offers during this period [2].
"A sponsored TS/SCI clearance can be worth tens of thousands in future earning potential." – Alpha Bravo [2]
Navigating the Cleared DevSecOps Job Market
The cleared DevSecOps job market operates under unique conditions compared to the commercial tech sector. Success here depends on understanding what employers prioritize and addressing the challenges specific to these roles.
What Employers Expect
For cleared DevSecOps positions, active security clearances are non-negotiable. This requirement often creates hiring challenges; one defense contractor noted losing 20–30% of placements because candidates accepted other offers while waiting for their clearances to process. Beyond clearances, employers look for expertise in areas like cloud-native security, compliance automation, and adherence to frameworks such as NIST 800-53 and STIGs. They value engineers skilled in embedding security into development workflows while navigating complex regulatory landscapes.
"Successful DevSecOps implementation requires that government users continuously learn new skills." – Nicolas Chaillan, Former Chief Software Officer of the U.S. Air Force
These demands highlight the critical skills and qualifications needed to thrive in this field.
Key Sectors and Employers
The Capital Region, spanning from Baltimore to Richmond, is the epicenter of cleared DevSecOps opportunities. In 2018 alone, more than 115,000 job postings required security clearances. The Department of Defense leads the pack, driven by its shift to cloud-native tools and secure container repositories like the "Iron Bank." Other key employers include defense contractors, intelligence agencies, and organizations managing critical infrastructure.
While government roles may lack the stock options or bonuses common in Silicon Valley, they offer the chance to contribute to national security – a compelling draw for many professionals. These mission-driven roles often provide stability and the opportunity to work on impactful projects [2].
Job Search Strategies for Cleared Professionals
Finding cleared DevSecOps roles requires a targeted approach. Specialized platforms like Cleared Cyber Security Jobs connect candidates with employers who value both clearance and technical expertise. These platforms simplify the process by focusing on direct-hire opportunities.
For veterans, military transition programs can be a game-changer, often bypassing lengthy clearance adjudication processes. If you hold a TS/SCI clearance, treat it as a major asset – it can add tens of thousands of dollars to your earning potential. Highlight it prominently on your resume and LinkedIn profile to stand out.
Networking is equally important. Attend industry conferences, government-sponsored events, and veteran organizations to connect with others in the cleared community. These interactions can provide insights into company cultures and help speed up hiring timelines [2].
Conclusion
The cleared DevSecOps career path brings together technical expertise and the mission of safeguarding national security. It’s a field where demand is high, compensation is competitive, and the work has a direct impact on protecting critical government systems and operations. What was once considered an optional capability has now become essential.
Having an active clearance gives you a clear edge in this space. It not only sets you apart from other professionals but also makes you an in-demand candidate who can contribute immediately. This distinction opens doors and ensures long-term career opportunities.
To thrive in this field, staying ahead of the curve is essential. The technical landscape evolves quickly – think Kubernetes, Infrastructure as Code, Zero Trust Architecture, and automated compliance. Certifications, hands-on experience with top DevSecOps tools, and familiarity with frameworks like NIST 800-53 and STIGs are key to staying relevant. As government agencies shift from traditional waterfall methodologies to agile DevSecOps practices, the demand for professionals skilled in both technical and security aspects will continue to grow[2].
Take stock of your current skills and clearance status. Focus your job search on areas like the Washington, D.C., region, where opportunities are abundant, and use niche platforms to connect with employers who value your unique expertise and clearance[2]. By stepping into this career path now, you position yourself for a role that combines purpose with professional growth.
The work you do in this field matters. National security and the delivery of essential government services depend on secure, efficient software solutions. If you’re ready to take on the challenge of protecting critical systems while advancing your career, the cleared DevSecOps path offers a meaningful and rewarding journey.
FAQs
How do I get sponsored for a clearance?
To get sponsored for a security clearance, you usually need to secure a job with a government agency or a contractor involved in classified projects. Once you’re hired, your employer initiates the clearance process on your behalf. This process includes a thorough background investigation conducted by a government agency, such as the Department of Defense. They review various factors, including your criminal history, financial records, and overall background, to determine your eligibility.
What does DevSecOps look like in a SCIF or air-gapped network?
In a SCIF (Sensitive Compartmented Information Facility) or an air-gapped network, DevSecOps functions differently to accommodate the lack of internet access. The setup typically involves two zones: the Low Side, which manages dependencies, and the High Side, where production occurs. Secure data transfer between these zones is achieved using physical media and specialized hardware like data diodes. To keep workflows running smoothly in these isolated environments, teams rely on local mirrors, offline scanning tools, and stringent controls to ensure everything stays compliant and secure.
Which 2–3 certifications should I get first for cleared DevSecOps?
To build a strong base in security and cloud systems, start with well-regarded certifications. For security, consider CISSP (Certified Information Systems Security Professional), CISM (Certified Information Security Manager), or CEH (Certified Ethical Hacker). In cloud platforms, look into certifications for AWS, Azure, or Google Cloud. Your choice should align with your job requirements and the specific needs of your role within the cleared community.
