Looking to secure a high-paying role in cybersecurity? Application Security Engineers with security clearances are in demand, offering salaries ranging from $149,000 to $220,000 annually. These professionals ensure software is secure during development, aligning with frameworks like OWASP Top 10 and NIST standards.
Key takeaways:
- What they do: Review code, conduct security tests (SAST/DAST), and identify vulnerabilities early.
- Skills needed: Programming (Java, Python, etc.), threat modeling, DevSecOps integration, and cloud security.
- Certifications: Start with Security+ or CEH, then advance to CISSP or CSSLP for leadership roles.
- Clearance perks: Active clearances unlock exclusive jobs, higher pay, and faster hiring.
With cybersecurity roles expected to grow 29% by 2034, now is the time to combine technical expertise with clearance credentials for a thriving career.
How to Become an AppSec Engineer: Skills, Projects, and Reality (No Fluff)
sbb-itb-bf7aa6b
Required Skills and Tools
Becoming proficient in Application Security Engineering within cleared environments requires a mix of programming knowledge, security testing expertise, and a solid understanding of compliance standards. It’s not just about using automated tools – it’s about diving deep into code, architecture, data flow, and APIs to identify vulnerabilities that tools might miss [5]. Below, we’ll explore the technical skills and tools that are essential for this role.
Core Technical Skills
Programming skills are the backbone of this field. Languages like Java, Python, .NET, JavaScript, and C/C++ are commonly used in cleared environments. Mastering at least one or two of these languages is critical, as it sharpens your ability to review and write secure code. This is key for preventing vulnerabilities like SQL injection [3][6].
Understanding how to identify and prioritize threats – such as SQL injection, cross-site scripting (XSS), or buffer overflows – is just as important as filtering out false positives in security scans [3][6]. Threat modeling frameworks like STRIDE or PASTA help map out potential attack vectors early in the development process, making them invaluable tools [3][5].
Security engineers are also expected to integrate security into DevSecOps workflows. This means automating security checks within CI/CD pipelines using tools like Jenkins, Terraform, and GitHub Actions to ensure secure and efficient deployments [3][6]. Additionally, expertise in cloud and container security is essential, particularly for protecting Kubernetes workloads on platforms like AWS, Azure, and GCP [3][6].
In cleared environments, compliance is non-negotiable. Engineers must align applications with frameworks like the OWASP Top 10, NIST standards, SANS Top 25, and CWE Top 25 [1][3][6]. Beyond technical skills, strong communication abilities are critical for explaining risks and security measures to both technical teams and management [3].
Application Security Tools
For cleared professionals, knowing the right tools is just as important as having the right skills. A strong toolkit is essential for meeting stringent security requirements. The following tools are must-haves for Application Security Engineers:
- Dynamic Application Security Testing (DAST) and Static Application Security Testing (SAST) tools: These are the cornerstone of application security. For example:
- Burp Suite: A go-to for penetration testing, offering advanced features like its Intruder tool for automated attacks and extensions like AuthMatrix for role-based access control testing [7].
- OWASP ZAP: A free, open-source alternative that integrates smoothly with CI/CD pipelines through its API and HUD overlay.
Lester Obbayi, Cyber Security Consultant, states: "The OWASP ZAP tool can be used during web application development by web developers or by experienced security experts during penetration tests to assess web applications for vulnerabilities." [8]
An Infosec Institute study from March 2018 highlighted OWASP ZAP’s effectiveness, showcasing its ability to detect critical vulnerabilities like XSS and OS Command Injection in real-world scenarios [8].
- Source Code Analysis: Tools like Checkmarx and Fortify are essential for identifying security flaws before deployment, while SonarQube and Snyk specialize in Software Composition Analysis (SCA) to scan for vulnerabilities in dependencies.
- Threat Modeling Platforms: Tools such as the Microsoft Threat Modeling Tool and IriusRisk simplify the process of mapping out potential threats during development.
For those looking to sharpen their skills, resources like the PortSwigger Web Security Academy offer practical training in identifying and exploiting vulnerabilities [5]. Entry-level professionals can start by focusing on scripting and pattern matching to reduce unnecessary noise in security scan results [3].
Certifications That Advance Your Career
Building technical and tool-based expertise is just the beginning. Industry certifications take it a step further, giving you the credentials to validate your skills, meet Department of Defense (DoD) requirements, and increase your earning potential in cleared Application Security roles. These certifications not only confirm your abilities to hiring managers but also fulfill federal mandates and often lead to higher salaries. As the job market in 2025 becomes increasingly competitive, having the right certifications will remain a key factor in career advancement and credibility [13].
The certifications you pursue should align with your career stage and goals. For beginners, entry-level credentials establish foundational knowledge and ensure compliance with federal standards. For seasoned professionals, advanced certifications demonstrate mastery and leadership in secure software development.
Entry-Level Certifications
CompTIA Security+ is widely regarded as the starting point for cleared professionals. It satisfies DoD 8570/8140 baseline requirements, making it essential for federal compliance. The exam costs between $370 and $392, and preparation typically requires 100 to 200 hours of study. Around 24% of the U.S. cybersecurity workforce holds this certification, reflecting its importance [14].
Certified Ethical Hacker (CEH) builds on foundational skills by introducing offensive security concepts and hacking techniques. Although the exam is more expensive – ranging from $1,100 to $1,300 – it is highly recognized by recruiters [13]. Professionals with CEH certifications often earn salaries of around $126,000 annually. However, some hiring managers note that CEH leans more toward theoretical knowledge compared to hands-on alternatives [13].
"In 2025’s tight job market, certifications remain key to credibility, hiring, and salary growth."
- Mohammed Khalil, Cybersecurity Architect, DeepStrike [13]
Once you’ve established a solid foundation, advanced certifications can help you transition into leadership roles.
Senior-Level Certifications
CISSP (Certified Information Security Systems Professional) is the gold standard for senior-level positions in cleared environments. The exam costs $749 and requires five years of paid work experience in at least two of its eight security domains [11][12]. If you don’t yet meet the experience requirement, you can earn an Associate status while working toward full certification. In North America, CISSP holders earn an average of $148,000 annually, with the certification often adding about $25,000 to base salaries.
CSSLP (Certified Secure Software Lifecycle Professional) is tailored specifically for Application Security Engineers. At $599, it focuses on secure software development lifecycle (SDLC) practices, including secure coding, threat modeling, and vulnerability testing [12]. To qualify, you need four years of SDLC experience. This certification is ideal for professionals looking to maintain a hands-on, technical focus. CSSLP holders must also earn 90 Continuing Professional Education (CPE) credits every three years to keep their certification active.
| Certification | Cost | Experience Required | Average Salary | Primary Value |
|---|---|---|---|---|
| Security+ | $370–$392 | 0–1 year | ~$125,000 | Baseline compliance |
| CEH | $1,100–$1,300 | 0–2 years | ~$126,000 | Offensive security fundamentals |
| CSSLP | $599 | 4 years | $150,000–$200,000 | Secure SDLC expertise |
| CISSP | $749 | 5 years | ~$148,000 | Senior leadership credential |
These certifications not only validate your technical expertise but also position you as a strong candidate for government and cleared job opportunities.
"Application security engineering rewards deep technical skill. CISSP adds the breadth that elevates technical experts into strategic leaders in secure software development."
- Elias Ward, Security Specialist [2]
For professionals aiming to work on government contracts, starting with Security+ is a practical move to meet immediate compliance requirements. From there, adding CEH or CSSLP can help you specialize in offensive security or secure development. If you’re looking to transition into senior leadership or security architecture roles, CISSP is the credential that opens doors to six-figure salaries and positions of strategic influence [13][15].
Career Path and Progression
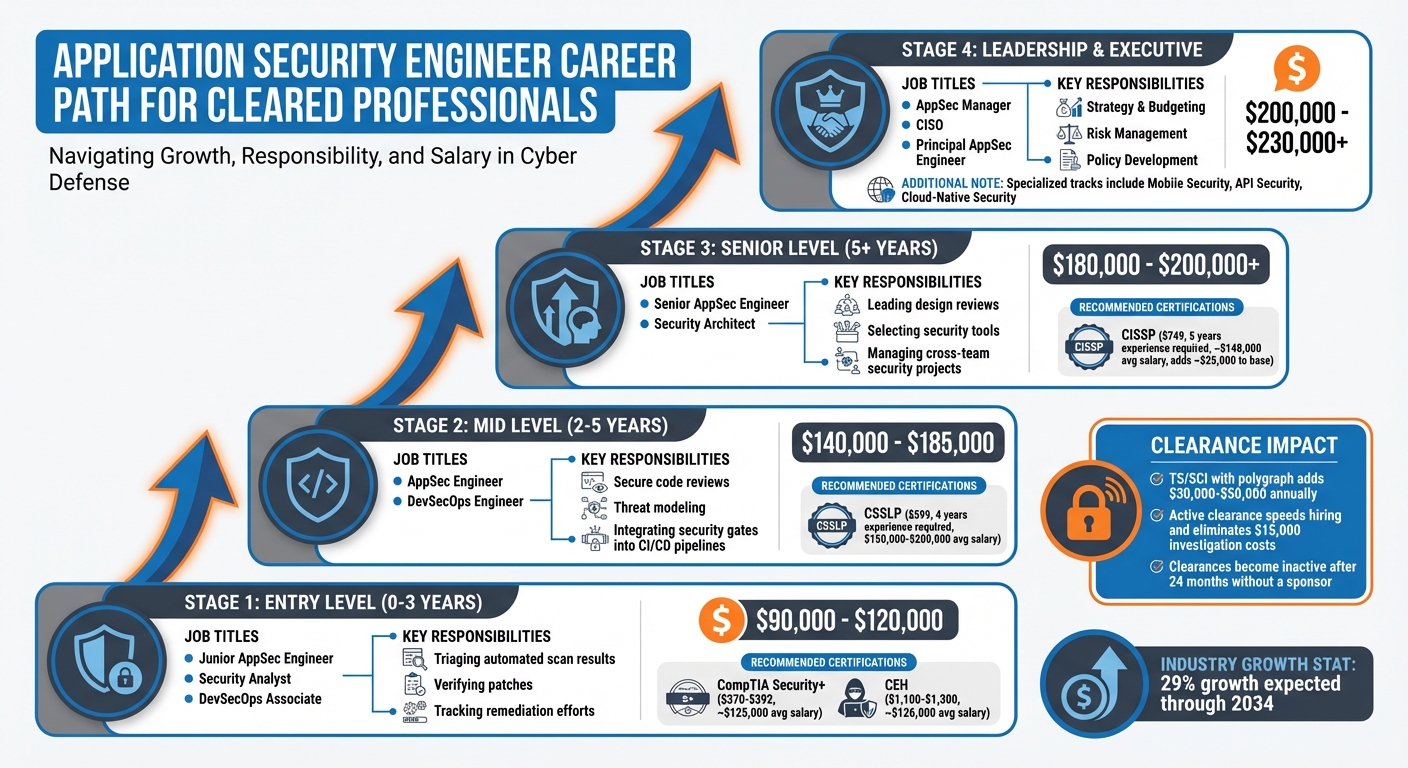
Application Security Engineer Career Path: Stages, Salaries, and Certifications
For Application Security Engineers with active security clearances, career advancement can happen faster and with more opportunities. Understanding the typical career stages and how clearances impact your trajectory can help you make informed decisions about your professional growth.
Typical Career Stages
Entry Level (0–3 years):
Starting out, roles like Junior AppSec Engineer, Security Analyst, or DevSecOps Associate focus on tasks such as triaging automated scan results, verifying patches, and tracking remediation efforts. These positions typically offer salaries between $90,000 and $120,000 annually [3][9]. Early on, it’s essential to hone your skills by automating triage tasks and improving detection rules through investigating recurring scan flags.
Mid Level (2–5 years):
As you gain experience, you might step into roles like AppSec Engineer or DevSecOps Engineer. Here, responsibilities expand to include secure code reviews, threat modeling, and integrating security gates into CI/CD pipelines. Salaries at this stage range from $140,000 to $185,000 annually [3][9][16][10]. This phase involves moving beyond basic scripting to enforcing policies, such as identifying dependencies with known vulnerabilities.
Senior Level (5+ years):
In senior positions, such as Senior AppSec Engineer or Security Architect, your role shifts to leading design reviews, selecting security tools, and managing cross-team security projects. Compensation typically ranges between $180,000 and $200,000 annually [3][9]. At this stage, technical expertise often transitions into strategic responsibilities, paving the way for leadership roles.
Leadership and Executive Tracks:
Advanced positions include specialized roles like Mobile Security, API Security, or Cloud-Native Security (e.g., Kubernetes), as well as leadership roles such as AppSec Manager, Program Owner, Principal AppSec Engineer, or Chief Information Security Officer (CISO). These roles focus on strategy, budgeting, and risk management, with salaries starting at $200,000 and often exceeding $230,000 annually [3][9][10].
"AppSec engineers bridge the gap between development and security teams, ensuring applications are built securely from the ground up."
- Wiz [9]
| Career Stage | Typical Job Titles | Focus Areas | Estimated Salary Range |
|---|---|---|---|
| Entry | Junior AppSec Engineer, Security Analyst | Triage, scanning, patch verification | $90,000–$120,000 [3][9] |
| Mid | AppSec Engineer, DevSecOps Engineer | Threat modeling, code reviews, CI/CD | $140,000–$185,000 [3][9][10] |
| Senior | Senior AppSec Engineer, Security Architect | Strategy, tool selection, mentoring | $180,000–$200,000+ [3][9] |
| Leadership | AppSec Manager, CISO, Principal Engineer | Risk management, budgeting, policy | $200,000–$230,000+ [3][9][10] |
A security clearance not only enhances your skillset but also accelerates your career progression.
How Clearances Affect Your Career
An active security clearance can be a game-changer, significantly speeding up hiring processes and boosting earning potential. Employers value clearances because they eliminate delays and the costs of investigations, which can run up to $15,000 [4][17]. If you already hold an active clearance, you’re often hired more quickly and at higher salaries.
Clearances also bring financial benefits. For instance, holding a TS/SCI clearance with a polygraph can add $30,000–$50,000 annually compared to similar non-cleared roles [17].
"Every month a position sits empty because a clearance investigation is in progress costs the company money. A veteran who walks in the door with an active clearance fills that seat immediately. That urgency is your leverage."
- Brad Tachi, CEO and Founder, Best Military Resume [17]
It’s important to remember that clearances are time-sensitive. If you leave a cleared role, your clearance typically becomes inactive after 24 months. To avoid this, secure a new sponsor within that period [4][17]. The Trusted Workforce 2.0 initiative aims to simplify transitions between federal agencies and contractors with the "clear once, trusted everywhere" approach. Additionally, the Continuous Vetting (CV) system now replaces periodic reinvestigations with real-time monitoring of criminal, financial, and foreign travel records [4].
"Letting a TS/SCI lapse because you took a non-cleared position is one of the most expensive mistakes a transitioning veteran can make."
- Brad Tachi, CEO and Founder, Best Military Resume [17]
By 2026, adjudicators are increasingly assessing public-facing online activities, like GitHub contributions and professional forums, to gauge judgment and operational security awareness [4]. A strong digital presence is becoming just as important as technical expertise for maintaining clearance eligibility.
Balancing skill development with careful clearance management is key to long-term success in Application Security Engineering.
How to Find Cleared Application Security Jobs
Landing a cleared Application Security Engineer role takes more than just submitting resumes – it’s about knowing how to navigate the unique cleared job market. This specialized community operates differently, so leveraging the right platforms and networks is key to finding your next opportunity.
Using Cleared Cyber Security Jobs
The platform Cleared Cyber Security Jobs is a valuable resource for professionals with security clearances seeking Application Security roles. To make the most of it, start by completing your profile thoroughly. Include details like your "Key Skills" and "Ideal Work Locations", as recruiters often review these sections before even looking at your resume [18][20].
Keep your profile active by logging in weekly – this helps boost your visibility in recruiter searches [18][20].
When searching for jobs, use zip codes and mileage ranges instead of city names. For example, searching "St. Louis" instead of "Saint Louis" ensures you don’t miss any listings [18][20]. Also, make sure to list all clearance levels you’re eligible for. If you hold a Top Secret clearance but are open to positions requiring only a Secret clearance, selecting both in your search filters can increase your chances [18][20].
Set up job alerts for terms like "Application Security" paired with your clearance level. This ensures you’re notified as soon as new positions are posted [18]. If you’re conducting a confidential search while employed, take advantage of the platform’s privacy settings to block your current employer from seeing your profile [18][20].
Cleared Cyber Security Jobs also hosts virtual and in-person job fairs, connecting you directly with hiring managers at companies like CACI, Amentum, and Booz Allen Hamilton. These events can be game-changers. G.B., a Technical Project Manager at CACI, highlights their importance:
"For veterans especially, attending Cleared Job Fairs can be critical to a successful career transition" [19].
While optimizing your online presence is important, building personal connections can be just as crucial.
Networking in the Cleared Community
Job boards are helpful, but many cleared positions – especially at senior levels – are filled through referrals. Building trust and a solid reputation within the cleared community can unlock opportunities that never make it to public job postings.
Attend industry events, conferences, and cleared job fairs to meet hiring managers in person. These settings allow you to showcase your expertise and experience in ways a resume can’t. Developing relationships with professionals already working in cleared Application Security roles can also provide insider tips about upcoming openings.
Stay informed with resources like the "Security Cleared Jobs: Who’s Hiring & How" podcast or YouTube channels that focus on cleared career paths. These platforms offer insights into hiring trends, interview strategies, and more [19][21]. Engaging in professional forums can also help you increase your visibility.
Networking is about more than finding a job – it’s about building a reputation that can open doors throughout your career.
Conclusion and Next Steps
Stepping into the world of a cleared Application Security Engineer means embracing a path of constant growth and deliberate career decisions. This role uniquely blends cybersecurity expertise with software development skills. With security-related engineering positions expected to grow by 29% through 2034, the demand is clear. Salaries reflect this need, ranging from $149,000 to $220,000 annually, with senior roles at top tech companies often exceeding $300,000[3][5].
Key Points to Remember
To excel, you must balance two critical mindsets: the "builder" and the "breaker." This means not only knowing how to develop software but also understanding how to identify and exploit vulnerabilities. As one expert from BSG explains:
"The role demands something rare – deep technical understanding of how software is built and how it breaks. Developers already have half of that equation solved." – BSG[5]
Your security clearance adds even more value to your profile, especially as organizations adopt DevSecOps practices and focus on embedding security throughout CI/CD pipelines. With trends like cloud-native security, AI-driven operations, and secure-by-design principles shaping the future, the opportunities in this field are only expanding[3].
What to Do Next
Start by revisiting your certification goals. Begin with foundational credentials like Security+ and work your way up to advanced certifications such as CSSLP or CISSP as you gain experience[3]. Keep your security clearance active to stay competitive.
Enhance your hands-on skills through platforms like PortSwigger Web Security Academy, Hack The Box, or TryHackMe[5]. Take on security code reviews at your workplace or participate in security champion programs to build real-world experience. Update your profile on Cleared Cyber Security Jobs, including your clearance level and preferred job locations, and set up alerts for relevant Application Security roles. Attending cleared job fairs is another excellent way to connect with hiring managers actively seeking talent in this area.
FAQs
Do I need a clearance before applying for AppSec roles?
Having a security clearance isn’t always necessary for Application Security (AppSec) roles, but it can give you an edge. Some positions – especially those in government or defense – specifically require it. If you already hold a clearance, it can strengthen your resume and unlock access to specialized roles within the cleared cybersecurity sector.
Which certification should I get first for cleared AppSec jobs?
The CISSP certification is a great starting point for professionals aiming for cleared Application Security (AppSec) roles. Known for its high regard in the cybersecurity industry, especially in security-cleared positions, it provides a solid base of knowledge and skills. This certification can open doors and set the stage for advancing in the cleared AppSec field.
How can I get hands-on AppSec experience without an AppSec title?
To build practical AppSec skills, dive into secure coding challenges, explore OWASP training programs, and take on self-directed projects. You can also contribute to open-source projects, participate in bug bounty programs, or work on personal security initiatives. Prioritize exercises that focus on OWASP vulnerabilities and tools like OWASP ZAP or Burp Suite. These activities not only sharpen your expertise but also help you create a portfolio that demonstrates your capabilities effectively.
