Looking to build a career as a cleared Information System Security Officer (ISSO)? Here’s what you need to know:
- Role Overview: ISSOs safeguard information systems by managing risks, ensuring compliance with frameworks like NIST and FISMA, and maintaining system security in high-stakes environments like government and defense sectors.
- Salary Outlook: By 2026, median ISSO salaries are projected at $107,500. Entry-level roles start around $84,750, while senior positions can exceed $140,000.
- Key Skills: Technical expertise (e.g., vulnerability scanning, SIEM tools), risk management, and communication are essential. Familiarity with frameworks like RMF and tools like eMASS is critical in cleared environments.
- Education: A bachelor’s degree in fields like Cybersecurity or Information Systems is typically required. Advanced roles may benefit from a master’s degree in Cybersecurity or Information Assurance.
- Certifications: Start with CompTIA Security+ for entry-level roles. As you advance, CISSP is a must-have for senior positions. Certifications align with DoD 8570/8140 standards.
- Clearances: Most roles require at least a Secret clearance, with many demanding TS/SCI. Clearance processing times range from 60–365+ days, depending on the level and polygraph requirements.
- Career Path: Progression typically moves from entry-level roles (SOC Analyst, Junior Security Analyst) to mid-level positions (Security Engineer, ISSO) and leadership roles (Senior ISSO, CISO). Experience, certifications, and specialization are key to advancement.
Takeaway: The ISSO career path combines technical skills, certifications, and clearance requirements to support national security. With strong demand and competitive salaries, it’s a rewarding field for those committed to cybersecurity.
How To Become Information System Security Officer With No Experience
sbb-itb-bf7aa6b
What ISSOs Do in Cleared Environments
In cleared environments, Information System Security Officers (ISSOs) operate under strict federal regulations such as FISMA, RMF, and NIST SP 800-37 [4]. These systems manage classified data tied to national security, so the stakes are high. One of their primary responsibilities is securing and maintaining an Authorization to Operate (ATO) – a formal approval that confirms any residual risk is within acceptable limits after a rigorous assessment process.
"The ISSO plays a pivotal role in bridging technical implementation with organizational risk management."
- Babux, Information System Security Officer [4]
Cleared ISSOs often utilize specialized government tools like eMASS (Enterprise Mission Assurance Support Service) to manage security controls and documentation. Since they frequently work on classified networks like SIPR and JWICS, their roles often require on-site presence. These efforts all tie back to the critical mission of protecting national security.
This sets the foundation for understanding the specific, high-stakes tasks ISSOs handle in these environments.
Core Responsibilities of Cleared ISSOs
ISSOs guide information systems through the Risk Management Framework (RMF) lifecycle, as outlined in NIST SP 800-37 [4]. This process starts with categorizing systems based on boundaries and impact levels – Low, Moderate, or High – using FIPS 199 and NIST 800-60 guidelines. From there, ISSOs customize NIST 800-53 controls to align with the system’s risk level and mission objectives, often recommending alternative measures when needed.
One of their key deliverables is the RMF package, which includes:
- System Security Plan (SSP): Outlines the system’s security requirements and controls.
- Security Assessment Report (SAR): Provides a detailed evaluation of the system’s security posture.
- Plan of Action and Milestones (POA&M): Tracks vulnerabilities, prioritizes fixes, and sets remediation timelines based on risk severity [4].
To minimize security incidents, ISSOs implement proactive measures like quarterly audits and phishing simulations, which have been shown to reduce errors and breaches significantly [5].
After a system is authorized, continuous monitoring becomes a priority. ISSOs oversee patch management, track security alerts, and analyze threat intelligence to ensure the ATO remains valid. Regular vulnerability scans play a big role here, enabling faster threat mitigation – up to 58% quicker when managed effectively [5].
To handle these responsibilities well, ISSOs need to balance technical expertise with strong communication skills.
Required Skills for ISSOs
Thriving as an ISSO in a cleared environment requires both technical know-how and the ability to communicate effectively. On the technical side, familiarity with tools like Nessus (vulnerability scanning), Splunk (SIEM systems), and RSA Archer (GRC platforms) is essential [5]. ISSOs must also interpret scan results, correlate security events, and configure monitoring tools to maintain system integrity.
Risk management is another cornerstone of the role. ISSOs translate technical findings into business-friendly language to brief Authorizing Officials about residual risks [4]. This skill directly impacts policy adoption rates, which can reach 74% when stakeholders are well-informed [5]. They also lead incident response efforts, determining how security events affect the system’s ATO and when to escalate issues to Authorizing Officials.
Familiarity with additional frameworks, like DoD’s CNSSI 1253, enhances an ISSO’s effectiveness in defense-focused roles [4]. With the rise of Zero Trust architecture and AI-driven security tools, modern ISSOs increasingly need experience in cloud security and emerging technologies like Microsoft Copilot to stay ahead in cyber defense [5].
Education Requirements for ISSOs
To become an Information Systems Security Officer (ISSO), a bachelor’s degree is typically required, whether you’re aiming for a role in the private sector or government. The most relevant fields of study include Computer Science, Cybersecurity, Information Systems, Information Technology, and Information Assurance. These programs provide the foundational knowledge needed to understand network protocols, system architecture, and security principles – skills that are crucial for navigating the complex regulations in cleared environments and advancing in an ISSO career.
"A bachelor’s degree in computer science, information technology, cybersecurity, or a related field is typically required to become an Information Systems Security Officer."
- Jobicy [2]
For those pursuing advanced positions, a master’s degree in Cybersecurity or Information Assurance offers specialized training in areas like cryptography, cyber law, and risk management. This advanced knowledge becomes increasingly important as you move from junior-level roles (0–2 years of experience) to senior positions (5+ years) and eventually to leadership roles, such as Chief Information Security Officer, which typically require 8–15 years of experience.
Recommended Degrees for ISSO Roles
Different degree programs prepare ISSOs in unique ways:
- Computer Science: Focuses on technical skills like programming, algorithms, and systems architecture.
- Cybersecurity: Emphasizes security protocols, ethical hacking, risk assessment, and cryptography.
- Information Systems: Combines technology and business processes, covering database management, IT governance, and network protocols.
- Information Assurance: Concentrates on compliance and data protection with coursework in cyber law, security audits, and disaster recovery.
The demand for information security professionals, including ISSOs, is growing. The job outlook for information security analysts is expected to rise by 33% from 2020 to 2030 [6]. In 2024, about 182,800 information security analysts were employed in the U.S., with salaries ranging from $92,160 to $159,600 for the 25th to 75th percentiles [8].
If pursuing a traditional degree isn’t feasible, there are alternative routes to entering the field.
Alternative Paths and Certifications
A four-year degree isn’t the only way to start a career as an ISSO. Options like bootcamps and cyber range exercises provide hands-on, practical training in a shorter timeframe. These programs are especially effective when paired with professional certifications.
Certifications can either complement or, in some cases, substitute for a formal degree. For beginners, CompTIA Security+ is a great starting point to establish core security knowledge during or soon after academic studies. As you gain experience, certifications like the CISSP (Certified Information Systems Security Professional) become essential. Widely regarded as the gold standard for ISSOs, the CISSP certification costs around $599 [7]. If you’re just starting out and lack job experience, the Associate of (ISC)² certification is a good entry-level option.
"If hackers are the real life equivalent of super villains, Information Systems Security Officers serve as the super heroes who protect organizations day and night."
- Abdul Mujeeb, Author [7]
Staying updated is crucial in this field. Continuous learning through online courses, seminars, and independent study is vital as new threats emerge. Topics like zero trust architectures, AI-driven threat detection, and cloud-native security are becoming increasingly relevant. By combining education, certifications, and ongoing learning, you’ll be well-prepared for a structured and rewarding career path in information security.
ISSO Career Progression Path
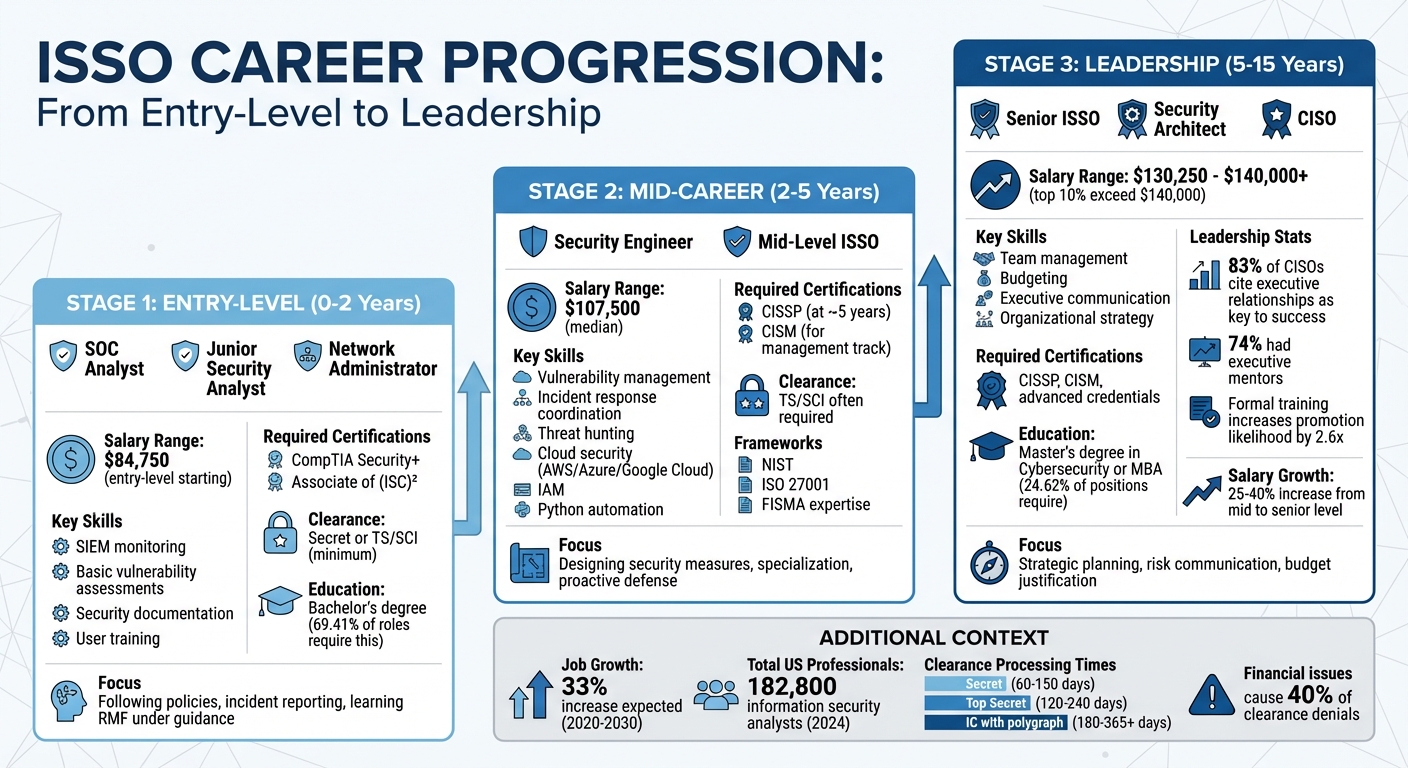
ISSO Career Progression Path from Entry-Level to Leadership
The journey from entry-level roles to senior leadership in the cleared cybersecurity field generally follows a structured path. While the timeline depends on factors like individual performance, certifications, and available opportunities, each step builds on a foundation of rigorous standards and the constant evolution of cybersecurity threats. Knowing the skills and qualifications needed at each stage – and the potential earnings – can help you map out your career effectively.
Entry-Level Positions and Skill Development
Most ISSOs begin their careers in roles like Security Operations Center (SOC) Analyst, Junior Security Analyst, or Network Administrator. These positions focus on tasks like real-time monitoring with SIEM tools, conducting basic vulnerability assessments, maintaining security documentation, and providing user training. During the first 0–2 years, you’ll develop skills in incident detection, user access management, and network protocols, while also learning to create and manage essential documentation.
A Bachelor’s degree in fields like Computer Science, Cybersecurity, or Information Systems is often a baseline requirement – about 69.41% of ISSO roles list this as mandatory [1]. Starting with certifications such as CompTIA Security+ is a great way to validate your core knowledge. If you’re still gaining experience, pursuing the Associate of (ISC)² credential can demonstrate your dedication to the field.
In the cleared market, even entry-level roles typically require at least a Secret clearance, with many positions demanding TS/SCI clearance. At this stage, you’ll focus on following established policies, reporting security incidents, and gaining hands-on experience with the Risk Management Framework (RMF) under the guidance of senior professionals. Once you’ve built a solid foundation, the focus shifts to proactive defense and specialization in your mid-career phase.
Mid-Career Growth and Specialization
With 2–5 years of experience, you’ll move into roles that emphasize designing and implementing security measures. Positions like Security Engineer or mid-level ISSO involve responsibilities such as managing vulnerabilities, coordinating incident responses, and proactively hunting for threats.
At this stage, specialization becomes key. You might focus on areas like cloud security (e.g., AWS, Azure, Google Cloud), Identity and Access Management (IAM), or automation. Learning to use programming languages like Python to automate security processes is increasingly valuable as AI-driven tools become more prevalent [9]. Additionally, gaining expertise in frameworks such as NIST, ISO 27001, and FISMA is critical for ensuring compliance in cleared environments.
Once you reach around five years of experience, pursuing the CISSP (Certified Information Systems Security Professional) certification can significantly enhance your credentials – it’s often considered the gold standard for senior ISSO roles. If you’re leaning toward a management track, certifications like CISM (Certified Information Security Manager) can help establish your leadership capabilities. As your expertise grows, transitioning to leadership roles becomes the logical next step.
Moving into Leadership Roles
After 5–15 years in the field, your focus will likely shift from technical execution to strategic leadership. Positions such as Senior ISSO, Security Architect, or CISO require a blend of technical knowledge and leadership skills. These roles involve responsibilities like team management, delegating tasks, and evaluating performance. Salaries at this level often exceed $130,250, with senior professionals typically seeing salary increases of 25% to 40% [5].
Leadership roles demand a different skill set than technical positions. You’ll need to understand budgeting and finance to justify funding for security initiatives, develop strong communication skills to convey complex risks in business terms, and navigate organizational dynamics to advance security goals. Research indicates that 83% of CISOs consider building relationships with other executives a key factor in their success [10].
"The ability to communicate complex security concepts to non-technical stakeholders is paramount."
- (ISC)² [10]
To stand out for senior roles, consider pursuing a Master’s degree in Cybersecurity or an MBA – 24.62% of ISSO positions require a Master’s degree [1]. Formal leadership training can also make a difference; professionals with such training are 2.6 times more likely to be promoted to senior roles. Mentorship plays a crucial role as well – 74% of successful CISOs had an executive mentor during their career transition [10]. Seeking mentorship early can provide invaluable guidance as you navigate the shift from technical expert to strategic leader.
Certifications and Security Clearances
Required Certifications for ISSOs
The Department of Defense (DoD) defines the qualifications for Information System Security Officers (ISSOs) through its DoD 8570.01-M manual, which is transitioning into the DoD 8140 framework. These guidelines classify roles into Information Assurance Management (IAM) levels. ISSOs typically align with IAM Level I for entry-level tasks, Level II for network-focused responsibilities, and Level III for enterprise-scale management.
For entry-level ISSOs (IAM Level I), CompTIA Security+ is the foundational certification. It needs 50 Continuing Education Units (CEUs) every three years to stay current. For those advancing to IAM Levels II and III, the CISSP (Certified Information Systems Security Professional) becomes a requirement, covering 44% of approved work roles [13]. CISSP holders must earn 120 Continuing Professional Education (CPE) credits for renewal, reflecting its advanced standing.
Another important credential is the ISC2 CGRC (formerly CAP), which is particularly useful for ISSOs focusing on the Risk Management Framework (RMF) and NIST SP 800-53 controls. If you don’t already have the required certification when hired for a DoD position, you typically have up to six months to obtain it [11][12]. Higher-level certifications like CISSP are cumulative, meaning they qualify you for lower IAM levels as well [12].
"DoD 8570/8140 certifications are not ‘nice to have’. For many military, civilian and contractor positions they are mandatory – and they have a direct impact on your salary, job security and future career options."
- CertWizard Editorial Team [16]
Security Clearance Levels and Requirements
In addition to certifications, security clearances are critical for ISSOs working in sensitive environments. While certifications confirm your technical expertise, clearances ensure you’re eligible to access classified national security systems. These clearances are essential for most ISSO roles and come in three main levels: Confidential (potential damage to national security), Secret (serious damage), and Top Secret (grave damage) [14][15]. Many ISSO positions demand Top Secret/Sensitive Compartmented Information (TS/SCI) clearance, especially in intelligence or advanced military technology sectors.
Clearance applications require sponsorship from a federal agency or a cleared contractor after receiving a conditional job offer [14][3]. Applicants use the eApp platform – set to replace e-QIP in 2026 – to complete the SF-86 questionnaire. You’ll need a detailed 10-year record of your residences, employment, and foreign contacts [3].
The timeline for clearance processing varies. As of 2026, Secret clearances take 60–150 days, while Top Secret clearances can take 120–240 days. For roles in the Intelligence Community that require a polygraph, the process may extend to 180–365+ days [3]. Financial issues, such as credit delinquencies or tax liens, account for about 40% of clearance denials, so addressing these issues beforehand is critical [14].
To maintain clearances, Trusted Workforce 2.0 now uses Continuous Vetting (CV). This automated system monitors your criminal, financial, and travel records in real time throughout the clearance period [3]. You’re required to report significant events – like arrests, major debts, or new foreign contacts – immediately, as CV systems flag these events within days [3]. Investigators also review public social media activity to assess judgment and operational security awareness, so it’s wise to regularly check your privacy settings and online activity [3].
Finding ISSO Jobs in the Cleared Market
Job Search Methods for Cleared ISSOs
If you’re looking for a cleared ISSO role, you’ll need more than just technical know-how. The cleared cybersecurity job market has its own unique dynamics, and understanding them can give you a real edge.
For starters, most ISSO positions require an active security clearance, making traditional job boards less effective. Instead, specialized platforms like Cleared Cyber Security Jobs connect candidates directly with employers who are hiring for these roles. When searching, focus on your clearance level and set up alerts with keywords like “ISSO,” “Information System Security Officer,” “RMF,” or “NIST 800-53” so you can act quickly when new openings appear.
Networking is another powerful tool. Many ISSO roles never make it to public job boards. With demand for ISSOs expected to grow by 12% – a rate much higher than the average job market [2] – building connections can help you access opportunities before they’re widely advertised. Industry events like the RSA Conference, Black Hat, or local ISSA chapter meetups are great places to meet hiring managers. You can also leverage internal networking within your current organization for promotions or referrals. And don’t underestimate the value of participating in cybersecurity forums. Engaging in discussions not only boosts your visibility but can also lead to early leads on job openings [2].
Once you’ve found a role that interests you, the next step is crafting a standout application.
How to Apply for Cleared ISSO Positions
Your application needs to do more than just list your skills – it should showcase your impact. Start with your resume. Highlight measurable achievements and certifications right at the top. Be specific. For instance, instead of saying you "improved security posture", you could write, “Reduced unauthorized access incidents by 70% through implementing multi-factor authentication.” Similarly, rather than stating you "managed incident response", say, “Restored critical services within two days following an incident.” These details make your contributions tangible [2].
Certifications are key for cleared ISSO roles. For senior positions, the CISSP is highly regarded, while CISM is often preferred for management-focused roles [2]. If you’re targeting DoD contractor positions, mention your IAT level qualifications, as many applicant tracking systems filter resumes using these keywords.
Another way to stand out is by assembling a portfolio of anonymized work samples. Include documents like security audit reports, risk assessments, incident response plans, or POA&M documentation. These examples provide real proof of your technical skills and problem-solving abilities, which can be especially helpful if you’re newer to the field.
Tailoring your cover letter is just as important. Highlight your experience with the frameworks mentioned in the job description. For example, if the employer emphasizes RMF (NIST 800-37), FISMA compliance, or Zero Trust architecture, share specific examples of your hands-on work with these frameworks. If cloud expertise is required, mention platforms you’ve worked with, like AWS, Azure, or Google Cloud.
Finally, emphasize your ability to make critical decisions, communicate technical risks clearly, and handle classified data with the highest ethical standards. These qualities, combined with a strategic approach to your application, can set you up for success in advancing your cleared ISSO career [2].
Conclusion
Start with a solid academic background – a bachelor’s degree in computer science, cybersecurity, or information technology. From there, aim for industry-recognized certifications like CompTIA Security+ for entry-level roles and CISSP or CISM for more advanced positions[2]. In the U.S., the median annual salary for an ISSO is $107,500, with senior roles climbing to $130,250 or higher. The top 10% of earners exceed $140,000 annually[2].
To stay ahead in the field, focus on mastering the Risk Management Framework (RMF), obtaining DoD 8570-approved certifications to meet IAT standards, and building expertise in areas like Zero Trust architecture, AI-driven security intelligence, and cloud-native environments[2]. Keeping your security clearance active through Continuous Vetting involves practicing strong digital hygiene and promptly reporting major life events to your Security Officer[3].
"The security clearance process in 2026 is defined by its dual nature: more digital and automated, yet still fundamentally human in its judgment of character." – Kevin James, Cybersecurity Professional and Writer[3]
FAQs
How do I get my first ISSO job if I don’t have RMF experience yet?
To break into your first ISSO role without direct RMF experience, start by strengthening your core cybersecurity skills. Earning certifications like Security+ or CISSP can showcase your knowledge, while obtaining a security clearance is often a key requirement for these positions. Familiarize yourself with NIST frameworks and commonly used security tools to build relevant expertise.
If you have experience in areas like vulnerability management or system administration, emphasize those transferable skills on your resume. These roles often overlap with ISSO responsibilities and can demonstrate your readiness to step into a security-focused position.
Finally, networking is a powerful tool. Connect with professionals in the field and explore junior roles supporting security teams – these can serve as stepping stones toward your ISSO career.
What should I do while waiting for my Secret or TS/SCI clearance to process?
While waiting for your Secret or TS/SCI clearance, use the time wisely to get ready for your role. Update your personal and professional documents to ensure everything is current. Connect with employers who have experience managing clearance transitions – they can offer valuable insights and opportunities. Stay updated on the latest industry requirements to remain competitive.
If you need to keep your skills sharp or maintain an income, look into bridge employment. Options like part-time or contract work can be a great way to stay active in your field while the clearance process is underway. Also, plan ahead – start preparing about 18–20 months before your clearance expires to avoid any last-minute hurdles.
How can I prove ISSO skills on my resume without sharing classified work?
To effectively highlight your ISSO expertise, focus on showcasing core technical skills such as risk management, security frameworks, and compliance. Emphasize your hands-on experience with critical security policies, procedures, and frameworks like NIST SP 800-137 and the Risk Management Framework (RMF). These demonstrate your ability to navigate complex security requirements and ensure system integrity.
Make sure to mention relevant certifications such as CISSP or Security+, as these credentials validate your professional knowledge and commitment to the field. Use specific keywords like vulnerability management, compliance audits, and risk assessment to align your qualifications with job descriptions. This approach not only highlights your technical proficiency but also underscores your ability to address organizational security challenges effectively – without delving into classified details.
