Cleared Application Security (AppSec) engineers are cybersecurity experts who protect classified government systems and data. These professionals require both technical certifications and active security clearances, making their roles distinct from commercial AppSec jobs. Here’s what you need to know:
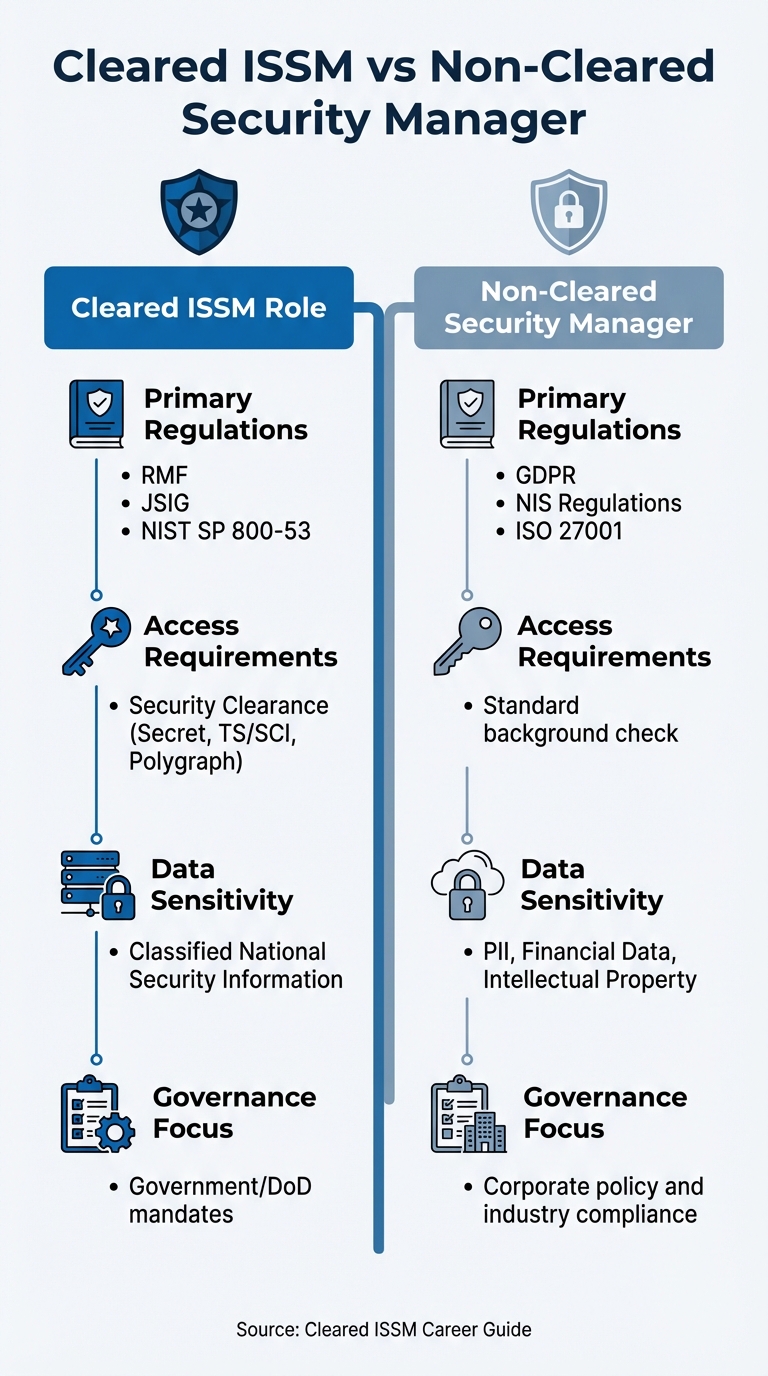
- Key Responsibilities: Implement security tools, configure systems to meet government standards (e.g., DISA STIGs), integrate security into CI/CD pipelines, and ensure compliance with frameworks like NIST SP 800-53 and RMF.
- Security Clearance: U.S. citizenship is mandatory. Most roles require Secret or Top Secret clearance, with some needing TS/SCI. The clearance process involves extensive background checks and continuous vetting.
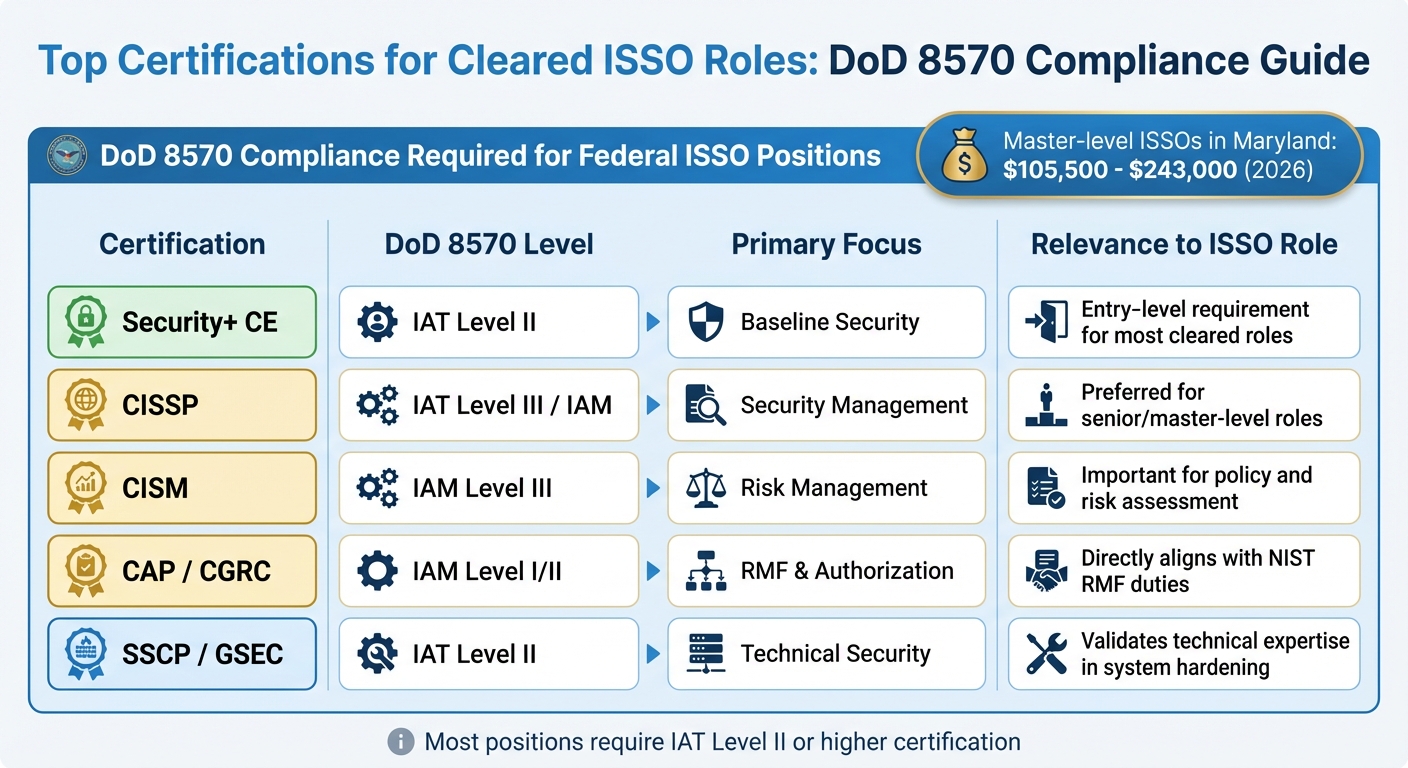
- Certifications: Common certifications include CompTIA Security+, CISSP, CSSLP, and OSCP. These validate technical skills and compliance with DoD 8140 standards.
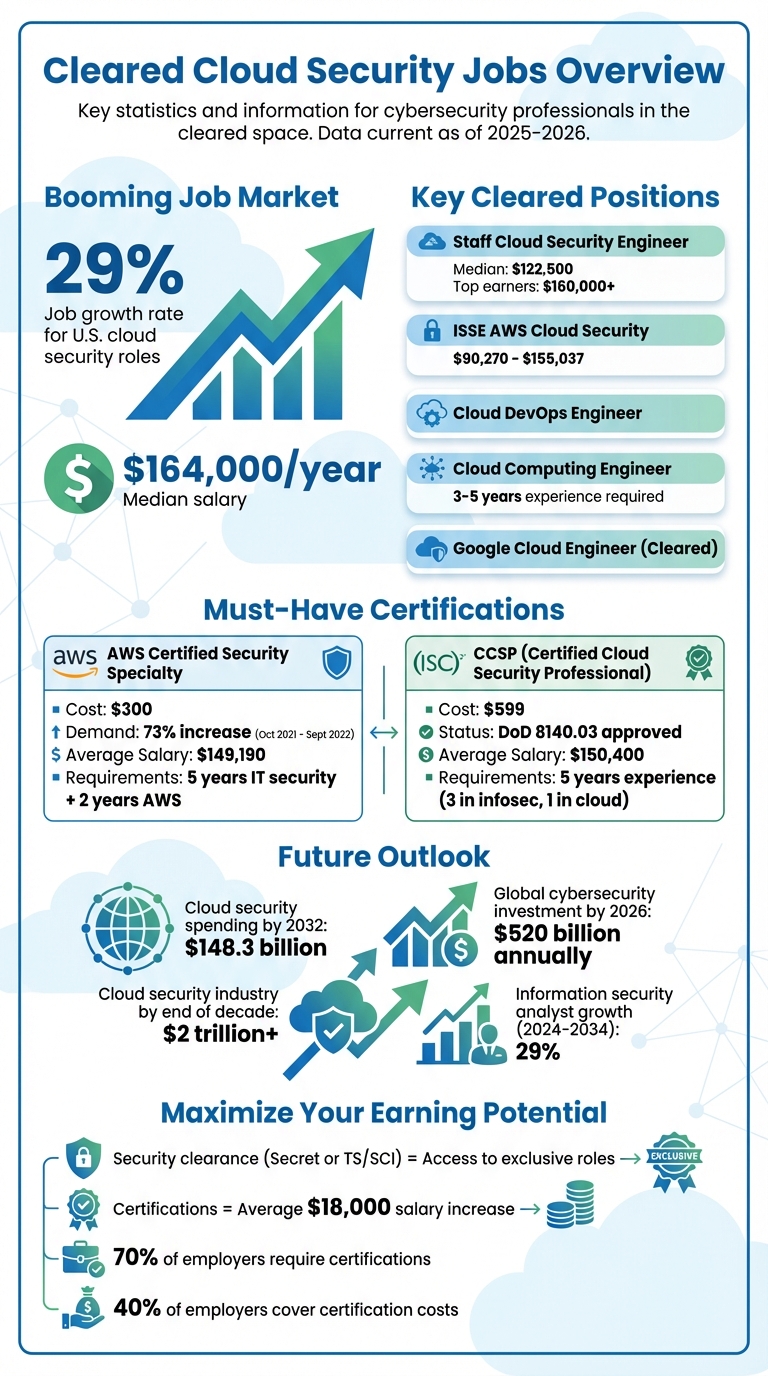
- Salary and Demand: Cleared roles often pay 10%-40% more than non-cleared positions, with salaries ranging from $65,000 for entry-level to $300,000+ for senior roles. Demand is high, with over 514,000 cybersecurity job postings expected by 2026.
- Challenges: Limited remote work opportunities, strict compliance requirements, and the need for ongoing professional development.
This field offers lucrative opportunities for professionals with the right mix of technical expertise, certifications, and clearance credentials.
FASTEST way to become Application Security Engineer and ACTUALLY get a job – UPDATED (2026)
sbb-itb-bf7aa6b
Required Qualifications and Certifications
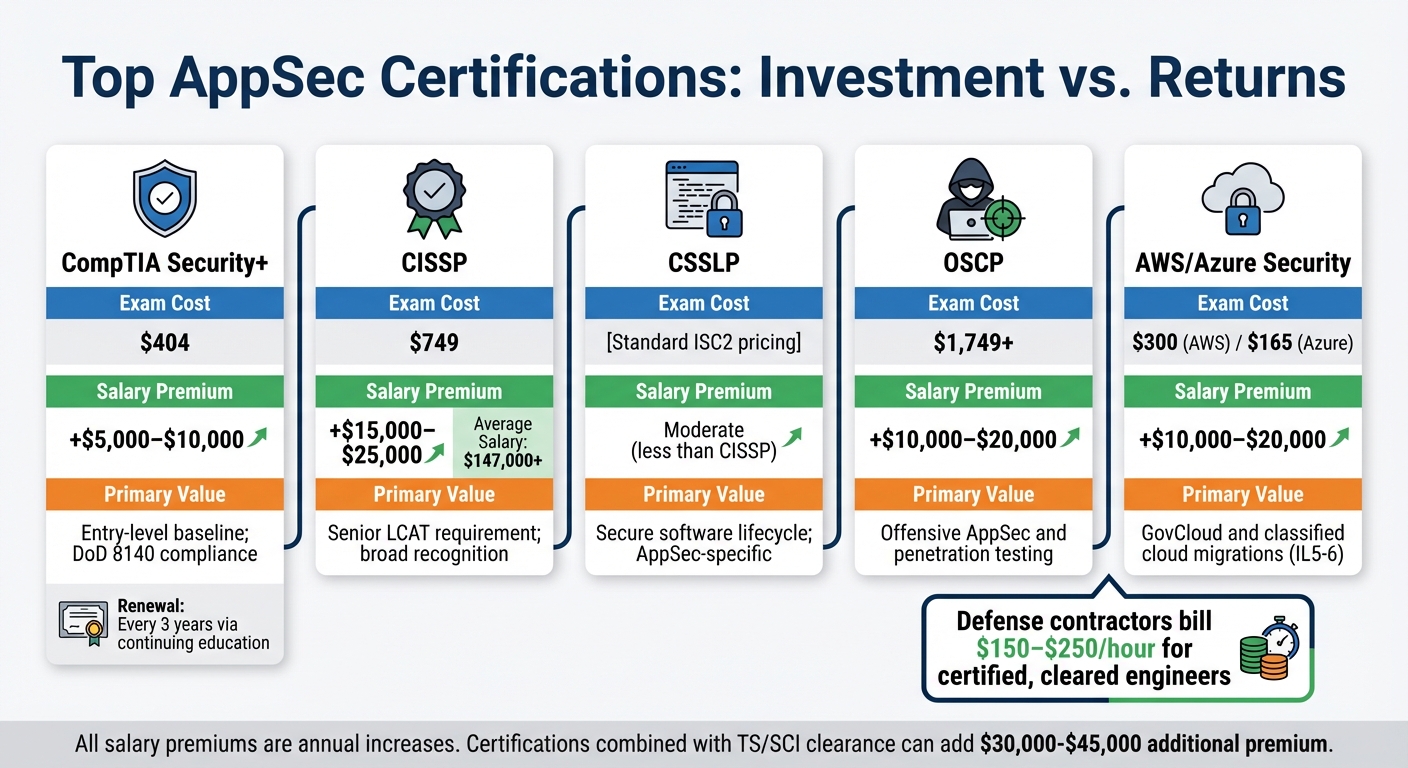
Top AppSec Certifications: Costs, Salary Impact, and Career Value Comparison
Cleared AppSec engineering roles demand a mix of technical expertise, a solid educational background, specific certifications, and an active security clearance [5]. These qualifications are non-negotiable for many government contract positions [5].
Security Clearance Requirements
Security clearance is a cornerstone of any cleared AppSec role [6]. To qualify, U.S. citizenship is a must, as only federal agencies or authorized defense contractors can sponsor your clearance for a designated position [6]. Most cleared AppSec roles require either a Secret (Tier 3) or Top Secret (Tier 5) clearance, with some specialized positions needing Top Secret/Sensitive Compartmented Information (TS/SCI) eligibility [6].
The clearance process varies by level. A Secret clearance typically takes 60 to 150 days, involving checks on employment history, education, and criminal records. For a Top Secret clearance, the timeline extends to 120 to 240 days and includes a Single Scope Background Investigation (SSBI), which digs deeper into finances, foreign contacts, and involves in-person interviews. TS/SCI roles with polygraph requirements can take 180 to 365+ days [6].
Since 2026, the Trusted Workforce 2.0 (TW 2.0) framework has replaced periodic reinvestigations with Continuous Vetting (CV). This system provides automated, real-time monitoring of criminal records, financial activity, and foreign travel throughout your career [6]. To maintain your clearance, you must promptly report any adverse events, such as arrests, significant debt, or new foreign contacts, to your Security Officer [6].
"A U.S. security clearance is a formal, renewable determination made by a federal agency that an individual is eligible for access to classified national security information."
– Kevin James, Cybersecurity Writer [6]
To expedite the clearance process, prepare a detailed 10-year history of your residences, employment, education, and foreign contacts before receiving your eApp link [6].
Top Certifications for AppSec Engineers
Certifications are essential for proving your technical skills and meeting DoD compliance requirements [5]. While a clearance demonstrates trustworthiness, certifications validate your expertise.
- CompTIA Security+: This entry-level certification is a baseline requirement, especially for DoD positions, and can boost your salary by $5,000 to $10,000. The exam costs $404 and requires renewal every three years through continuing education credits [5][7].
- CISSP (Certified Information Systems Security Professional): Ideal for mid-to-senior roles, this certification is highly sought after and can add $15,000 to $25,000 to your salary. The $749 exam focuses on designing and managing comprehensive cybersecurity programs [5].
- CSSLP (Certified Secure Software Lifecycle Professional): Tailored for embedding security into the software development lifecycle, this certification aligns closely with AppSec responsibilities, though it doesn’t offer the same salary boost as CISSP [4].
- OSCP (Offensive Security Certified Professional): This certification is valued for offensive security roles, including penetration testing, with salary premiums ranging from $10,000 to $20,000. The cost starts at $1,749 and includes both coursework and a practical exam [5].
- AWS Security Specialty and Azure AZ-500: As cloud adoption grows, these certifications are becoming increasingly relevant in the cleared sector. They are priced at $300 and $165, respectively, and can add $10,000 to $20,000 to your salary for roles involving GovCloud and IL5-6 environments [5].
| Certification | Exam Cost | Salary Premium | Primary Value |
|---|---|---|---|
| CompTIA Security+ | $404 | +$5,000–$10,000 | Entry-level baseline; DoD 8140 compliance [5] |
| CISSP | $749 | +$15,000–$25,000 | Senior LCAT requirement; broad recognition [5] |
| OSCP | $1,749+ | +$10,000–$20,000 | Offensive AppSec and penetration testing [5] |
| AWS/Azure Security | $300/$165 | +$10,000–$20,000 | GovCloud and classified cloud migrations [5] |
When discussing compensation, it helps to know that defense contractors often bill the government $150 to $250 per hour for certified, cleared engineers. Use this information to negotiate effectively [5].
"The AppSec space has gotten rather crowded with a number of certifications… However, we feel the 2 most commonly recognised and relevant certifications are CSSLP – Certified Secure Software Lifecycle Professional, or CISSP – Certified Information Systems Security Professional."
– Aneesh Bhargav, Head of Content Strategy, AppSecEngineer [4]
In addition to certifications, most roles require a bachelor’s degree in computer science, information technology, or a related field [2]. Advanced degrees or specialized training in cybersecurity and software development can further enhance your qualifications, especially for senior positions. Proficiency in programming languages like Java, C++, Python, and Ruby is also essential for conducting thorough code reviews and navigating development environments [2][4].
Technical Skills and Tools for Cleared AppSec Engineers
Core Technical Skills
Proficiency in programming languages like Python, Java, JavaScript, C++, Ruby, Go, .NET, and C# is essential for AppSec engineers. While mastering every language isn’t necessary, being able to read code and pinpoint vulnerabilities is a critical skill.
Secure coding practices are equally important. Techniques such as input validation, output encoding, error handling, and input sanitization should align with the OWASP Top 10:2025. This updated list prioritizes systemic issues like architectural weaknesses and operational gaps – areas such as Broken Access Control, Security Misconfiguration, and Supply Chain Failures take center stage [8].
Effective vulnerability management goes beyond coding. Engineers must excel in threat modeling, perform both manual and automated security code reviews (using tools like SAST), and conduct thorough post-deployment testing. Familiarity with MVC architecture, microservices, and API security is also key. Moreover, integrating security tools into CI/CD pipelines through DevSecOps practices – using Infrastructure as Code and automation scripts (e.g., Bash, Python) – has become a standard expectation. These practices directly influence the selection and application of specialized security tools.
Tools and Platforms
These technical skills are supported by a range of specialized tools. SAST (Static Application Security Testing) and DAST (Dynamic Application Security Testing) form the foundation of any security toolkit. SAST examines source code for vulnerabilities before deployment, while DAST identifies real-time issues in running applications. For instance, Checkmarx One combines SAST, DAST, Software Composition Analysis (SCA), and Application Security Posture Management (ASPM), reportedly scanning over 800 billion lines of code each month [9].
In high-security environments, tool selection becomes even more critical. Checkmarx supports a variety of deployment models – cloud, on-premises, and hybrid – while SaaS-only solutions like StackHawk may not be suitable for air-gapped or highly secure roles. Engineers should also be familiar with container security tools such as Docker and Kubernetes, along with cloud platforms like AWS GovCloud and Azure Government. Modern DAST tools increasingly emphasize API-first scanning, covering protocols like REST (OpenAPI), GraphQL, SOAP, and gRPC.
"Bringing ASPM context directly into the IDE reflects a forward-looking approach to prioritizing security efforts based on risk earlier in the development process." – Gartner [9]
DevSecOps automation extends beyond traditional scanning. Tools like gitleaks and truffleHog help identify secrets within CI/CD hooks, while platforms like WebGoat and DVWA (Damn Vulnerable Web Application) provide hands-on vulnerability training. Additionally, the rise of AI-assisted development has introduced new challenges, requiring fresh approaches to code review and testing.
Cleared-Specific Technical Requirements
For cleared roles, compliance with federal frameworks is non-negotiable. Adhering to DISA STIG guidelines is mandatory for all DoD-related applications. The Application Security and Development STIG (Version 6, Release 3) outlines 286 findings, categorized into 34 High (Category I), 230 Medium (Category II), and 22 Low (Category III) requirements [10]. Tools like Coverity and HCL AppScan simplify this process by mapping vulnerabilities to DISA STIG requirements, aiding in RMF accreditation.
Engineers must also understand the NIST Secure Software Development Framework (SSDF SP 800-218), which aligns closely with SDLC automation. Key practices include enforcing signed commits, implementing branch protection, and generating Software Bills of Materials (SBOMs) in formats like CycloneDX or SPDX. For container hardening, engineers follow DISA requirements by configuring non-privileged execution in Dockerfiles (via the USER directive), using DoD-approved base images (e.g., Iron Bank), and setting up Kubernetes readiness/liveness probes.
Compliance doesn’t stop there. FedRAMP and FISMA mandate continuous monitoring, requiring pipelines to produce machine-readable evidence in OSCAL format. Additionally, CMMC Level 2 certification involves 110 security practices, with SDLC-relevant controls carrying significant weight. Under DISA standards, critical vulnerabilities must be resolved within 21 days. However, 74% of organizations still face security debt, with unresolved flaws lingering for over a year [11] [12].
"Of all federal compliance frameworks, the SSDF maps most directly to SDLC automation. Its practices read like a specification for what a pipeline enforcement system should do." – Earthly Blog [11]
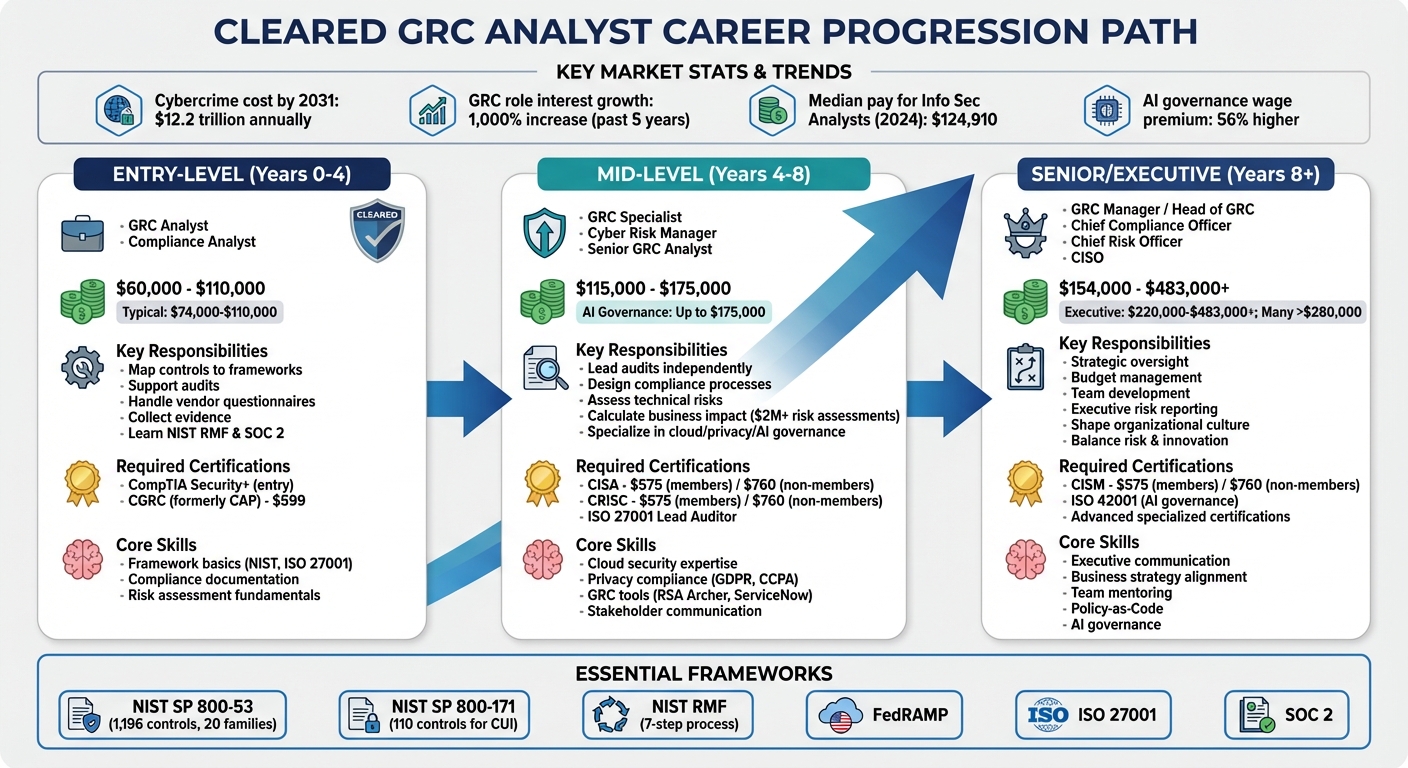
Career Progression and Opportunities
Navigating career growth in cleared Application Security (AppSec) roles is essential for maximizing both your impact and earning potential in the government cybersecurity space. Cleared AppSec careers typically evolve from hands-on technical work to high-level strategic leadership, with greater responsibilities and compensation at each stage.
Career Levels in AppSec Engineering
At the Associate or Junior level (0–3 years), AppSec engineers focus on foundational technical tasks under supervision. This includes running basic static application security testing (SAST) scans, triaging lower-severity vulnerabilities, and assisting with code reviews. Salaries for these entry-level roles generally fall between $65,000 and $100,000[5].
Progressing to the Mid-Level and Senior stages (3–7 years), engineers begin to lead projects independently and gain deeper technical knowledge. Responsibilities expand to include complex threat modeling, driving DevSecOps automation, and mentoring junior team members. Salaries at this level range from $90,000 to $140,000 for mid-level roles and $120,000 to $185,000 for senior positions[5]. Around the five-year mark, professionals with mission-specific expertise see a notable increase in market value.
At the Principal Engineer or Security Architect level (7+ years), the focus shifts to strategic responsibilities like designing secure systems, conducting audits, and advising on organizational best practices. Advanced roles, such as Lead Engineer or Subject Matter Expert (10–15 years), offer compensation between $150,000 and $220,000, while senior leadership positions (15+ years) can exceed $300,000 annually. Notably, the cleared cybersecurity market often pays nearly double the salaries of entry-level commercial roles, with a TS/SCI clearance adding a premium of $30,000 to $45,000 per year[5].
As professionals advance, technical expertise must be paired with leadership skills to unlock higher-level opportunities.
Moving into Leadership Roles
Climbing into leadership positions requires more than just technical know-how. It demands strong communication skills and the ability to align security strategies with broader organizational goals. Leaders must be able to explain risks clearly to non-technical stakeholders while maintaining a strategic focus on enabling secure software development.
"When I look at an Application Security team, it comes down to enabling the engineering of software in a secure manner. This will require the ability to understand development environments, how code is written so you can perform code reviews, how software is built and tested, and how applications are run in a production environment." – Derek Fisher, Vice President of Application Security at Envestnet[4]
Earning a Master’s degree in cybersecurity can fast-track advancement to management or senior architectural roles, where median salaries often surpass $110,000. Certifications like CISSP and CISM also demonstrate readiness for enterprise-level strategy, with CISSP holders reporting average salaries above $147,000. The job outlook remains strong, with Information Security Analysts projected to grow by 29% between 2024 and 2034[1].
While the career path is promising, cleared AppSec professionals encounter unique challenges that can affect their progression.
Career Progression Challenges
Cleared professionals face obstacles that are less common in commercial AppSec roles. For instance, the reliance on Sensitive Compartmented Information Facilities (SCIFs) limits work flexibility, as fully remote cleared roles are rare. Most positions require at least partial physical presence in a SCIF. Additionally, under Continuous Vetting, professionals must promptly report adverse events – such as arrests, significant debt, or foreign contacts – to avoid clearance revocation. Adjudicators are increasingly scrutinizing candidates’ GitHub activity, professional profiles, and even online gaming communities for signs of sound judgment and operational security[6].
Another challenge is over-reliance on automated tools without understanding how to remediate vulnerabilities. This can stall career growth.
"I can tell you with no uncertainty that we can teach the security requirements and tooling far more easily than we can teach coding." – Bruce Parr, AppSec DevSecOps Manager at Paylocity[13]
Finally, compliance with DoD Directive 8140 is critical, as certain certifications are mandatory for specific roles. Failure to meet these certification requirements could result in losing a position[3].
Cleared AppSec professionals must navigate these challenges while continuing to develop both technical and leadership skills to thrive in this demanding yet rewarding field.
Job Search Strategies for Cleared AppSec Engineers
Finding roles in the cleared AppSec field often requires navigating specialized platforms and approaches. Knowing where to look and how to present yourself can make the process smoother and more efficient.
Using Cleared Cyber Security Jobs
Cleared Cyber Security Jobs is a platform tailored for professionals with active security clearances. It’s exclusive to U.S. citizens and connects candidates directly with employers, cutting out staffing agencies. To improve your visibility, keep your profile updated, highlight your skills, and specify preferred locations.
Set up job alerts to stay on top of new postings that match your criteria. When searching, include all clearance levels you qualify for – such as both Top Secret and Secret – to cast a wider net. Use Boolean search terms like "Application Security" OR "AppSec" and search by Zip Code with a mileage radius, as many listings may be tied to military base names rather than cities. Focus on regions with a high concentration of cleared jobs, such as Washington, DC/Northern Virginia, Colorado Springs, San Antonio, and Huntsville. With cybersecurity job postings projected to exceed 514,000 by 2026 – a 12% annual growth rate – and 26% of roles remaining unfilled, there’s significant demand for skilled individuals [14]. Attending both in-person and virtual job fairs can also provide direct access to recruiters.
Once you’ve identified potential opportunities, the next step is crafting a resume tailored to cleared positions.
How to Write a Resume for Cleared Roles
Start by listing your clearance level prominently alongside your contact details – this is a crucial screening factor for employers.
"Your security-cleared resume is not a biography or a mere list of qualifications. It’s an ad designed to help you land that coveted cleared job interview." – Ashley Jones, Blog Editor and Cleared Job Search Expert [15]
Dedicate a section to your AppSec skills and certifications. If a certification is in progress, include the expected completion date. Tailor your resume by incorporating specific keywords from job descriptions, such as "penetration testing", "threat modeling", or "secure coding", to ensure it aligns with Applicant Tracking Systems. Use the STAR method (Situation, Task, Action, Result) to showcase your achievements, and back them up with measurable results.
Keep your resume concise – one to two pages is ideal – and format it simply for easy electronic scanning. Include a brief summary highlighting your technical expertise and years of experience, avoiding subjective language. Never disclose classified project details, colleague names, or sensitive personal information like your Social Security Number. While listing your clearance level is essential for cleared job boards, it’s best to leave it off public platforms like LinkedIn.
Beyond a polished resume, networking is a key component of success in this field.
Networking and Professional Development
Attending cybersecurity events such as BSides, Black Hat, DEF CON, and RSA can help you establish meaningful connections. Often, the most impactful conversations happen casually in hallways or between sessions. Contributing to open-source security projects on GitHub or participating in forums like Reddit’s r/netsec or Stack Overflow can also enhance your visibility and credibility in the community.
Seek out informational interviews with experienced professionals who can offer guidance on navigating the cleared job market. Networking within this niche not only opens doors but also provides insights into government-specific requirements.
Participating in Capture The Flag (CTF) challenges and building home labs can demonstrate your hands-on skills. Volunteering at cybersecurity events or with non-profits can further expand your network and experience. Following major industry players and defense contractors on social media is another way to stay informed about trends and job openings.
Continuous learning is critical in this field. Cleared professionals often earn 20% to 40% more than their peers in commercial roles [14]. For instance, obtaining a CISSP certification can increase your salary by $15,000 to $25,000 annually, while a Full Scope Polygraph clearance might add $45,000 to $65,000 – potentially boosting lifetime earnings by as much as $1.3 million over a 20-year career [14]. After networking events, sending thank-you emails can help maintain those valuable connections.
Conclusion
Breaking into the cleared AppSec field requires a combination of strong software development and cybersecurity expertise to bridge the gap between creating and securing applications. Focus on mastering at least one widely-used programming language, like Python or Java, and gain a solid understanding of the OWASP Top 10 vulnerabilities. Additionally, earning foundational certifications such as CompTIA Security+ will help you meet DoD 8140 standards [14].
The financial incentives for cleared cybersecurity roles are hard to ignore. Professionals with security clearances earn 20%–40% more than their commercial counterparts. Adding a Full Scope Polygraph clearance can boost annual earnings by $45,000–$65,000, potentially translating into $900,000 to $1.3 million over a 20-year career [14]. With over 514,000 job postings expected by 2026 and approximately 26% of positions unfilled, the demand for skilled professionals continues to rise [14].
Your clearance can be a game-changer. Focus on regions like Washington, DC/Northern Virginia, San Antonio, and Huntsville, where high-clearance roles are abundant [14]. Keep in mind that most of these positions require on-site work due to SCIF requirements, though GRC roles might allow for more flexibility.
"Stop collecting certifications. Start applying. I see too many people with 6 certs and no job applications. You need ONE good cert and 100 job applications, not six certs and 10 applications." – Cybersecurity Hiring Manager [14]
Rather than collecting certifications, emphasize developing practical skills. Build home labs, participate in Capture The Flag competitions, and contribute to open-source projects to showcase your hands-on abilities. Stay competitive by maintaining your clearance, aiming for high-clearance roles, and keeping up with advancements in areas like cloud security, zero trust, and AI/ML [14][16].
FAQs
Can I get a clearance without a job offer?
No, you can’t get a security clearance without a job offer. The process requires an employer or organization to sponsor you, as they are responsible for starting and supporting the vetting process.
What should I do while waiting for my clearance to process?
While waiting for your security clearance to process, it might be worth exploring a non-cleared job. Many contracting companies offer such roles because the adjudication process can take quite a while. This period is also an excellent opportunity to build up your skills or earn certifications that are relevant to your field. For instance, diving into areas like secure coding or vulnerability assessment can help you align your expertise with the demands of AppSec engineering and make you stand out for future opportunities.
How do I prove AppSec skills without sharing classified work?
To present your AppSec skills without revealing classified work, emphasize your knowledge of secure coding practices, vulnerability assessments, and certifications such as CISSP or CEH. Tailor your resume to showcase technical strengths and project achievements, but avoid sharing sensitive information. You can also contribute to open-source projects, complete professional training, and earn industry-recognized certifications to prove your expertise while respecting confidentiality.