The journey to becoming a cleared Chief Information Security Officer (CISO) blends technical expertise, leadership skills, and security clearance. This role is critical for safeguarding classified systems in government and defense sectors. Here’s what you need to know:
- Demand and Growth: Cybersecurity roles are expected to grow by 29% from 2024 to 2034, with a significant shortage of professionals, especially at the executive level.
- What Cleared CISOs Do: They secure classified information, comply with federal standards like NIST and DoD directives, and lead cybersecurity strategies for sensitive government operations.
- Security Clearance: A must-have for accessing classified data, with new real-time vetting systems introduced under Trusted Workforce 2.0.
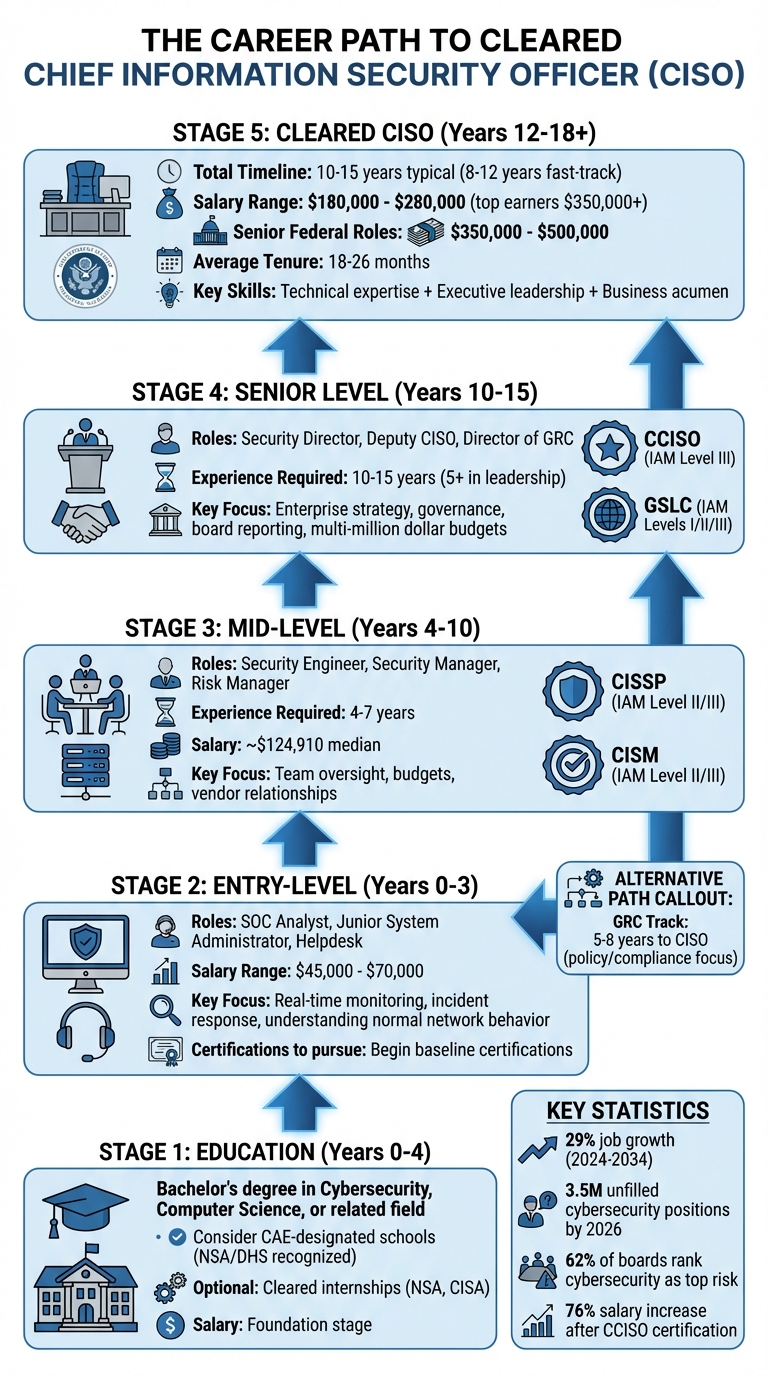
- Education and Experience: A bachelor’s in Cybersecurity or related fields is essential, with advanced degrees (e.g., MS, MBA) being highly valued. The path typically spans 10–15 years, starting from entry-level roles like SOC Analyst or System Administrator.
- Certifications: Key certifications include CISSP, CISM, and CCISO, which are often mandatory under DoD Directive 8140.
- Skills: Mastery of frameworks like NIST 800-171 and Zero Trust principles is crucial, alongside strong communication for translating technical risks into business terms.
This career path offers salaries ranging from $180,000 to $280,000, with top roles exceeding $350,000 annually. Success hinges on a mix of technical knowledge, executive leadership, and continuous learning.
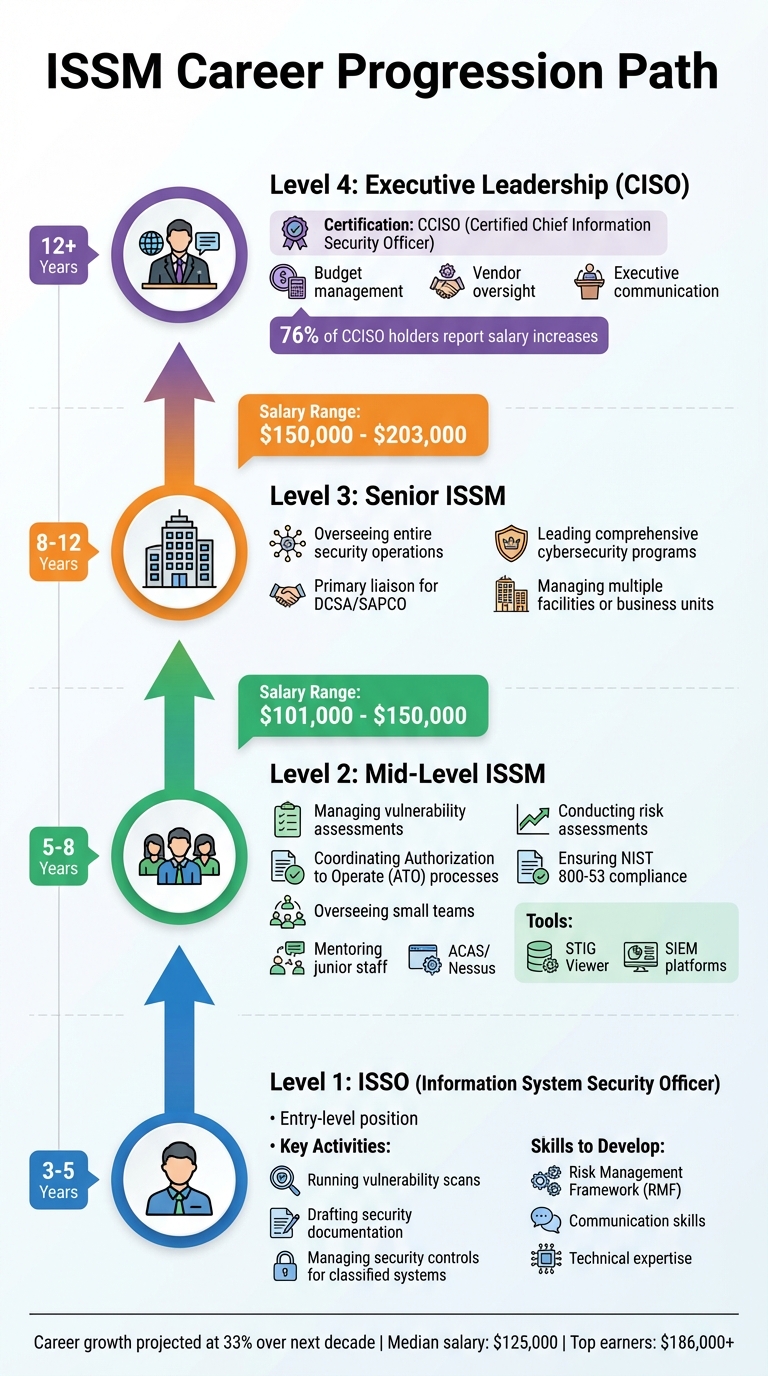
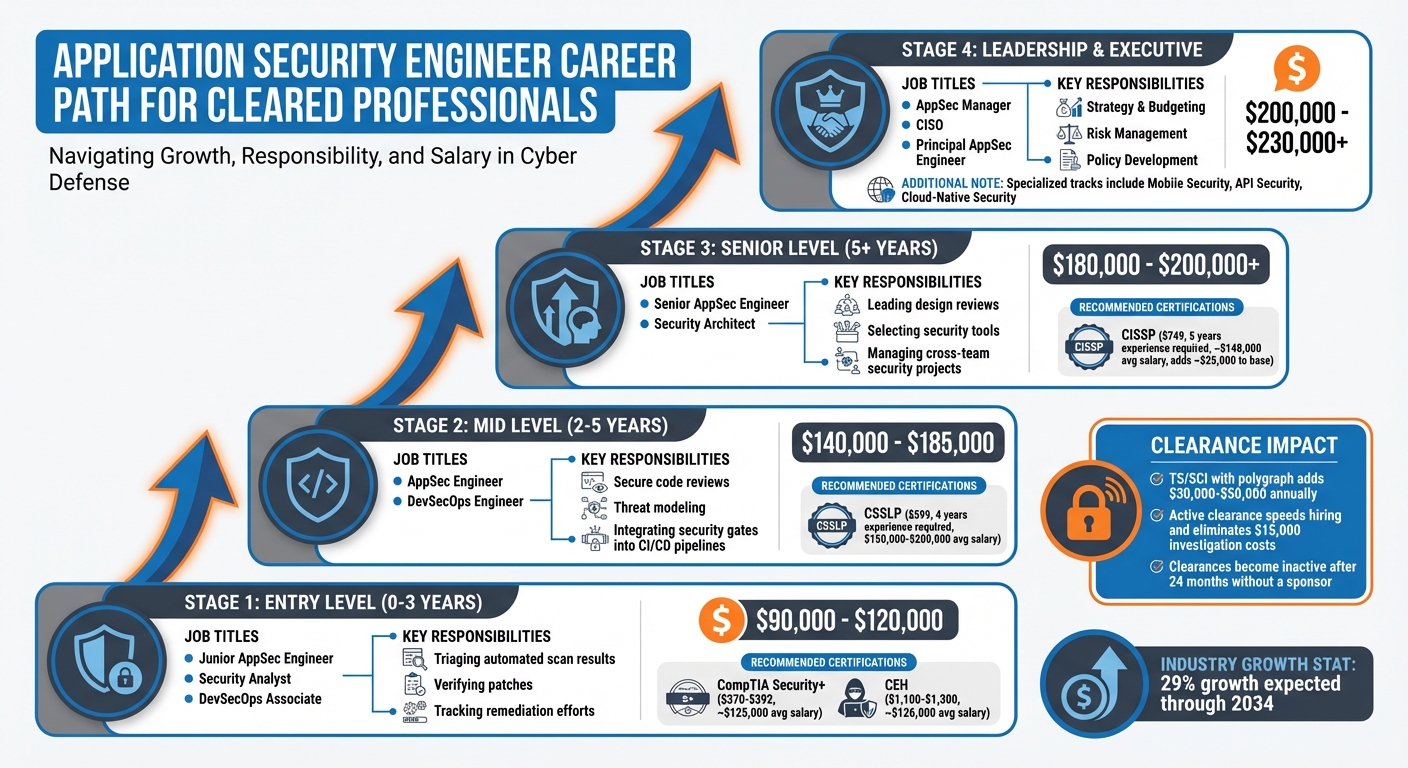
Career Path Timeline to Cleared CISO Position
Education and Early Career Requirements
Degrees and Educational Paths
For most Chief Information Security Officer (CISO) roles, a bachelor’s degree in Cybersecurity, Computer Science, or a related field is the starting point [2][5]. Ideal undergraduate majors include Cybersecurity, IT, Information Assurance, Computer Engineering, or Computer Forensics. If you’re aiming for cleared roles, earning your degree from a school recognized as a Center of Academic Excellence (CAE) in Cyber Defense by the NSA and DHS can give you an edge [5].
Advanced degrees such as an MS in Cybersecurity or an MBA with a focus on Information Security can reduce the amount of experience required and show you’re ready for executive responsibilities [2][4]. With the increasing need for CISOs to bridge the gap between security and business, many boards favor candidates who possess not just technical expertise but also business acumen. This has led to a rise in professionals with MBAs or Business Administration degrees [1][4]. Modern programs now include topics like AI governance, predictive risk modeling, and automated auditing, ensuring leaders are equipped to handle evolving threats [1].
"No amount of formal education could ever replace real-world experience, hard work, and living a life. Education is obviously important, but it is not what separates the good from the great." – Steve Tcherchian, CISO, XYPRO [2]
For those aiming for cleared CISO positions, participating in cleared internship programs at organizations like the NSA or CISA is a smart move. These internships provide hands-on experience while also initiating the clearance process [2]. A solid educational background paired with practical experience is key to launching a cybersecurity career.
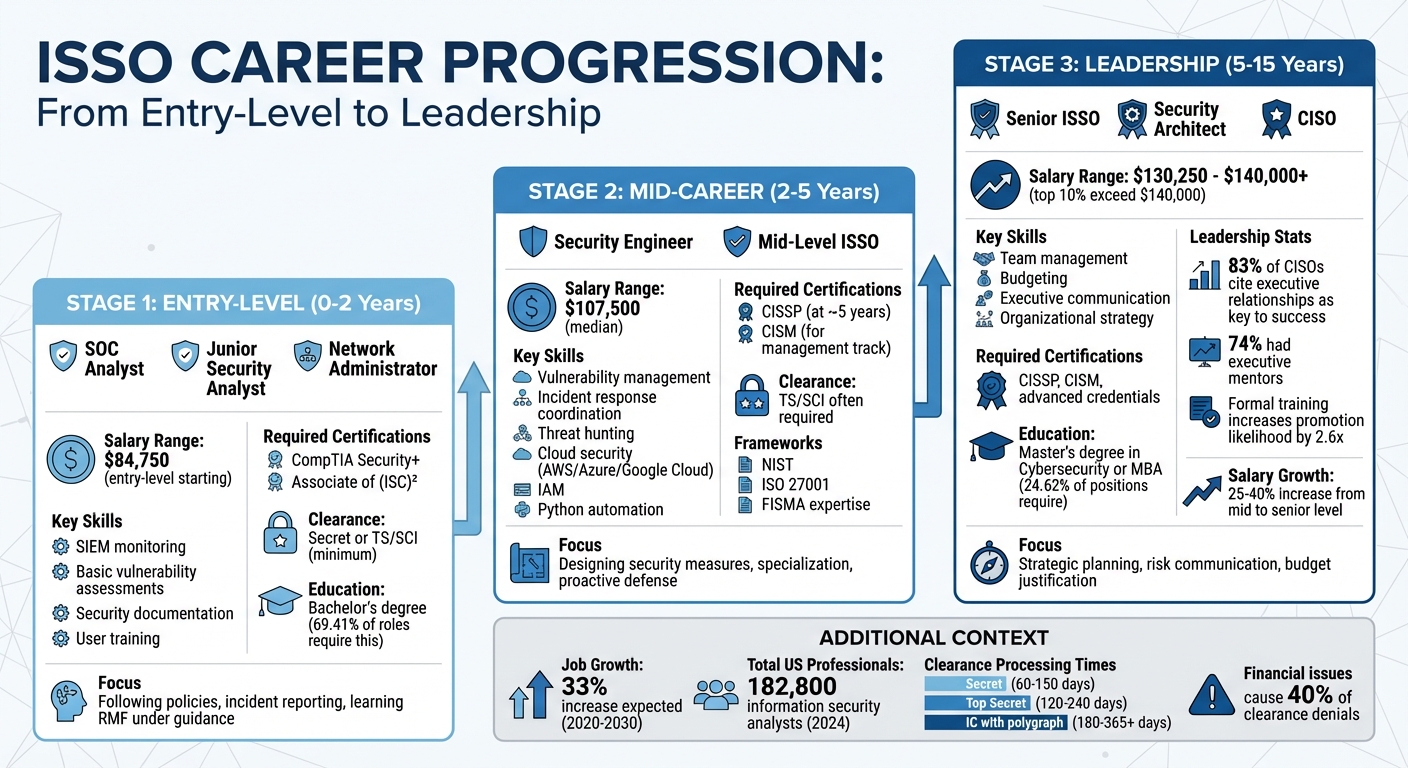
Entry-Level Cybersecurity Roles
Once you’ve got the academic credentials, entry-level roles are where you’ll gain the hands-on experience needed to climb the cybersecurity ladder. Typically, it takes about 12 to 18 years to go from an entry-level analyst to a CISO, although it’s possible to achieve this in 8 to 12 years on a fast track [3]. Salaries for entry-level security analyst positions generally range from $45,000 to $70,000 [3].
Some foundational roles to consider include:
- SOC Analyst: Focuses on real-time monitoring, incident response, and threat intelligence.
- Helpdesk or Service Desk Administrator: Builds troubleshooting skills that can transition into system administration.
- Junior System Administrator: Manages infrastructure, account creation, and system configurations.
- Technical Writer: Creates documentation while gaining exposure to security concepts [6][7][8].
These roles are critical because they help you understand what "normal" network behavior looks like. This knowledge is essential for spotting anomalies that could signal potential threats later in your career [8].
If you’re a veteran with an existing clearance, government contracting roles are a natural fit, as obtaining a clearance as a civilian can be expensive [7]. For those without a clearance, starting in Public Trust positions can pave the way toward full clearance [7]. These early roles not only provide operational knowledge but also lay the groundwork for the strategic thinking required to protect assets and eventually lead at the executive level.
sbb-itb-bf7aa6b
Required Certifications for Cleared CISOs
Top Certifications for Cleared Professionals
If you’re pursuing a cleared Chief Information Security Officer (CISO) role, certifications aren’t just helpful – they’re mandatory. Under DoD Directive 8140, you can’t legally perform cybersecurity or information assurance work on Department of Defense (DoD) contracts without the appropriate certifications [9].
The CISSP (Certified Information Systems Security Professional) is widely regarded as the gold standard for senior-level technical and management roles. It checks the box for IAM Level II/III and IASAE requirements under DoD 8140. Beyond DoD compliance, it aligns with federal standards like FISMA and the NIST Risk Management Framework, making it a top choice for cleared professionals [10]. For those focusing on policy, compliance, and team oversight, the CISM (Certified Information Security Manager) is an excellent fit, particularly for Information Assurance Management roles [14].
At the executive level, the CCISO (Certified Chief Information Security Officer) is designed to prepare professionals for governance, financial oversight, and boardroom communication. The latest CCISO curriculum (v4) even addresses modern challenges like AI-driven governance and predictive budgeting. Training programs for CCISO certification can enhance executive skill sets, and achieving this certification has been shown to increase salaries by an average of 76% [1].
Other certifications worth considering include:
- GSLC (GIAC Security Leadership Certification): Approved for all three IAM levels under DoD 8570/8140, this certification is ideal for leadership roles.
- CISA (Certified Information Systems Auditor): A strong option for professionals focusing on audit and compliance tracks [14].
- CASP+ (now rebranded as SecurityX): Required for architecture and engineering roles within the IASAE category [9].
New hires in cleared positions typically have just 180 days to obtain the required baseline certification, or they risk losing their role [13].
| Certification | Primary Focus | DoD 8140 Level | Experience Required | Renewal Period |
|---|---|---|---|---|
| CISSP | Technical Security & Architecture | IAM Level II/III, IAT Level III | 5 years (in 2 of 8 domains) | 3 years (120 CPEs) |
| CCISO | Executive Leadership & Business Strategy | IAM Level III, Program Manager | 5 years (in 3 of 5 domains) | Annual (US$100 fee) |
| CISM | Information Security Management | IAM Level II/III | 5 years (in CISM domains) | 3 years (120 CPEs) |
| GSLC | Security Leadership | IAM Levels I/II/III | Varies | 4 years (36 CPEs) |
These certifications are stepping stones toward a cleared CISO role. Choosing the right one depends on your career goals and the path you want to take within the cybersecurity landscape.
How to Choose the Right Certification
The certification you pursue should align with both your current role and your long-term career ambitions. If you’re aiming for a cleared CISO position, focus on certifications that meet IAM Level III requirements, such as CISSP, CISM, GSLC, or CCISO. Use the DoD 8570/8140 framework to identify which certifications are required for your desired roles.
"Clearances and certifications serve different purposes: clearances verify trustworthiness to access classified information while certifications verify technical competence."
– Morgan Reyes, Cybersecurity Consultant [10]
If you’re in a technical role and looking to move into architecture, certifications like CISSP or CASP+ can help bridge that gap. For those already in management and preparing for C-suite responsibilities, the CCISO certification is a logical next step, with its focus on finance, strategic planning, and vendor management.
When preparing for demanding certification exams, aim for practice test scores in the 90th percentile before taking the official exam [12]. Keep in mind that some cleared employers may conduct their own technical evaluations, so practical skills are just as important as the certification itself. Additionally, staying on top of continuing education is crucial – both CISSP and CISM require 120 CPEs every three years for renewal [11].
With federal CISO roles, such as those at the GS-15 or SES levels, offering salaries from $150,000 to over $200,000, investing in the right certifications is a smart financial and professional decision [10].
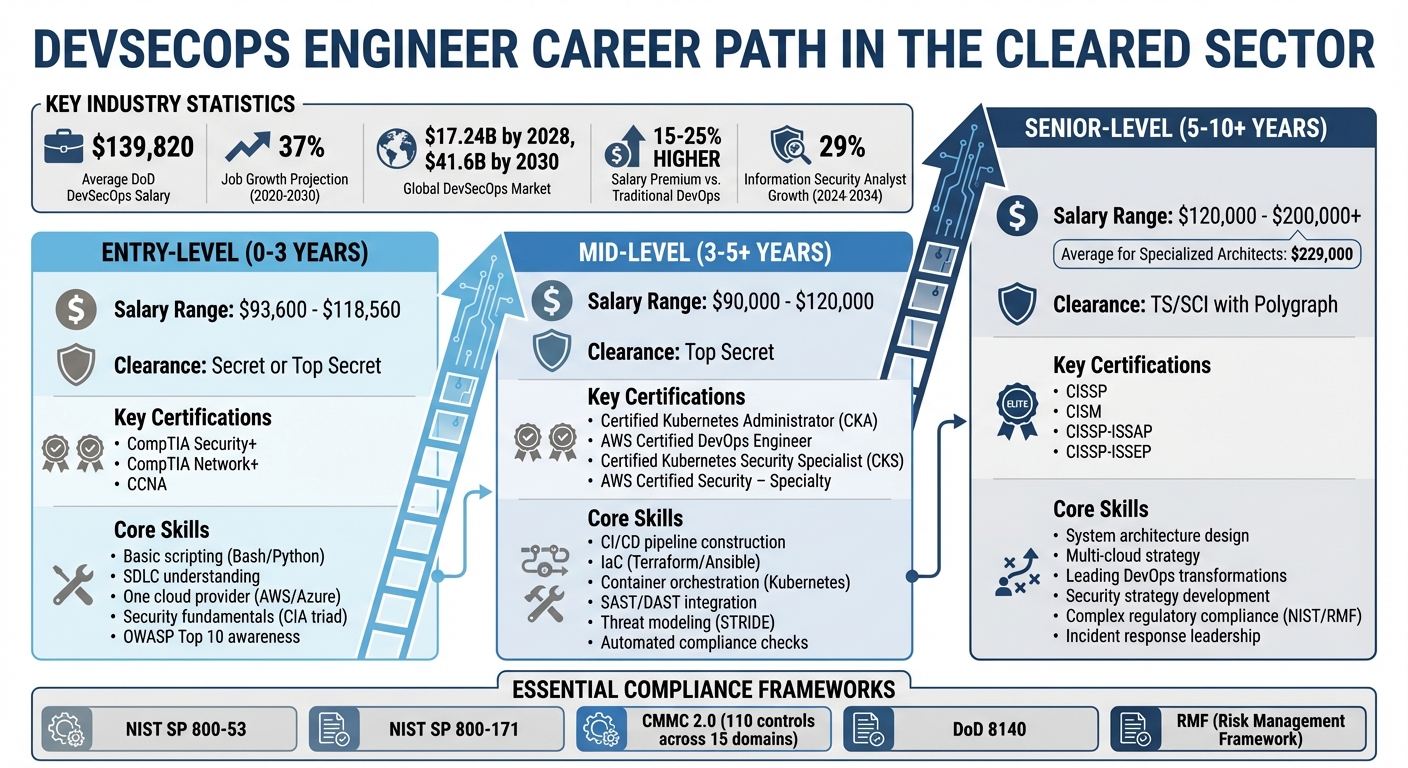
Technical and Leadership Skills Development
Core Technical Skills
For cleared CISOs, mastering frameworks like NIST SP 800-171, NIST SP 800-172, CMMC 2.0 (Levels 1–3), FISMA, and DFARS 252.204-7012 is a must [22,24]. A deep understanding of how to identify and counter Advanced Persistent Threats (APTs) from nation-state actors – including those from China, Russia, Iran, and North Korea – is equally critical.
With the growing emphasis on Zero Trust Architecture, CISOs must focus on strict identity verification, least privilege principles, and micro-segmentation. Advanced Identity and Access Management (IAM) skills, such as implementing MFA, RBAC, and PAM, are essential. Additionally, they oversee 24/7 Security Operations Centers that leverage tools like SIEM, EDR/XDR, and AI-powered threat hunting. These capabilities ensure informed risk management while maintaining compliance and audit readiness.
A practical first step is conducting a gap analysis of the 110 NIST 800-171 controls to prepare for CMMC 2.0 certification. Using User and Entity Behavior Analytics (UEBA) can help detect unusual insider activity tied to APTs. Cleared CISOs are also responsible for managing DFARS’ 72-hour incident reporting requirement and ensuring subcontractors comply with CMMC 2.0. While technical expertise is the foundation, effective leadership ensures security initiatives align with the organization’s business goals.
Leadership and Communication Skills
To complement their technical expertise, cleared CISOs need strong leadership and communication skills to drive cybersecurity strategies at the executive level. The role has shifted from being purely technical to one that requires a strategic, business-focused approach.
"The CISO role has become a pivotal figure in the modern corporate landscape, tasked with providing a strategic vision for the organization’s cybersecurity enterprise" [15].
This shift means CISOs now spend about 35–40% of their time in meetings and managing stakeholders, with another 20–25% dedicated to strategy and planning [17]. The ability to translate technical risks into business language is crucial for success in these settings.
"CISOs act as trusted advisers, using data to help their organization become more agile in the marketplace and make wise business decisions without unnecessary risks" [16].
Frameworks like FAIR (Factor Analysis of Information Risk) help CISOs quantify vulnerabilities in terms of financial impact. With the average data breach costing approximately $4.45 million and global cybercrime expected to hit $10.5 trillion annually by 2025 [15], board members must grasp the monetary risks tied to cybersecurity.
Board simulations are a valuable tool for honing concise communication skills while fostering collaboration with teams like Legal, HR, Finance, and IT. It’s worth noting that 61% of CISOs focus on improving metrics and KPIs to better articulate risks to stakeholders [18]. Scheduling career-oriented one-on-one meetings and implementing mentorship programs can also help retain talent and institutional knowledge.
Additionally, building an executive presence through speaking at conferences like RSA or publishing thought leadership articles can boost a CISO’s visibility within the cybersecurity community. By combining technical expertise with leadership and communication skills, cleared CISOs can effectively bridge the gap between cybersecurity and business strategy – key steps toward a thriving career in this field.
Career Path to Cleared CISO
Mid-Level Roles
Becoming a cleared Chief Information Security Officer (CISO) is a long-term career journey, often taking 12–18 years, though some achieve it in as little as 8–12 years [3]. After starting out in foundational roles like security analyst, professionals gradually transition from technical tasks to overseeing teams, budgets, and vendor relationships.
Security Engineers focus on designing and implementing security measures, prioritizing threat mitigation and system hardening. This role usually requires 4 to 7 years of experience and involves mastering security tools while beginning to think strategically on an enterprise level [9, 12]. On the other hand, Security Managers and Risk Managers take on broader responsibilities, such as managing small teams and coordinating across departments. These roles, typically requiring 7 to 10 years of experience, represent a shift from being an individual contributor to stepping into leadership [9, 31].
Certifications like CISM (Certified Information Security Manager) can help professionals make this leap [19]. With information security analysts earning a median salary of roughly $124,910, these mid-level roles are both rewarding and crucial stepping stones [10, 31]. They prepare individuals for the more strategic and complex challenges of senior leadership.
Senior Roles and Transition to CISO
The final stages before reaching a CISO role often involve senior positions like Security Director or Deputy CISO. These roles typically require 10–15 years of experience, including at least 5 years in leadership, and focus on enterprise-wide strategy, governance, and reporting at the board level [9, 10]. At this stage, professionals are tasked with managing multi-million-dollar budgets, leading cross-departmental incident responses, and crafting long-term security plans [10, 27].
"A Chief Information Security Officer is not just a security expert; they are a business leader responsible for aligning cybersecurity strategy with organizational goals."
- Safwan Azeem, Author, ACSMI [4]
In the U.S., CISOs earn between $180,000 and $280,000 annually, with some top earners surpassing $350,000 [4]. However, the role comes with its challenges, as the average tenure of a CISO is relatively short, ranging from 18 months to 4 years [27, 31].
For those with a background in strategy and compliance, an alternative pathway exists. The GRC (Governance, Risk, and Compliance) track allows professionals to prioritize policy and risk management over technical depth. Roles like Director of GRC or VP of Risk and Security can lead to a CISO position in just 5 to 8 years, provided the individual has strong business acumen [27, 31]. With an estimated 3.5 million unfilled cybersecurity positions projected globally by 2026, cleared professionals who bring together technical expertise, leadership, and business insight are increasingly sought after [12, 31].
The Essential Guide to Becoming a CISO
Using Cleared Job Platforms
These platforms can help transform your technical and leadership skills into real career opportunities.
Using Cleared Cyber Security Jobs Effectively
Cleared Cyber Security Jobs provides tailored features for professionals aiming for roles like Chief Information Security Officer (CISO). Employers initially see key details such as your Key Skills and Ideal Work Locations before viewing your full resume. That makes it crucial to keep your profile complete and up-to-date. Regularly logging in and updating your "last activity" date ensures you remain visible to recruiters.
When searching for positions, select all clearance levels you hold (e.g., if you have TS, also select Secret) to broaden your options. Instead of searching by city names, use zip code radius searches to pinpoint opportunities near military bases or specific facilities. Setting up automated alerts with keywords like CISO or Chief Information Security Officer ensures you’re among the first to know about new listings. Additionally, privacy tools allow you to block specific employers or browse anonymously while still showcasing your skills [20].
"Use ClearedJobs.Net as a research tool to mine data from tens of thousands of jobs and hundreds of cleared facilities employers. Determine which skills are in demand, see what kind of jobs match your experience, and identify hiring trends."
- Ashley Jones, Blog Editor and Cleared Job Search Expert, ClearedJobs.Net [20]
These strategies for using job platforms work hand-in-hand with networking techniques, which are just as important.
Networking and Professional Development
Cleared platforms also open doors to networking through career fairs and educational resources. Attending Cleared Job Fairs can help you secure referrals, which often play a key role in landing a job [23]. Combine these online tools with in-person events like RSA, Black Hat, and BSides. Even casual "HallwayCon" conversations at these events can lead to meaningful connections [21].
After meeting someone at a conference or fair, follow up with a short email to maintain the relationship. You might also consider requesting informational interviews to build rapport long before a position becomes available [21][22].
In addition, many cleared platforms offer career development resources like the Security Cleared Jobs: Who’s Hiring & How podcast, webinars, and guides on topics like salary negotiations and interview prep. These tools can help you stay informed about industry trends and better prepare for your path to a CISO role [23].
Conclusion
Climbing the ladder from technical roles to a strategic CISO position requires a mix of persistence, skill-building, and networking. Achieving a cleared CISO role typically takes 10 to 15 years of progressive experience, blending deep technical expertise with a strong grasp of executive-level strategy. The role has shifted dramatically, evolving from a purely technical focus to one of strategic business leadership. This transformation is underscored by the fact that 62% of boards now rank cybersecurity as their top risk [1]. To succeed, you must bridge the gap between technical vulnerabilities and their business implications – something only 12% of current CISOs have formally developed [1].
While technical skills lay the groundwork, successful CISOs also bolster their qualifications with certifications that demonstrate readiness for executive responsibilities. Start with foundational industry certifications and aim for leadership roles – such as Security Director or Manager – for at least five years before targeting a CISO position [24][4]. Advanced education, like an MBA or executive training, can also be invaluable, especially when learning to present cybersecurity risks in financial terms – a vital skill for boardroom discussions [17].
Given that many CISO roles are filled through executive searches, networking is just as critical as skill-building. Engage with recruiters and current CISOs early, and use platforms like Cleared Cyber Security Jobs to stay visible and informed about hiring trends in the cleared space [17].
The financial rewards reflect the weight of these responsibilities, with senior CISO salaries ranging between $350,000 and $500,000 [17]. Additionally, 76% of professionals report salary increases after earning the CCISO credential [1]. However, the role comes with challenges, including an average tenure of just 18 to 26 months [1]. To stay competitive, focus on continuous learning, whether through professional development, publishing thought leadership articles, or speaking at industry events.
Becoming a cleared CISO is a long-term commitment. By combining technical expertise, business acumen, and executive presence, you can prepare yourself for one of the most impactful roles in cybersecurity. Stay ahead of emerging challenges – like AI-driven threats – and remain intentional about every step of your career path.
FAQs
How do I get a security clearance to pursue a cleared CISO role?
To land a cleared CISO role, you’ll need to secure a security clearance, which can only happen through sponsorship by an employer or a government agency. This isn’t something you can apply for on your own – your sponsor takes the lead in initiating the process.
The clearance process involves a thorough background investigation. This includes a deep dive into your finances, criminal history, and personal conduct. Investigators will conduct interviews, verify the details you provide, and perform extensive background checks. Be prepared for this process to take time – anywhere from several months to a year.
Which certification should I earn first for DoD 8140 cleared jobs?
To kick off your journey, focus on earning a DoD 8140-compliant certification that aligns with your specific role. If you’re aiming for advanced leadership positions, the CISSP is often regarded as a top choice. Additionally, there are several other certifications recognized across the industry that can help you meet the qualifications for cleared DoD roles. The key is to select a certification that fits your career stage and aligns with the job requirements you’re targeting.
What’s the fastest path from technical roles to a cleared CISO?
To quickly step into a cleared CISO role, you’ll need a mix of broad technical expertise, strong leadership abilities, and industry-recognized certifications like CISSP or CISM. Start by working in foundational IT positions, such as a support engineer, to build a solid understanding of systems and networks. From there, transition into security-focused roles like a Security Analyst to gain hands-on experience in protecting systems and managing risks.
As you progress, shift your focus toward management roles. This is where leadership, strategic thinking, and effective communication become essential. Along the way, make it a priority to develop both your technical knowledge and business skills. This combination of expertise will prepare you to take on senior-level responsibilities and excel as a CISO.