Cleared Information System Security Manager (ISSM) roles are critical for protecting classified data in government and defense sectors. These positions focus on managing cybersecurity for sensitive systems, ensuring compliance with federal frameworks like RMF, NIST SP 800-53, and JSIG. Here’s what you need to know:
- Key Responsibilities: Overseeing risk management, incident response, system security governance, and compliance auditing.
- Certifications: CISSP, ISSMP, CISM, and CGRC are highly valued.
- Experience: Employers seek candidates with hands-on expertise in security frameworks, risk assessments, and technical controls.
- Security Clearance: Most roles require TS/SCI clearance, often with polygraph requirements.
- Job Locations: Concentrated in defense hubs like El Segundo, CA; Chantilly, VA; and Fort Belvoir, VA.
Demand for ISSMs is growing, with cybersecurity job growth projected at 33% from 2023 to 2033. Whether you’re starting or advancing in this field, focus on certifications, clearances, and federal compliance knowledge to stand out.
An ISSE, ISSO or ISSM differences in NIST 800 (my current Job) #convocourses #podcast
sbb-itb-bf7aa6b
The ISSM Role in Cleared Environments
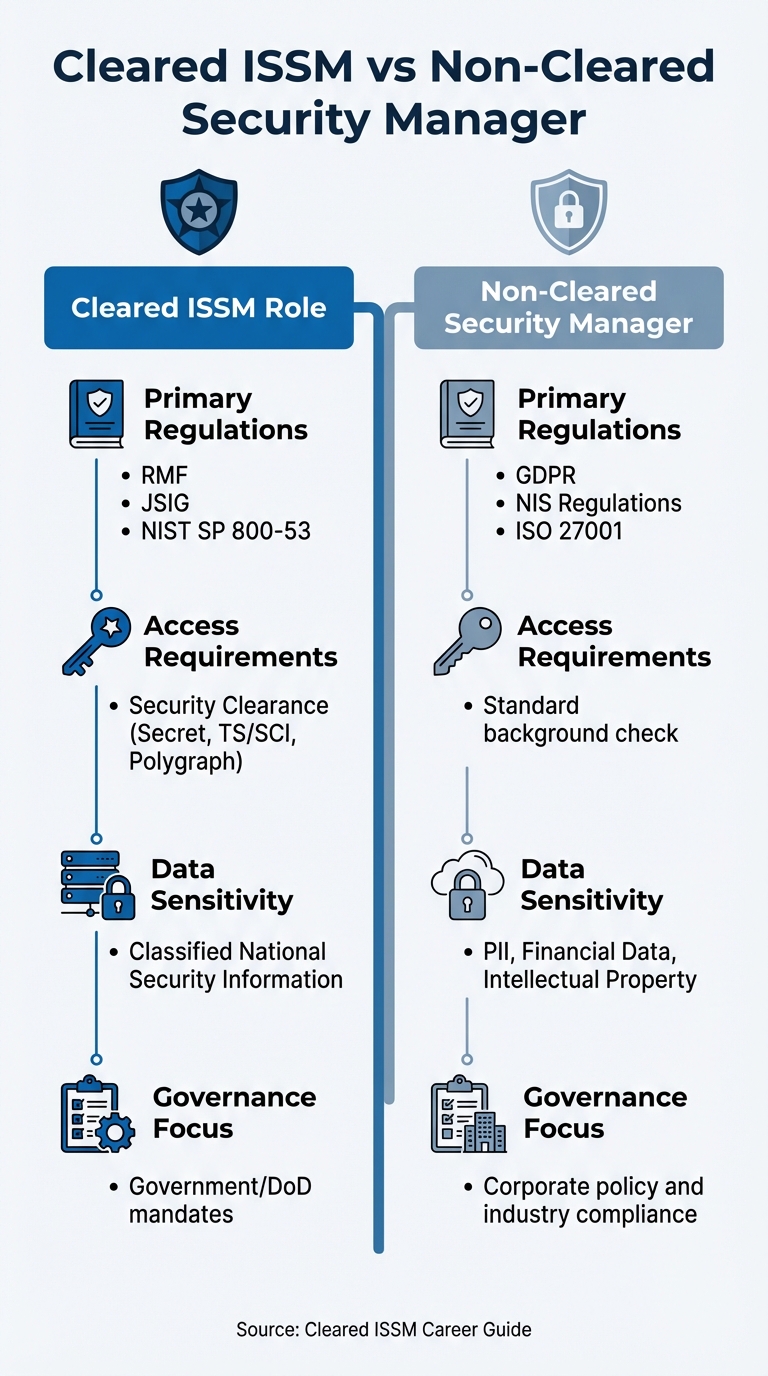
Cleared ISSM vs Non-Cleared Security Manager: Key Differences
A cleared ISSM works specifically with classified national security data, requiring both security clearances and strict adherence to federal regulations. This role is all about managing comprehensive security programs that align with government-mandated frameworks.
The regulatory framework is the backbone of this position. Unlike commercial security managers who focus on standards like GDPR or ISO 27001, cleared ISSMs must ensure compliance with the Risk Management Framework (RMF), Joint Special Access Program (SAP) Implementation Guide (JSIG), and NIST SP 800-53. These frameworks guide how classified systems are secured, accredited, and maintained throughout their lifecycle. This unique regulatory environment shapes the strategic priorities of every cleared ISSM, influencing their daily responsibilities and long-term goals.
Core ISSM Responsibilities
The daily responsibilities of a cleared ISSM align closely with the CISM certification structure, covering four key areas: information security governance, risk management, program development, and incident management[4]. Each of these domains requires a combination of technical know-how and strategic foresight.
- Information security governance: This involves creating frameworks to ensure security strategies meet both government mandates and organizational goals. ISSMs translate complex federal requirements into practical policies that are easy for teams to follow while maintaining operational efficiency[4].
- Risk management: ISSMs conduct ongoing risk assessments to identify and mitigate threats to classified systems. This includes implementing technical controls like multi-factor authentication (MFA), encryption, and digital signatures to reduce risks to acceptable levels[2].
- Program development and management: This spans the entire security lifecycle, from drafting and implementing security policies to managing technical controls across systems. Even minor security gaps can be exploited, so ISSMs continuously update software and apply patches to protect classified systems[2].
- Incident management: This focuses on developing strong response and recovery plans. ISSMs ensure robust incident response capabilities, maintain data backups, and implement disaster recovery strategies. They also provide security awareness training to prepare personnel for emerging threats[2].
Compliance is an ongoing effort. ISSMs perform regular audits to identify and address gaps before they turn into vulnerabilities. They also oversee the Accreditation and Authorization (A&A) process, ensuring systems meet federal standards before handling classified information.
Security Clearance Requirements for ISSMs
Given the complexity of this role, having the right security clearance is essential. Security clearances aren’t just preferred – they’re mandatory. These positions require access to restricted government data and facilities, meaning candidates must hold clearances ranging from Secret to Top Secret/Sensitive Compartmented Information (TS/SCI), sometimes with polygraph requirements[3].
The clearance level directly affects the scope of responsibilities and job opportunities. While a Secret clearance might suffice for some roles, most ISSM positions demand TS/SCI due to the highly classified nature of the systems involved. The more sensitive the information, the more thorough the background investigation. Candidates can expect a multi-step hiring process, including phone interviews, technical assessments, and extensive background checks tailored to the required clearance level[1].
Clearance requirements also influence job locations. ISSM roles are concentrated in defense and technology hubs such as El Segundo, California; Fort Belvoir, Virginia; and Chantilly, Virginia – areas with a strong government and contractor presence[3].
| Feature | Cleared ISSM Role | Non-Cleared Security Manager |
|---|---|---|
| Primary Regulations | RMF, JSIG, NIST SP 800-53 | GDPR, NIS Regulations, ISO 27001 |
| Access Requirements | Security Clearance (Secret, TS/SCI, Polygraph) | Standard background check |
| Data Sensitivity | Classified National Security Information | PII, Financial Data, Intellectual Property |
| Governance Focus | Government/DoD mandates | Corporate policy and industry compliance |
Required Qualifications and Certifications
When hiring for cleared ISSM roles, employers prioritize candidates who bring a mix of proven certifications and practical experience to the table. These positions require not only technical expertise but also a deep understanding of federal security frameworks. Below is a breakdown of the key certifications and qualifications that demonstrate this expertise.
Required Certifications for ISSMs
The Certified Information Systems Security Professional (CISSP) is often considered the gold standard for advanced cybersecurity roles, including ISSM positions[5]. For those aiming to emphasize leadership and management skills, the Information Systems Security Management Professional (ISSMP) certification is a strong fit, aligning with the responsibilities of ISSM roles[5]. Another highly regarded certification is the Certified Information Security Manager (CISM), which focuses on best practices in managing information security programs[6][7]. For ISSMs dealing heavily with regulatory compliance, the Governance, Risk and Compliance (CGRC) certification is particularly valuable[5].
Education and Experience Requirements
Certifications alone don’t complete the picture – formal education and hands-on experience play a crucial role in preparing candidates for ISSM responsibilities. Most employers expect applicants to hold at least a bachelor’s degree in fields like computer science, cybersecurity, or IT systems. A master’s degree in specialized areas such as cybersecurity, cryptology, or network security can provide a competitive edge[6][7]. Some organizations even favor engineering degrees that are accredited by national security agencies[6]. For candidates following alternative pathways, intensive boot camps or professional certificates can also validate technical skills and readiness for the role[7].
Experience is another critical factor. Employers often seek candidates with prior roles in IT, such as systems or database administration, or entry-level security positions, as a foundation for ISSM responsibilities[7]. The role itself spans a spectrum from junior-level positions to expert-level responsibilities, with compensation and duties scaling accordingly[6]. To stand out, candidates should showcase practical experience in risk assessment, threat modeling, and compliance auditing, as well as familiarity with frameworks like NIST SP 800-53 or ISO 27001[7].
The demand for skilled ISSM professionals is on the rise. According to the US Bureau of Labor Statistics, the information security analyst field is projected to grow by 33% between 2023 and 2033, highlighting significant opportunities for career growth in this area[1].
Skills Needed for Cleared ISSM Roles
To thrive as an ISSM in cleared environments, you need a blend of technical expertise and strong interpersonal abilities. It’s not just about knowing the tools and frameworks – it’s about fostering a culture of security while effectively navigating the complexities of cleared cybersecurity roles.
Technical Skills
A solid technical foundation is non-negotiable. This includes:
- Understanding system architecture: You should be well-versed in information systems architecture, programming interfaces (APIs), and managing secure infrastructures.
- Proficiency with security tools: Familiarity with firewalls, authentication servers, antivirus software, and cyber defense platforms is essential.
- Risk management expertise: Identifying and managing cybersecurity risks requires a strong handle on risk assessment methodologies and tools.
- Compliance knowledge: You need to understand standards like ISO 27001 and PCI-DSS, along with relevant data protection regulations. This includes performing vulnerability audits and using intrusion testing tools.
- Crisis preparedness: Designing and testing Business Continuity Plans (BCP) and Disaster Recovery Plans (DRP) ensures systems are resilient during disruptions.
- ISMS principles: Mastery of Information Security Management Systems and the tools that support them is crucial for maintaining security in cleared environments.
Leadership and Communication Skills
Being an ISSM isn’t just about technical know-how. You also need to communicate and lead effectively:
- Simplifying complex concepts: Translating technical jargon into actionable strategies that non-technical staff can grasp is a key part of the job.
- Training and awareness: Conducting security awareness campaigns, distributing charters, and organizing training sessions requires strong teaching abilities.
- Crisis leadership: During incidents, you’ll lead response teams, coordinate with groups like the Computer Security Incident Response Team (CSIRT), and work to minimize the impact while restoring operations.
- Balancing priorities: Diplomacy is critical when negotiating between strict security requirements and business objectives, especially when working with management and stakeholders.
- Team management: Supervising IT teams, setting clear goals, and tracking progress are essential for ensuring projects stay on course.
These combined skills equip you to handle the multifaceted responsibilities of an ISSM in cleared environments, ensuring both system security and operational effectiveness.
How to Find Cleared ISSM Jobs
Landing the right ISSM job takes more than just scrolling through generic job boards. With over four million cleared professionals in a labor market of 170 million people [10], you’re part of a niche group. This means you need focused strategies to connect with employers who understand clearance requirements and value your expertise. Here’s how you can narrow your search and stand out.
Using Job Search Tools
Online tools can be powerful, but only if you use them wisely. Platforms like Cleared Cyber Security Jobs are tailored for professionals with security clearances. Start by completing your profile – recruiters often look at your skills and preferred work locations before even glancing at your resume. A well-rounded profile makes it easier to catch their attention. Use Boolean search techniques (e.g., "ISSM" OR "Information System Security Manager" OR "Cybersecurity Manager") to broaden your search and enclose exact phrases in quotation marks for better precision.
Location plays a bigger role than you might think. Instead of searching by city names, use ZIP Codes and mileage radius to avoid missing opportunities listed under variations like "St. Louis", "Saint Louis", or "Scott AFB." Also, include all clearance levels you’re eligible for – for example, if you have a Top Secret clearance, make sure to include both Secret and Top Secret in your search to access a wider range of openings.
Keep your profile active by logging in regularly. Many platforms prioritize "fresh" accounts in employer search results, so even a quick login weekly or monthly can boost your visibility. Once you’ve fine-tuned your search, set up Job Agents to receive email alerts whenever new positions matching your criteria are posted.
Use ClearedJobs.Net to gather insights from thousands of job postings and employers. Analyze which skills are in demand, identify roles that align with your experience, and spot hiring trends.
Once your online job search is running smoothly, it’s time to expand your efforts by building connections within the industry.
Building Your Professional Network
While online tools are essential, personal connections can be just as important – if not more so – in the cleared community. Networking here often requires a different approach than traditional job hunting. Many ISSM roles take place in Sensitive Compartmented Information Facilities (SCIFs), where personal electronics are banned, making it harder for recruiters to reach passive candidates during the workday [10]. That’s why proactive networking is key.
Upload your resume and complete your profile to access networking features on Cleared Cyber Security Jobs. When you find an interesting job posting or company, reach out directly to the listed recruiters to grow your network. Follow organizations you’re interested in to stay updated on their hiring activities and security requirements. Also, attend Cleared Job Fairs, both in-person and virtual, to connect directly with hiring managers at cleared facilities.
In the security and intelligence fields, credibility and reputation are everything. A complete and professional profile helps establish trust with recruiters. Make sure to check your network inbox regularly for messages from employers, followed companies, or job alerts. If privacy is a concern, you can set your profile to "Anonymous" to hide your name while still showcasing your skills. You can also block your current employer from viewing your profile if needed.
Applying and Interviewing for ISSM Positions
When pursuing ISSM roles, it’s crucial to create a resume that stands out and prepare thoroughly for interviews. In cleared cybersecurity roles, showcasing your clearance and technical expertise is essential both on your resume and during the interview. Keep in mind that about 75% of qualified candidates are filtered out by Applicant Tracking Systems (ATS) [12]. This means your resume needs to be ATS-friendly while also catching the attention of hiring managers. Your interview preparation should focus on the specific frameworks, compliance requirements, and risk management strategies relevant to ISSM positions.
How to Tailor Your Resume
Your security clearance is a major asset. TS/SCI clearances are costly for employers to sponsor, ranging from $3,000 to over $15,000 [14]. Highlight this prominently on your resume. Include your clearance (e.g., Active TS/SCI) in the header and use keywords from the job listing. If you have a polygraph (CI or Full-Scope), specify it, as this can increase your appeal to recruiters.
"I’ve talked to defense contractor recruiters who told me they search their ATS for ‘TS/SCI’ as their first filter before looking at anything else. If your clearance isn’t in a searchable text field on your resume… you’re invisible to these recruiters." – Brad Tachi, CEO, Best Military Resume [14]
Tailor your resume to align with the job description. Highlight your experience with RMF, NIST 800-53, and JSIG. Include a technical skills section that lists tools like Nessus, XACTA, Splunk, and HBSS. Use the STAR method to present your accomplishments, quantifying results where possible (e.g., "Reduced vulnerabilities by 35% through proactive threat monitoring"). Keep your resume concise – ideally one or two pages covering the last decade of your experience.
While emphasizing your clearance, remember to maintain operational security (OPSEC). Avoid mentioning classified project names, mission details, SCI compartments, codewords, or budget specifics. This aligns with the strict OPSEC standards required in cleared roles. Also, list your certifications and include projected completion dates for any in progress.
Once your resume is ready, shift your attention to interview preparation.
Preparing for Technical Interviews
A well-prepared interview performance is key to proving your expertise. ISSM interviews often delve deeply into your knowledge of security frameworks and your ability to apply them in cleared environments. Expect questions on frameworks like NIST SP 800-53, the Cybersecurity Framework, ISO 27001, and CIS Critical Security Controls. You’ll also need to demonstrate a strong understanding of core principles like the CIA triad (Confidentiality, Integrity, Availability) and the principle of least privilege.
Prepare to discuss incident response using the STAR method. Walk through a clear example, from isolating the affected system to conducting root cause analysis. For vulnerability management, be ready to explain your approach, including defining the scope, collecting data, and prioritizing risks based on severity.
"Defense-in-depth is a security strategy that employs multiple layers of protection… if one layer fails or gets compromised, the other layers will continue to provide protection." – InterviewPrep Career Coach [13]
Showcase your policy development skills by explaining a lifecycle approach. This might include conducting risk assessments, collaborating with key stakeholders (e.g., HR, Legal, IT), and implementing continuous monitoring and audit cycles. Be prepared to discuss Business Continuity Plans (BCP) and Disaster Recovery Plans (DRP), including your experience with Business Impact Analysis (BIA) and setting Recovery Time Objectives (RTO). Finally, demonstrate how you balance security with usability by explaining how you address stakeholder resistance. Use examples to show how you employ empathy, active listening, and clear communication to articulate risk-benefit trade-offs effectively.
Career Growth as a Cleared ISSM
Once you’ve secured a role as an ISSM, the next step is to focus on advancing your career. The cleared cybersecurity field moves fast, so staying competitive requires intentional effort. Your security clearance is a key asset – Top Secret clearances, for instance, need to be reinvestigated every five years [9] – so maintaining your eligibility is crucial. Ongoing learning and skill development are essential for climbing the ladder into senior leadership positions, such as Cybersecurity Director or Chief Information Officer. By committing to professional growth, you can build on your current skills and adapt to the ever-changing industry landscape.
Keeping Up with Industry Standards
Cybersecurity frameworks are constantly evolving, which means staying updated is non-negotiable. Take the example of NIST 800-53 Revision 5, which now outlines 1,196 security and privacy controls split across 20 families. For organizations implementing the Moderate baseline, which includes 287 controls, initial implementation can take up to 24 months or more [15].
To stay ahead, establish a continuous monitoring program as part of the Risk Management Framework (RMF). This involves regularly assessing the effectiveness of controls through activities like vulnerability scanning and tracking configuration changes [15]. Keeping an eye on regulatory and technological changes is equally important, as it allows for timely updates to security policies [6]. Following the RMF’s seven steps – Prepare, Categorize, Select, Implement, Assess, Authorize, and Monitor – can streamline your approach. Additionally, using Governance, Risk, and Compliance (GRC) platforms can help automate documentation and tracking, saving time and reducing errors.
Pursuing Additional Certifications and Training
To accelerate your career progression, consider pursuing advanced certifications and specialized training. Certifications like CISSP, CISM, and CISA are highly regarded and can open doors to leadership roles [11].
"Your CISSP Certification is highly valued by both Agencies and Contract Companies" [11].
Beyond these, certifications in areas like ISO 27001 for information security management or CEH (Certified Ethical Hacker) can broaden your technical expertise [6]. Training in platforms such as AWS GovCloud and Microsoft Azure Government is also highly useful for managing accredited systems. Additionally, skills in Cyber Threat Intelligence and Network Defense Forensics can set you apart, especially for roles requiring expertise in securing classified networks like SIPRNet. For veterans, leveraging military credentials can further strengthen federal job applications [11].
Mentoring junior professionals is another effective way to grow. By guiding less experienced team members, you not only help develop new talent but also enhance your own leadership skills. This includes honing soft skills like communication and diplomacy, which are critical as you transition into roles involving budget management and subcontractor evaluations. These are the kinds of responsibilities that prepare you for executive-level positions [6].
Conclusion
Pursuing a career as a cleared ISSM requires a mix of technical expertise, ongoing education, and a focused job search strategy. Certifications like CISSP and CISM are must-haves, paired with hands-on experience in managing intricate security challenges. However, technical skills alone aren’t enough – strong leadership and communication abilities are essential, especially as you advance to senior positions where you’ll lead crisis response efforts and collaborate with executive teams. This balance of technical and managerial skills reflects the core responsibilities of an ISSM.
The demand for cleared ISSMs is strong in areas like El Segundo, CA, Chantilly, VA, and Fort Belvoir, VA, where employers actively seek professionals with TS/SCI clearances and polygraph credentials. For senior-level roles, maintaining these clearances is crucial for career growth.
To land these roles, it’s important to use specialized job search platforms. Tools like Cleared Cyber Security Jobs can send tailored job alerts directly to your inbox, helping you stay on top of new opportunities as soon as they arise[8]. Expand your search beyond "ISSM" roles – positions like Configuration Management Specialist or Senior Operations Lead often require similar expertise and can provide valuable career moves.
Once you find a promising role, tailoring your application materials to the job’s specific requirements is key. Customize your resume to highlight how your qualifications meet both the basic and preferred criteria[1]. Be prepared for a multi-step hiring process involving phone screenings, technical interviews, and extensive background checks due to the sensitive nature of these positions[1]. Keeping your profiles updated on cleared-job platforms also increases your visibility to recruiters looking for qualified candidates.
For those aiming for leadership roles like Cybersecurity Director or Chief Information Officer, continuous learning and professional development are essential to stay competitive in this ever-evolving field.
FAQs
Can I get an ISSM job without an active TS/SCI clearance?
Most ISSM positions require an active TS/SCI clearance, as it’s typically listed as a mandatory qualification in job postings. Without this clearance, you likely won’t meet the eligibility requirements for these roles.
Which RMF tasks does an ISSM usually own vs delegate?
An ISSM is usually responsible for tasks like keeping RMF documentation up to date, managing hardware and software inventories, and assisting the system owner with security-related duties. However, responsibilities like formal configuration management and crafting risk management strategies are often shared with or assigned to other roles, such as system owners, risk executives, or organizational leaders.
How do I show ISSM impact on my resume without breaking OPSEC?
When showcasing your impact as an ISSM while adhering to OPSEC guidelines, focus on measurable accomplishments and use general, non-specific language. Highlight your involvement in areas like implementing security protocols, conducting risk assessments, or leading security-related initiatives. Avoid mentioning classified systems or incidents directly.
You can also emphasize professional credentials like CISSP or CISM to underline your expertise. Frame your contributions in terms of enhancing compliance or strengthening overall security measures. This approach allows you to demonstrate your value and skills without compromising sensitive information.
