Cyber warfare offers a high-demand career path for military veterans, especially those with security clearances. With over 500,000 unfilled cybersecurity jobs in the U.S. by 2025 and a 0% unemployment rate in the field, transitioning military personnel are uniquely positioned to excel in this industry. Here’s why:
- Military Skills Translate Directly: Threat detection, incident response, and secure communications are core military skills that align with cybersecurity roles.
- Active Security Clearance Is a Major Asset: Veterans with clearances can bypass lengthy background checks, making them attractive to federal agencies and defense contractors.
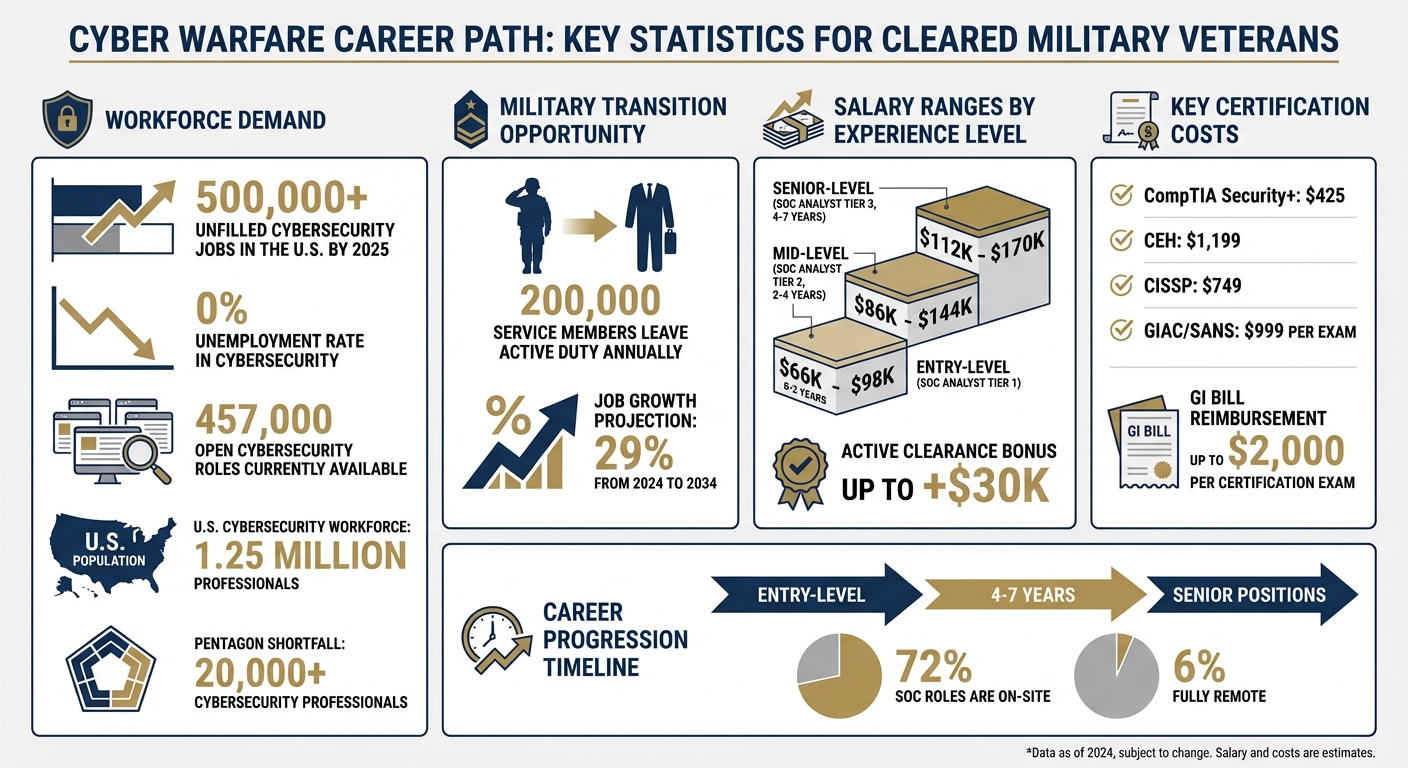
- High Salaries and Job Growth: Entry-level roles start around $80K, with mid-level and senior positions offering six-figure salaries. Cybersecurity jobs are projected to grow 29% from 2024 to 2034.
- Certifications Open Doors: Earning certifications like CompTIA Security+, CISSP, or CEH can fast-track your entry into the field.
- Veteran-Specific Resources: Programs like DoD SkillBridge, SANS VetSuccess Academy, and CyberVetsUSA provide training, mentorship, and job placement.
Whether you’re aiming for entry-level roles like SOC Analyst or advancing to senior positions, your military background and a strategic approach to certifications can set you up for success in cyber warfare. Start by tailoring your resume, leveraging veteran-focused resources, and connecting with employers through platforms like Cleared Cyber Security Jobs.
Cyber Warfare Career Statistics for Military Veterans
Cyber Warfare Operators: Fighting America’s Battles in Cyberspace | Chief’s Corner #23
sbb-itb-bf7aa6b
What Does a Cyber Warfare Specialist Do?
Cyber Warfare Specialists are the guardians of critical systems, tasked with defending against digital threats while also carrying out precision offensive operations in cyberspace.
Primary Job Duties
Your main responsibility is to safeguard classified networks like SIPRNet and secure government-only cloud environments such as AWS GovCloud [6]. This involves conducting penetration tests to identify system vulnerabilities and leading responses to breaches. In these situations, you’ll investigate incidents, gather evidence, and map out how the attack occurred [7].
"On the defensive side what we’re mostly looking for is either the presence of or recovering from the effects… any type of cyber threat whether it’s a computer virus or degradation of service. On the offensive side what we’ll be working on is, you know, trying to find and exploit vulnerabilities and systems to our advantage in the cyber space battle."
– Gunnery Sergeant Timothy Erickson, Cybersecurity Technician, U.S. Marine Corps [2]
Another key aspect of the job is threat analysis and intelligence. You’ll monitor adversary tactics, analyze malicious activities, and use open-source intelligence (OSINT) to predict and prevent future attacks. In a Security Operations Center (SOC), your role includes reviewing security alerts and investigating unusual activity through constant monitoring. The Pentagon’s current shortfall of over 20,000 cybersecurity professionals underscores the pressing need for skilled specialists in this field [7].
To meet these challenges, you’ll need a broad range of technical expertise.
Required Skills and Abilities
To succeed, you must excel in areas like network engineering, packet analysis, and operating systems. Knowing programming languages such as C and Python is crucial for tasks like malware analysis and reverse engineering. Equally important are skills in cloud security, firewall management, and cryptology.
In addition to technical skills, strong analytical abilities and quick decision-making under pressure are vital. You’ll often need to maintain situational awareness, solve intricate problems with limited information, and juggle multiple high-priority tasks in fast-paced environments. Communication is just as important – you’ll brief leaders, collaborate with team members, and document findings in a clear, concise manner. As cyber threats continue to evolve, staying adaptable, disciplined, and committed to ongoing learning will keep you ahead of potential adversaries.
Moving from Military Service to Cyber Warfare
Transitioning from military service to cyber warfare can give you a significant advantage in the job market. With around 200,000 service members leaving active duty annually and more than 500,000 unfilled cybersecurity positions across the country, the timing couldn’t be better to leverage your skills [3][5][8]. Here’s how to make the most of your military background and security clearance during this career shift.
How to Apply Your Military Background
Your military training has already equipped you with valuable skills like threat detection and incident response, which translate seamlessly into civilian cyber warfare roles. The situational awareness you honed in high-pressure environments can easily become expertise in handling incidents, while your ability to make quick decisions under stress is a key asset in mitigating threats.
Rob Hughes, CISO at RSA, highlights why employers value this experience: "Knowing that a prospective hire has had experience in mitigating risks and identifying threats, and knowing that they learned those skills in the highest-stakes environments, always makes those prospects stand out" [8].
To make your military experience resonate with civilian employers, adjust your resume to use terminology they’ll understand. For instance, instead of listing yourself as a Navy "Cryptologic Technician", frame your role in terms like "managing network monitoring systems" or "detecting and mitigating threats" [8]. Civilian employers highly regard military cyber operations experience [4].
Programs like DoD SkillBridge can help bridge the transition. This initiative allows you to gain practical experience with government agencies or defense contractors during your last months of service, giving you a head start in the civilian workforce [3]. You can also connect with organizations like VetSec, CyberVetsUSA, or Hiring Our Heroes, which offer mentorship and job placement services tailored to veterans [8].
Why Your Security Clearance Matters
An active security clearance is a major advantage in the cyber warfare field. It can fast-track your hiring process by eliminating the lengthy background investigation phase [3][9]. A clearance also serves as proof of your trustworthiness, which is critical when working with sensitive information. If your clearance has expired within the past two years, you might be able to have it reinstated quickly, keeping you competitive in the job market.
It’s important to maintain good financial standing, as issues like debt or delinquencies can jeopardize your clearance. Ultimately, having an active clearance opens the door to specialized roles that are off-limits to candidates without one.
Education, Certifications, and Training You’ll Need
You don’t need a four-year degree to step into cyber warfare roles. Certifications can quickly open doors to positions like SOC Analyst or entry-level Security Analyst, allowing you to start earning while continuing to learn. With the right credentials and a military background, you could land roles offering salaries between $80,000 and $135,000 per year. Your military experience not only strengthens your qualifications but also prepares you to tackle the demanding training programs in this field.
Top Certifications for Cyber Warfare
Certifications are key in this industry, and some are more sought-after than others. Here are a few that stand out:
- CompTIA Security+ ($425) and Network+: These foundational certifications are often considered essential for entry-level roles, especially within the Department of Defense (DoD). Many branches of the military offer funding for these through the COOL program.
- Certified Ethical Hacker (CEH) ($1,199): Focused on offensive tactics and penetration testing, this certification is ideal for those looking to specialize in hacking and security breaches.
- Offensive Security Certified Professional (OSCP): Known for its hands-on, rigorous training, the OSCP is highly regarded in the industry.
- CISSP ($749): Aimed at mid-to-senior level roles or management positions, this certification is highly respected but requires five years of professional experience. Military cybersecurity service often counts toward this requirement.
- GIAC certifications through SANS ($999 per exam): These certifications are among the most respected in the industry, covering areas like incident response and penetration testing.
Tom Marsland, Board Chair of VetSec, emphasizes the importance of preparation: "You’ve got to do a lot of prior planning and owning your destiny" [5].
Once you’ve earned these certifications, additional training can help refine your skills even further.
Where to Get Training
Certifications are just the starting point – hands-on training is critical for building expertise. The military and specialized academies offer excellent opportunities:
- U.S. Army Cyber Center of Excellence (Fort Eisenhower, GA): Provides training in signal, cyber, and electronic warfare.
- U.S. Navy Center for Information Warfare Training: Operates across 19 locations and trains over 26,000 students annually in cryptology and cyber-related fields.
- Air Force Cyberspace Technical Center of Excellence (Wright-Patterson AFB): Offers advanced degrees and immersive summer courses focused on cyber warfare.
- DC3 Cyber Training Academy (Hanover, MD): Features over 30 courses covering digital forensics, network intrusion, and log analysis.
Your Post-9/11 GI Bill can reimburse up to $2,000 per certification exam without using a full month of benefits. Additionally, several programs cater specifically to veterans and transitioning service members:
- SANS VetSuccess Academy: Provides free advanced training and certification vouchers, with many graduates moving on to federal cyber roles.
- Onward to Opportunity (Syracuse University): Offers free courses for certifications like Security+, CASP+, and CISSP.
- VetsinTech: Hosts free 5-day bootcamps for the CompTIA Security+ certification.
- CISA Learning (formerly FedVTE): Gives access to hundreds of hours of free training and prep courses for certifications like CEH and CISSP.
These resources ensure you’re not only certified but also well-prepared for the challenges of cyber warfare roles.
How to Build Your Career and Find Jobs
Entry-Level Positions to Start Your Career
Starting your career in cyber warfare? A Security Operations Center (SOC) Analyst (Tier 1) is a great entry point for cleared veterans. Think of it as the "emergency room" of cybersecurity. You’ll handle tasks like triaging alerts, monitoring systems like SIEM and EDR, and investigating phishing attempts. Salaries for entry-level SOC Analysts range from $66K to $98K, with active clearance potentially adding up to $30K more [10].
Other entry-level options include roles like Junior Penetration Tester, IT Auditor, or Compliance Officer. These positions leverage the procedural and analytical skills you developed in the military [5]. Companies such as Booz Allen Hamilton, Leidos, Peraton, GDIT, and CACI are known for hiring junior professionals with active clearances [10]. Keep in mind, though, that most SOC analyst roles (72%) are on-site, with only 6% offering fully remote options [10].
These roles serve as stepping stones, setting you up for more advanced opportunities later in your career.
Finding Jobs on Cleared Cyber Security Jobs
Cleared Cyber Security Jobs is a job board tailored specifically for security-cleared professionals. The platform allows you to filter job searches by clearance level, location, and specific areas of cyber warfare. Upload your resume and set up job alerts to connect directly with hiring managers.
The platform also hosts job fairs where you can meet decision-makers from federal agencies and defense contractors. Since only direct-hire employers are allowed to post, you’ll avoid staffing firms and speak directly with those who can expedite the hiring process. Pro tip: Use civilian-friendly language on your resume. For instance, replace military ranks with terms like "Team Lead" or "Manager" to make your experience more relatable to civilian employers [5].
Moving Up to Senior Positions
Once you’ve gained some experience, certifications and leadership development become key to advancing into higher-level roles. For example, transitioning from a Tier 1 SOC Analyst to senior positions typically takes 4–7 years and requires continuous learning.
- Tier 2 Analysts (2–4 years experience): Handle deeper investigations and root cause analysis, often using tools like Python or PowerShell. Salaries range from $86K to $144K [10].
- Tier 3 Analysts (4–7 years experience): Focus on proactive threat hunting and creating custom detection rules, earning between $112K and $170K [10].
"The SOC is a launchpad, not a destination." – Cybersecurity Jobs List [10]
Senior positions like Cyber Operations Manager or Information Security Architect often demand advanced certifications such as CISSP. Some roles may also require a bachelor’s or master’s degree in cybersecurity [1]. Your military leadership experience can be a major asset when transitioning into management roles.
To ease this transition, consider joining veteran-focused communities like VetSec, which has over 3,300 members, for mentorship and guidance from veterans already in senior cyber positions [5]. Additionally, start building your LinkedIn network early. Connect with HR professionals and cybersecurity teams at your target companies well before your transition date [11].
Conclusion
Shifting from military service to a career as a cyber warfare specialist is a logical next step when approached strategically. Your military background already equips you with invaluable skills – like situational awareness, quick decision-making under pressure, and the ability to adapt – which are highly sought after by cybersecurity employers. These qualities, honed in high-stakes environments, make military candidates stand out in the hiring process.
With over 457,000 open cybersecurity roles waiting for qualified professionals, your military experience gives you a competitive edge [8]. Here’s how to make the most of it:
- Tailor your resume to use civilian-friendly language, and highlight your active security clearance to showcase your readiness for sensitive roles.
- Earn certifications such as CompTIA Security+, CISSP, or OSCP to validate your technical expertise.
- Tap into veteran-focused resources like DoD SkillBridge, SANS VetSuccess Academy, and Navy COOL for training and financial support [8].
- Engage with communities like VetSec to access mentorship and networking opportunities [8].
By following these steps, you can secure roles that value your unique background. When you’re ready to start job hunting, platforms like Cleared Cyber Security Jobs can help you find positions that specifically require and appreciate your active security clearance. These roles often connect directly to hiring managers at federal agencies and defense contractors, simplifying the job search process.
As the U.S. cybersecurity workforce surpasses 1.25 million professionals, demand continues to grow. With approximately 200,000 service members transitioning to civilian life each year, now is an ideal time to enter this field [8]. Begin your journey today – your military-honed skills could be the key to a successful career in cyber warfare.
FAQs
Which cyber roles best match my military MOS/AFSC/rate?
The cybersecurity roles that match your military MOS/AFSC/rate are closely tied to the skills and responsibilities you developed during your service. Positions in areas like communications, IT, spectrum management, and signals often align well. For instance, if you served as an Army MOS 25U (Signal Support Systems Specialist), 25N (Nodal Network Systems Operator-Maintainer), or 25B (Information Technology Specialist), you may find a natural transition into cybersecurity roles. To pinpoint opportunities, compare your specific MOS/AFSC/rate with related cyber job functions.
How do I keep or reinstate my security clearance when I separate?
To keep your security clearance active or to reinstate it after a break, it’s crucial to avoid gaps of more than 24 months between cleared positions. Start planning well in advance – ideally 18 to 20 months before your clearance is set to expire. Use this time to update your paperwork, expand your professional network, and actively seek roles that require a clearance.
If your clearance does lapse, you’ll likely need to update your background information and collaborate with adjudicators to get it reactivated. Staying ahead of the process with careful preparation can make the transition much smoother.
What certification should I earn first for a cleared SOC job?
To land a cleared SOC (Security Operations Center) role, the first step is building a solid foundation in cybersecurity. Starting with a certification like CompTIA Security+ is an excellent choice for beginners. It covers essential concepts and provides a strong entry point into the field.
As you gain experience, consider advancing to certifications like CISSP (Certified Information Systems Security Professional), which is highly regarded for senior-level positions. Alternatively, the CEH (Certified Ethical Hacker) certification is a great way to showcase your skills in ethical hacking and cybersecurity principles. Both certifications can significantly boost your credentials and open doors to more specialized roles.
