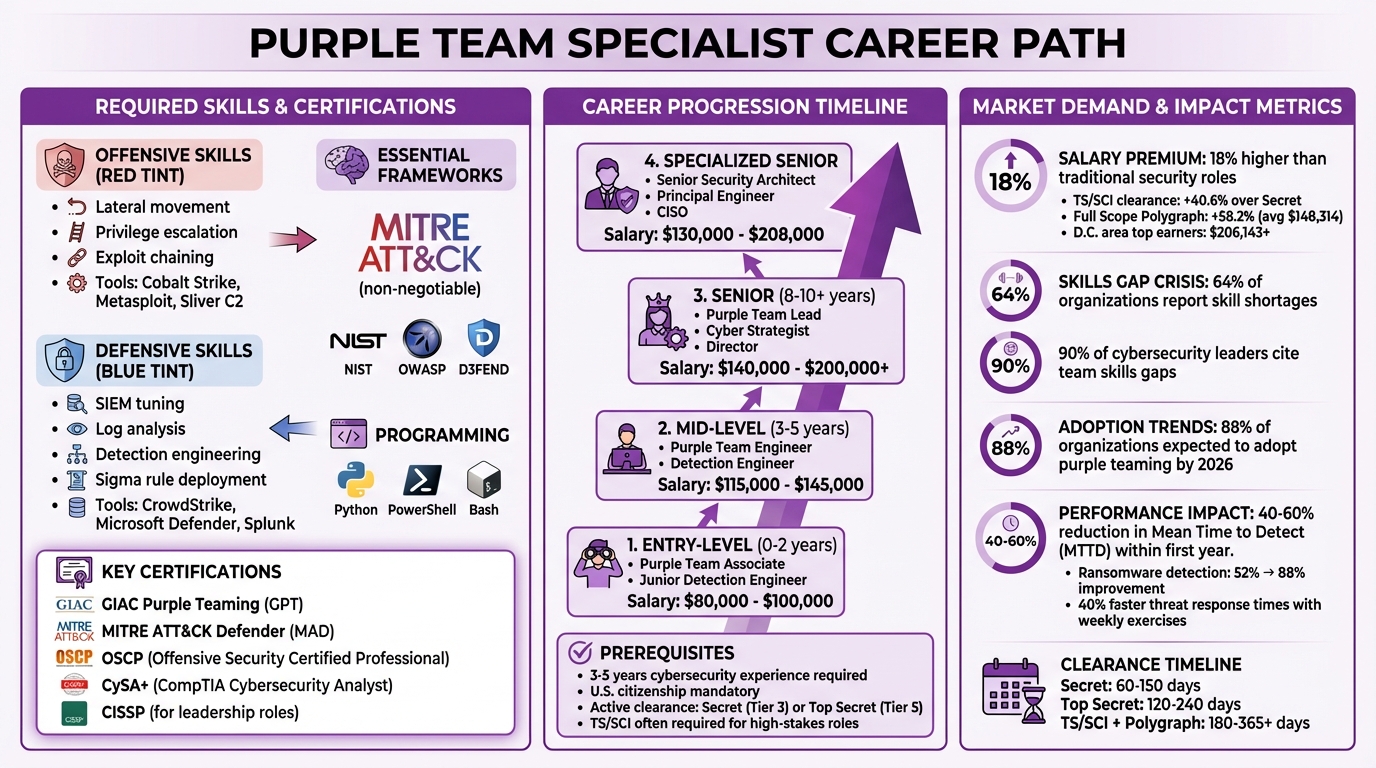
Looking to advance your career in cybersecurity? Purple Team Specialists bridge the gap between offensive (Red Team) and defensive (Blue Team) roles, ensuring simulated attacks lead to stronger security measures. These roles are especially critical in cleared environments like government agencies and defense contractors, where protecting classified data from advanced threats is paramount.
Key Highlights:
- Role Overview: Combines attack simulation with improving detection and response systems.
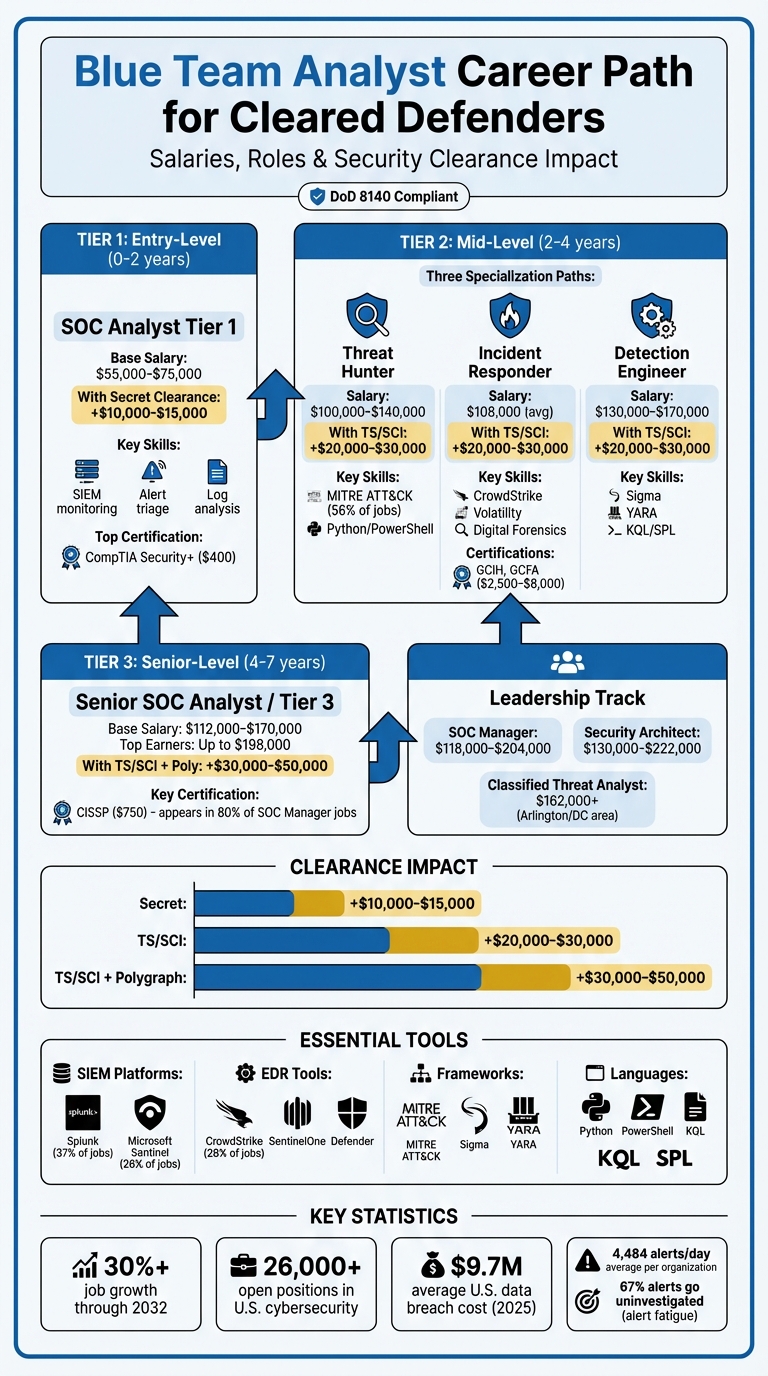
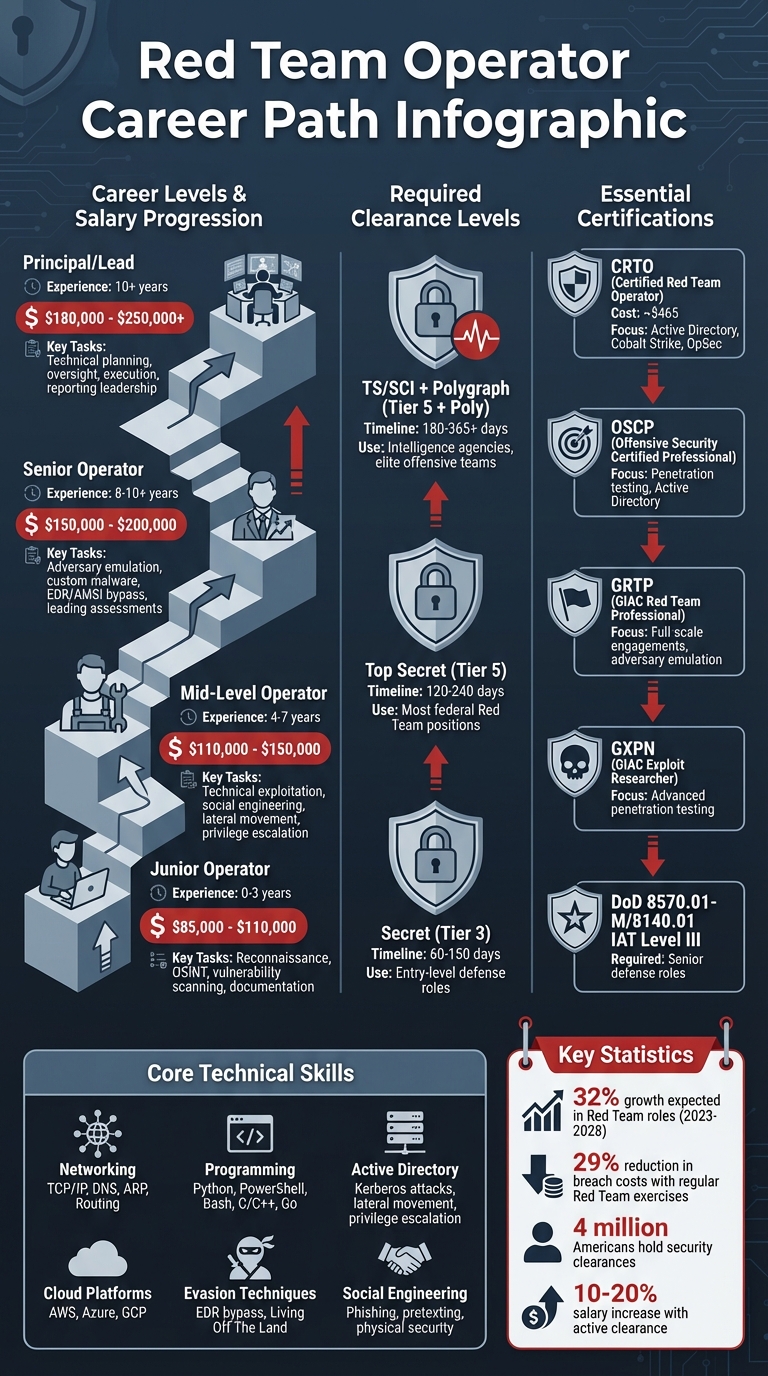
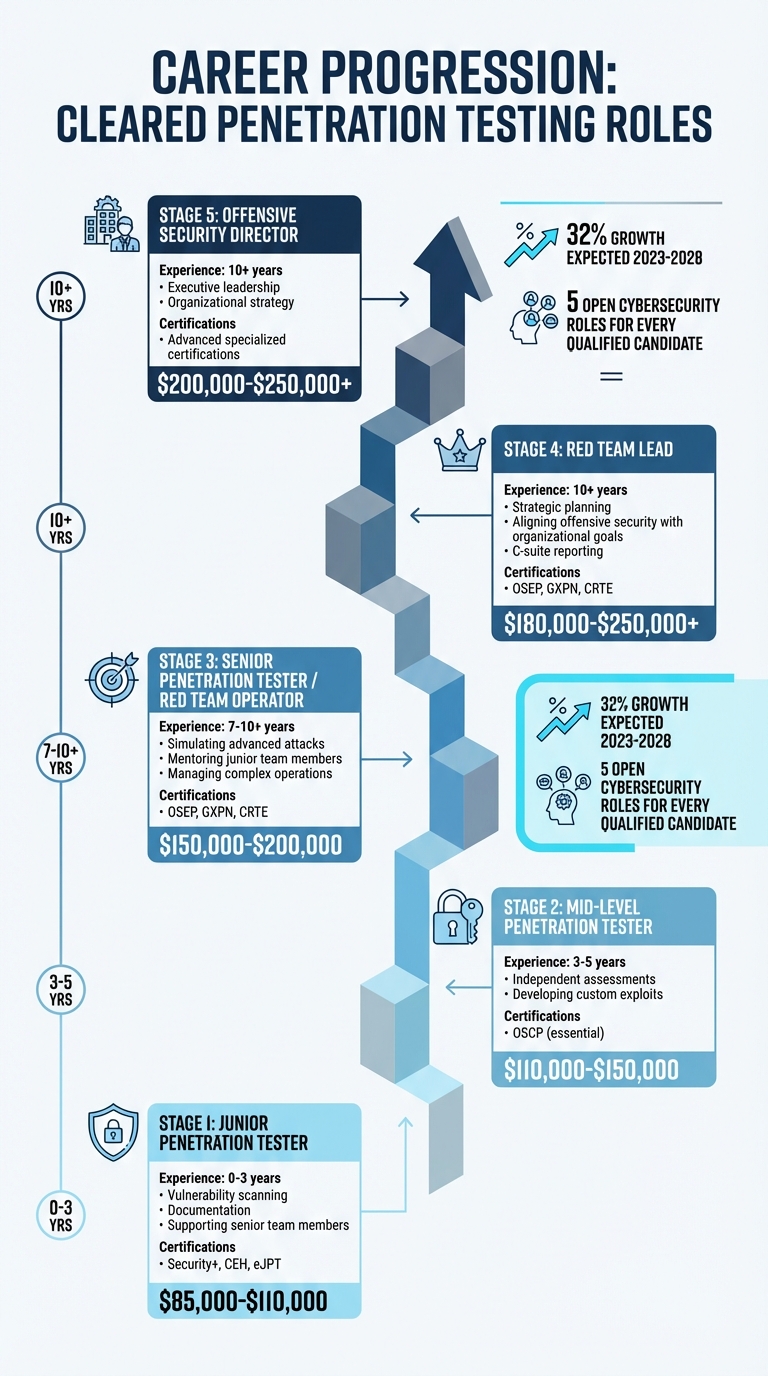
- Salary Range: $110,000–$180,000 annually, with up to an 18% premium over other roles.
- Skills Needed: Offensive techniques (e.g., lateral movement, exploit chaining), defensive practices (e.g., SIEM tuning, log analysis), and tools like MITRE ATT&CK, Cobalt Strike, and Splunk.
- Certifications: GIAC Purple Teaming (GPT), OSCP, CySA+, and CISSP for leadership roles.
- Demand: 64% of organizations report skill shortages in this area, with increased demand expected by 2026.
If you’re a cleared professional with experience in cybersecurity, transitioning to this role can offer job security, higher pay, and a chance to tackle advanced threats head-on.
Purple Team Specialist Career Path: Skills, Certifications, and Salary Progression
What’s a Purple Team and Skills Needed to be a Purple Teamer
sbb-itb-bf7aa6b
What is a Purple Team Specialist?
A Purple Team Specialist is a cybersecurity expert who bridges the gap between offensive (Red Team) and defensive (Blue Team) strategies, creating a feedback loop that strengthens an organization’s security posture. Unlike traditional roles that often work separately, this position requires collaboration and a dual skill set. As Mike Parkin, Senior Technical Engineer at Vulcan Cyber, explains:
"Rather than working against each other competitively, they cooperate. The Red Team explains what they’re doing, and the Blue Team shares where they did or didn’t see the attack as it happened." [6]
Their goal? To turn simulated attacks into actionable defensive improvements. JF Malvik of Malvik Security sums it up well:
"Purple teaming transforms security from a guessing game into an engineering discipline." [2]
Let’s break down what Purple Team Specialists do and why they’re crucial, particularly in environments handling classified information.
Core Responsibilities
Purple Team Specialists juggle offensive and defensive tasks, ensuring both teams work in sync. They design and execute attack simulations that mimic real-world threats – like ransomware or advanced persistent threats (APTs) – and collaborate with Security Operations Centers (SOCs) to refine detection and response systems. This includes fine-tuning tools like SIEM, SOAR, and EDR/XDR to ensure alerts trigger when they should.
When an attack simulation goes undetected, these specialists dig into the reasons. Was it a logging gap, where no data was captured? Or a detection gap, where data existed but no alert was raised? Identifying these gaps is a critical part of their role.
They also use adversary emulation tools like CALDERA and Atomic Red Team to automate test cases, validating defensive measures. Additionally, they simplify complex offensive techniques into actionable insights, often visualizing improvements with tools like VECTR.
This blend of skills is especially important in high-stakes settings, where attackers are continuously evolving their tactics.
Why Purple Teaming Matters in Cleared Environments
For organizations such as government agencies, defense contractors, and others handling classified data, purple teaming tackles challenges that compliance-based approaches often miss. These environments face advanced threats from nation-state actors using cutting-edge techniques, far beyond what standard security audits can catch. While annual penetration tests provide static insights, adversaries evolve constantly – especially in dynamic cloud-based systems.
Purple teaming introduces a process of continuous validation that adapts to modern threats. By conducting quarterly exercises, organizations can significantly improve their detection capabilities, reducing Mean Time to Detect (MTTD) by 40–60% within the first year [5]. As Jared Atkinson, a leader in detection engineering, points out:
"Traditional approaches often deliver a false sense of detection coverage; modern cybersecurity cannot function with either team in isolation." [4]
The shift toward purple team operations is gaining momentum, with 88% of organizations expected to adopt this approach by 2026 [5]. For cleared professionals, this method aligns with NIST and government standards, enabling active, ongoing validation of security controls. It moves organizations beyond mere compliance, building real resilience against advanced threats.
Required Skills and Certifications
To excel as a Purple Team Specialist, you need a strong mix of technical expertise and certifications, particularly in environments that require security clearances. Your skillset should cover both offensive and defensive strategies, bridging the gap between these two critical areas of cybersecurity.
Technical Skills
On the offensive side, you’ll need to master techniques like lateral movement, privilege escalation, and exploit chaining. Tools such as Cobalt Strike, Metasploit, and Sliver C2 are essential for simulating advanced threat scenarios. But being effective in this role also means excelling in defensive architecture and engineering. This includes fine-tuning SIEM platforms, analyzing logs, and configuring endpoint detection systems like CrowdStrike or Microsoft Defender.
A strong grasp of detection engineering is key. You’ll need to write detection logic and automate Sigma rule deployment using CI/CD pipelines. Familiarity with the MITRE ATT&CK framework is non-negotiable, as it helps map attack techniques to defensive gaps. Knowledge of frameworks like NIST, OWASP, and D3FEND further strengthens your ability to identify and mitigate vulnerabilities.
Proficiency in scripting and automation sets you apart. Skills in Python, PowerShell, and Bash allow you to automate tasks, simulate adversarial behavior, and integrate continuous testing into your workflows. Understanding telemetry and logging is another critical area – whether it’s Windows Event Logs, Sysmon (using configurations like sysmon-modular), or Event Tracing for Windows (ETW), you need to validate telemetry before creating detection rules.
Modern threats demand expertise in areas like identity-based attacks, including OAuth abuse and MFA fatigue, as well as cloud and container security, which involves defending against escape techniques in these environments.
Key Certifications
Certifications play a crucial role in building credibility and validating your skills as a Purple Team Specialist. The following certifications are particularly relevant:
- GIAC Purple Teaming (GPT) and MITRE ATT&CK Defender (MAD) focus on purple team methodologies and threat-informed defense [10][1].
- Offensive certifications like OSCP (Offensive Security Certified Professional) demonstrate hands-on penetration testing skills [9].
- Alternatives such as Certified Ethical Hacker (CEH) and GIAC Penetration Tester (GPEN) provide additional offensive credentials, while Certified Red Team Professional (CRTP) specializes in Active Directory exploitation [9].
- On the defensive side, CompTIA Cybersecurity Analyst (CySA+) covers detection and response, while GIAC Certified Incident Handler (GCIH) and GIAC Certified Forensic Analyst (GCFA) enhance forensics capabilities [9][1].
- For leadership or cleared roles, CISSP (Certified Information Systems Security Professional) is often required and highly respected [9][4].
Combining certifications from both offensive and defensive domains creates a well-rounded skillset. For example, pairing OSCP with CySA+ establishes a strong foundation, while adding GPT or MAD highlights your expertise in purple teaming. As Nick Villa, a GPEN-certified professional, explains:
"Being able to and knowing how to exploit a vulnerability not only looks good for you, but the impact it has on the business is extremely valuable" [10].
Purple team roles often come with an 18% salary premium compared to traditional single-discipline security positions [3]. While technical skills and certifications are crucial, soft skills are equally important for success in this field.
Soft Skills
Technical knowledge alone isn’t enough to bridge the gap between offensive and defensive teams. Strong communication skills are essential. You’ll need to translate complex attack techniques into actionable defensive measures and articulate business risks to leadership. Tracy Wallace, Director of Content Development at INE Security, puts it this way:
"Purple teams teach you to think systematically about security challenges, communicate across disciplines, and adapt to new situations" [3].
A collaborative mindset is vital. Instead of perpetuating the traditional “Red vs. Blue” divide, you’ll act as a bridge, fostering cooperation and shared learning. This means thinking holistically about security – understanding how individual vulnerabilities fit into the broader attack surface [6][4].
Adaptability is another critical trait. The threat landscape is always changing, and staying ahead requires continuous learning. With 90% of cybersecurity leaders citing skills gaps on their teams [3], the ability to remain calm and effective during high-pressure situations, such as incident response or breach simulations, sets top specialists apart. Finally, strong documentation and reporting skills ensure that your work leads to actionable improvements rather than being lost in forgotten reports.
Experience and Prerequisites for Cleared Professionals
Professional Experience
Purple Team Specialist roles demand significant prior experience – they’re not entry-level positions. Typically, you’ll need 3 to 5 years of hands-on work in cybersecurity to qualify [4]. Employers look for candidates with deep expertise in either offensive or defensive security disciplines. For example, a background as a SOC Analyst, Incident Responder, Threat Hunter, or Security Engineer equips you with skills like SIEM monitoring, log analysis, and forensics. On the offensive side, roles such as Penetration Tester, Red Team Operator, or Adversary Emulation Specialist develop the attacker mindset critical for purple teaming. Professionals with experience in Detection Research, Engineering, or Threat Intelligence are also well-prepared for this transition [4].
You’ll also need a thorough understanding of Advanced Persistent Threats (APT) and Tactics, Techniques, and Procedures (TTP). This expertise comes from years of exposure to real-world threats and is reflected in the compensation. Mid-level Purple Team Engineers typically earn between $115,000 and $145,000 annually, while senior-level roles can command salaries exceeding $200,000 [6]. For cleared professionals, these technical qualifications are paired with stringent security clearance requirements.
Security Clearance Requirements
Beyond technical expertise, U.S. citizenship is a must for cleared Purple Team roles [11]. An active security clearance is also required, usually at the Secret (Tier 3) or Top Secret (Tier 5) level. Many high-stakes positions – especially those involving sensitive defense systems or work in a Sensitive Compartmented Information Facility (SCIF) – require Top Secret/Sensitive Compartmented Information (TS/SCI) eligibility [11][12]. Some roles in the Intelligence Community may also require a polygraph exam, which can extend the onboarding process.
The time it takes to obtain a clearance varies. A Secret clearance can take 60–150 days, while a Top Secret clearance may require 120–240 days. For TS/SCI with a polygraph, the timeline can extend to 180–365+ days [11]. Importantly, you’ll need sponsorship from a federal agency or a cleared contractor to apply for a clearance, which often comes after receiving a conditional job offer.
Once you have a clearance, maintaining it requires ongoing vigilance. The government now employs Continuous Vetting, an automated system that monitors criminal, financial, and travel records in real time, replacing the older periodic reinvestigation process [11]. You’re also required to self-report any "adverse events", such as arrests, significant debt, or foreign contacts, to your Facility Security Officer (FSO) to maintain trust. Additionally, adjudicators increasingly assess your online presence, including contributions on platforms like GitHub, social media activity, and participation in gaming communities, to evaluate your operational security awareness. Before starting the clearance process, you’ll need to prepare a detailed 10-year history of your residences, employment, education, and foreign contacts to avoid potential "Personal Conduct" concerns [11].
How to Transition into a Purple Team Specialist Role
Building Your Offensive and Defensive Skills
Developing purple team expertise requires a structured approach where you simulate attacks, detect them, refine your techniques, and improve detection capabilities. This continuous feedback loop is key to mastering the role [2]. A great starting point is creating a personal lab environment. Use tools like Proxmox or VMware to set up a lab with enough resources to mimic a real-world Active Directory environment. Tools like BadBlood can help populate the directory, while Sysmon (with the sysmon-modular configuration) enables full telemetry. Pair this setup with a SIEM solution like Elastic Stack or Splunk for comprehensive monitoring [2].
To streamline your learning, follow this 30-day roadmap:
- Week 1: Build your lab infrastructure and ensure that logs are flowing correctly.
- Week 2: Execute five techniques from Atomic Red Team (e.g., T1059 for command-line execution) and create three Sigma detection rules based on your findings.
- Week 3: Use MITRE Caldera to design a chained attack sequence, covering stages like Initial Access, Discovery, and Lateral Movement. Document any detection gaps you encounter.
- Week 4: Create a Git repository for your Sigma rules and commit to testing two or three new techniques each week [2].
This hands-on approach fosters the "translator" mindset that is essential for bridging offensive and defensive strategies in purple teaming [4][6].
To further enhance your skills, consider using Breach and Attack Simulation (BAS) platforms. These tools automate much of the offensive work, allowing you to focus on testing and improving your defensive measures without manually executing each attack [14]. Once you’ve built a strong technical foundation, you’ll be ready to explore job opportunities and expand your professional network.
Using Job Boards and Networking
After sharpening your technical abilities, the next step is to leverage job boards and networking to land a purple team role. Platforms like Cleared Cyber Security Jobs cater specifically to professionals with active security clearances. Uploading your resume to their database increases your visibility, as many cleared positions are filled through direct outreach rather than public postings. Use the platform’s filters to refine job searches by clearance level (e.g., Secret, Top Secret, TS/SCI), location, and keywords like "detection engineering" or "adversary emulation." Setting up job alerts ensures you won’t miss new opportunities.
Attending job fairs hosted on these platforms is another effective way to connect with hiring managers. These events are tailored for cleared professionals, allowing direct interaction with employers rather than staffing agencies. Discussions often cover specifics like SCIF environments and polygraph requirements, which are common in cleared roles. Networking within the cleared community can also uncover unadvertised positions and provide valuable referrals from those already working in purple team roles. Once you start securing interviews, a finely tuned resume will help you stand out.
Optimizing Your Resume
Your resume should clearly showcase your dual expertise in offensive and defensive strategies, as well as your active clearance. Place your clearance level (e.g., Secret, Top Secret, TS/SCI) prominently at the top of your resume, as this is a key factor for cleared hiring managers.
Focus on highlighting collaborative experiences rather than isolated red or blue team roles. For example, instead of listing skills like "penetration testing" or "SIEM monitoring" separately, emphasize roles that involved "joint analysis", "detection engineering", or "cross-functional validation exercises" [8][6]. Data supports the impact of these approaches – weekly purple team exercises can reduce threat response times by 40%, and collaborative testing has been shown to increase ransomware detection rates from 52% to 88% [4][13].
Include certifications that demonstrate your balanced skill set, such as SANS SEC599 or detection engineering courses from Malvik Security. Mention specific tools and frameworks you’ve worked with – like MITRE ATT&CK, Atomic Red Team, Caldera, Sigma rules, VECTR, and BAS platforms – to showcase hands-on expertise [2][8]. This combination of technical skills and collaborative experience will make your resume stand out in the competitive field of purple teaming.
Tools and Platforms for Purple Team Operations
Threat Emulation and Detection Tools
Purple team operations heavily depend on tools that simulate realistic attacks and validate both offensive and defensive strategies. Among these, adversary emulation frameworks and command-and-control (C2) tools are particularly crucial. Atomic Red Team, for instance, offers a library of small, focused tests aligned with the MITRE ATT&CK framework, making it ideal for testing specific security controls. On the other hand, MITRE Caldera automates multi-stage attack chains using agents and plugins, allowing for more comprehensive simulations of adversary behavior. While Atomic Red Team is perfect for testing individual detections, Caldera shines when simulating complex, chained attack sequences.
For environments centered on Windows, PurpleSharp generates realistic attack telemetry using .NET executables, supporting 47 different MITRE ATT&CK techniques [15]. When it comes to C2 frameworks, Cobalt Strike is a leading tool for simulating long-term embedded threats with flexible communication channels. If you’re looking for an open-source alternative, Sliver C2 provides cross-platform implant capabilities to mimic realistic C2 behavior. Additionally, Metasploit remains a standard tool for simulating various attack vectors and exploiting vulnerabilities.
Detection tools play an equally important role. Sysmon, when configured with optimized detection settings (e.g., sysmon-modular), captures detailed host-level telemetry, which is essential for detecting advanced techniques such as LSASS memory dumping. For example, Sysmon Event ID 10 logs LSASS access, which can be a key data point for detection. Before creating detection rules, ensure your SIEM system captures the necessary telemetry. These tools not only simulate adversary actions but also supply critical data for broader monitoring and analysis.
SIEM and BAS Platforms
To complement emulation tools, SIEM (Security Information and Event Management) and BAS (Breach and Attack Simulation) platforms provide real-time data analysis and attack visualization. SIEM platforms, like the ELK Stack (Elasticsearch, Logstash, Kibana), consolidate telemetry from both red and blue teams, offering a unified view to identify gaps and visualize attack data. Splunk offers similar capabilities and even provides a six-month free license for lab environments, with up to 10 GB of daily indexing [7]. For those seeking a free alternative, Wazuh is another reliable option for log aggregation and alert validation.
BAS platforms take things further by automating the execution of tactics, techniques, and procedures. SCYTHE, for example, enables continuous validation with features like campaign customization, auto-pausing for real-time analysis, and integrated reporting. This automation allows teams to focus on improving defenses rather than managing manual tests. For tracking campaign outcomes, VECTR is particularly effective. It logs detected versus missed activities and generates MITRE ATT&CK heatmaps to highlight detection trends over time. Pairing VECTR with DeTTECT can also help assess the quality of your data sources and visibility across specific tactics, ensuring a more robust defense strategy.
Career Growth and Advancement Opportunities
Pathways to Senior Roles
Purple Team Specialists often climb the career ladder faster than professionals focused solely on offensive or defensive security. Why? Organizations place a premium on their well-rounded expertise in both areas. The typical career path starts with hands-on technical roles and progresses to strategic positions. At this stage, you’ll find yourself managing tabletop exercises, overseeing collaboration between Red and Blue teams, and presenting technical findings in a way that aligns with business risks for leadership teams [4][6].
Some common roles along this journey include Detection Engineer, Security Validation Engineer, Purple Team Lead, Cybersecurity Strategist, and ultimately titles like Director of Cybersecurity or Chief Information Security Officer (CISO) [4]. Increasingly, these positions emphasize a "Cyber Strategist" approach, blending technical execution with risk management. This dual focus makes Purple Team professionals indispensable for building stronger organizational defenses.
To prepare for senior roles, it’s critical to develop leadership skills rooted in measurable outcomes. Tools like VECTR can help you track and showcase improvements in detection coverage over time, providing tangible evidence of your contributions. Senior-level roles also demand proficiency in coding languages such as Python, PowerShell, Golang, or Node.js for automating attack simulations and fine-tuning detections [6]. Advanced certifications like CISSP, CISM, or CGEIT can further strengthen your resume, especially for roles in cleared environments where certifications like CISSP are often required for top-tier positions [17][16].
"The most bulletproof careers are built on adaptability rather than narrow expertise. Purple teamers represent exactly that kind of versatility… they are not only keeping their positions – they’re actually advancing, thriving, and proving that they possess strong earning power." – Tracy Wallace, Director of Content Development, INE Security [3]
This adaptability and skillset often lead to greater financial rewards.
Salary Insights
In addition to expanded responsibilities, career progression in this field often comes with a significant pay boost. Purple Team Specialists earn roughly 18% more than traditional security roles [3]. Entry-level positions start at a higher salary range ($80,000–$100,000) compared to junior SOC analysts or penetration testers, who typically earn between $60,000 and $86,000. This difference reflects the prior experience required in at least one security discipline [4].
Security clearance can further amplify earnings. Professionals with a Top Secret/SCI clearance earn, on average, 40.6% more than those with a Secret clearance. Adding a Full Scope Polygraph (FSP) pushes average salaries to $148,314 – a 58.2% increase over the baseline for Secret clearance holders [17]. In high-cost areas like Washington, D.C., top earners with TS/SCI FSP clearance can exceed $206,143 annually [17].
| Experience Level | Typical Roles | Salary Range |
|---|---|---|
| Entry-Level (0-2 years) | Purple Team Associate, Junior Detection Engineer | $80,000 – $100,000 [4] |
| Mid-Level (3-5 years) | Purple Team Engineer, Detection Engineer | $115,000 – $145,000 [4] |
| Senior (8-10+ years) | Purple Team Lead, Cyber Strategist, Director | $140,000 – $200,000+ [4] |
| Specialized Senior | Senior Security Architect, Principal Engineer | $130,000 – $208,000 [4][6] |
Real-world job postings illustrate this earning potential. For example, in June 2026, Meta advertised an Offensive Security Engineer (Purple Team) position in Washington, D.C., offering $117,000–$137,000. Meanwhile, Kroll listed remote-capable Purple Team Specialist roles with salaries ranging from $100,000 to $140,000 [3]. These examples highlight the strong financial incentives for cleared professionals in this field.
Conclusion
Purple Team Specialists hold a critical position in cleared cybersecurity, bridging the divide between identifying vulnerabilities and implementing effective solutions. In environments where operational readiness takes precedence over simple compliance, these experts create a dynamic feedback loop that turns security challenges into measurable progress. This method strengthens protection for mission-critical systems in tangible ways [4].
For those looking to step into this dual-discipline role, the path is clear: focus on honing both offensive and defensive skills through hands-on labs and targeted certifications. Familiarity with frameworks like MITRE ATT&CK is essential for speaking the common language of cybersecurity. The financial rewards reflect the importance of this skill set, with mid-level roles offering salaries between $115,000 and $145,000, and senior positions exceeding $200,000 [4].
"The most bulletproof careers are built on adaptability rather than narrow expertise. Purple teams teach you to think systematically about security challenges, communicate across disciplines, and adapt to new situations." – Tracy Wallace, Director of Content Development, INE Security [3]
The demand for Purple Team Specialists in cleared environments is on the rise as defense contractors and government agencies recognize that 64% of organizations cite skills gaps – not a lack of personnel – as their top security challenge [3]. By mastering attack emulation, crafting detection rules, and effectively communicating findings to leadership, you’re preparing for a career that evolves alongside the ever-changing threat landscape.
Start with a dedicated lab, conduct initial atomic tests, and track your progress. The cleared cybersecurity jobs field urgently needs professionals who can turn simulated attacks into actionable defenses, and the opportunities for those with these skills are only growing.
FAQs
How do I prove purple team skills without prior purple team job titles?
To showcase your purple team skills, it’s essential to demonstrate expertise in both offensive (red team) and defensive (blue team) practices. Hands-on experience is key – this could include building detection labs or conducting adversary emulation to simulate real-world threats.
Familiarity with tools like SIEM platforms and frameworks such as MITRE ATT&CK is crucial. These tools help bridge the gap between detecting threats and understanding attacker behavior. Certifications such as CEH, CISSP, or OSCP can add credibility to your skill set, signaling your technical knowledge and commitment to professional growth.
Additionally, active participation in purple team exercises or collaborative projects can highlight your ability to merge offensive and defensive strategies effectively. These activities not only showcase your technical skills but also your ability to work in a team-oriented environment to strengthen an organization’s security posture.
What’s the fastest path from SOC or pentest roles into purple teaming?
The fastest path to getting into purple teaming is by blending offensive and defensive cybersecurity skills, earning certifications such as CEH, OSCP, or CISSP, and building practical experience. Begin with roles like security analyst or penetration tester, and actively engage in purple team exercises and labs. These activities help you refine and demonstrate your ability to emulate adversaries while improving threat detection skills.
What clearance level is most common for purple team roles?
The most frequent clearance levels for purple team roles often include TS/SCI or equivalent, based on the organization’s requirements. Though the exact clearance level can differ, these roles typically demand a security clearance that matches the organization’s operational needs and the sensitivity of the tasks at hand.