The OSCE³ certification is a top-tier credential for advanced penetration testers, especially those in U.S. government or defense roles. It requires passing three challenging 48-hour exams: OSWE (web application testing), OSEP (bypassing hardened defenses), and OSED (Windows exploit development). This certification demonstrates expertise in areas like custom exploit creation, advanced evasion techniques, and vulnerability analysis, making it highly sought after in cybersecurity.
Key Takeaways:
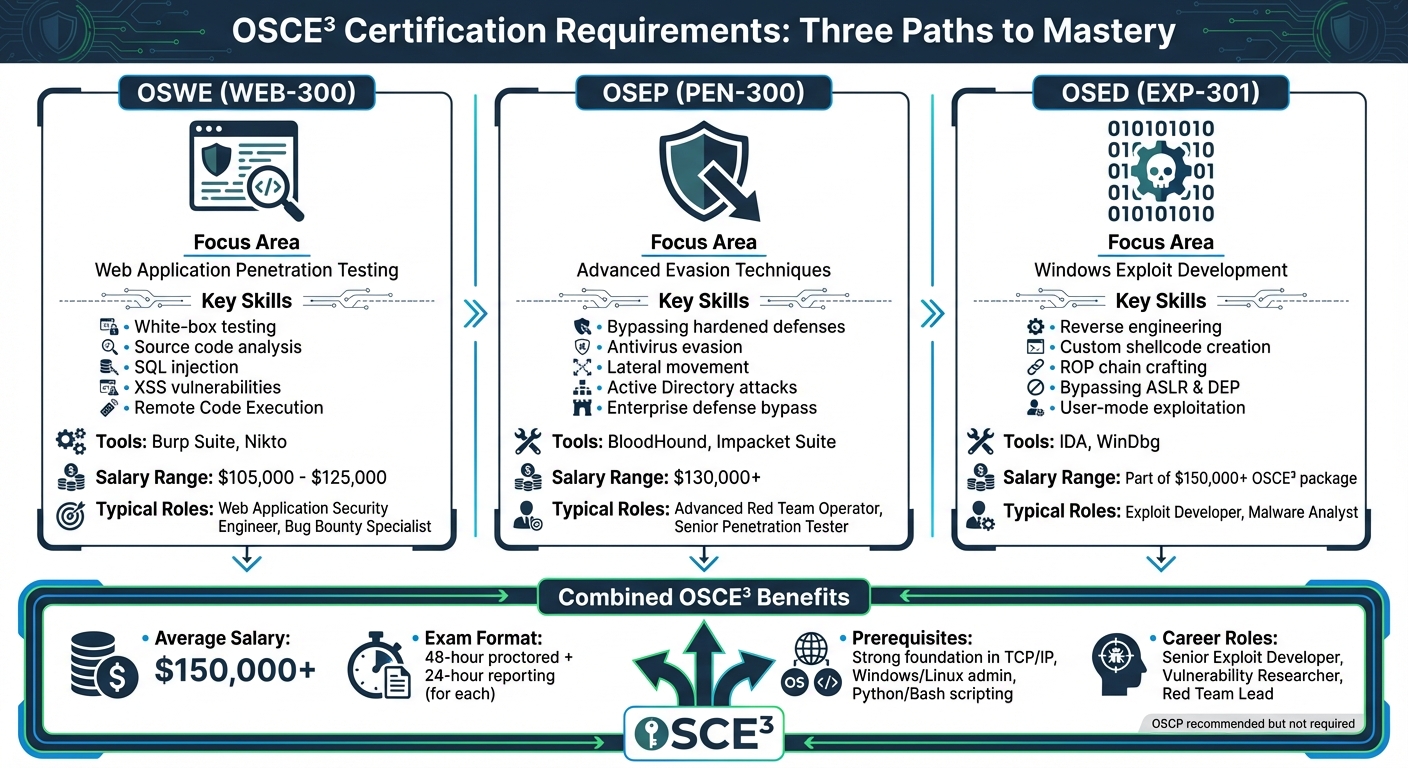
- Certifications Required: OSWE, OSEP, OSED.
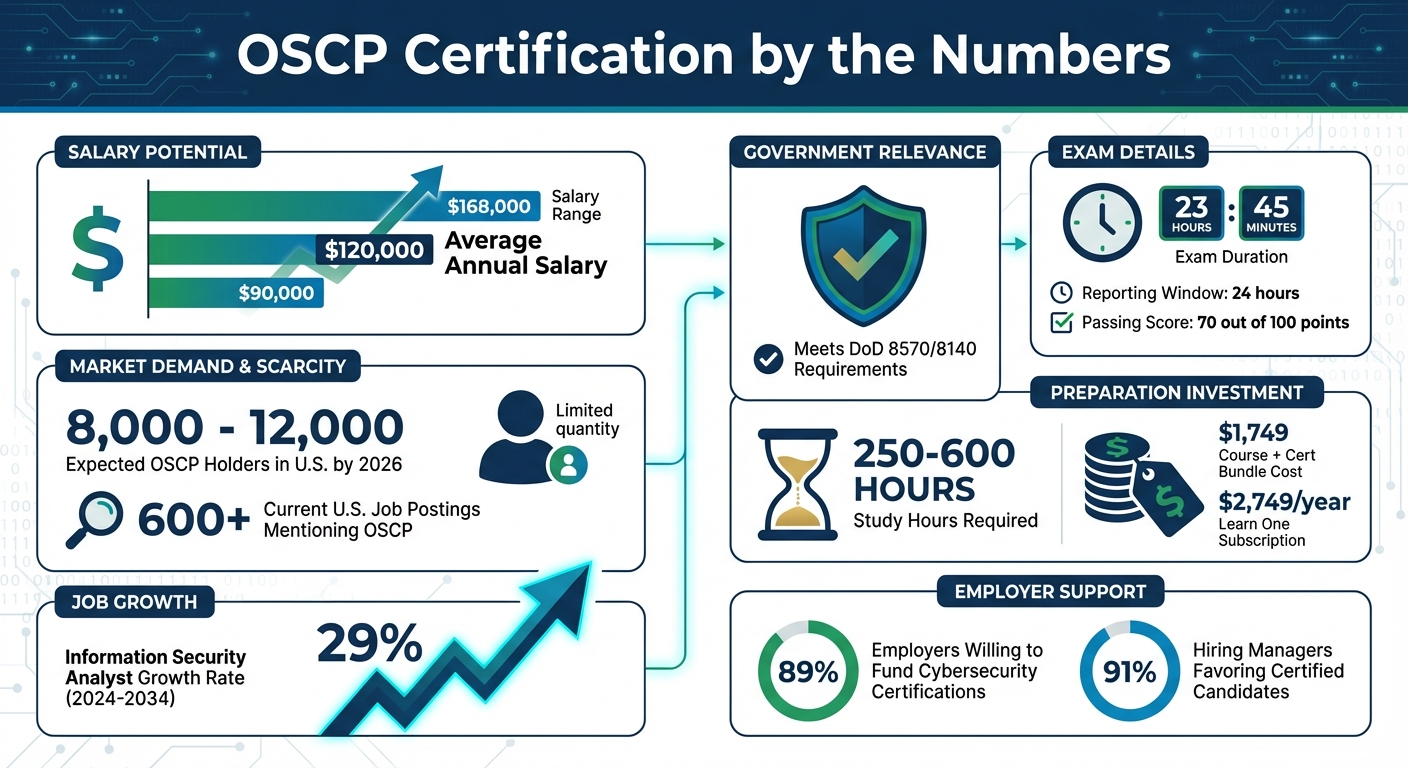
- Cost: Learn One Subscription ($2,749/year) or Course + Cert Bundle ($1,749 for 90 days).
- Skills Needed: Proficiency in networking, scripting (Python, Bash), and advanced exploitation techniques.
- Exam Format: 48-hour proctored sessions with a 24-hour reporting phase.
- Career Benefits: Opens doors to roles like Red Team Lead, Vulnerability Researcher, and Senior Exploit Developer, with salaries often exceeding $150,000 annually.
With ransomware attacks up 30% in early 2026 and AI-driven threats growing, this certification positions you for senior roles in advanced penetration testing and exploit development, especially within the cleared sector. For preparation, focus on OffSec’s courses (WEB-300, PEN-300, EXP-301), hands-on practice in labs, and strong documentation skills. Balancing certification prep with cleared work commitments is crucial; plan exams during leave or less demanding work periods.
The OSCE³ not only validates your expertise but also significantly boosts career opportunities and earning potential in the cybersecurity field.
I Became OffSec Certified Expert (OSCE3)!

OSCE Certification Requirements and Prerequisites
OSCE³ Certification Requirements: Three Paths to Advanced Penetration Testing Mastery
To earn the OSCE³ certification, you must complete three advanced certifications: OSWE, OSEP, and OSED. Once these are achieved, you’ll automatically receive a printed certificate, wallet card, and challenge coin – no additional exams required [4].
"Earning all three of the following certifications automatically grants you the new OSCE³ certification… No additional exam will be required once you have obtained the other three standalone certifications." – OffSec Support [4]
Here’s a closer look at the certifications and the skills they focus on.
Required Certifications and Skills
Each certification hones in on a specific area of offensive security:
- OSWE (WEB-300): Specializes in white-box web application penetration testing. You’ll need to analyze large codebases and identify vulnerabilities like SQL injection, XSS, and Remote Code Execution [1].
- OSEP (PEN-300): Focuses on advanced evasion techniques for bypassing hardened defenses, including antivirus evasion and lateral movement within networks [1].
- OSED (EXP-301): Centers on Windows user-mode exploit development. This includes reverse engineering with tools like IDA and WinDbg, and crafting ROP chains to bypass protections such as ASLR and DEP [1].
While the OSCP certification isn’t a formal prerequisite, it’s often considered the starting point for this advanced learning path [4]. To succeed, you’ll need a strong foundation in TCP/IP networking, Windows and Linux administration, and scripting skills in Bash or Python [7]. For OSWE, the ability to read and analyze web application code is critical, while OSED demands proficiency in C and Assembly. Each certification exam consists of a challenging 48-hour proctored session, followed by a 24-hour reporting phase [1].
| Certification | Course Code | Focus Area |
|---|---|---|
| OSWE | WEB-300 | Web application penetration testing and code analysis |
| OSEP | PEN-300 | Evasion techniques and lateral movement |
| OSED | EXP-301 | Exploit development and mitigation bypass |
Considerations for Cleared Professionals
While government security clearance isn’t required for OSCE³, cleared professionals should keep a few logistical factors in mind. The exams are proctored, requiring a reliable internet connection and the use of specific proctoring software [9]. If you work in a restricted environment like a SCIF, it’s best to schedule your exam outside of work hours.
The OSEP course is particularly relevant for professionals in environments with mature security functions, such as government or defense sectors. It mirrors the challenges of breaching hardened systems, often protected by enterprise-grade defenses [3]. Cleared professionals may find it helpful to schedule the 48-hour exams during leave periods to avoid conflicts with job responsibilities. Additionally, your experience with advanced security functions and tools like EDR systems can be a strong advantage when tackling the OSEP exam.
How to Prepare for OSCE Certification
Getting ready for OSCE³ means tackling three distinct exams – OSWE, OSEP, and OSED – each requiring its own set of skills. The PEN-300 course alone offers over 615 hours of content, so having a structured, long-term plan is crucial, especially if you’re balancing it with a demanding work schedule [11]. Instead of memorizing tools, focus on building repeatable methodologies to handle the 48-hour exam effectively. Below, we’ll look at how each training path aligns with the requirements of the OSCE³ exams.
Recommended Courses and Training Paths
OffSec provides three main courses that correspond directly to the OSCE³ exams:
- WEB-300: Prepares you for the OSWE certification by focusing on web application testing. It covers source code analysis, chaining vulnerabilities, and tools like Burp Suite and Nikto.
- PEN-300: Helps you earn the OSEP certification by teaching advanced evasion techniques, lateral movement, antivirus bypassing, and Active Directory attacks.
- EXP-301: Focuses on Windows exploit development for the OSED certification. It includes training on tools like WinDbg and IDA, creating custom shellcode, and bypassing protections like ASLR and DEP.
For pricing details, refer to the subscription table in the Introduction. The Learn One subscription is particularly helpful for those with unpredictable schedules, offering extended access to accommodate high-pressure work periods or deployments.
Study Tips for Cleared Pen Testers
Once you’ve selected your training path, refine your study habits to maximize efficiency. Strong documentation skills are critical, as your exam report must be detailed enough for a technically skilled reader to replicate every step of your attacks. Practice documenting commands, custom scripts, and console outputs during your lab sessions. Keeping a "Failure Log" can also help you learn from unsuccessful exploits.
Set specific goals for each study session. For instance, focus on mastering a particular privilege escalation method within 20 minutes. The Pomodoro Technique – working in 25-minute sprints – can help maintain focus during extended study periods. Additionally, organize a searchable knowledge base to quickly reference syntax or commands during the high-pressure exam.
Use the final challenge labs in each course to test your readiness. These labs are designed to reflect the complexity of the actual exams. If you have experience working in cleared environments with hardened systems and enterprise-grade defenses, you already have a strong foundation that will serve you well during the exams. Keep in mind that certain tools are prohibited during exams, such as AI chatbots like ChatGPT, automated tools like SQLmap (restricted in OSWE but allowed in OSEP), and commercial tools like Cobalt Strike [10][5].
Managing Certification Prep with Cleared Work Commitments
Balancing certification prep with cleared assignments requires careful planning. The 48-hour proctored exams demand a stable internet connection and cannot be taken in restricted environments. Schedule your exam attempts during planned leave or less demanding work periods when you’re not required at a secure facility. Use the 24/7 lab access to study during evenings or weekends when secure facility restrictions don’t apply.
If your employer offers workforce development programs, ask about Learn Enterprise subscriptions. These provide structured training for teams, along with multiple exam attempts [1][6]. Additionally, communicate your certification goals with your supervisor – they may be able to offer dedicated study time or flexible scheduling to support your preparation.
sbb-itb-bf7aa6b
Tools and Resources for OSCE Preparation
Recommended Penetration Testing Tools
Once you’ve mapped out your study plan, the next step is gathering the right tools for your OSCE³ preparation. Your toolkit should cover five essential areas: reconnaissance, Active Directory exploitation, web application testing, privilege escalation, and post-exploitation.
For reconnaissance, tools like AutoRecon, RustScan, and Feroxbuster (or Gobuster) are excellent for discovery and scanning tasks [14]. When it comes to Active Directory exploitation, BloodHound can help visualize relationships, while the Impacket Suite pairs well with tools like Kerbrute, Rubeus, and PowerView for enumeration and Kerberos-related tasks [14].
Web application testing benefits from Burp Suite as a strong proxy tool, along with SQLmap for injection vulnerabilities, and Nikto or WPScan for specialized scanning [14]. For privilege escalation, PEASS-ng tools like LinPEAS and WinPEAS are invaluable for identifying escalation paths on Linux and Windows systems. Finally, in post-exploitation, tools such as Mimikatz for credential dumping, Evil-WinRM for remote management, and CrackMapExec for network assessments are highly effective.
While these tools are powerful, focus on manual exploitation techniques and custom scripts using languages like Python, Bash, PowerShell, or C# to strengthen your skills [7][13].
Study Platforms and Labs
To sharpen your skills, hands-on practice is crucial. The OffSec Proving Grounds Practice platform offers access to over 200 lab environments, featuring more than 250 hours of content designed to mimic real-world attack scenarios [12][15]. This platform costs $19 per month or $199 annually, providing unlimited access – perfect for deep-dive exploitation practice [12][17]. For maximum security, prioritize "Private Machines" during your sessions [12].
The OffSec Learning Library is another excellent resource, offering 14 certifications, over 125 learning paths, and more than 750 labs, totaling an impressive 7,500 hours of content [16]. For each OSCE³ exam, you’ll find dedicated labs tailored to specific techniques: WEB-300 for OSWE, EXP-301 for OSED, and PEN-300 for OSEP [2].
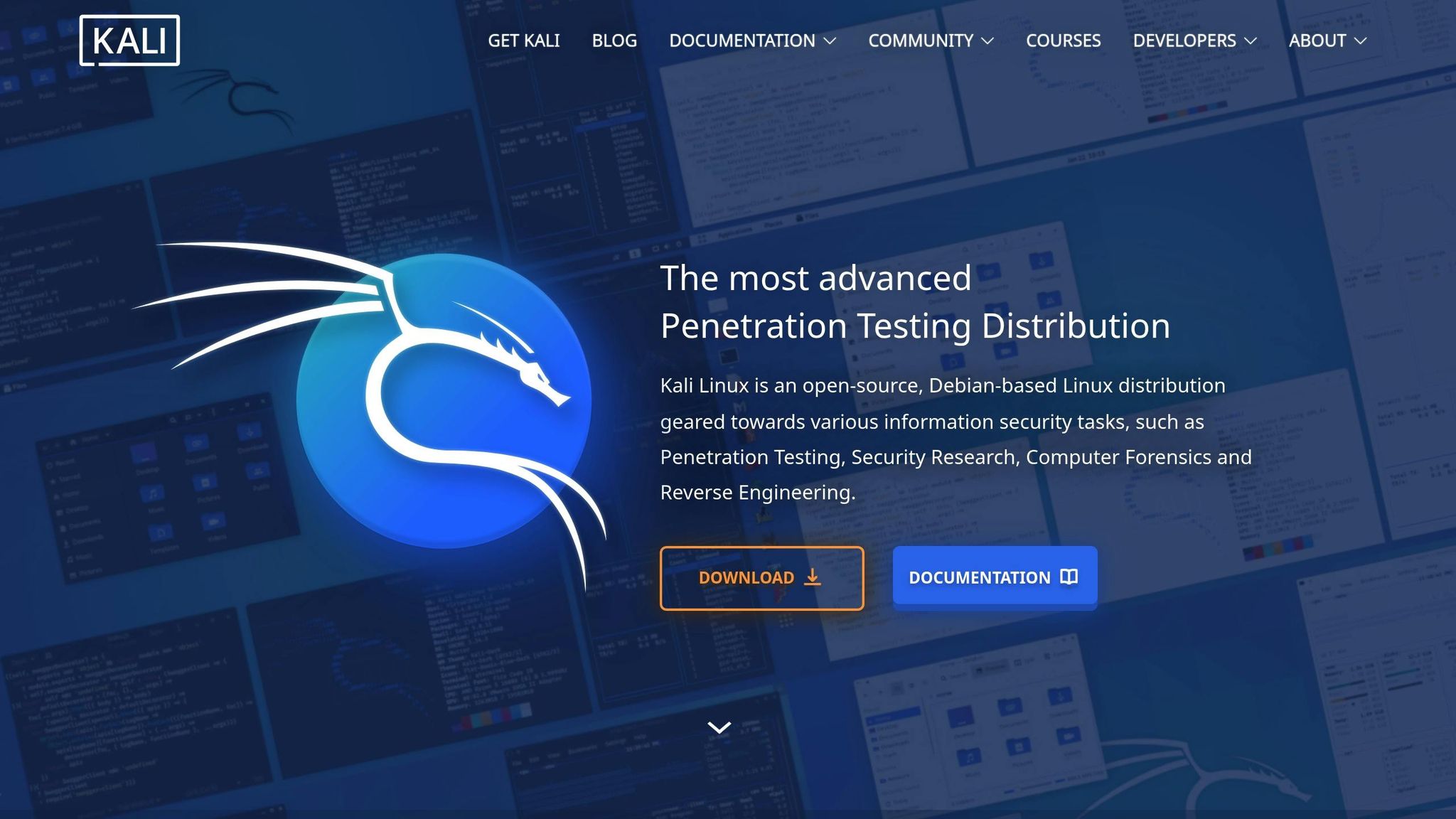
If you’re on a tight budget, consider the OffSec Proving Grounds Play option, which provides free access to over 50 community-generated Linux labs. However, note the daily three-hour usage limit [12][15]. To ensure smooth access during your preparation, practice using both in-browser Kali Linux and VPN-based connections with OpenVPN [15][18].
Outside of structured labs, engaging with the broader security community can provide additional insights and practical tips.
Community and Networking Resources
The journey to OSCE³ certification isn’t just about tools and labs; it’s also about learning from others who’ve been through the process. Peer insights and community support can offer valuable guidance, especially for tackling the challenging 48-hour exam format.
OffSec provides a dedicated community for Proving Grounds users, where you can troubleshoot and collaborate with others working on the same machines [12]. Additionally, GitHub repositories like verylazytech/OSCP-Resources serve as treasure troves of roadmaps, cheatsheets, and practice box recommendations, encouraging collaboration [19].
"This guide is a community-driven effort. Feel free to suggest improvements or share your insights via pull requests." – verylazytech [19]
Platforms like Twitter/X are another way to connect with certified OSCE³ professionals. For instance, Nourrisson Julien (OSCE³) actively invites discussions and shares advice:
"If you wish to contact me to discuss anything you can DM me on twitter… @0x_woofy" [8]
Reading blogs and write-ups from successful OSCE³ holders can also provide practical tips for managing the intense exam format. Beyond informal networking, consider formal mentorship programs or mastermind groups available through professional development platforms. These resources can help refine your approach and boost your confidence as you prepare for advanced certifications [20].
Career Benefits of OSCE Certification for Cleared Professionals
Earning the OSCE³ certification can significantly enhance your cybersecurity career, especially in roles requiring advanced offensive security skills. This credential demonstrates expertise in areas like custom exploit development, advanced evasion techniques, and white-box source code analysis [1]. It positions you for senior-level roles that demand specialized knowledge, while also opening doors to higher compensation levels.
Job Opportunities on Cleared Cyber Security Jobs
With an OSCE³ certification, you gain access to specialized positions such as Vulnerability Researcher, Malware Analyst, Application Security Researcher, and Secure Code Reviewer [1]. These roles are highly sought after by major cleared employers running advanced offensive security programs [25]. The platform’s veteran-founded approach allows you to connect directly with these employers – no staffing firms involved. You can upload your resume, set alerts for OSCE³-specific jobs, and even participate in job fairs tailored to cleared professionals.
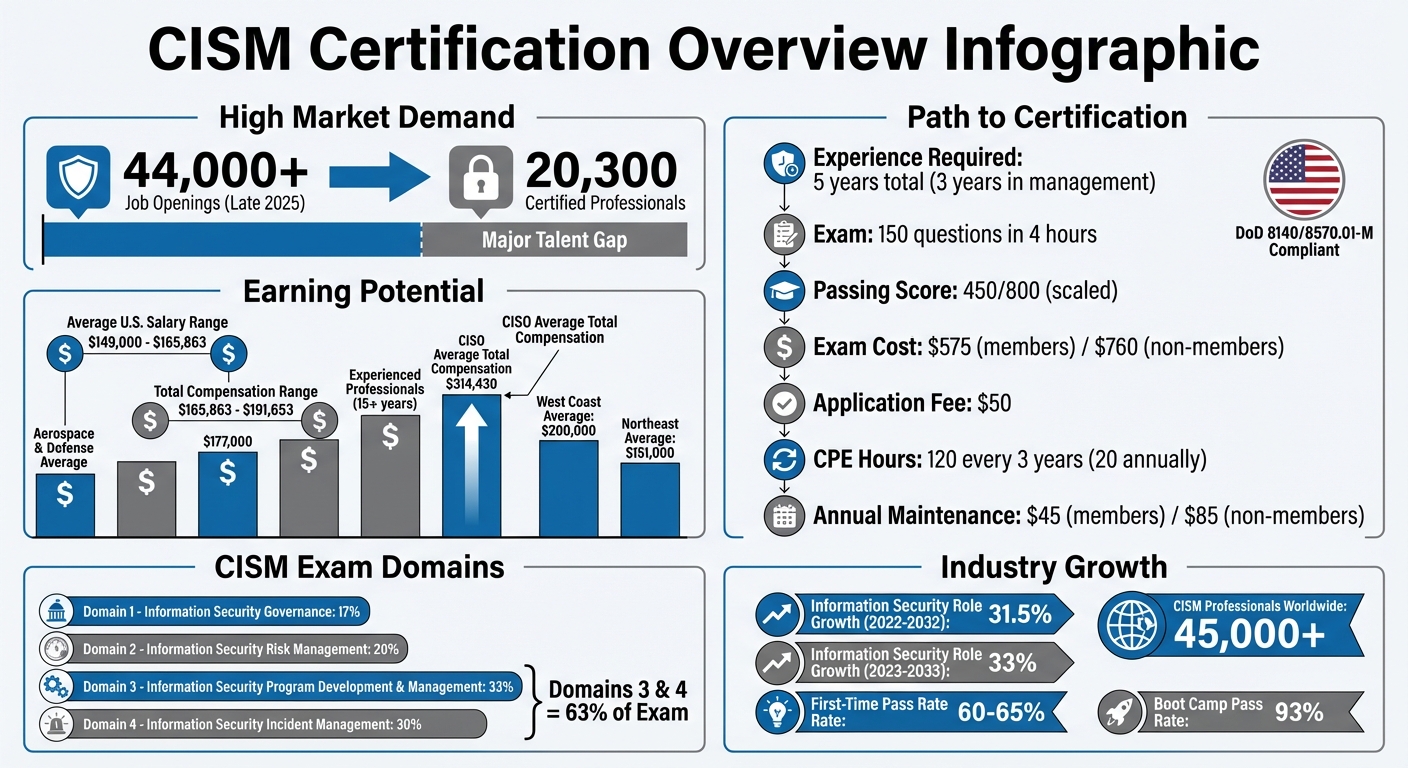
The value of certifications in hiring cannot be overstated. A staggering 91% of hiring managers prefer certified candidates [23]. With OSCE³ credentials, you stand out in a competitive applicant pool, gaining access to roles that not only expand your career options but also offer impressive financial rewards.
Salary Expectations and Role Comparisons
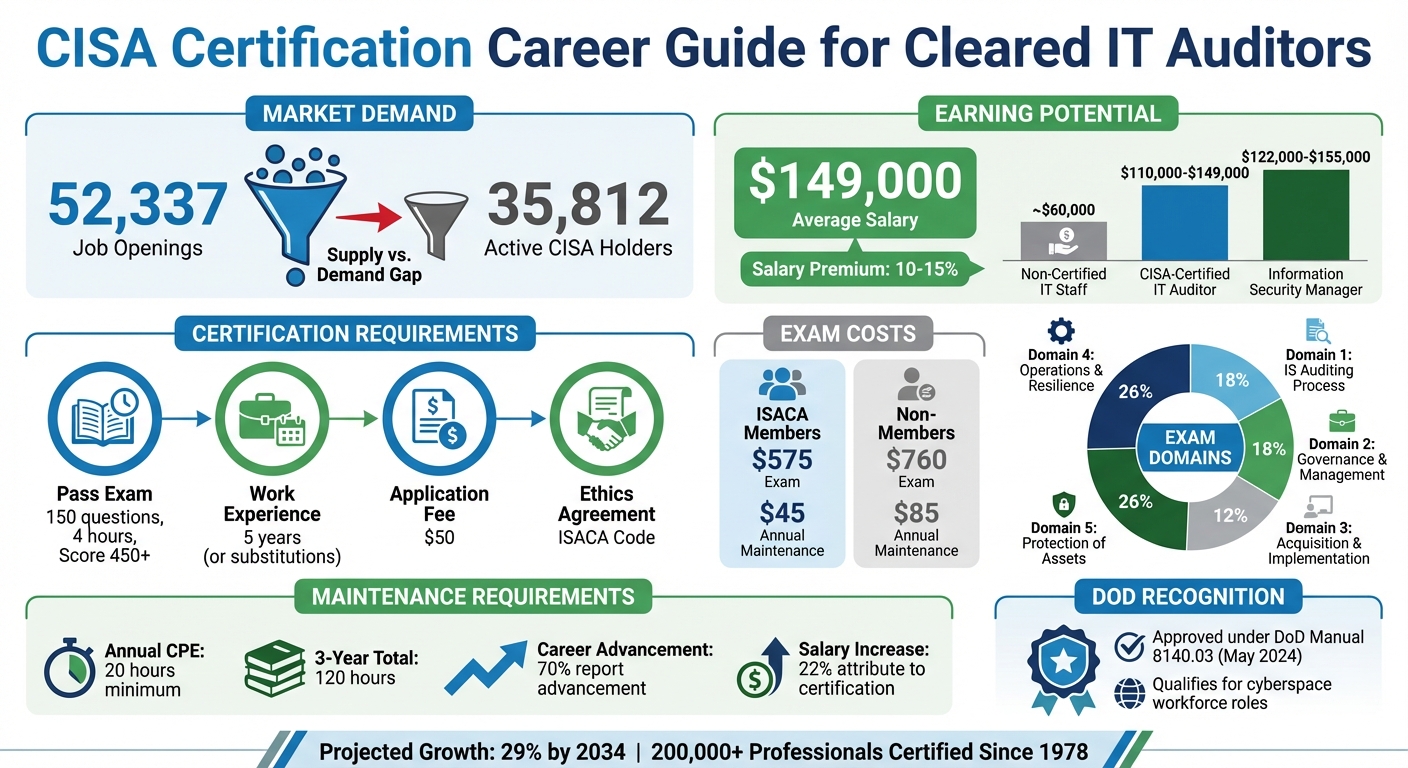
The financial benefits of OSCE³ certification are undeniable. Professionals with this credential typically earn $150,000+, which is a significant jump compared to the average salary of $103,000 for OSCP-certified professionals [24][25].
| Certification | Average U.S. Salary | Typical Cleared Roles |
|---|---|---|
| OSWE | $105,000 – $125,000 | Web Application Security Engineer, Bug Bounty Specialist [21] |
| OSEP | $130,000+ | Advanced Red Team Operator, Senior Penetration Tester [21] |
| OSCE³ | $150,000+ | Senior Exploit Developer, Vulnerability Researcher, Red Team Lead [24] |
At top cleared employers, salaries are even more competitive. For instance, Booz Allen Hamilton offers an average salary of $138,188 for OffSec-certified professionals, while Leidos averages around $135,000 – and these figures are based on OSCP holders [25]. With OSCE³ certification, you can command even higher pay for roles requiring advanced exploit development and leadership in red team operations.
Staying Competitive in the Cleared Cybersecurity Industry
The cybersecurity landscape evolves rapidly, and staying competitive means continuously upgrading your skills. The OSCE³ certification ensures you remain ahead of the curve, equipping you to tackle sophisticated threats and navigate advancements in defensive technologies. Your ability to bypass modern defenses and perform detailed source code analysis makes you an asset for leadership roles in high-demand areas [23].
"The OSCE³ is a symbol of determination, knowledge, and skill… distinguishing you as a top-tier offensive security professional." – OffSec Team [1]
Beyond immediate opportunities, OSCE³ certification lays the groundwork for long-term career growth. It prepares you for roles like Red Team Lead, Principal Security Researcher, or Offensive Security Architect. In a field where 65% of global practitioners agree certifications are the best way to demonstrate knowledge [22], this credential not only proves your expertise but also shows you can handle real-world challenges under pressure. This is a critical quality for cleared employers tasked with protecting sensitive government systems and critical national infrastructure.
Conclusion
The OSCE³ certification represents the pinnacle of offensive security credentials for cleared professionals. By mastering the advanced disciplines of OSWE, OSEP, and OSED, you join an elite group of experts who possess skills that few can claim [1][3]. This certification not only distinguishes you but also positions you as a leader in advanced offensive security.
Achieving the OSCE³ requires dedication and effort. It validates your expertise and opens doors to high-impact roles like Senior Exploit Developer, Vulnerability Researcher, and Red Team Lead. In a field where over 90% of security leaders prioritize investing in employee certifications [26], this credential can drive significant career growth and financial rewards.
The journey begins with one of the three required 300-level courses: WEB-300, PEN-300, or EXP-301. With the Learn One subscription, you gain flexible lab access and multiple exam attempts, making it easier to balance preparation with your professional commitments. Prioritize methodical enumeration, practice in realistic lab settings, and sharpen your documentation skills to meet the exam’s rigorous reporting standards.
Your OSCE³ isn’t just a badge of honor – it’s a pathway to exclusive opportunities. Maximize its value by connecting with cleared employers through Cleared Cyber Security Jobs. Upload your resume, set alerts for OSCE³-specific roles, and participate in job fairs tailored for cleared professionals. This ensures direct access to top-tier positions that recognize and reward your advanced qualifications.
With information security analyst roles projected to grow by 29% through 2034 [27], the OSCE³ certification equips you to stay ahead in the ever-evolving cybersecurity landscape. Start your journey today and secure your place among the leaders in cleared offensive security.
FAQs
What advantages does the OSCE³ certification offer for security-cleared penetration testers?
Earning the OSCE³ certification highlights a high level of skill in offensive security techniques, setting cleared professionals apart in the competitive world of cybersecurity. It proves your ability to tackle intricate challenges, enhancing both your credibility and technical reputation.
For cleared penetration testers, this certification offers more than just a credential – it can lead to opportunities for upper-level roles, improve job flexibility, and increase acknowledgment within the specialized cleared cybersecurity sector. It’s a powerful tool for career growth and staying ahead in an ever-changing industry.
How can cleared professionals prepare for the OSCE³ exam while managing their work responsibilities?
Balancing preparation for the OSCE³ exam with a hectic work schedule might seem daunting, but it’s entirely doable with some thoughtful planning. Start by crafting a structured study plan that breaks your preparation into clear, bite-sized goals. Tackling one topic or skill at a time can help you stay focused and avoid feeling swamped.
Fit study sessions into your daily routine by using early mornings, lunch breaks, or evenings. Short, consistent study periods work better than marathon sessions – regular practice keeps the material fresh without overwhelming you. Focus on quality over quantity by prioritizing hands-on exercises and labs that mirror real-world scenarios. These practical activities can make a big difference in understanding and retention.
Above all, stay disciplined but flexible. Life happens, and work demands can shift, so don’t hesitate to adjust your plan when needed. The key is steady, focused effort – not last-minute cramming. By keeping a balanced approach, you can confidently prepare for the OSCE³ while staying on top of your professional responsibilities.
What key skills and tools do I need to succeed in the OSCE³ exams?
To succeed in the OSCE³ exams, you’ll need a solid grasp of advanced penetration testing techniques. This means being skilled in areas like exploiting web applications, crafting shellcode, bypassing security features such as ASLR and DEP, and building ROP chains. These techniques are essential for navigating the complex scenarios you’ll face during the certification process.
Familiarity with tools like Kali Linux and other specialized penetration testing utilities is also crucial. Practical, hands-on experience with these tools will allow you to apply your skills effectively when it matters most. Spend time honing your problem-solving skills and working through real-world scenarios to prepare yourself for the challenges ahead.