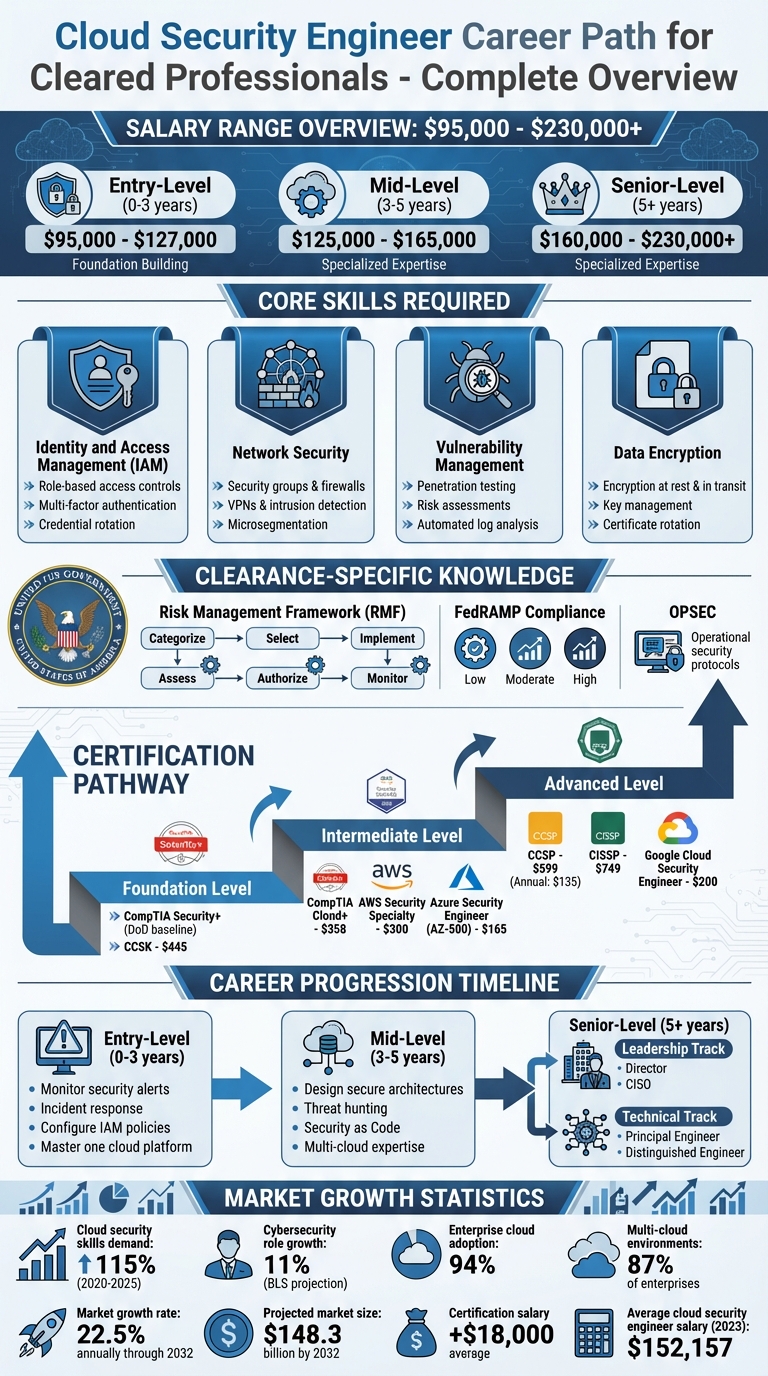
Cloud security engineers play a key role in safeguarding sensitive data and networks, especially in government and defense sectors. For professionals with security clearances, this field offers lucrative opportunities, with salaries ranging from $95,000 to $230,000+ depending on experience. Here’s what you need to know:
- Core Skills: Identity and Access Management (IAM), network security, vulnerability management, and data encryption.
- Clearance-Specific Knowledge: Familiarity with Risk Management Framework (RMF), FedRAMP compliance, and operational security (OPSEC).
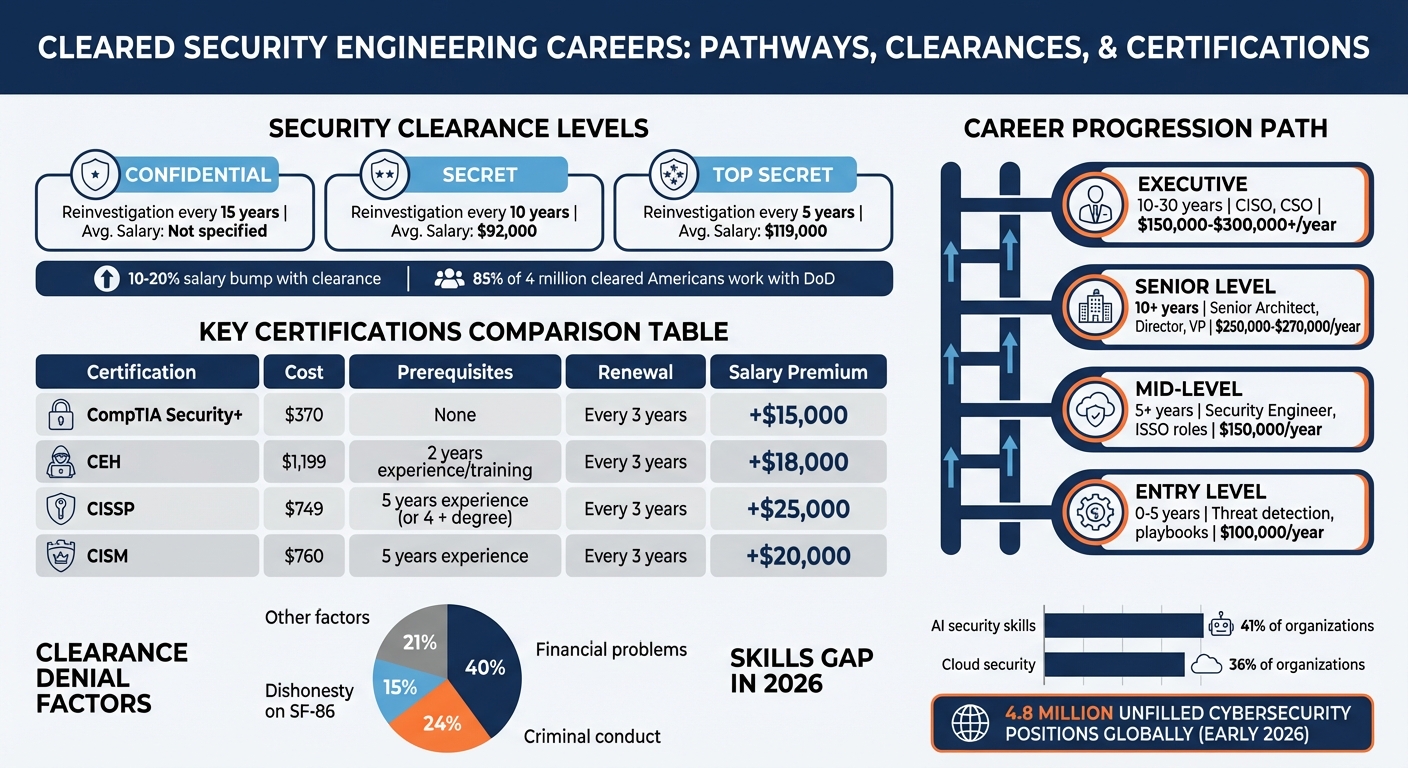
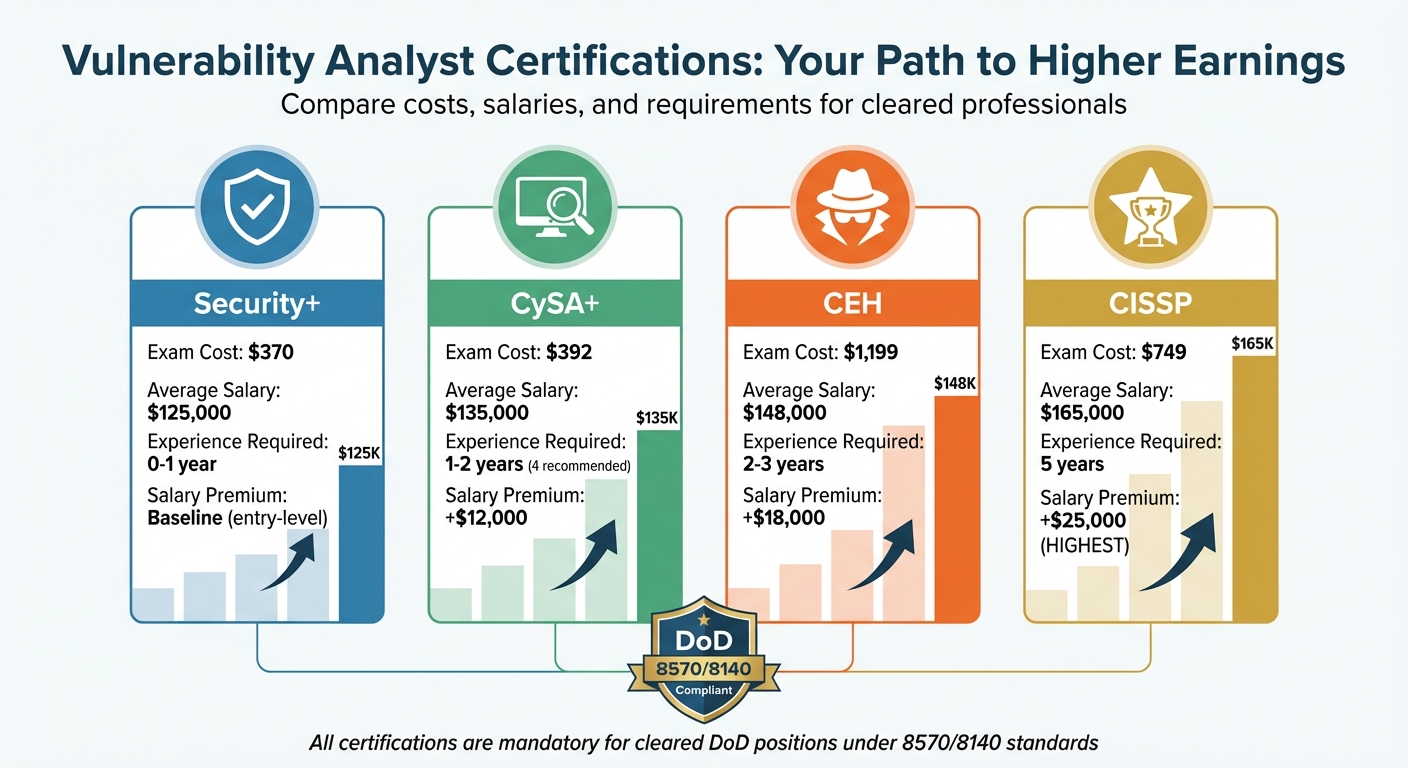
- Certifications: Start with CCSK or CompTIA Security+ for foundational knowledge, then advance to CCSP, AWS Security Specialty, or Azure Security Engineer Associate for specialized expertise.
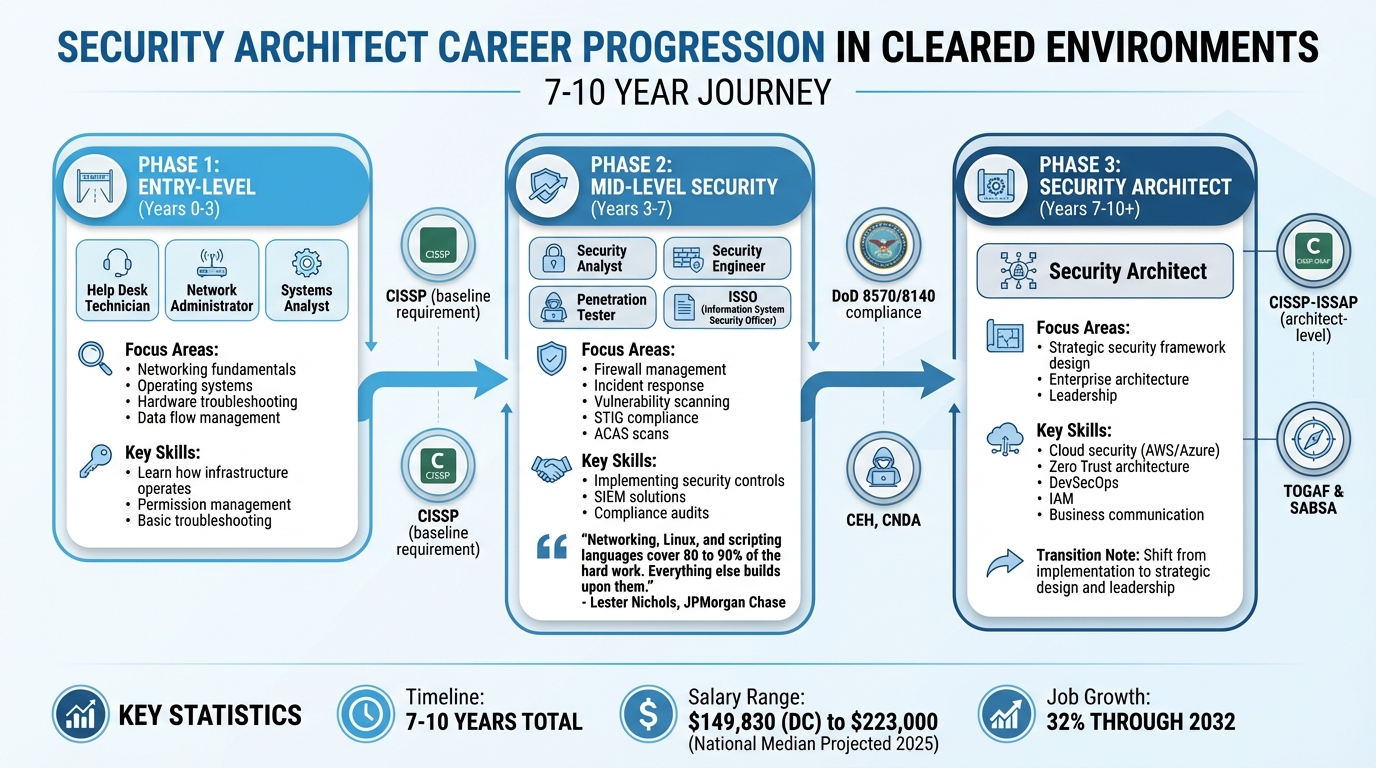
- Career Progression: Entry-level roles focus on monitoring and incident response, mid-level positions involve secure system design, and senior roles emphasize leadership or advanced technical oversight.
With government agencies rapidly adopting cloud technologies, cleared cloud security engineers are in high demand. This career path combines technical mastery with the ability to navigate strict federal compliance standards, making it ideal for those seeking impactful work in national security.
Cloud Security Engineer Career Path: Skills, Certifications, and Salary Progression
Become a Cloud Security Engineer in 2025 | THE Beginner ROADMAP (AWS & PWNED LABS)
sbb-itb-bf7aa6b
Required Skills for Cleared Cloud Security Engineers
Cleared cloud security roles demand a high level of technical expertise, combined with a deep understanding of federal compliance standards. Between 2020 and 2025, the demand for cloud technology skills surged by 115% [6]. Engineers working in classified settings must not only master commercial cloud platforms but also navigate the unique security protocols that protect national security workloads.
Core Technical Skills
Identity and Access Management (IAM) is at the heart of cloud security. With the shift away from physical offices and on-premises servers, identity has become the primary security boundary [4]. Engineers must apply the principle of least privilege effectively, managing both human users and the exponentially larger number of machine identities [4][5][6]. This includes configuring role-based access controls, enabling multi-factor authentication, and automating credential rotation across AWS, Azure, and Google Cloud Platform (GCP).
Network security in cloud environments requires expertise in setting up security groups, firewalls, private endpoints, virtual private networks (VPNs), and intrusion detection systems [5][6]. Unlike traditional perimeter-focused security, cloud security relies on software-defined networking and microsegmentation. Engineers must design systems that can isolate threats and revoke credentials instantly using event-driven automation [4].
Vulnerability management has shifted from reactive responses to proactive security engineering [4]. Regular audits, penetration testing, and risk assessments are key to identifying vulnerabilities before deployment. Engineers skilled in scripting languages like Python or PowerShell can automate log analysis and respond swiftly to suspicious activity [4][5].
Data encryption – both for stored data and data in transit – is non-negotiable [8][11]. Engineers must know how to manage encryption keys, rotate certificates, and implement encryption controls that meet federal standards. As of late 2023, cloud security engineers in the U.S. earned an average annual salary of $152,157, with top earners making over $205,000 [5]. These technical skills form the backbone of the expertise required for classified environments.
Clearance-Specific Skills
Working in classified environments involves proficiency in the Risk Management Framework (RMF), which includes six steps: Categorize, Select, Implement, Assess, Authorize, and Monitor [8][10]. Engineers need to select and implement security controls from NIST SP 800-53, ensuring compliance with federal standards like session timeouts and encryption key lengths [10].
A deep understanding of FedRAMP standards is also critical. Engineers must manage impact levels (Low, Moderate, and High), secure Provisional Authority to Operate (P-ATO) through the Joint Authorization Board (JAB) or an Agency ATO, and work with accredited Third Party Assessment Organizations (3PAOs) [9][10][12]. Unlike commercial roles, self-attestation is not allowed under FedRAMP, which requires independent validation [10]. Engineers often deal with extensive documentation, like System Security Plans (SSP), which can exceed 300 pages [10].
"FedRAMP is a compliance regime, not just a set of best practices. It demands proof, oversight, and continuous diligence." – TrustCloud [10]
For Moderate and High impact levels, ensuring that data resides in the U.S. and is accessible only to U.S. persons is essential [10]. This requires familiarity with government-specific cloud services like AWS GovCloud and Microsoft Azure Government [7]. Continuous monitoring has replaced periodic reviews, with monthly vulnerability scans and real-time reporting now standard [10][12]. These skills are vital for meeting the stringent requirements of federal compliance.
Additionally, engineers in classified roles must maintain strict operational security (OPSEC). This involves adhering to digital hygiene practices and being cautious about public-facing activities such as GitHub contributions, forum discussions, and social media posts, all of which could have national security implications [7]. Under Continuous Vetting, engineers are required to report significant life events to their Facility Security Officer (FSO) [7]. Thorough documentation is also crucial, as activities like collaborating with international researchers, attending conferences, or contributing to open-source projects are closely scrutinized during the vetting process [7].
Certifications for Cleared Cloud Security Positions
Certifications play a key role in proving your technical expertise to employers and often fulfill Department of Defense (DoD) requirements for information assurance jobs. Did you know that 70% of employers require industry certifications for cybersecurity roles? On top of that, earning one can boost your salary by an average of $18,000 in the U.S. [16]. For professionals with security clearances, certifications not only demonstrate your skills but also open doors to high-impact roles that demand both technical knowledge and compliance with strict standards.
Vendor-Neutral Certifications
If you’re just starting with cloud security, the Certificate of Cloud Security Knowledge (CCSK) is a great first step. Priced at $445 (including two exam attempts), this certification covers 12 key areas, from Cloud Governance to Incident Response [13]. The latest version, CCSK v5, now focuses on topics like Artificial Intelligence and Zero Trust strategies, phasing out older subjects like IoT [13]. The exam is open-book, includes 60 questions, and takes two hours to complete [13].
"The CCSK certificate is highly regarded as the benchmark for cloud security expertise. It provides a comprehensive and unbiased understanding of how to effectively secure data in the cloud." – Cloud Security Alliance [13]
For experienced professionals, the Certified Cloud Security Professional (CCSP) is a top-tier choice. At $599 (plus a $135 annual maintenance fee), this certification dives into enterprise-level cloud architecture, design, operations, and service orchestration [16][19]. The exam includes 125-150 questions and takes 3-4 hours [14][18]. If you already hold a CISSP, you’re automatically eligible for the CCSP [18]. Approved under DoDM 8140.03, the CCSP is especially valuable for cleared positions [14].
Other great vendor-neutral options include:
- CompTIA Cloud+: Focuses on planning and automating secure cloud environments. Cost: $358 [16].
- GIAC Cloud Security Automation (GCSA): Centers on DevSecOps and open-source tools. Cost: $949 [16].
- Certified Cloud Security Engineer (CCSE): Combines vendor-neutral concepts with hands-on skills for AWS, Azure, and GCP. This certification is particularly relevant since 87% of enterprises use multi-cloud environments [17].
Cloud Platform Certifications
Platform-specific certifications are just as important, especially when working with the most widely used cloud providers in government settings.
The AWS Certified Security – Specialty (SCS-C02) is tailored for securing AWS environments. It covers areas like incident response, logging, monitoring, IAM, and data protection [20][22]. The certification costs $300, includes 65 questions, and requires a score of at least 750 out of 1,000 to pass [20][22]. Demand for this certification is growing fast – job postings requiring it increased by 73% between October 2021 and September 2022 – and professionals holding it earn an average annual salary of $203,597 [20][22].
If your focus is on Microsoft environments, the Microsoft Certified: Azure Security Engineer Associate (AZ-500) is a solid option. At $165, it emphasizes implementing security controls, managing identity and access, and securing data in both cloud and hybrid setups [22]. The certification is valid for one year and is highly valued in government roles [22].
For Google Cloud experts, the Google Professional Cloud Security Engineer certification is worth considering. It costs $200 and tests your ability to design and manage secure infrastructure on GCP, with a focus on multi-cloud strategies and Kubernetes security [15][19][22]. Although GCP expertise is less common, it commands higher salaries due to the scarcity of skilled professionals [22]. Most candidates benefit from having 1-2 years of practical experience before attempting this exam [22].
Baseline and DoD Certifications
To meet DoD baseline requirements, CompTIA Security+ CE is the standard entry-level certification [21]. For roles like SOC Analyst or Incident Responder, the CompTIA CySA+ (around $392) fulfills CSSP Analyst requirements [21].
"CySA+ satisfies DoD 8570 baseline requirements for CSSP Analyst roles, which opens up government contracting jobs – the most reliable place to get a job." – CloudJobs Insights [21]
For senior-level positions, the CISSP is a must-have. At $749, it’s a gateway to management and architect roles, often with salaries exceeding $150,000 [21]. With Trusted Workforce 2.0 streamlining clearance maintenance through real-time checks, keeping your certifications up to date is more important than ever [7]. Your choice of certification should align with the cloud provider your target agency uses – AWS Security Specialty for AWS environments or AZ-500 for Microsoft-heavy organizations [21][22].
These certifications are essential for building a successful career in cleared cloud security, ensuring you’re prepared to meet the demands of government roles.
Career Path and Experience Levels
The cleared cloud security field offers a structured career progression with clear opportunities for salary growth. Entry-level professionals typically earn between $95,000–$127,000, mid-level engineers see salaries of $125,000–$165,000, and senior roles can command $160,000–$230,000+ [3][23]. With the U.S. Bureau of Labor Statistics predicting 11% growth in cybersecurity roles – outpacing many other fields – and around 94% of enterprises now relying on cloud services, the demand for skilled professionals is rapidly increasing [23][24]. Holding a security clearance can further accelerate career advancement in these defined roles. Let’s break down the journey from entry-level to senior positions.
Entry-Level Positions (0-3 Years)
In the early stages of your career, the focus is on building technical skills and gaining hands-on experience. Key responsibilities include monitoring security alerts, investigating potential threats, and resolving incidents by following established protocols. You’ll also work on configuring IAM (Identity and Access Management) policies, implementing network controls, and ensuring compliance with security standards.
At this stage, mastering one major cloud platform – most commonly AWS – is essential. Developing scripting skills in languages like Python or Go is equally important, as these are used to automate security tasks and create custom detection rules.
"Cloud security spans across just about every domain in security. Cloud engineers are deploying tools in those domains, working with internal and external clients." – Joe South, Infosec Instructor [23]
As your technical foundation strengthens, your role will naturally evolve to include more proactive responsibilities, such as designing secure systems and managing risks.
Mid-Level Positions (3-5 Years)
Mid-level roles mark a shift from reactive tasks to proactive security design and implementation. At this stage, you’ll take on responsibilities like designing secure architectures, implementing network segmentation, and conducting security assessments across multiple cloud platforms. Your work will likely include advanced tasks such as threat hunting, malware analysis, and digital forensics, requiring a deeper level of technical expertise.
One emerging trend at this level is Security as Code, which emphasizes automation over manual configurations. You’ll use tools like Infrastructure as Code (IaC) to automate compliance checks and security processes, making your work more efficient and scalable.
With these expanded responsibilities, mid-level roles serve as a critical bridge to senior leadership positions.
Senior-Level Positions (5+ Years)
Senior roles combine technical expertise with strategic oversight. As a senior professional, you’ll guide risk mitigation efforts for complex challenges while acting as a subject matter expert (SME). Key responsibilities include advanced threat modeling, managing relationships with high-level stakeholders, and leading enterprise-wide initiatives such as implementing Zero Trust frameworks.
At this stage, you can choose between two main career tracks: leadership roles like Director or Chief Information Security Officer (CISO), or technical roles such as Principal or Distinguished Engineer. Leadership positions focus on team management and organizational strategy, while technical roles emphasize long-term scalability and security-first design.
Mentorship also becomes a key aspect of senior roles. You’ll help develop junior talent and influence organizational security policies, ensuring your expertise benefits the broader team.
"Accomplishments, no matter how impressive, have limited impact if they go unnoticed." – Bianca Dunlap, Learning and Development Program Manager, AWS Security [1]
Using Your Security Clearance to Find Cloud Security Jobs
Your security clearance can give you a real edge when applying for specialized cloud security roles. By aligning your clearance level with the right opportunities, you can streamline your job search and focus on roles that match your skills, certifications, and clearance status.
How Clearance Levels Align with Roles
Different clearance levels open doors to specific types of cloud security work. For example, Secret clearance qualifies you for roles involving less sensitive systems, often with defense contractors or federal agencies managing day-to-day infrastructure projects. Meanwhile, Top Secret clearance is needed for positions tied to intelligence agencies, advanced defense programs, or national security initiatives where cloud systems handle highly sensitive data. If you hold a TS/SCI clearance, you’ll be eligible for the most sensitive roles, such as supporting intelligence community cloud migrations, working on special access programs, or managing compartmented information systems.
The nature of the work also changes with the clearance level. Secret-cleared roles might focus on implementing security measures for general government cloud platforms. In contrast, TS/SCI positions often involve designing secure architectures for classified environments or managing security for intelligence workloads. Location can also play a big role – just in the Washington, D.C. area, there are over 200 cloud security engineer positions requiring clearance, especially near government hubs and contractor offices [25]. Once you understand how your clearance fits into these roles, you can start focusing on where to find them.
Finding Jobs on Cleared Cyber Security Jobs
Leverage your clearance to target roles directly through platforms like Cleared Cyber Security Jobs. This site simplifies your search by listing positions specifically for candidates with active clearances. Start by creating a profile and uploading your resume, making sure to highlight your cloud certifications and clearance level prominently. Use search filters to narrow down roles based on your clearance type, salary expectations, and preferred cloud platforms like AWS, Azure, or Google Cloud.
Set up job alerts with keywords such as "cloud security engineer", "AWS security", or "cloud architect", combined with your clearance level. These alerts will notify you as soon as new roles matching your qualifications are posted. The platform also hosts job fairs where you can meet hiring managers from government agencies and defense contractors. These events are a great way to showcase your technical skills and discuss roles in person – something that goes beyond what’s on your resume.
Since Cleared Cyber Security Jobs works exclusively with direct-hire employers rather than staffing firms, you’ll connect directly with organizations looking for cloud security talent. This approach not only speeds up the hiring process but also ensures you get a clearer picture of the role requirements, especially for positions that demand specific cloud platform expertise or Department of Defense (DoD) certifications.
Advancing Your Cloud Security Career
For professionals with security clearances, staying on top of your game in cloud security means committing to continuous learning. Cloud providers roll out new security features and services almost weekly, so it’s crucial to regularly review your platform’s official security updates. Focusing on mastering these updates first will give you a solid foundation before you expand your expertise to include multi-cloud environments [3].
Once you’re confident with the technical side, it’s time to broaden your horizons through networking. Engaging with peers and mentors in niche communities, such as the fwd:cloudsec Slack group or CloudSecDocs, can significantly boost your career trajectory [3]. For those working in classified environments, connecting with others who share similar challenges can be especially helpful. Beau Guidry, Global Field Operations Manager at AWS, offers this advice:
"Flex your network! Find a mentor to help you navigate the process and understand how your skills can translate to an AWS role" [2].
To align with industry trends, focus on areas like "security as code" and aim for advanced certifications such as AWS Security Specialty, CCSP, or CKS to showcase your expertise. The cloud security market is expected to grow at an annual rate of 22.5% through 2032, potentially reaching $148.3 billion [26]. With more organizations adopting tools like Terraform and Pulumi, there’s a growing demand for cloud-native skills, particularly in container security, Kubernetes, and zero-trust architectures [3].
Building a public portfolio is another way to stand out. Contribute to open-source cloud security projects or publish technical blog posts on platforms like GitHub. This not only showcases your skills but also gives recruiters and hiring managers a tangible sense of your capabilities – something a resume can’t always capture. Free training resources are also a great way to explore emerging areas like cloud penetration testing or AI-driven threat detection [26][23]. As Joe South, Senior Cloud Engineer, puts it:
"Every person you look up to in a specific field at one point knew nothing and was a beginner. You, too, can change your life starting from nothing" [23].
Taking these steps not only enhances your technical abilities but also prepares you for leadership opportunities. Practice discussing your cleared experience in at least 10 mock interviews focused on leadership and behavioral scenarios [2]. This preparation will help you clearly demonstrate how your background can contribute to impactful cloud security solutions. By aligning your goals with the public sector’s push for digital transformation and national security innovation, you’ll position yourself for a career that’s both fulfilling and forward-moving.
Conclusion
Building a career as a cleared cloud security engineer requires a blend of technical know-how, industry-recognized certifications, and the ability to leverage your security clearance for unique opportunities. With median annual salaries hovering around $122,500 and the potential to earn over $160,000 at the high end [24], the financial incentives reflect the specialized skills and responsibilities involved.
A security clearance unlocks access to roles that are vital to supporting national security efforts. As Beau Guidry, Global Field Operations Manager at AWS, puts it:
"I think purpose and impact are absolutely essential to job satisfaction and I think it’s a real attraction to cleared individuals looking for work with AWS" [2].
This combination of purpose-driven work and the fast-paced evolution of cloud technology makes this career path both impactful and rewarding.
To stay competitive, focus on sharpening your skills in areas like DevSecOps integration, zero-trust architecture, and multi-cloud strategies. Earning certifications such as AWS Security Specialty, CCSP, or CKS demonstrates your dedication to staying at the forefront of the field. Additionally, showcasing your expertise through open-source projects or technical writing can make you stand out to employers.
For veterans, tools like the Military Skills Translator can help align military experience – such as secure communications or information assurance – with civilian cloud security roles [2]. The ability to remain calm under pressure, developed through military service, is a strength that directly applies to the high-stakes nature of cloud security.
FAQs
Which clearance level do I need for cloud security engineer roles?
The clearance level needed for cloud security engineer roles depends on the specific job and employer. Typical levels include Secret, Top Secret, and TS/SCI. Positions supporting defense or intelligence agencies often require Top Secret or TS/SCI clearances, as these allow access to highly sensitive information. The exact clearance level is determined by the security needs of the job and the agency or project it supports.
What projects can I share publicly without risking OPSEC or my clearance?
When sharing projects, focus on those that demonstrate your ability to tackle key cloud security challenges. Examples include detecting cloud misconfigurations, securing identities and permissions, monitoring logs for anomalies, investigating security incidents, and enforcing security controls in active cloud environments. These types of projects not only showcase hands-on expertise but also highlight your practical knowledge of cloud security practices.
Just remember to prioritize OPSEC (operational security) and safeguard any sensitive information or clearance-related details while presenting your work.
How do I move from Security+ to a cloud security role fast?
To move efficiently from Security+ to a cloud security role, start by diving into the major cloud platforms – AWS, Azure, or GCP – and familiarize yourself with infrastructure-as-code tools like Terraform or CloudFormation. Earning certifications such as the AWS Certified Security Specialty, Azure Security Engineer (AZ-500), or CCSP will also strengthen your credentials. Pair this with practical, hands-on experience in cloud security and automation to build on your Security+ foundation. With focused effort, you can aim to achieve this transition in 12 to 18 months.