The eJPT (eLearnSecurity Junior Penetration Tester) certification is a hands-on, entry-level credential designed to validate penetration testing skills. It’s ideal for professionals in government or defense sectors with security clearances, as it focuses on practical techniques like network penetration, auditing, and web application testing. The exam costs $249, includes three months of training, and is valid for three years.
Key Highlights:
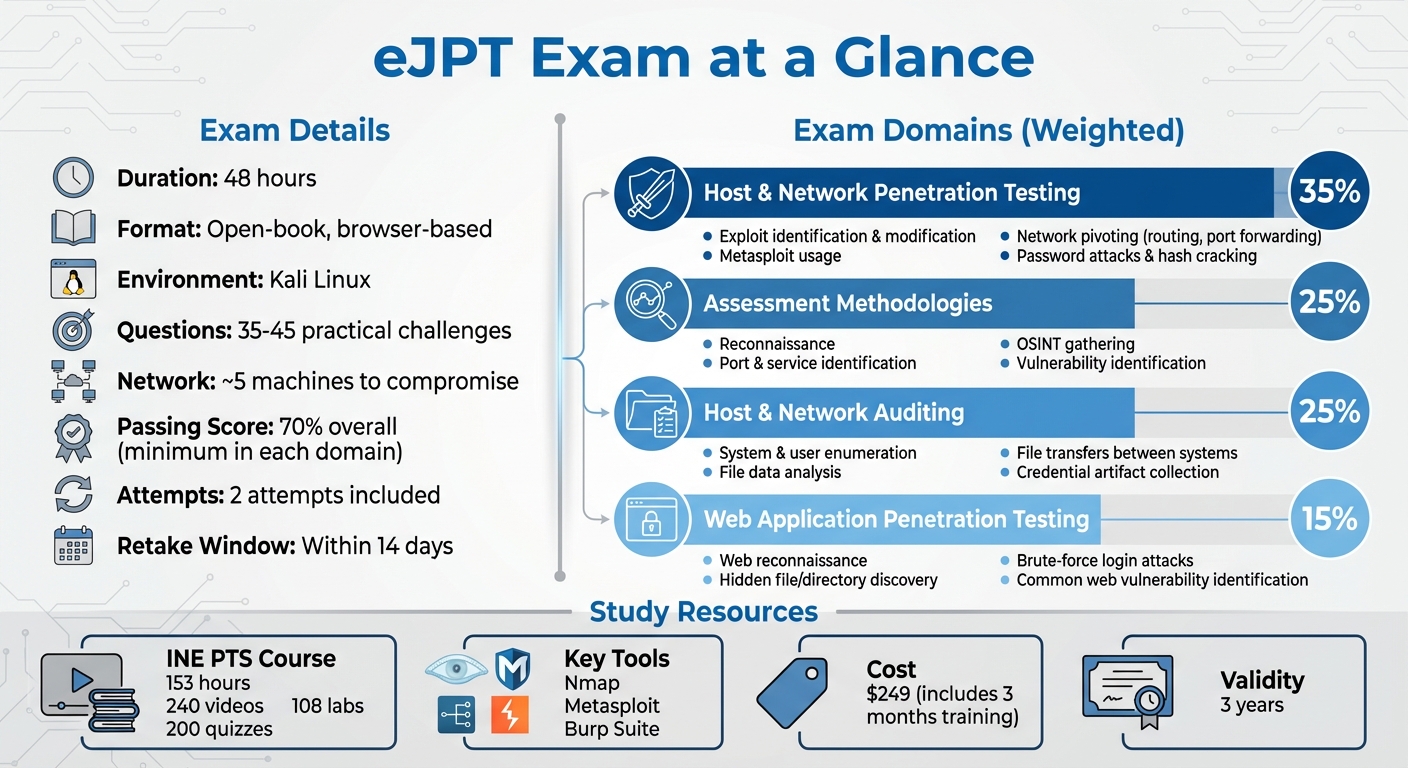
- Exam Structure: 48-hour, open-book, browser-based test with 35–45 questions.
- Domains Covered:
- Host & Network Penetration Testing (35%)
- Assessment Methodologies (25%)
- Host & Network Auditing (25%)
- Web Application Penetration Testing (15%)
- Study Resources: INE’s Penetration Testing Student (PTS) course (153 hours, 108 labs).
- Tools to Master: Nmap, Metasploit, Burp Suite, and pivoting techniques.
The certification is a stepping stone to more advanced credentials (e.g., eCPPT, OSCP) and aligns well with the growing demand for penetration testers. It also helps cleared professionals transition into offensive security roles or advance their careers.
This guide explains how the eJPT equips you with practical penetration testing skills, prepares you for cleared cybersecurity roles, and boosts your career prospects in a growing field.
The Definitive 2026 eJPT Certification Guide | Pass the eLearnSecurity Penetration Tester Exam
sbb-itb-bf7aa6b
eJPT Exam Structure and Content Areas
eJPT Certification Exam Structure and Domain Breakdown
Exam Format and Key Details
The eJPT exam is a hands-on, open-book test conducted entirely within a browser-based Kali Linux environment. You’ll navigate a simulated network of around five machines, tackling tasks like enumeration, exploitation, pivoting, and privilege escalation to complete 35 practical challenges[6]. The focus here is on applying penetration testing skills rather than memorizing facts.
"Rather than questions designed to test how well you have memorized information, these questions assess your ability to actively perform the tasks and processes of a Junior Penetration Tester." – The INE Team[6]
To pass, you need an overall score of at least 70%, with minimum requirements in each of the four domains. Your exam voucher includes two attempts, but if you fail, the retake must be used within 14 days[8]. The exam also employs dynamic and static flagging technologies to ensure a unique experience for every candidate[6].
Understanding this practical format is essential to navigating the exam’s weighted content areas effectively.
Core Domains of the eJPT Exam
The exam evaluates your skills across four key domains, each weighted according to its importance in penetration testing:
- Host and Network Penetration Testing (35%)
This domain focuses on tasks like identifying and modifying exploits, using tools such as Metasploit, pivoting through networks with routing and port forwarding, conducting password attacks, and cracking hashes[6]. - Assessment Methodologies (25%)
Here, you’ll demonstrate your ability to perform reconnaissance, which includes locating endpoints, identifying ports and services, OS fingerprinting, gathering open-source intelligence (like emails or technical details), and spotting vulnerabilities[6]. - Host and Networking Auditing (25%)
This section assesses your skill in enumerating system and user information, analyzing target file data, transferring files between systems, and collecting credential artifacts[6]. - Web Application Penetration Testing (15%)
Focused on web reconnaissance, this domain involves finding hidden files and directories, performing brute-force login attacks, and identifying common web vulnerabilities[6].
A strong grasp of pivoting techniques, such as adding routes and using port forwarding, is critical to accessing all targets during the exam[2].
How to Prepare for the eJPT Exam as a Cleared Professional
Prerequisites and Study Resources
The Penetration Testing Student (PTS) learning path from INE is your main resource for exam preparation. This comprehensive course includes 240 videos, 200 quizzes, and 108 labs, adding up to 153 hours of material[2].
"Everything you need to pass the eJPT exam is covered in the Penetration Testing Student (PTS) learning path on INE." – Lily Clark, Client Success Representative, INE[9]
For additional practice, TryHackMe provides a great platform for around $10/month. Rooms such as "Basic Pentesting", "RootMe", and "Simple CTF" are particularly useful for sharpening your skills with tools like Nmap, Burp Suite, and Metasploit[9]. To further enhance your learning, John Hammond’s YouTube channel offers practical demonstrations of Linux workflows and penetration testing techniques, making it an excellent complement to your formal studies.
Once you’ve gathered these resources, the next step is to create a structured and achievable study plan.
Creating a Study Plan
Given the 153 hours of course material and your professional obligations, a well-thought-out study schedule is key. Use SMART goals (Specific, Measurable, Achievable, Relevant, and Time-bound) to divide your study time into manageable chunks that fit around your work and clearance responsibilities[9]. Tools like Google Sheets can help you map out study sessions while keeping track of work deadlines and personal commitments, reducing the risk of burnout.
"For each lab you do, create a report for yourself that includes common commands for the tool or technique you are learning… Do this for every lab." – Lily Clark, Client Success Representative, INE[9]
Structure your study sessions around the exam’s core areas: Host and Network Penetration Testing (35%), Assessment Methodologies (25%), Host and Network Auditing (25%), and Web Application Penetration Testing (15%)[5][6]. If you encounter a challenging concept, keep moving through the material – hands-on labs will help reinforce your understanding over time.
Once your study plan is in place, it’s time to focus on mastering the tools and techniques.
Tools and Practice Labs
Proficiency with the tools highlighted in the Host and Network Penetration Testing and Web Application Testing sections is essential. The exam’s browser-based lab environment eliminates the need for complex installations, but you should still focus on the "Big Three" tools: Nmap for reconnaissance, Metasploit for exploitation, and Burp Suite for web application testing[9]. Practice pivoting techniques, such as adding routes and port forwarding, to navigate scenarios effectively during the exam[2].
Document your lab work thoroughly. Use note-taking tools like CherryTree or Obsidian to organize key commands and screenshots by exam domains[4]. This documentation becomes an invaluable reference during the 48-hour exam period.
Using eJPT Skills in Cleared Cybersecurity Roles
Practical Applications in Penetration Testing
The skills covered in the eJPT certification are not just exam material – they translate directly into tasks you’ll encounter in cleared cybersecurity roles.
For example, the certification teaches network traversal and pivoting, essential techniques for navigating segmented networks in classified environments [1]. Many classified systems are divided into isolated enclaves, requiring you to add routes and use port forwarding to move laterally through these restricted zones.
Another critical area is vulnerability identification and exploitation. The eJPT validates your ability to pinpoint vulnerabilities in services and web applications, assess their severity, and exploit them using tools like Metasploit [1]. In cleared roles, this means you’ll be responsible for evaluating internal systems, identifying weaknesses, and creating detailed reports that meet government documentation standards [8].
The certification also emphasizes enumeration skills – gathering system information, user accounts, and network details – which is vital for internal security audits [1]. These audits ensure compliance with security protocols and help detect unauthorized access points within sensitive environments.
These technical capabilities don’t just make you more effective – they also build the confidence needed to tackle the challenges of cleared cybersecurity work.
Building Confidence in Cleared Workflows
The eJPT doesn’t just teach technical skills; it also helps you develop a workflow that mirrors real-world penetration testing scenarios.
The hands-on 48-hour lab environment of the exam is designed to simulate actual testing conditions. You’ll practice documenting technical findings with evidence [8], a skill directly applicable when preparing vulnerability reports for security officers or program managers in cleared operations.
"The eJPT is more than a certification – it’s a confidence builder. Whether you’re aiming for a career in ethical hacking or want to understand better how networks are attacked and defended, passing this exam will open doors." – Evan Isaac, Lead Technical Writer [2]
Through the eJPT, you’ll refine a methodical approach that starts with reconnaissance and progresses through exploitation to detailed reporting. This structured framework ensures you can systematically identify live endpoints, open ports, and services [1]. By reducing guesswork, it helps you focus on uncovering critical vulnerabilities without overlooking key details.
Using eJPT for Career Growth on Cleared Cyber Security Jobs
Highlighting Your Certification on Cybersecjobs.com
The eJPT certification can significantly enhance your visibility on Cleared Cyber Security Jobs – especially when highlighted effectively. This 48-hour practical exam mirrors real-world scenarios [2][7], making it stand out compared to theory-heavy credentials.
To maximize its impact, emphasize the four key domains it covers: Host and Network Penetration Testing, Assessment Methodologies, Host and Network Auditing, and Web Application Penetration Testing. These terms are often used by recruiters searching for junior penetration testers, so including them in your profile can boost your chances of being noticed. Additionally, list tools like Metasploit, Nmap, and Hashcat in your skills section, and mention your expertise in pivoting (such as adding routes and port forwarding). This demonstrates your ability to navigate segmented networks – an essential skill for classified environments with complex internal infrastructures.
In your profile summary, describe the eJPT as a practical, hands-on certification. This phrasing appeals to hiring managers who prioritize technical skills over theoretical knowledge. Also, highlight your ability to produce detailed technical reports, which aligns with the workflow standards in cleared environments.
Once your certification is prominently displayed, ensure your technical skills align with employer expectations for cleared cybersecurity roles.
Matching eJPT Skills with Employer Requirements
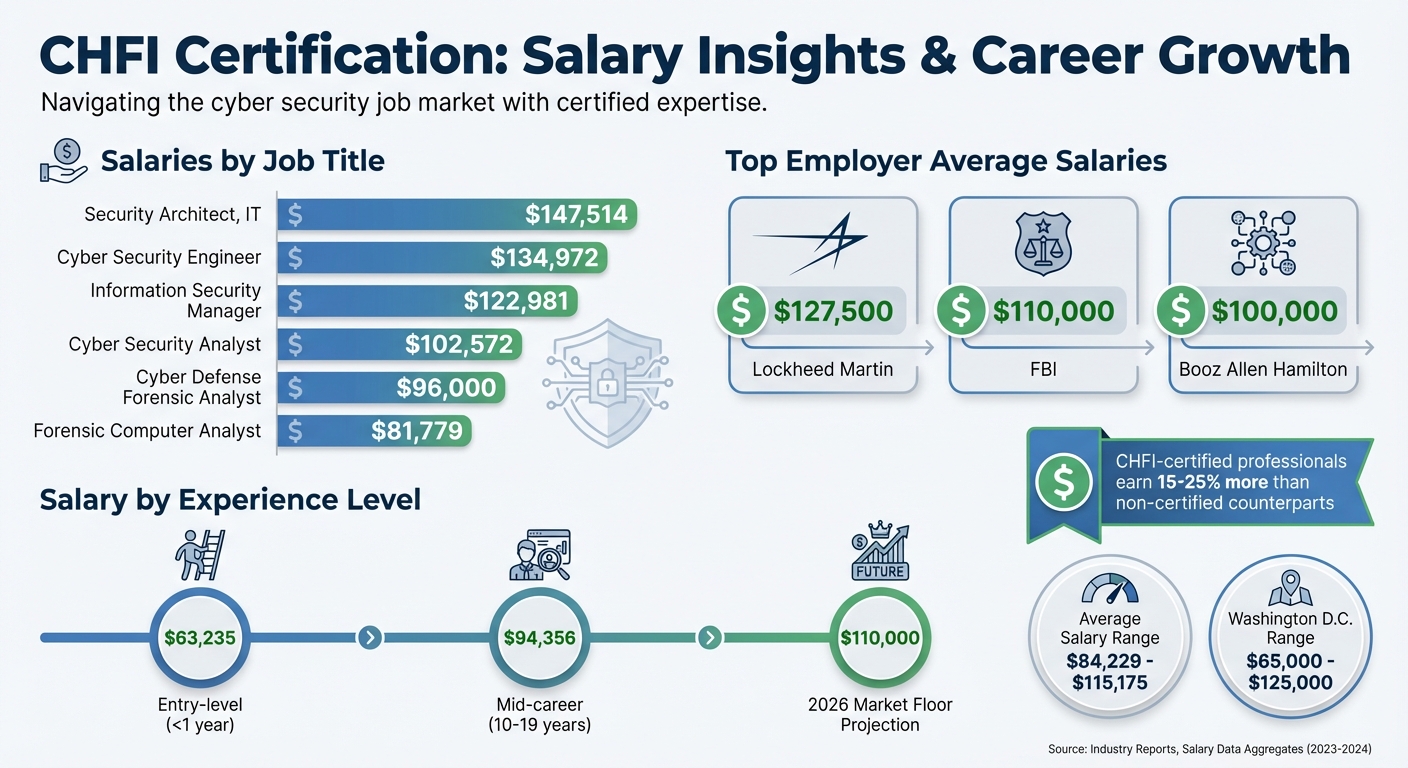
Employers value candidates who showcase both certifications and real-world skills like OSINT, vulnerability identification, and exploitation. The eJPT aligns perfectly with these needs, making it a strong asset for cleared penetration testing roles. With penetration testing jobs expected to grow by nearly 35,000 positions by 2031 [3], and junior penetration testers earning an average salary of $87,105 [3], the certification positions you for a growing field with competitive pay.
When applying through Cleared Cyber Security Jobs, reference your eJPT skills in your resume and cover letter. Highlight its focus on the entire penetration testing lifecycle – from reconnaissance to exploitation and reporting. This shows that you not only understand technical methodologies but also possess the practical expertise required for government and defense sector roles.
The eJPT also serves as a gateway to more advanced certifications like the eCPPT or OSCP, which are often prerequisites for mid-to-senior-level cleared positions. By presenting the eJPT as a foundational step in your career journey, you demonstrate a commitment to professional development and readiness to tackle more complex security challenges in the future.
Conclusion
The eJPT certification offers a practical and respected credential for entry-level penetration testers, especially those pursuing opportunities in government or defense sectors. With demand increasing in this competitive field [3], earning this certification can help set you apart and pave the way for career growth.
The certification’s hands-on focus delivers clear career advantages. As Evan Isaac, Lead Technical Writer at MRE Security, explains:
"The eJPT is more than a certification – it’s a confidence builder. Whether you’re aiming for a career in ethical hacking or want to understand better how networks are attacked and defended, passing this exam will create career opportunities" [2].
Affordable and accessible, the eJPT also serves as a stepping stone toward more advanced certifications like the eCPPT or OSCP.
To make the most of this opportunity, craft a study plan targeting the four core areas – Host and Network Penetration Testing, Assessment Methodologies, Host and Network Auditing, and Web Application Penetration Testing. Practice essential techniques like pivoting and thoroughly document your work to highlight your skills on your professional profile.
The eJPT equips you with the practical abilities that matter most in this field, providing the perfect starting point for your journey as a penetration tester.
FAQs
How hard is the eJPT exam for beginners?
The eJPT exam is tailored for beginners, emphasizing hands-on, entry-level skills. With the right preparation – like completing the suggested coursework and practicing tools such as Nmap – many candidates find it approachable. Key areas to focus on include information gathering, vulnerability assessment, and basic exploitation techniques. While having some technical background can be helpful, the exam’s practical format and clear-cut questions make it a solid starting point for newcomers who are committed to consistent study.
What should I practice most before the eJPT?
To excel in penetration testing, it’s crucial to focus on applying core methodologies effectively. This includes mastering information gathering, vulnerability assessment, exploitation, and post-exploitation techniques. These steps form the backbone of any successful penetration test.
Key skills to develop include:
- Using tools like Nmap: Learn to map networks, identify open ports, and gather essential details about target systems.
- Web application testing: Understand how to uncover vulnerabilities in web applications, such as SQL injection or cross-site scripting (XSS).
- Leveraging Metasploit: Gain expertise in using this powerful framework for exploit development and post-exploitation activities.
Beyond tools, practice is everything. Spend time identifying and modifying exploits, conducting host and network audits, and working through real-world scenarios. This hands-on experience helps bridge the gap between theory and application.
Don’t overlook the importance of hands-on labs. Familiarity with the exam’s practical environment can make a significant difference. These labs allow you to simulate realistic attack scenarios, giving you the confidence and skills needed for success.
How can eJPT help me get cleared pen test work?
The eJPT certification showcases your practical abilities and core understanding of offensive security, making it a strong credential for entry-level penetration testing positions. It focuses on key areas such as assessment techniques, host and network auditing, and testing web applications.
By earning this hands-on certification, you demonstrate to employers that you can effectively identify vulnerabilities and perform penetration tests. This is especially valuable for roles in sensitive cybersecurity environments, where proven skills are essential.