Digital forensics examiners with security clearances play a critical role in investigating cyberattacks, insider threats, and national security cases. These professionals analyze digital evidence from devices, networks, and cloud systems to support federal agencies like the FBI, NSA, DHS, and DoD. With cybercrime increasing, demand for these roles is high, offering salaries starting at $53,000 and reaching over $100,000 for those with advanced skills and clearances.
Key Takeaways:
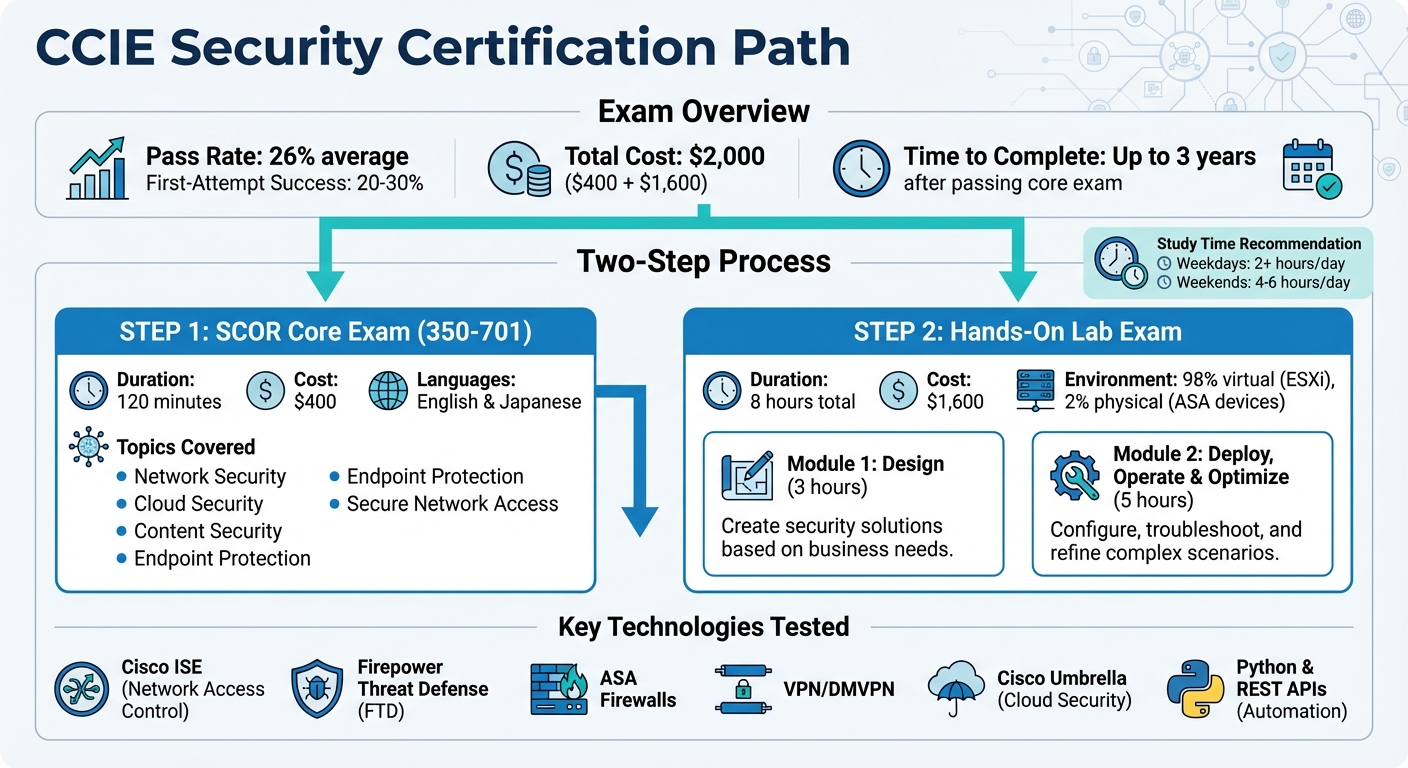
- Certifications Matter: GIAC (GCFE, GCFA), CFCE, and EnCE are top certifications to boost career prospects and earning potential.
- Tools of the Trade: Proficiency in forensic tools like EnCase, FTK, and Cellebrite is essential.
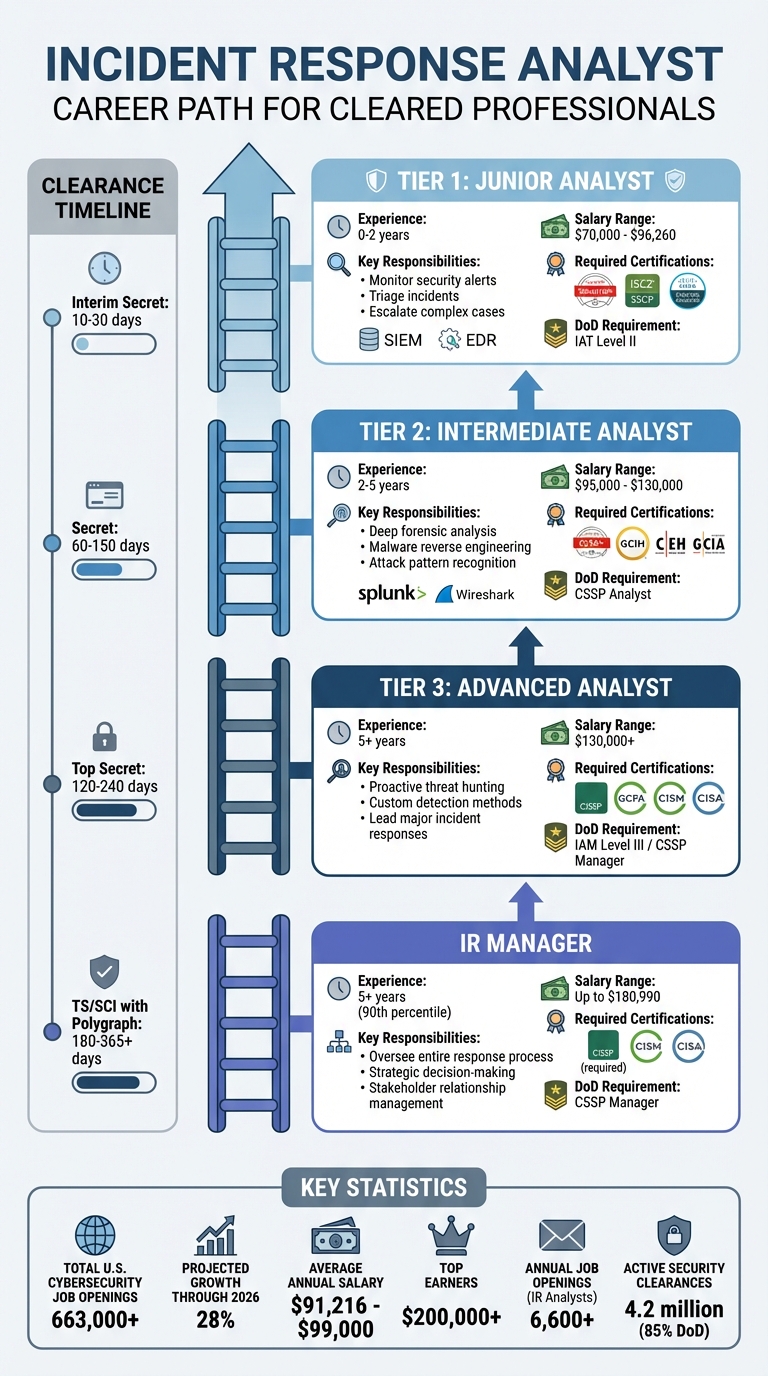
- Career Progression: Entry-level salaries range from $60,000 to $80,000, while senior roles can exceed $145,000, especially with specialized expertise.
- Security Clearance: Highlighting your clearance (e.g., Secret, TS/SCI) is vital for accessing classified roles and increasing job opportunities.
Whether you’re starting out or aiming for senior roles, combining technical expertise, certifications, and clearance can lead to a lucrative and impactful career in digital forensics.
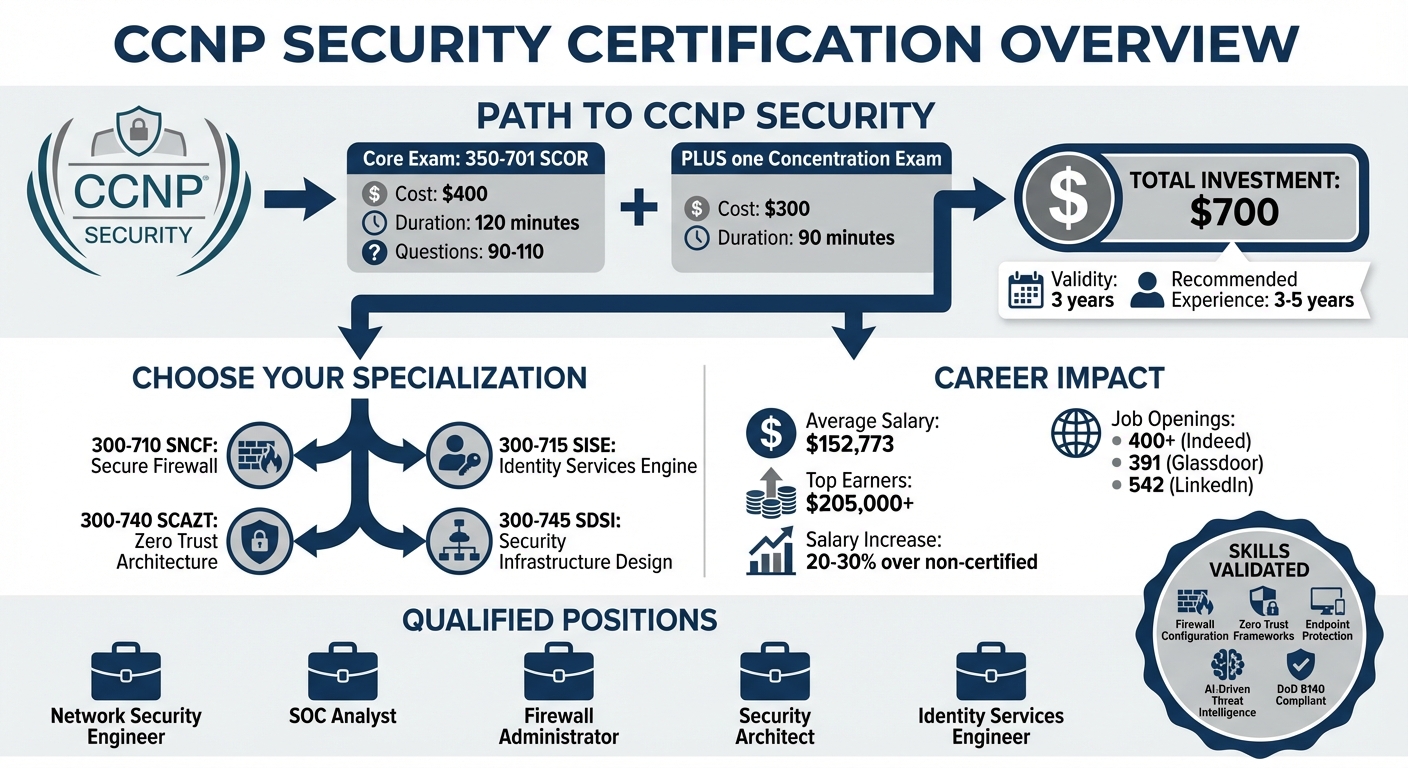
Digital Forensics Career Path: Salary Progression and Key Certifications
What Digital Forensics Examiners Do
Primary Job Duties
Digital forensics examiners specialize in recovering, analyzing, and preserving electronic evidence from devices like computers, smartphones, servers, and cloud storage systems. Their work supports criminal investigations, counterintelligence efforts, and legal cases. To ensure that this evidence is admissible in court or security reviews, examiners must follow strict protocols when handling and documenting it.
Their daily tasks often include creating exact copies of hard drives or mobile devices, analyzing file systems to locate deleted or hidden files, and meticulously recording their findings for investigators, attorneys, or intelligence analysts. In some cases, they may also testify as expert witnesses, breaking down complex technical details for judges and juries. For classified cases, their responsibilities might extend to investigating insider threats, espionage attempts, or cyberattacks targeting sensitive government systems. This role requires a deep technical skillset and provides a strong foundation for career growth.
Where Cleared Professionals Work
Cleared digital forensics examiners have opportunities in various settings, including federal agencies, defense contractors, and private firms involved in government work. Agencies like the FBI, NSA, DHS, and DoD rely on these professionals to investigate national security threats. Meanwhile, defense contractors such as Booz Allen Hamilton, Leidos, and Northrop Grumman employ examiners to support government programs on long-term contracts.
Some cleared examiners work in consulting firms that focus on cybersecurity and incident response for government clients. Others may serve as civilian employees or uniformed personnel in military branches, conducting forensic investigations on bases or in field operations. These work environments highlight the critical role that security clearances play in enabling access to sensitive investigations and projects.
Why Security Clearances Matter
Security clearances are essential for accessing classified investigations and government contracts that non-cleared professionals cannot handle. Cleared examiners are authorized to work with classified networks and sensitive intelligence during incidents like cyberattacks, ensuring the confidentiality of investigations. This exclusivity not only increases demand for their skills but also leads to better pay and job opportunities.
To maintain clearance eligibility, examiners must demonstrate personal integrity, financial responsibility, and transparency about foreign associations [3]. Background checks are rigorous because mishandling classified information could jeopardize national security. For those who qualify, security clearances open doors to specialized roles, greater job stability, and higher earning potential.
sbb-itb-bf7aa6b
Required Certifications for Cleared Digital Forensics Examiners
Top Industry Certifications
Certifications not only validate your technical expertise but also help you stand out when applying for cleared positions. Let’s break down some of the key certifications in the field:
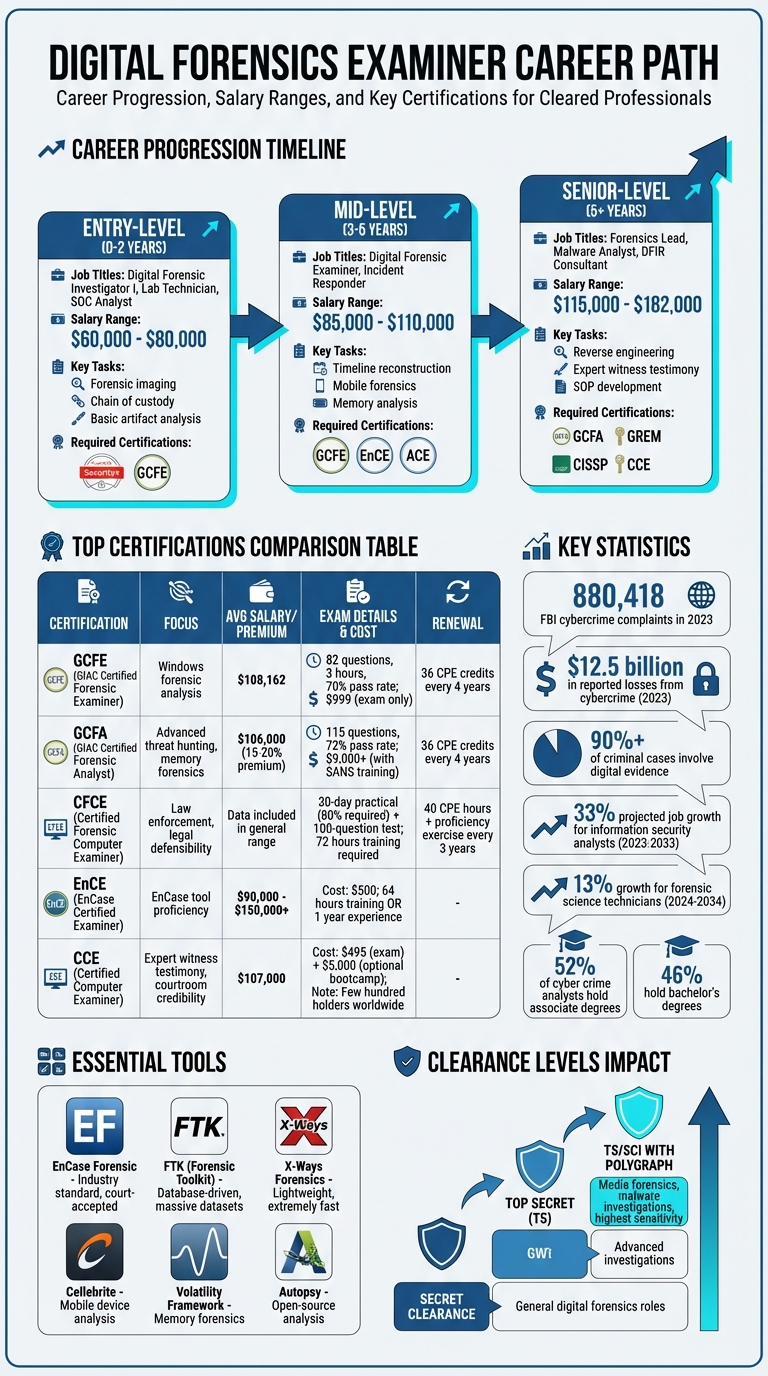
- GIAC Certified Forensic Examiner (GCFE): This certification focuses on Windows forensic analysis, covering areas like registry examination, web browser artifacts, and user activity tracking. It’s a solid choice for entry-level and mid-level analysts, with an average salary of $108,162 per year. The exam includes 82 questions, must be completed in three hours, and requires a 70% pass rate to succeed [4][6].
- GIAC Certified Forensic Analyst (GCFA): Often seen as the gold standard for senior-level roles in corporate incident response, this certification delves into advanced topics like threat hunting, memory forensics, and timeline reconstruction. The exam consists of 115 questions, and candidates need about 72% to pass. GCFA-certified professionals typically earn around $106,000 annually. Its alignment with the DoD 8140/NICE framework makes it particularly valuable for government contracting [7].
- Certified Forensic Computer Examiner (CFCE): Offered by IACIS, this certification is highly regarded in law enforcement and government roles. Candidates must pass a demanding two-part test: an 80% score on a 30-day hard-drive practical and a 100-question knowledge exam. Known for its rigorous standards and anti-cheating measures, the CFCE is often a requirement for police cyber units [5].
- Tool-Specific Certifications: These certifications focus on specific forensic tools, such as:
- EnCase Certified Examiner (EnCE): Costs $500 and is commonly required for federal contracting roles.
- AccessData Certified Examiner (ACE): Free for those with an FTK license [7].
- Certified Computer Examiner (CCE): This certification emphasizes legal defensibility and expert witness testimony, making it a great fit for those involved in court proceedings. With only a few hundred holders worldwide, it offers strong courtroom credibility and an average salary of around $107,000. The exam costs $495, and optional bootcamp training is available for approximately $5,000 [7].
These certifications not only enhance your skill set but also open doors to specialized roles in digital forensics.
How to Prepare for Certification Exams
Earning these certifications takes more than just sitting for the exam – it requires thorough preparation to ensure your skills are applicable in real-world scenarios. Here’s how you can get ready:
- Experience Requirements: While formal degrees aren’t mandatory for most certifications, relevant experience is often recommended. For example:
- Cost Considerations: Certifications can be expensive. SANS training and GIAC exam bundles, for instance, can cost over $9,000 [6]. To manage these costs, look into employer sponsorship or programs like the SANS Work Study. The GCFE exam alone costs $999, with retakes priced at $899 [6].
- Study Strategies: For GIAC open-book exams, create an alphabetized index of study materials to quickly find keywords during the test [6]. For hands-on certifications like the CFCE, focus on a "manual first, tool second" approach – use hex editors to verify findings. This method not only sharpens your skills but also builds a defensible process for legal scrutiny [5].
- Renewal Requirements: Most certifications need to be renewed every three to four years. For example:
Proper preparation ensures these certifications go beyond just a title, equipping you with the expertise to excel in the field.
Technical Skills and Tools You Need
Forensic Software and Tools
When it comes to digital investigations, having the right forensic tools in your arsenal is essential. These tools allow investigators to analyze digital evidence with speed and precision, making them indispensable for solving cases effectively.
The "Big Three" forensic tools – EnCase Forensic, Forensic Toolkit (FTK), and X-Ways Forensics – are staples in the field. They form the foundation of most computer forensics investigations [10].
- EnCase Forensic is widely recognized as the industry standard. Its scripting capability (EnScript) and the universally accepted .E01 disk imaging format make it a trusted choice in courtrooms.
"Proficiency in EnCase is almost a mandatory requirement for senior forensic roles. Its legacy and court acceptance mean that verification by EnCase is often the final word in a digital dispute" [10].
Professionals skilled in EnCase often earn salaries ranging from $90,000 to over $150,000 [10]. - Forensic Toolkit (FTK) stands out for its database-driven PostgreSQL architecture, which is ideal for managing massive datasets. This makes it a go-to option for teams where multiple analysts need simultaneous access [19,20].
- X-Ways Forensics is known for its lightweight design and exceptional speed. It’s particularly valued for its precision and deep understanding of file systems, making it a favorite for targeted investigations [10].
For specialized scenarios, other tools come into play. The Volatility Framework is a leader in memory forensics, often used to uncover active malware and encryption keys [11]. For mobile device analysis, Cellebrite is a top-tier option, offering deep data extraction and app artifact analysis [11]. Many of these commercial tools require a physical USB security dongle for licensing [10].
| Feature | FTK (Forensic Toolkit) | EnCase Forensic | X-Ways Forensics |
|---|---|---|---|
| Architecture | Database-driven (PostgreSQL) | Evidence file-based | Lightweight/Portable |
| System Resources | High (RAM & CPU intensive) | High | Very Low |
| Processing Speed | Fast (Distributed) | Moderate | Extremely Fast |
| Learning Curve | Moderate | Steep | Very Steep (Technical) |
| Best For | Massive datasets & e-discovery | Law enforcement & scripting | Speed & precision |
Mastering these tools is just the start. To excel in digital forensics, you also need a solid foundation in technical skills.
Core Technical Skills
Beyond using the tools, technical expertise plays a huge role in ensuring accurate investigations. One of the most critical skills is evidence preservation and integrity. Creating bit-by-bit forensic copies (forensic imaging) ensures that the original data remains untouched during analysis [23,24]. This is especially important given that digital evidence is a factor in most criminal cases [12].
Metadata analysis is another key skill, allowing investigators to examine file attributes and histories to piece together user activity, authorship, and modification timelines [13]. Similarly, network and log analysis is vital for identifying unauthorized access or suspicious behavior by reviewing firewall, server, and access logs [13]. The scale of cyber threats is staggering – just in 2023, the FBI’s Internet Crime Complaint Center received 880,418 complaints, with reported losses exceeding $12.5 billion [13].
Scripting skills, particularly in Python and PowerShell, are increasingly important for handling large datasets efficiently [22,23]. Investigators also need to understand anti-forensic techniques, as adversaries often use tools like VPNs, encryption, and even AI to obscure their tracks [23,24].
The field is evolving rapidly, with advancements like AI-powered forensics, which uses machine learning to identify key artifacts and detect unusual patterns in large datasets [11]. Additionally, cloud-native forensics tools now allow investigators to access data directly from platforms like Azure, AWS, and Office 365, eliminating the need for physical devices [19,20]. Remote acquisition is another game-changer, enabling evidence to be streamed back from endpoints using deployed agents [10].
Working with Classified Data
Handling classified data requires a unique set of skills and procedures. Investigators working in these environments must have a deep understanding of government regulations, secure communication protocols, and the heightened chain-of-custody standards. Even minor mistakes can jeopardize national security or render evidence inadmissible in high-profile cases.
In such settings, every action must be meticulously documented, and strict access controls are enforced to secure evidence. Many organizations provide virtual lab environments, allowing professionals to test new forensic tools without risking live classified systems.
The demand for skilled professionals in this field is growing. Employment for information security analysts, including digital forensics experts, is expected to increase by 33% between 2023 and 2033 [14]. To stay competitive, it’s important to keep up with emerging tools like advanced versions of X-Ways or platforms such as Axiom. Many employers, particularly cleared defense contractors, offer annual stipends for continuing education and certifications, ensuring their teams stay ahead in this ever-evolving field.
Education and Career Progression
Recommended Degrees and Education
A strong academic foundation in fields like cybersecurity, digital forensics, or computer engineering is key for success in cleared positions. While no single degree is mandatory, these areas provide the technical expertise needed to thrive.
To excel in digital forensics, you’ll need to understand data storage, access, and deletion at the system level. This includes proficiency in file systems such as NTFS, ext4, and APFS, as well as knowledge of computer architecture, operating systems, and scripting languages like Python, Bash/Shell, and PowerShell. These skills are essential for practical forensic work [2][15].
Statistics reveal that approximately 52% of cyber crime analysts – a closely related role – hold at least an associate degree, while 46% have earned a bachelor’s degree [15]. Employment in this field, particularly for forensic science technicians (which includes digital forensics professionals), is expected to grow by 13% between 2024 and 2034 [15]. Salaries are competitive, with digital forensics experts earning an average of $95,000 annually in 2025, and some roles offering as much as $171,000 [15].
"Many digital forensic experts are employed by governments or government contractors. For a large portion of these positions, a security clearance is necessary." – Cybersecurity Guide [15]
Keeping up with the latest developments is crucial. Organizations like the High Technology Crime Investigation Association and the Scientific Working Group on Digital Evidence (SWGDE) offer valuable resources to help professionals stay current [15].
Once you’ve built a solid educational foundation, you can start exploring entry-level roles to gain practical experience.
Getting Started with Entry-Level Roles
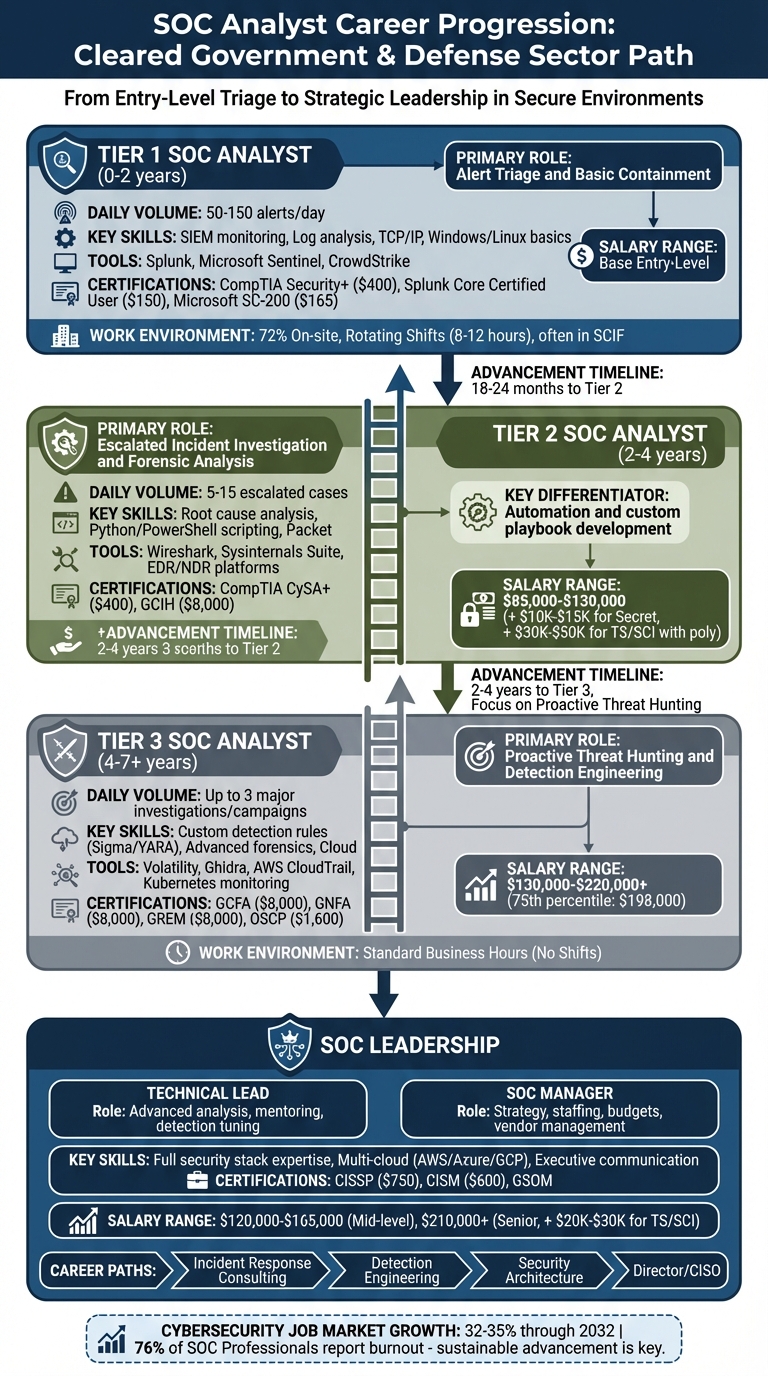
Most professionals begin their digital forensics careers in roles such as Digital Forensic Investigator I, Digital Forensics Lab Technician, or related jobs like SOC Analyst or Incident Responder [2][1]. These positions focus on essential tasks like creating forensic images, maintaining the chain of custody, and performing basic artifact analysis.
Building the necessary skills for these roles typically takes about 12 to 18 months. Start by mastering IT and operating system basics in 3-4 months, then spend 2-3 months learning security and incident response fundamentals. Dedicate another 3-4 months to developing core forensic skills using tools like Autopsy and FTK Imager [2].
Entry-level analysts can expect to earn between $60,000 and $80,000 annually [2]. To stand out, create a portfolio showcasing your work from Capture The Flag (CTF) challenges on platforms like CyberDefenders. This demonstrates your technical abilities and analytical skills to potential employers. Certifications like CompTIA Security+ or GCFE can further strengthen your credentials, especially for cleared positions [2][1].
After gaining foundational experience, you’ll be ready to take on roles with greater technical and leadership responsibilities.
Advancing Your Career
As you progress in digital forensics, you’ll take on more responsibility and enjoy higher compensation. Professionals with 3-5 years of experience often move into roles like Digital Forensic Examiner or Incident Responder, focusing on tasks such as timeline reconstruction, mobile forensics, and memory analysis. Salaries for these positions generally range from $85,000 to $110,000 [2].
At the senior level, roles like Forensics Lead, Malware Analyst, or DFIR Consultant require advanced expertise. This includes skills in reverse engineering, developing standard operating procedures, and serving as an expert witness. Salaries for these roles typically range from $115,000 to $145,000, with some high-level federal or specialized positions offering up to $182,000 depending on expertise and location [2][1].
Specializing in areas like memory forensics, network forensics, mobile device analysis, cloud forensics (AWS/Azure/GCP), or Industrial Control Systems (ICS) forensics can significantly boost your career prospects [2]. Analysts with GCFA certification, for example, tend to earn 15-20% more than their peers without it [8]. Advanced certifications like GCFA, GREM, or CISSP are particularly valuable for securing senior-level cleared positions [2][1].
"The role offers something increasingly rare in cybersecurity: the satisfaction of deep, methodical investigation rather than reactive firefighting." – Unihackers Career Guide [2]
As you advance, developing "soft skills" becomes increasingly important. The ability to explain complex technical findings to non-technical audiences, such as juries, executives, or legal teams, sets top performers apart [2][1]. For those working in law enforcement forensics, emotional resilience is also essential, particularly when dealing with sensitive or distressing material [2][3].
How to Find Jobs as a Cleared Digital Forensics Examiner
Highlighting Your Security Clearance
Make sure your active security clearance is easy to spot on your resume – place it right under your contact information. Include the clearance level (e.g., Secret, Top Secret, or TS/SCI with polygraph) and the date it was granted or last updated. This tells potential employers you’re ready to hit the ground running.
In interviews, emphasize your history of financial and personal integrity, as these factors play a role in clearance renewals or upgrades. Showcasing your responsibility with classified materials highlights your professionalism and readiness for sensitive roles. This clear focus on your clearance makes you stand out and prepares you to explore specialized job platforms.
Leveraging Cleared Cyber Security Jobs
Platforms like Cleared Cyber Security Jobs are a direct link to government contractors. Upload your resume, set up job alerts tailored to your forensic expertise – whether it’s mobile forensics, malware analysis, or incident response – and start connecting with the right opportunities.
These platforms often provide career resources, offering tips on maintaining your clearance, earning certifications, and preparing for interviews. They also host job fairs where you can meet hiring managers from top government contractors face-to-face, giving you a chance to make a strong impression.
What Employers Are Looking For
Employers want more than certifications – they’re looking for hands-on experience in forensic investigations. After fine-tuning your resume and leveraging job alerts, focus on showcasing your technical skills and practical expertise during the hiring process.
Digital forensics roles for cleared professionals are often categorized by clearance levels. For example, Secret-level roles may focus on general digital forensics, while TS/SCI with polygraph positions often involve advanced tasks like media forensics or malware investigations.
Proficiency with forensic tools like EnCase, FTK, Autopsy, Cellebrite, and X-Ways is essential. Employers also value scripting skills in Python, PowerShell, or Bash to automate evidence processing tasks [12][15]. Your resume should highlight specific investigations you’ve worked on, the data volumes you’ve handled, and any courtroom testimony experience. Certifications such as GCFE, GCFA, or EnCE further demonstrate your ability to tackle complex forensic challenges. With digital evidence now playing a role in over 90% of federal and state criminal cases [12], employers are looking for examiners who understand chain-of-custody protocols and can deliver findings that hold up in court.
My life as Cyber Forensic Investigator and what Certifications you should
Wrapping It Up
To excel in digital forensics, you need a mix of active security clearance, industry-recognized certifications, and strong technical skills. Whether it’s a Secret, Top Secret, or TS/SCI clearance, this qualification can unlock opportunities with federal agencies like the FBI, NSA, or Department of Defense, giving you access to high-stakes, classified investigations.
Certifications such as GCFA, GCFE, or CFCE validate both your technical and legal expertise. For example, analysts with the GIAC Certified Forensic Analyst (GCFA) certification often earn 15–20% more than peers without it, with seasoned professionals earning $133,000 or more annually [8]. These certifications prove you’re capable of delivering legally sound, court-ready findings that can withstand intense scrutiny.
On the technical side, proficiency with tools like EnCase, FTK, Cellebrite, and X-Ways, combined with skills in scripting languages like Python or PowerShell, is essential. Expertise in imaging, memory forensics, and maintaining a strict chain of custody for evidence ensures you’re prepared for even the most complex investigations. Employers also value professionals who can translate highly technical findings into clear, compelling courtroom testimony. These skills not only enhance your career prospects but also position you for roles with greater responsibility and influence.
FAQs
Which clearance level is most useful for digital forensics roles?
The Top Secret clearance holds immense importance for digital forensics roles, particularly those tied to national security or military operations. High-level positions in this field often demand this clearance to manage classified information and contribute to essential missions.
What’s the fastest certification path to land a cleared forensics job?
The fastest path to landing a forensics job with security clearance is by obtaining well-known certifications such as the EnCase Certified Examiner (EnCE) or GIAC Certified Forensic Examiner (GCFE). With dedicated effort, you can usually complete these in just 3 to 4 months. These certifications showcase your skills in digital forensics and meet the criteria for many security-cleared positions.
How do I get hands-on forensics experience without real casework?
To build practical skills in digital forensics, creating a home lab is a great starting point. This setup allows you to practice techniques, experiment with forensic tools, and simulate scenarios such as data recovery or evidence analysis. You can use free, open-source tools and virtual machines to keep things accessible and cost-effective.
Additionally, participating in Capture the Flag (CTF) challenges can sharpen your problem-solving abilities in a fun, competitive way. Online courses and certifications also offer structured learning paths, giving you the chance to gain hands-on experience in a controlled, risk-free environment. These activities are excellent ways to strengthen your expertise and confidence in digital forensics.