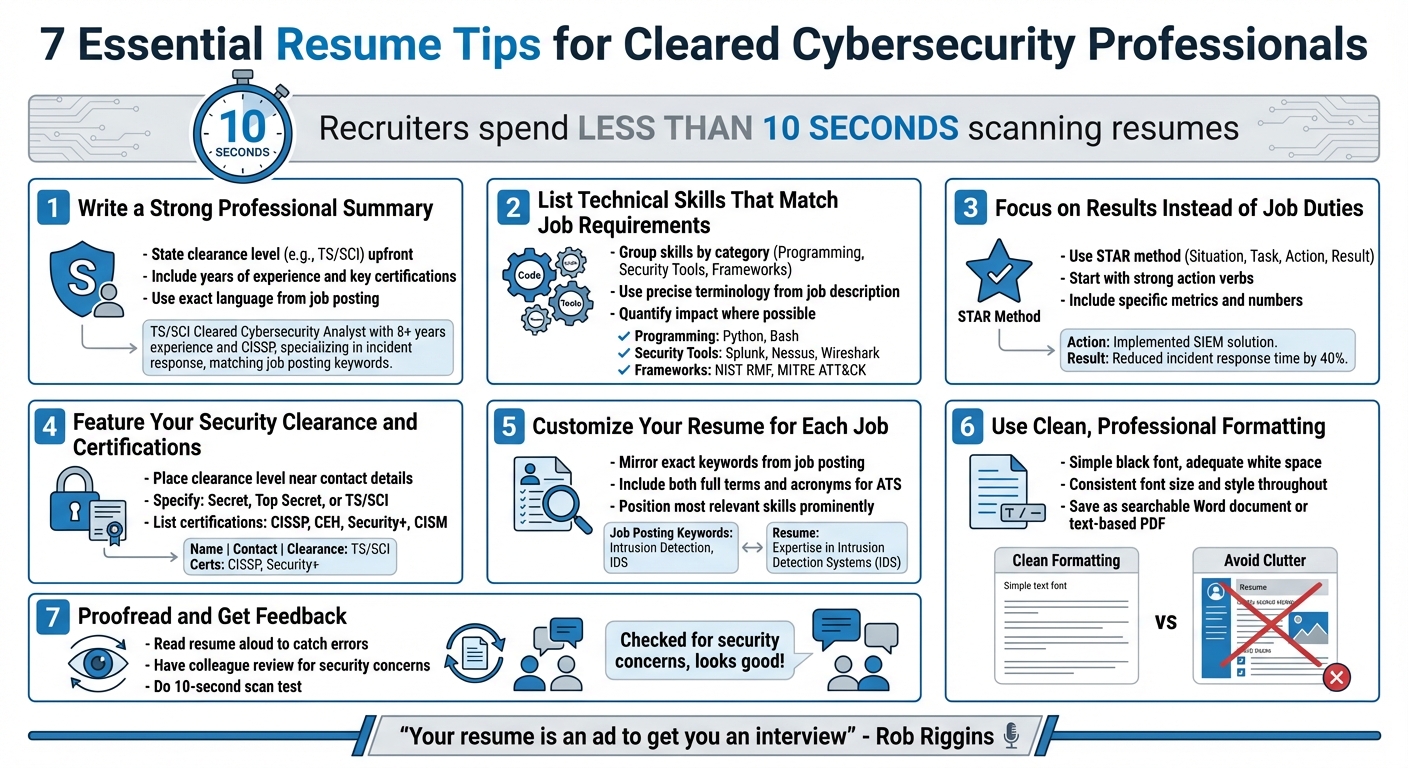
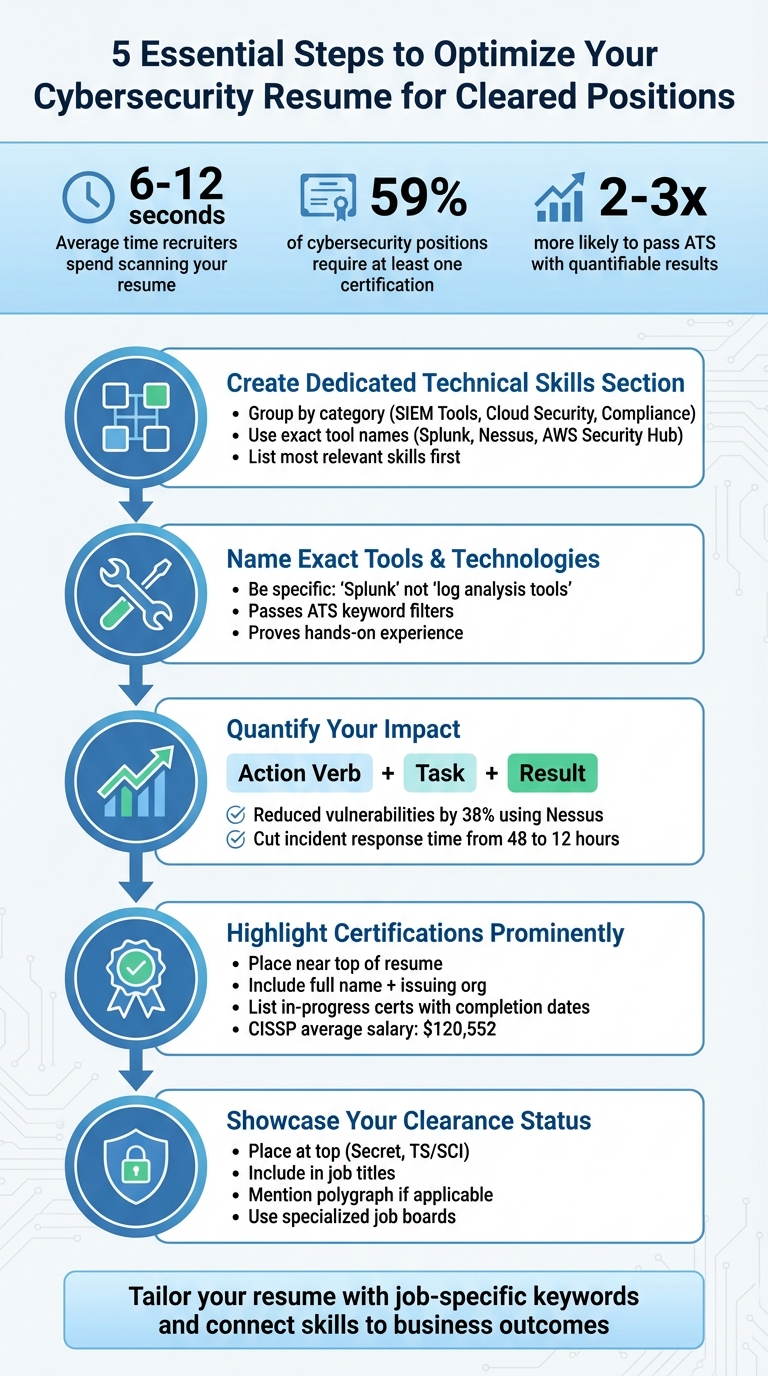
Your cybersecurity resume must immediately highlight your technical skills and clearance to stand out in a competitive job market. With recruiters spending just 6–12 seconds per resume and many companies using Applicant Tracking Systems (ATS), crafting a clear, results-driven resume is essential. Here’s how:
- Prioritize Technical Skills: Create a dedicated "Technical Skills" section organized into categories like SIEM Tools, Cloud Security, and Compliance Frameworks. Use exact tool names (e.g., Splunk, Nessus) to pass ATS filters.
- Show Results: Use metrics to demonstrate impact, such as "Reduced vulnerabilities by 38% using Nessus." Highlight achievements with action verbs and measurable outcomes.
- Certifications Matter: List certifications (e.g., CISSP, Security+) prominently, including in-progress ones with completion dates. Tailor certifications to job requirements.
- Leverage Clearance: Place your security clearance (e.g., TS/SCI) at the top of your resume and integrate it into job titles. Mention polygraphs if applicable.
5 Essential Steps to Optimize Your Cybersecurity Resume for Cleared Positions
The ULTIMATE RESUME GUIDE For CYBERSECURITY In 2026
How to Organize Your Technical Skills
Recruiters typically spend just 6 to 12 seconds scanning a resume during their initial review [7]. That’s barely enough time to skim, let alone read through lengthy paragraphs. If your technical skills are buried in dense text or scattered across your resume, they might get overlooked. To ensure your expertise stands out, dedicate a separate "Technical Skills" section. This should be distinct from soft skills and organized into clear, logical categories.
Group Skills by Category
Organizing your skills into categories transforms a jumbled list into a well-structured snapshot of your expertise. For example, instead of listing everything in one long line – like "Splunk, Python, NIST, AWS Security Hub, penetration testing" – break them down into groups such as Network Security, SIEM Tools, Scripting/Languages, Cloud Security, and Risk & Compliance. This format not only highlights your skills but also shows you understand how to present them effectively within the broader cybersecurity context.
For space efficiency and ATS compatibility, use a comma-separated format within each category. For example: "SIEM Tools: Splunk, IBM QRadar, LogRhythm." While tables can enhance clarity, avoid overly complex layouts or multi-column designs, as older ATS systems may struggle to process them.
| Skill Category | Example Tools & Technologies |
|---|---|
| Network Security | Firewalls, VPNs, IDS/IPS, Wireshark, Cisco ASA, Fortinet |
| SIEM Platforms | Splunk, IBM QRadar, LogRhythm |
| Vulnerability Management | Nessus, Nmap, Qualys, OpenVAS |
| Cloud Security | AWS Security Hub, Azure Security Center, Google Cloud Platform |
| Scripting & Languages | Python, PowerShell, Bash, Java, C++ |
| Compliance & Frameworks | NIST, ISO 27001, GDPR, HIPAA, SOC2 |
Make sure to align these categories with the skills emphasized in the job description to capture the recruiter’s attention quickly.
List the Most Relevant Skills First
Start with the skills that directly match the job description. This ensures recruiters instantly see how you fit the role. For example, if the job posting highlights "experience with Splunk and threat hunting", make sure those terms are prominently featured at the top of your Technical Skills section.
Use exact keywords from the job listing to align with ATS filters, and keep descriptions concise – stick to one or two words rather than lengthy phrases. This focused strategy not only grabs attention but also sets the stage for showcasing your achievements with specific tools and technologies.
How to List Cybersecurity Tools and Technologies
List Common Industry Tools
When listing tools on your resume, be specific. Employers want to see the exact names of the tools you’ve worked with – not vague descriptions like "vulnerability scanners" or "security monitoring platforms." For example, mention Splunk for SIEM, Nessus for vulnerability scanning, Metasploit for penetration testing, or CrowdStrike for endpoint protection.
Why does specificity matter? Two key reasons:
- Applicant Tracking Systems (ATS): Many companies use ATS to scan resumes for keywords that match the job description. If the job posting mentions "Splunk" and your resume only says "log analysis tools", your application might not get past the automated screening.
- Hiring Managers and Recruiters: Specific tool names signal that you’re familiar with the platforms used in real-world cybersecurity operations. They don’t just show knowledge of concepts – they prove you’ve worked hands-on with the tools that matter.
"Naming any specific programming or scripting languages you’re familiar with, or data analytic programs you’ve worked with can impress an employer." – Zoë Morris, President, Frank Recruitment Group [2]
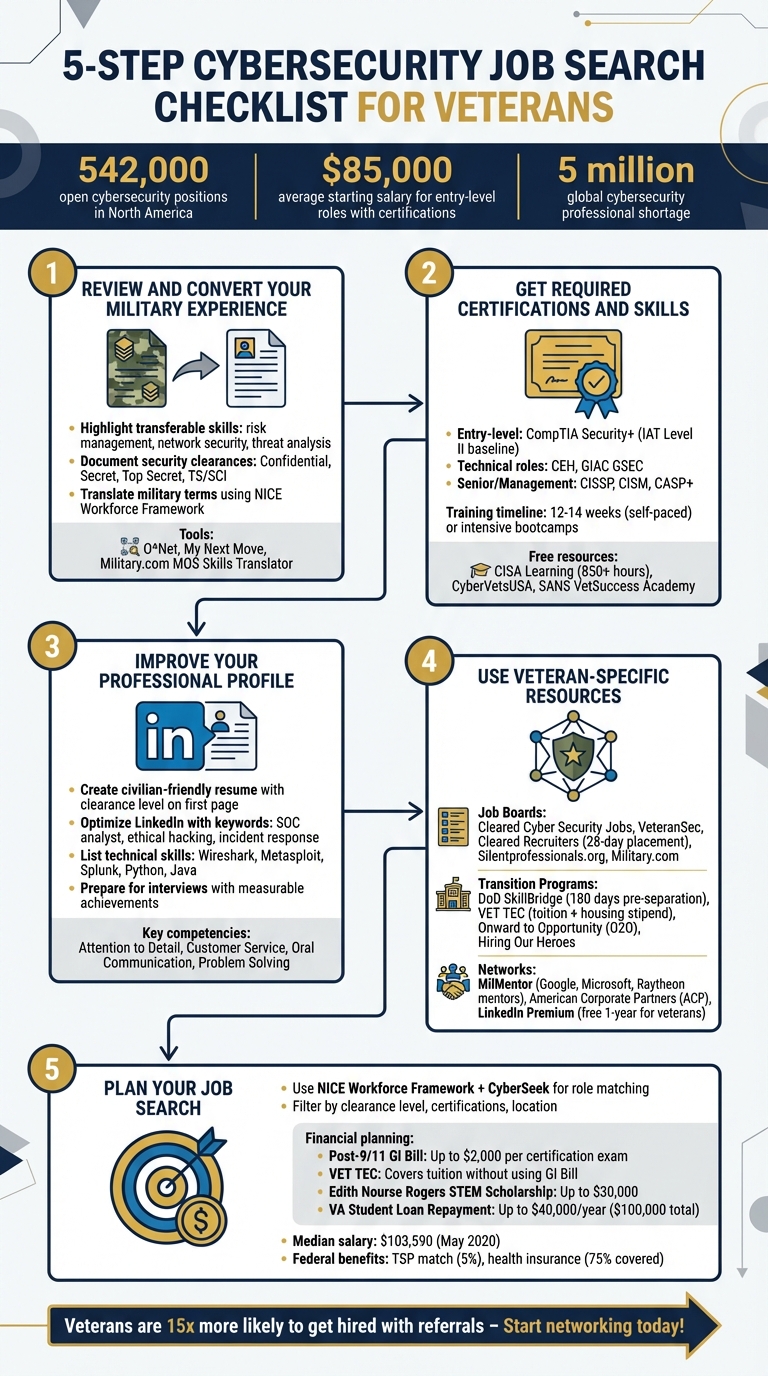
For roles requiring security clearance, focus on tools relevant to government and defense work. Highlight platforms that meet DoD 8570 compliance or support the Risk Management Framework (RMF). Additionally, with federal agencies increasingly adopting cloud solutions, expertise in AWS Security Hub, Azure Security Center, and container security tools like Docker and Kubernetes can set you apart [3][6]. Include scripting languages like Python for automation and tool development, and PowerShell for managing Windows environments and responding to incidents [3].
Don’t stop at listing tools – detail your results and accomplishments with them to make your resume stand out.
Explain How You Used Each Tool
Simply listing tools isn’t enough. To make an impact, show how you’ve used them to solve problems or achieve results. Instead of isolating tools in a skills section, integrate them into your work experience bullet points. This transforms a static list into a narrative that highlights your problem-solving abilities.
For instance, rather than just listing "Wireshark" under Network Security, craft a result-driven statement like: "Detected and mitigated 150+ intrusion attempts using Snort and Wireshark, reducing network breach incidents by 40% over six months." This format demonstrates not only your familiarity with the tool but also your ability to apply it effectively to protect an organization.
Use strong action verbs like "Architected," "Mitigated," "Detected," and "Optimized" to emphasize your initiative and ownership [6][8]. If you’re early in your career and lack professional experience, showcase tools you’ve used in personal projects or home labs. For example: "Built a virtualized network with pfSense and ELK stack for log analysis to simulate enterprise security monitoring." This highlights hands-on learning and self-motivation – qualities that resonate with employers [3].
How to Show Technical Skills Through Results
Use Numbers to Show Results
Numbers are a powerful way to turn responsibilities into measurable achievements. Considering that recruiters spend just six seconds scanning resumes, it’s no surprise that resumes with quantifiable results are 2–3 times more likely to make it past Applicant Tracking Systems [9]. In the field of cybersecurity, metrics are especially crucial.
"In cybersecurity, where threats are measured in dollars and downtime, numbers speak louder than buzzwords." – Resumly [9]
To effectively showcase your accomplishments, follow the "Action Verb + Task + Result" formula [10]. Instead of vague descriptions, use clear, data-driven examples like: "Reduced high-risk vulnerabilities by 38% within six months through weekly Nessus scans and automated patching."
Focus on areas that resonate with hiring managers, such as risk reduction, operational efficiency, team enablement, and technology adoption [9]. For instance, you could highlight efficiency improvements: "Cut incident response time from 48 hours to 12 hours by implementing automated threat detection with Splunk." Or, demonstrate reliability: "Maintained 99.9% uptime for secure networks supporting 5,000+ users" [1][9].
If exact numbers aren’t available, use conservative estimates and qualifiers like "approximately" or "over." Just be ready to explain your methodology during interviews [9]. For roles involving classified work, ensure your metrics remain high-level to avoid disclosing sensitive information. Focus on emphasizing your technical contributions and measurable results without breaching confidentiality [1].
By quantifying your achievements, you validate your technical expertise while showing how your work supports broader business objectives.
Connect Skills to Business Goals
Once you’ve presented measurable results, the next step is to tie your technical skills to the company’s strategic goals. While tools and methods highlight your technical abilities, linking those accomplishments to cost savings or compliance initiatives demonstrates your broader value to the organization.
Translate technical tasks into business outcomes. For example: "Reduced policy violations by 27% within three months, ensuring HIPAA compliance and avoiding potential $50,000 in regulatory fines" or "Saved $120,000 annually by automating patch management across 800 endpoints" [9].
For roles requiring security clearances, emphasize how your skills contributed to key objectives like meeting DoD 8570 compliance, improving Risk Management Framework (RMF) audit scores, or enabling mission-critical operations. Use specific metrics to show progress, such as: "Raised ISO 27001 compliance score from 78% to 95% through systematic control implementation" [9].
"Led 12 security workshops that boosted simulation pass rates from 62% to 91% and cut human-error risk by 47%." [9]
Whenever possible, include the timeframe and tools used in your descriptions to add credibility [9]. By connecting your technical achievements to business priorities, you underscore your ability to deliver value that goes beyond the technical realm.
sbb-itb-bf7aa6b
How to List Certifications and Compliance Knowledge
Certifications and compliance expertise are just as important as technical skills and measurable results when it comes to showcasing your readiness for cleared roles.
Certifications
Certifications serve as proof of your skills and can often secure you an interview. In fact, nearly 59% of all cybersecurity positions require at least one certification [5]. That makes this section a key element for cleared roles. Place your certifications prominently – ideally near the top of your resume – especially if they’re required for the role or strengthen your security clearance.
"I prefer when relevant certifications and clearances are near the top of the resume, such as TS/SCI, CISSP, Public Trust, Private Trust, etc. They should be current." – John Boyle, Senior Talent Director, CIBR Warriors [2]
Always include the full name of the certification and the issuing organization. For example, write "Certified Information Systems Security Professional (CISSP) – (ISC)²" instead of just "CISSP." If you’re in the process of earning a certification, list it as "In Progress" and include the expected completion date. This can be critical if the certification is a mandatory requirement for the job.
Tailor your certifications to match the job description. For instance, if the role emphasizes penetration testing, prioritize certifications like CEH or OSCP. For entry-level cleared roles, CompTIA Security+ is a must-have because it satisfies DoD 8570 requirements. Mid-level roles often value certifications like CEH and CISM, while advanced positions may require CISSP, which comes with an average annual salary of $120,552 [13].
Highlight Compliance Framework Experience
After listing your certifications, demonstrate your hands-on experience with compliance frameworks. This not only shows your technical expertise but also your understanding of risk management. Make a clear distinction between regulatory frameworks (e.g., GDPR, HIPAA, FISMA, CMMC) and information security frameworks (e.g., NIST CSF, ISO 27001, SOC 2). For cleared roles, focus on frameworks relevant to government work, such as NIST RMF and CMMC, which will be mandatory for all DoD contractors by 2026 [11].
Be specific about your contributions to each framework. For example, you could write, "Conducted gap analysis for NIST 800-171 compliance, developing 23 corrective action plans that increased compliance from 78% to 95%." If you’ve used GRC tools like Nessus, Qualys, or RSA Archer, include them to highlight your technical proficiency. Use terms like "NIST RMF – Expert" or "ISO 27001 – Advanced" to indicate your level of expertise.
Whenever possible, quantify your results. For instance, implementing privacy compliance procedures can reduce data breach incidents by up to 50% [12]. Highlight achievements such as "Achieved 100% PCI DSS compliance within 6 months" or "Reduced compliance-related fines by 40% over two years" to illustrate the real-world impact of your work.
How to Customize Your Resume for Cleared Cybersecurity Jobs
Cleared cybersecurity jobs require a tailored approach that differs from standard tech roles. Your resume needs to clearly demonstrate that you meet the unique demands of handling classified information and working within sensitive government systems.
Highlight Your Security Clearance
Your security clearance is one of your biggest assets in the cleared job market, so make sure it’s front and center. Place it prominently at the top of your resume, specifying the clearance level (e.g., Secret, Top Secret, TS/SCI). If you’ve undergone a polygraph (either CI or Full-Scope), mention that as well, along with the date of your most recent Periodic Reinvestigation.
"Having an active security clearance tells employers: You’ve passed extensive background checks, you understand secure systems and data protection, [and] you can be trusted with classified or sensitive projects." – LaunchCode [1]
To emphasize your clearance further, include it in job titles and project descriptions. For instance, instead of just listing your role as "Cybersecurity Analyst", you could write "Cybersecurity Analyst (TS/SCI)." This immediately signals that your clearance was integral to your job. However, be mindful of operational security – avoid sharing classified project details on public profiles or inappropriately disclosing sensitive information.
Once your clearance is clearly showcased, focus on platforms that cater to cleared professionals to ensure your resume lands in front of the right recruiters.
Leverage Specialized Job Boards
After emphasizing your clearance, use job boards specifically designed for cleared positions to connect with employers who value your credentials. Platforms like Cybersecjobs.com are excellent for targeting roles where both technical expertise and security clearances are essential. These sites are tailored to match candidates with hiring managers who understand the value of your qualifications.
To ensure your resume stands out, tailor it with keywords that align with cleared job descriptions and applicant tracking systems (ATS). Include terms like "TS/SCI developer", "security clearance", and "polygraph." Additionally, spell out acronyms at least once – such as "Top Secret/Sensitive Compartmented Information (TS/SCI)" – to ensure ATS software picks up on all relevant terms. Mirroring the language used in job descriptions can further highlight your clearance and technical skills.
"A well-crafted resume not only highlights your skills and experience but also sets you apart from other candidates vying for the same roles." – Cybersecjobs.com [4]
Conclusion
Your cybersecurity resume should highlight measurable achievements and showcase your qualifications effectively. Organize your information into clear sections, emphasize quantifiable results, and prominently display certifications to create a resume that stands out – especially for roles requiring security clearance.
Certifications play a crucial role in the cybersecurity field, with nearly 59% of positions requiring at least one professional credential [5]. Make sure to list your current certifications prominently and include any in-progress credentials, along with their expected completion dates.
For cleared positions, your security clearance is just as important as your technical skills. Place your clearance status – such as Secret, Top Secret, or TS/SCI – front and center. Don’t forget to mention polygraph details if applicable, and reiterate this information throughout your work history. Platforms like Cybersecjobs.com can help you connect with employers who value both your technical expertise and clearance credentials.
"A well-crafted resume not only highlights your skills and experience but also sets you apart from other candidates vying for the same roles." – CyberSecJobs [4]
Each section of your resume should reinforce your technical skills and clearance status. Tailor your resume with job-specific keywords and fully spelled-out acronyms to ensure it passes ATS filters. By linking your expertise to measurable outcomes, you can position yourself for success in this fast-growing field. Take the time to refine your resume and unlock opportunities that align with your career goals.
FAQs
What’s the best way to showcase technical skills on a cybersecurity resume?
To make your technical skills stand out on a cybersecurity resume, include a dedicated Skills or Core Competencies section near the top. Use this space to clearly list your most relevant technical abilities, certifications, and tools. This makes it easier for both recruiters and applicant tracking systems (ATS) to spot your qualifications quickly.
Another way to emphasize your skills is by incorporating them into your professional summary. This approach immediately showcases your expertise and aligns your resume with the job description. Be selective – focus on the qualifications that are most relevant to the role you’re targeting. Certifications like CISSP, CEH, or Security+ can add credibility and make your resume leave a stronger impression.
Why should I include specific tools and technologies on my cybersecurity resume?
Including specific tools and technologies on your cybersecurity resume is a smart way to showcase your hands-on experience and expertise with systems that matter in the field. It gives potential employers a clear sense of your capabilities and makes it easier for them to evaluate your qualifications.
For example, listing tools like firewalls, SIEM platforms, or vulnerability scanners signals your ability to tackle practical cybersecurity challenges. These details can give you an edge, particularly when applying for positions that demand cleared professionals who are ready to hit the ground running.
How can I effectively showcase my security clearance on a cybersecurity resume?
To make your security clearance stand out on your cybersecurity resume, place it prominently in your professional summary or near your contact information at the very top. This way, hiring managers can spot it immediately.
You should also weave your clearance level (e.g., Top Secret, TS/SCI) into relevant job titles or project descriptions, especially if those roles required such credentials. If applicable, mention polygraph details to further emphasize your qualifications. However, avoid disclosing any classified or sensitive information – just clearly state your clearance status to showcase your eligibility for sensitive positions.
For cleared professionals, platforms like Cybersecjobs.com can help connect you with employers actively seeking candidates with security clearances like yours.