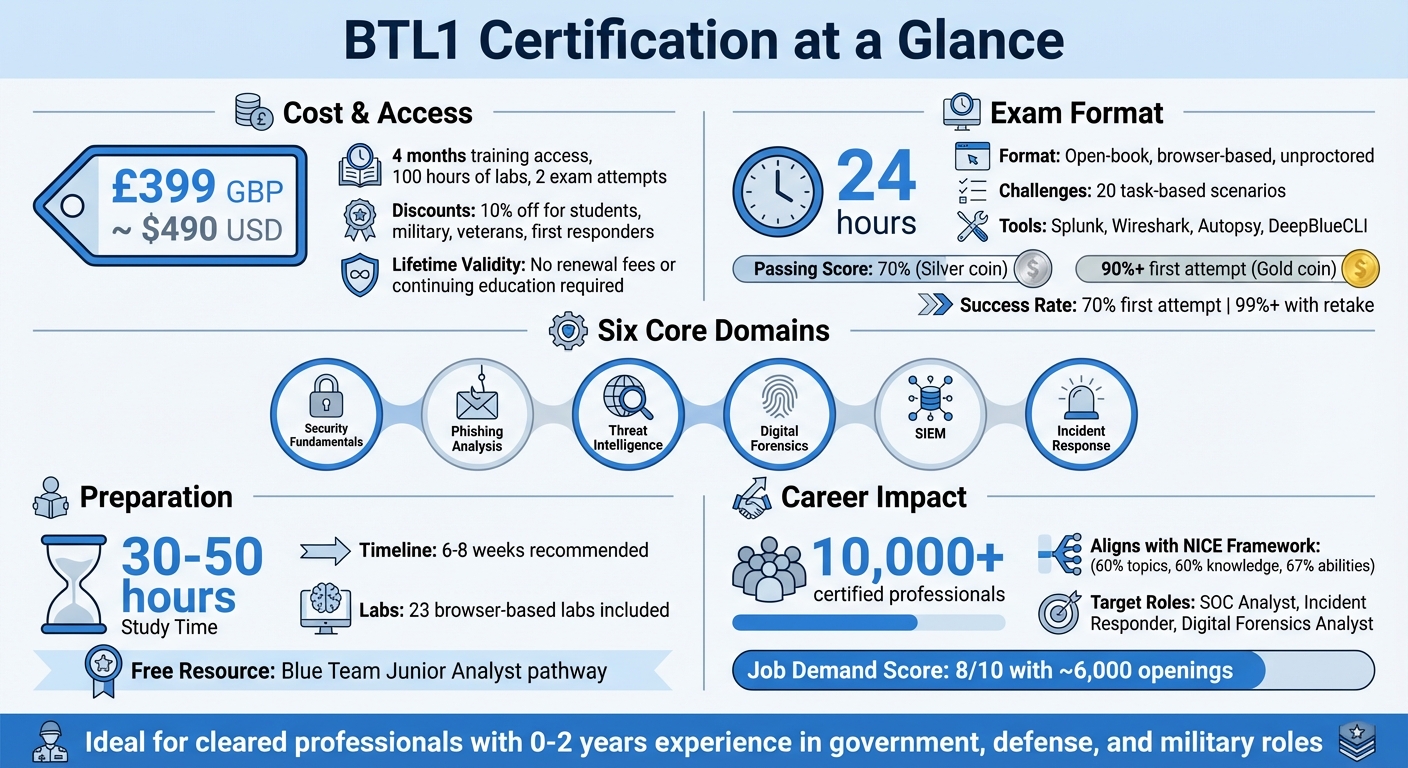
The Blue Team Level 1 (BTL1) certification is a practical, entry-level credential for cybersecurity professionals, especially those in government, defense, and military roles requiring security clearances. It tests your ability to handle security incidents through a 24-hour, task-based exam focusing on six domains: Security Fundamentals, Phishing Analysis, Threat Intelligence, Digital Forensics, SIEM, and Incident Response.
Key Points:
- Cost: $490 USD (includes training, labs, and 2 exam attempts; discounts available for students, military, and first responders).
- Format: Open-book, browser-based, unproctored, with 20 challenges using tools like Splunk, Wireshark, and Autopsy.
- Passing Criteria: 70% for certification; 90%+ on the first attempt earns a gold challenge coin.
- Preparation: 30–50 hours of study, with access to 100 hours of labs and free resources like the Blue Team Junior Analyst pathway.
- Lifetime Validity: No renewal fees or continuing education requirements.
BTL1 aligns with the NICE Framework, making it ideal for roles like SOC Analyst or Incident Responder. It’s a one-time investment that directly demonstrates your hands-on skills to employers. With over 10,000 certified professionals and a 99% pass rate with retakes, it’s a strong option for building your cybersecurity career.
BTL1 Certification Quick Reference Guide: Cost, Format, and Key Benefits
BTL1 Exam Structure and Prerequisites
Exam Format
The BTL1 exam is a 24-hour, open-book, browser-based simulation that includes 20 task-based challenges. These challenges are designed to mirror real-world cybersecurity incidents, using industry-standard tools like Splunk, Wireshark, Autopsy, and DeepBlueCLI for tasks such as SIEM, network analysis, forensics, and log review.
The exam is unproctored, meaning you can complete it from home or work, with access to your notes, course materials, and even search engines. However, using AI tools like ChatGPT is strictly prohibited and will result in disqualification. To pass, you’ll need a 70% score, which earns you the silver challenge coin. Achieving a 90% or higher on your first attempt secures the coveted gold challenge coin.
"The exam guides you through a very realistic incident response scenario in which you have to combine mostly your Splunk/Wireshark/Autopsy knowledge." – Synack12, Security Researcher [9]
If you don’t pass on your first try, you’re entitled to one free retake. Additional retake vouchers are available for $123 each, with a mandatory 10-day waiting period between attempts. Encouragingly, over 99% of candidates who use their free retake eventually pass.
A strong understanding of core security concepts is essential to navigate the challenges effectively.
Prerequisites and Required Knowledge
The BTL1 exam has no formal prerequisites, making it ideal for professionals with 0–2 years of experience, including students, career changers, and IT generalists exploring cybersecurity. However, candidates are expected to have a foundational understanding of six key areas: Security Fundamentals, Phishing Analysis, Threat Intelligence, Digital Forensics, SIEM, and Incident Response.
To boost your chances of success, Security Blue Team advises completing all 23 browser-based labs included with your exam purchase. These labs provide 100 hours of hands-on practice with the tools featured in the simulation. Additionally, the Blue Team Junior Analyst (BTJA) pathway, offered for free, serves as a helpful self-assessment tool to measure your readiness.
For optimal results, organize your notes by domain before the exam. A well-prepared, searchable document containing Splunk queries, Wireshark filters, and phishing analysis workflows can save you precious time during the 24-hour window.
sbb-itb-bf7aa6b
How to Prepare for the BTL1 Exam
Study Plan and Core Domains
The BTL1 exam focuses on six key domains, but the real emphasis is on practical, hands-on skills rather than rote memorization. To prepare effectively, aim for 30–50 hours of study spread over 6–8 weeks. This pace allows for consistent practice without overwhelming yourself [1].
Break your preparation into weekly segments. Dedicate one week each to topics like Phishing Analysis, Threat Intelligence, SIEM (Splunk), and Digital Forensics. Reserve two weeks toward the end for integrated incident response scenarios and final reviews. Here’s a suggested timeline to guide your studies:
| Study Week | Focus Area | Key Tools/Tasks |
|---|---|---|
| Week 1 | Security Fundamentals | Basic Splunk syntax |
| Week 2 | Phishing Analysis | Header analysis, artifact extraction |
| Week 3 | Threat Intelligence | MISP, VirusTotal, WHOIS pivots |
| Week 4 | SIEM (Splunk) | Scoping activity, filtering malicious logs |
| Week 5 | Digital Forensics | Volatility, KAPE, FTK Imager, Wireshark |
| Week 6 | Incident Response | PICERL framework, report writing practice |
| Week 7-8 | Review | Redoing challenging labs, refining notes |
Completing all 23 browser-based labs is a great way to boost your chances of earning the coveted gold challenge coin. With a solid plan in place, the next step is to leverage the best study resources.
Study Resources
Your exam purchase includes 4 months of on-demand training access and 100 hours of lab time. To start, explore the free Blue Team Junior Analyst (BTJA) pathway. This resource covers OSINT, Digital Forensics, and Threat Hunting, giving you a chance to identify any knowledge gaps before diving into the paid curriculum.
For additional practice, platforms like Blue Team Labs Online (BTLO) offer extra scenarios, including Malicious PowerShell and Phishing Analysis. TryHackMe‘s SOC Level 1 path is another excellent option, helping you sharpen investigative skills through realistic challenges. If you’re undecided about committing to the course, Security Blue Team provides a free limited-access demo, allowing you to preview the structure and content.
Once you’ve built a strong foundation, focus on refining your strategy for acing the exam.
Exam Success Tips
Since the BTL1 exam is open-book, effective note-taking is far more important than memorizing details. Use tools like Notion or Obsidian to create a searchable database organized by domain. Include sections for Splunk search commands (e.g., stats, eval, rex) and Wireshark display filters (e.g., http.request, dns.qry.name). This setup will help you quickly find the information you need during the exam.
"Complete the theory part as quickly as you can… Instead, focus on the labs and make procedural notes." – drsh, Security Professional [7]
Plan your exam day carefully. Schedule breaks for rest, meals, and sleep to stay sharp. In the first two hours, focus on creating a timeline of attacker activity and drafting answers externally to avoid losing work due to browser timeouts. For the forensics section, keep a reference list of Windows Event Log IDs handy to speed up artifact analysis.
BTL1 Pricing and Benefits
Certification Cost
The BTL1 certification is more than just a credential – it’s an investment in your future within the cleared cybersecurity field. The cost is £399 GBP (around $490 USD) and includes everything you need: comprehensive training, lab access, and exam attempts. Specifically, this price gives you 4 months of on-demand access to over 330 lessons, 100 hours of browser-based lab time, and one initial exam attempt with a free retake included. The exam voucher is valid for 12 months, offering flexibility to schedule your exam even after your course access expires [2][5].
If you’re a verified student, military personnel, veteran, or first responder, you can take advantage of a 10% discount on the bundle price [2][5]. Need extra time to prepare? You can extend your training access for £100 GBP (31 days) or £150 GBP (62 days) without affecting the 12-month exam window. If both attempts are unsuccessful, a final attempt is available for £100 GBP, provided you submit a success plan. This fee structure is specific to the certification bundle [10].
For U.S. professionals, it’s worth keeping an eye on currency exchange rates. The all-in-one bundle ensures there are no hidden fees – training materials, lab access, and even physical rewards like your printed certificate and challenge coin are all included.
This upfront cost is designed to deliver value not just during the course but throughout your career.
Lifetime Certification Value
One of the standout benefits of BTL1 is its lifetime validity. Once you earn this certification, there are no renewal fees or continuing education requirements [4][5]. That means the $490 investment is a one-time cost that permanently enhances your resume. Over the past five years, more than 10,000 students have earned this certification, with about 70% passing on their first attempt. For those who use the free retake, the success rate jumps to over 99% [5].
The certification also comes with exclusive physical rewards. Passing the exam earns you a silver challenge coin, but if you score 90% or higher on your first attempt, you’ll receive the prestigious gold coin [2][8].
"The hands-on training gave me everything I needed to gain the coveted gold when I finally took the exam, and the confidence to jump straight into a senior SOC analyst role." – Tom, Tier 2 SOC Analyst [11]
BTL1’s alignment with the NIST NICE Framework for Cyber Defense Analyst roles further enhances its value. It covers 60% of topics, 60% of knowledge, and 67% of ability requirements, making it a strong choice for cleared professionals aiming for government or defense roles [5].
Using BTL1 to Advance Your Cleared Career
Showcasing BTL1 on Resumes and in Interviews
Earning your BTL1 certification highlights your ability to handle practical defensive operations, not just theoretical concepts. To make the most of this credential, emphasize your active clearance level (like Secret or TS/SCI) in your professional summary. In the technical skills section of your resume, list the tools you’ve mastered – such as Splunk, Wireshark, Autopsy, Volatility, KAPE, and MISP – to ensure your resume catches the attention of Applicant Tracking Systems.
When it comes to interviews, the STAR method is your best friend. Use it to describe specific BTL1 lab scenarios where you applied the PICERL process (Preparation, Identification, Containment, Eradication, Recovery, Lessons Learned) to tackle incidents during the 24-hour exam. These examples demonstrate your ability to handle real-world cybersecurity challenges.
Make sure to feature your BTL1 Credly digital badge on LinkedIn and in your email signature for easy skill verification. If you scored 90% or higher on your first attempt, mention earning the Gold Challenge Coin – it’s a standout achievement. To further strengthen your profile, consider publishing 2–3 write-ups of your lab work to showcase your hands-on investigative skills.
"Many students have told us that recruiters are very impressed when candidates discuss the projects and labs they have completed during the interview stage!"
By following these strategies, you’ll position yourself effectively for roles that match your specific expertise.
Finding Cleared Roles with Job Boards
Platforms like Cleared Cyber Security Jobs are tailored for professionals with active security clearances, connecting them with direct-hire employers in cybersecurity. Use job board filters to zero in on roles that align with your BTL1 skills and clearance level. Upload your resume and set up job alerts to stay informed about positions that fit your qualifications.
BTL1’s alignment with the NICE Framework makes it particularly valuable for government and defense roles. When searching for jobs, include keywords like "SOC Analyst", "Incident Response", "Cyber Defense Analyst", or "Digital Forensics" to ensure your applications match the roles seeking these competencies.
After applying, keep an eye on the job market to stay ahead of new opportunities.
Monitoring Job Market Demand
Keep tabs on openings for positions such as Tier 1 and Tier 2 SOC Analysts, Incident Responders, Digital Forensics Analysts, and Threat Intelligence Analysts – roles that align closely with the skills your BTL1 certification validates. Pay attention to job descriptions that mention tools like Splunk, Wireshark, and Volatility.
The certification’s recognition by military, government, and law enforcement sectors highlights the steady demand for BTL1-certified professionals[3]. Set up alerts for job postings that reference the "NICE Framework" or "hands-on defensive operations."
"BTL1 is hands-on and relates directly to our daily work."
How I Passed The Blue Team Level 1 (24-Hour Practical Exam) | Security Blue Team Guide + Tips
Conclusion
The BTL1 certification provides a practical, hands-on credential that demonstrates your ability to manage real-world defensive operations through an intense 24-hour incident simulation. With lifetime validity and no renewal fees, it’s a one-time investment tailored for cleared professionals aiming for junior SOC or Incident Response roles.
BTL1’s credibility is underscored by its recognition from military, government, and law enforcement organizations worldwide [1]. Its alignment with the NICE Framework makes it especially relevant for federal and cleared positions. Plus, the open-book exam format mirrors real-world problem-solving, testing your investigative skills as you would use them on the job.
Priced at £399 GBP (about $490 USD), the training bundle includes 100 hours of browser-based labs, two exam attempts, and four months of course access [1][2]. Cleared professionals should explore available discounts before purchasing. Achieving a score of 90% or higher on your first try earns you a physical "Gold" challenge coin – a standout credential for recruiters [1].
This certification is not only affordable but also a standout addition to your resume, recognized as a mark of quality by industry leaders. As Steffan J, Cyber Security Services Manager at Fortra, shared:
"This methodology helps Fortra ensure that our analysts have a consistent education with sufficient hands-on training to competently approach many of the complicated scenarios which they are likely to encounter" [6].
With around 6,000 job openings requiring BTL1-related skills and a demand score of 8/10 [12], now is an excellent time to pursue this credential.
To maximize your success, integrate your BTL1 training into your career strategy. Build searchable notes during your coursework, practice extensively with the labs, and use platforms like Cleared Cyber Security Jobs to connect with employers seeking cleared defensive analysts. Your active clearance and proven hands-on expertise set a solid foundation for career growth.
FAQs
Is BTL1 worth it for cleared jobs?
BTL1 is definitely worth considering for those aiming for cleared cybersecurity jobs. It provides hands-on, practical skills tailored to cybersecurity defense, making it ideal for entry-level SOC analyst roles. By earning this certification, you can showcase your expertise and boost your prospects in the competitive field of cleared cybersecurity positions.
How do I prep if I’m new to SOC work?
If you’re stepping into the world of SOC (Security Operations Center) work, it’s essential to concentrate on developing core cybersecurity skills. Some key areas to focus on include phishing analysis, threat intelligence, SIEM (Security Information and Event Management) investigation, digital forensics, and incident response.
To get started, explore beginner-friendly courses that cover these topics. Pair your learning with practical experience by using virtual machines to simulate real-world scenarios and practicing basic scripting skills, such as Python. Hands-on labs or simulations that mimic SOC workflows can be incredibly helpful in building confidence and understanding.
For those with 0-2 years of experience, the BTL1 program is specifically tailored to your level. Prioritize practical learning to lay a strong foundation for your cybersecurity career.
What should I do during the 24-hour exam?
During the 24-hour BTL1 exam, managing your time effectively and staying organized are key to success. Start by creating a clear timeline of the artifacts you uncover – this will make it easier to reference them when tackling later questions. Before the exam, prepare playbooks for common procedures so you can follow a structured approach without wasting time figuring out each step.
The exam centers on investigating a compromised environment and answering task-specific questions, so maintaining focus is crucial. Avoid using any prohibited AI tools, as this could jeopardize your results. Lastly, ensure you’re well-rested before the exam begins – your ability to concentrate for the full 24 hours will make all the difference.