Information System Security Managers (ISSMs) are vital for safeguarding classified systems in government and defense sectors. They ensure compliance with strict cybersecurity standards, manage Authorization to Operate (ATO) processes, and act as liaisons between organizations and federal agencies like the Defense Counterintelligence and Security Agency (DCSA). Here’s what you need to know:
- Role Overview: ISSMs oversee cybersecurity programs, maintain audit-ready systems, and resolve vulnerabilities using tools like Splunk, ACAS, and Nessus.
- Qualifications: U.S. citizenship, an active Top Secret clearance, and certifications like CISSP, CISM, or GSLC are required. A bachelor’s degree and 5–12 years of experience are typical.
- Career Progression: Start as an ISSO, gain RMF expertise, and advance to senior ISSM roles. Salaries range from $101,000 to $203,000 annually, depending on experience and location.
- Challenges: Maintaining a security clearance requires financial responsibility and adherence to federal laws. Continuous Evaluation (CE) ensures real-time monitoring of clearance holders.
- Future Outlook: With cybersecurity jobs projected to grow by 33% over the next decade, ISSMs are in high demand, offering lucrative and fulfilling career opportunities.
This guide breaks down the ISSM career path, including required skills, certifications, and strategies for long-term success.
ISSO vs ISSM and what to do after ISSO work
sbb-itb-bf7aa6b
Core Responsibilities of an ISSM in Cleared Environments
An ISSM’s role revolves around safeguarding classified systems through meticulous documentation, ongoing monitoring, and serving as a bridge between technical security teams and officials responsible for granting an Authorization to Operate (ATO). Their work ensures sensitive information remains secure. Here’s a closer look at some of their key responsibilities.
Implementing RMF and Managing ATO Processes
One of the ISSM’s primary tasks is applying the Risk Management Framework (RMF) outlined in NIST Special Publication 800-37. This structured six-step process – Categorize, Select, Implement, Assess, Authorize, and Monitor – guides how classified systems are secured [5].
During the Categorize phase, ISSMs work closely with system architects to define system boundaries and assign impact levels (Low, Moderate, or High) based on FIPS 199 and NIST 800-60. This ensures resources are allocated appropriately [5]. After categorizing, ISSMs customize security controls from the NIST 800-53 catalog to align with the system’s risk level. They coordinate with assessors to evaluate the effectiveness of these controls and brief the Authorizing Official on any remaining risks to secure an ATO. Additionally, they translate technical vulnerabilities into risk assessments, enabling senior leaders to make informed decisions [5]. By doing so, ISSMs maintain a robust security posture, ensuring risks are managed and controls remain effective.
Ensuring Compliance with DoD and NIST Standards
Compliance is a core part of an ISSM’s responsibilities. They manage essential RMF documentation, including the System Security Plan (SSP), Security Assessment Report (SAR), and Plans of Action and Milestones (POA&M). The POA&M is particularly important, as it tracks security weaknesses and outlines corrective actions until issues are resolved [5].
To maintain audit readiness, ISSMs compile evidence like configuration screenshots, access logs, and scan results, often using systems like eMASS [5]. They also conduct regular reviews of system configurations to ensure they align with NIST 800-53 controls and Department of Defense (DoD) guidelines. This continuous effort helps organizations adapt to evolving technologies and threats, reinforcing system security [5].
Managing Classified Systems Security
In addition to documentation, ISSMs actively monitor classified systems to address vulnerabilities before they become critical. This includes tracking patch deployments, reviewing logs, and coordinating incident response efforts. By staying vigilant, ISSMs ensure systems remain compliant between formal assessments, providing consistent protection for classified information.
Required Qualifications and Certifications for Cleared ISSMs
Stepping into the ISSM field requires meeting specific qualifications and certifications. Below, you’ll find the key requirements, certifications, and experience necessary to build a successful career as a cleared ISSM.
Basic Requirements for ISSMs
To qualify for cleared ISSM roles, U.S. citizenship is mandatory. Additionally, an active Top Secret or TS/SCI clearance is required. As of early 2026, the processing time for a Top Secret (Tier 5) clearance typically ranges from 120 to 240 days. However, an Interim Secret clearance may be granted in as little as 10 to 30 days, depending on initial fingerprint and background checks [6].
Most roles require a bachelor’s degree in fields like cybersecurity, computer science, or engineering. That said, some federal contracting environments allow for substitutions. For instance, holding a master’s degree can reduce the required work experience from 8 years to 5 years [1]. Before applying to a cleared position, it’s important to address any potential credit issues, as financial concerns are a common reason for clearance denial [6].
Required Certifications: CISSP, CISM, and GSLC
Beyond meeting the basic criteria, obtaining key certifications is essential. ISSM roles require an IAM Level III certification, and the most recognized options include:
- CISSP (Certified Information Systems Security Professional)
- CISM (Certified Information Security Manager)
- GSLC (GIAC Security Leadership Certification)
These certifications demonstrate expertise in implementing the Risk Management Framework, ensuring compliance with NIST 800-37/53, managing Authorization to Operate (ATO) processes, and advising leadership on cybersecurity risks. While some entry-level positions accept IAM Level II certifications, most competitive and higher-paying roles prioritize candidates with IAM Level III certification [1].
Experience and Skills Needed
Experience requirements vary from 5 to 12 years, depending on the level of the position. For mid-level ISSM roles, at least 5 years of experience in DoD/IC Cybersecurity is typically required, while senior-level roles may demand 8 to 12 years or more [1].
Practical expertise with key security tools is critical, including:
- ACAS/Nessus for vulnerability scanning
- SCAP for compliance checks
- STIG Viewer for system hardening
- SIEM platforms like Splunk for log analysis [1]
Core responsibilities often include conducting risk assessments, managing vulnerability scanning programs, and ensuring compliance with NIST 800-53 controls. A growing emphasis is placed on understanding modern security frameworks, such as Zero Trust architectures, Identity Access Management (IAM), and DevSecOps pipelines [1].
Leadership and communication skills are equally important. ISSMs not only guide ISSO teams but also act as the primary liaison with agencies like the Defense Counterintelligence and Security Agency (DCSA). These roles require the ability to mentor team members and effectively communicate complex cybersecurity concepts to senior leadership [1].
Salaries for cleared ISSM positions reflect this blend of technical expertise and leadership. Depending on experience and location, roles can range from $101,000 to $203,000 annually [1].
Career Progression Path for Cleared ISSMs
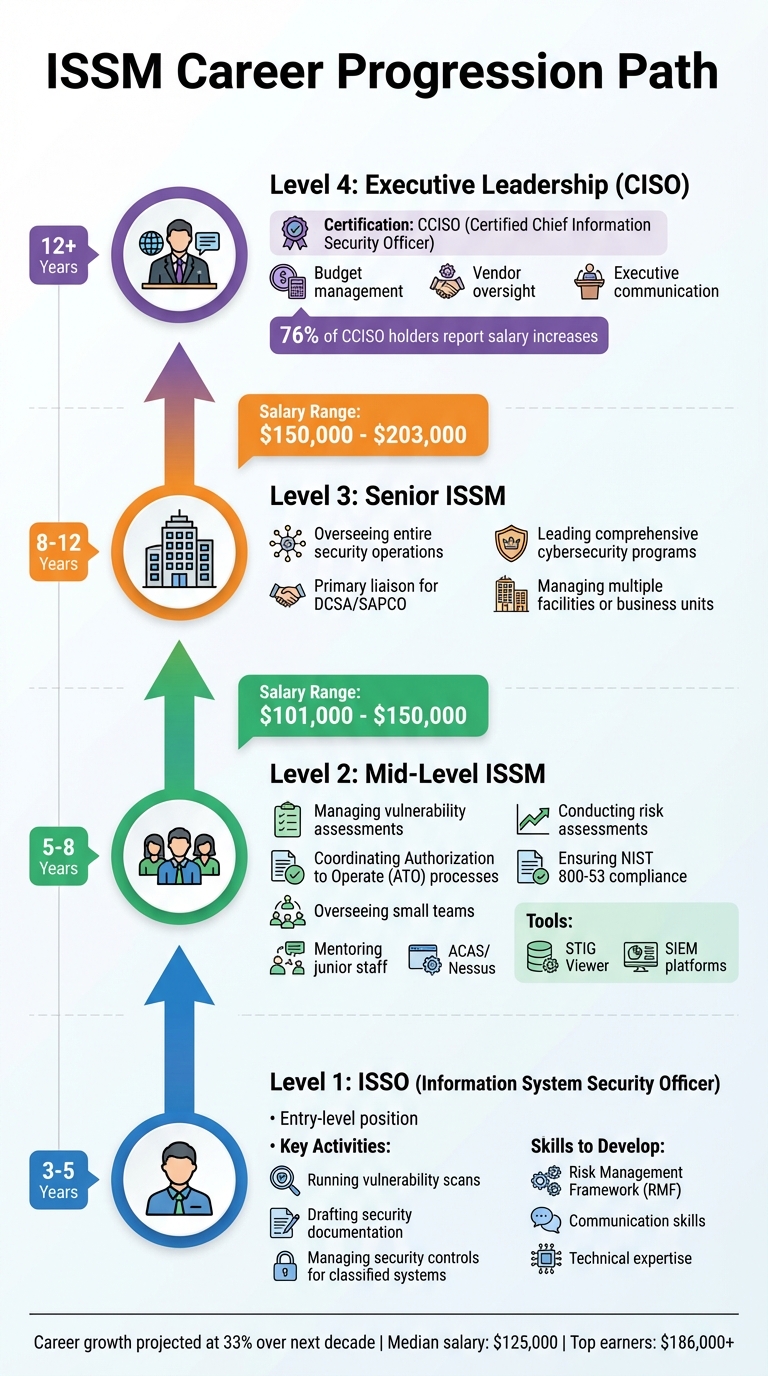
ISSM Career Progression Path: From ISSO to Senior Leadership
A cleared ISSM career typically follows a structured path, requiring both skill-building and strategic career moves. Most professionals start as Information System Security Officers (ISSOs), where they gain practical experience with security controls – an essential stepping stone toward leadership roles.
Moving from ISSO to ISSM
Making the leap from ISSO to ISSM generally takes about 3 to 5 years of experience managing security controls for classified systems. As an ISSO, you handle tasks like running vulnerability scans and drafting security documentation. This hands-on work not only builds technical expertise but also establishes the credibility needed to advance. To move into an ISSM role, you’ll need to demonstrate a solid understanding of the Risk Management Framework (RMF), earn relevant certifications, and hone your communication skills. These skills are vital because ISSMs often act as the main point of contact between technical teams and agencies like the Defense Counterintelligence and Security Agency (DCSA). Once this foundation is in place, transitioning into mid-level roles becomes more attainable.
Mid-Level ISSM Responsibilities
At the mid-level, ISSMs take on a mix of technical and leadership duties. This includes managing vulnerability assessments, coordinating the Authorization to Operate (ATO) process, and overseeing small teams. Tools like ACAS/Nessus for scanning, STIG Viewer for system hardening, and various Security Information and Event Management (SIEM) platforms for log analysis become part of your daily toolkit. Beyond technical tasks, you’ll be expected to mentor junior staff, conduct risk assessments, and prepare security documentation for audits, all while ensuring compliance with NIST 800-53 controls.
Typically, mid-level ISSMs have 5 to 8 years of experience and earn salaries ranging from $101,000 to $150,000 per year, depending on factors like location and clearance level. This role serves as a bridge to senior positions, offering a chance to refine your expertise and expand your influence.
Advancing to Senior ISSM and Leadership Roles
Senior ISSM roles shift the focus from managing individual systems to overseeing entire security operations across facilities or business units. Responsibilities often include leading comprehensive cybersecurity programs and serving as the primary liaison for agencies like DCSA or SAPCO. These positions usually require 8 to 12 years of experience and come with salaries between $150,000 and $203,000 annually.
To move beyond senior-level roles, pursuing executive-level credentials like the Certified Chief Information Security Officer (CCISO) can be a game-changer. This certification emphasizes skills like budget management, vendor oversight, and effective communication with executives. According to EC-Council, 76% of professionals reported a salary boost after earning the CCISO certification, highlighting that "technical excellence alone won’t earn a seat at the executive table" [7].
Challenges and Career Strategies for Cleared ISSMs
Navigating Security Clearance Processes
Maintaining a security clearance requires constant attention and a disciplined lifestyle. The introduction of Continuous Evaluation (CE) has transformed how clearance holders are monitored. Instead of periodic reinvestigations, such as the traditional five-year cycle for Top Secret clearances, CE ensures risk factors are assessed in real time. Dan Meyer, Esq., Partner at Tully Rinckey PLLC, explains:
"Continuous Evaluation (CE) shifts the focus to people presenting risk. If you do not present a risk, you will be reviewed less and less" [8].
Financial stability plays a key role in maintaining clearance. Meyer highlights this by stating:
"Financial instability is one of the leading causes of clearance revocation" [8].
This underscores the importance of staying financially responsible to avoid potential issues. Clearance holders must also self-report various activities, including foreign travel, foreign contacts, financial problems like bankruptcy or wage garnishments, criminal charges, and substance use. It’s important to note that THC use remains illegal under federal law and can jeopardize your clearance [8]. Working closely with your Facility Security Officer (FSO) and consulting a national security attorney can help you navigate these requirements effectively. Managing these challenges is a critical step toward building a stable and successful career.
Using Career Resources for Cleared Professionals
Once you’ve addressed clearance-related hurdles, tapping into specialized career resources can help you advance. Platforms tailored to the cleared community, such as Cleared Cyber Security Jobs, offer tools like personalized job alerts, resume builders, and career guidance specifically for security-cleared professionals [9]. These platforms also provide insights into hiring trends from major defense contractors, helping you identify the certifications and skills currently in demand [9][10][11].
Setting up automated job alerts for ISSM positions in key locations – like Arlington, VA; Fort Meade, MD; and El Segundo, CA – can help you stay informed about regional needs and specific agency requirements [9][10][11]. Additionally, reviewing recommendations for "similar jobs" can reveal emerging trends, such as advanced RMF (Risk Management Framework) implementations or expertise in cloud security, which are becoming increasingly sought after [10][11].
Continuing Education and Advanced Certifications
Staying competitive in the cleared cybersecurity field requires a commitment to continuous learning. The landscape evolves rapidly, and advanced education can set you apart. While foundational certifications like CISSP and CISM remain important, pursuing advanced credentials in areas like cloud security or specific compliance frameworks ensures your skills align with current threats and Department of Defense (DoD) requirements. Monitoring job postings from top contractors can help you identify which certifications are gaining popularity, allowing you to make informed decisions about your professional development [9][10][11].
Conclusion: Building a Successful Career as a Cleared ISSM
Key Points to Remember
To build a successful career as a cleared ISSM, you need a mix of technical expertise and leadership abilities. Starting as an ISSO is a smart move to gain hands-on experience with RMF and ATO processes. From there, earning DoD 8140-approved certifications like CISSP, CISM, or GSLC can set you on the path for career advancement [2][13].
For senior ISSM roles, executive-level skills become crucial. These include managing budgets, overseeing vendors, and effectively communicating the value of cybersecurity to leadership. With 62% of corporate boards identifying cybersecurity as their top organizational risk, understanding how to speak the language of executives is more important than ever [7]. If you’re aiming for higher leadership positions, the Certified Chief Information Security Officer (CCISO) certification can help bridge the gap between technical expertise and executive responsibilities. Notably, 76% of CCISO holders report salary increases [7].
To stay ahead, make use of specialized resources to track hiring trends and set up job alerts. Veterans should take advantage of preference points on USAJOBS, which can provide a significant edge – up to a 30-point lead – in federal hiring processes [3].
These steps create a solid foundation for long-term growth in an ISSM career.
Final Thoughts on ISSM Career Growth
The cleared cybersecurity field offers promising opportunities for those who commit to ongoing professional development. With employment expected to grow by 29% between 2024 and 2034, and median salaries around $125,000 (with top earners making up to $186,000), the potential rewards are substantial [4][12]. Joseph Stenaka, CISO at the Social Security Administration, shared how earning his CCISO certification was pivotal in achieving one of the most impactful roles in government cybersecurity:
"Being selected as the CISO for the Social Security Administration, one of the best cybersecurity jobs in the US government, was my most impactful achievement after earning CCISO" [7].
Staying ahead in this field means keeping up with emerging trends, such as AI-driven threat intelligence and cloud security. In fact, 69% of top-performing CISOs attribute their success to continuous learning and development [7]. Remember, your career growth depends on more than just technical skills – it hinges on your ability to adapt, lead with strategy, and maintain the ethical and financial standards required to hold a clearance.
FAQs
How can I move from ISSO to ISSM quickly?
To move swiftly from an ISSO role to an ISSM position, prioritize earning certifications such as CISSP or Security+. These credentials not only validate your technical knowledge but also signal your commitment to the field. Alongside certifications, focus on developing leadership skills by seeking roles that involve managing ISSOs or overseeing audits. Gaining hands-on experience with security policies, risk management, and compliance frameworks like RMF is equally important. A combination of these elements – certifications, leadership experience, and practical expertise – can significantly speed up your career advancement.
Do I need TS/SCI before applying for ISSM jobs?
Yes, many ISSM positions, especially those tied to classified or sensitive programs, mandate a TS/SCI clearance as a prerequisite. This requirement is standard for roles in security-cleared settings.
Which certification is best for ISSM: CISSP, CISM, or GSLC?
The best certification for an ISSM (Information System Security Manager) largely depends on the specific responsibilities of the role. CISSP (Certified Information Systems Security Professional) is highly regarded due to its extensive coverage of cybersecurity and risk management principles. On the other hand, CISM (Certified Information Security Manager) is tailored for those focusing on security management and policy creation, making it a great fit for managing security programs.
While the GSLC (GIAC Security Leadership Certification) emphasizes leadership and incident response, it’s less frequently associated with ISSM roles. Ultimately, CISSP and CISM stand out as the most sought-after certifications for professionals in this field.
