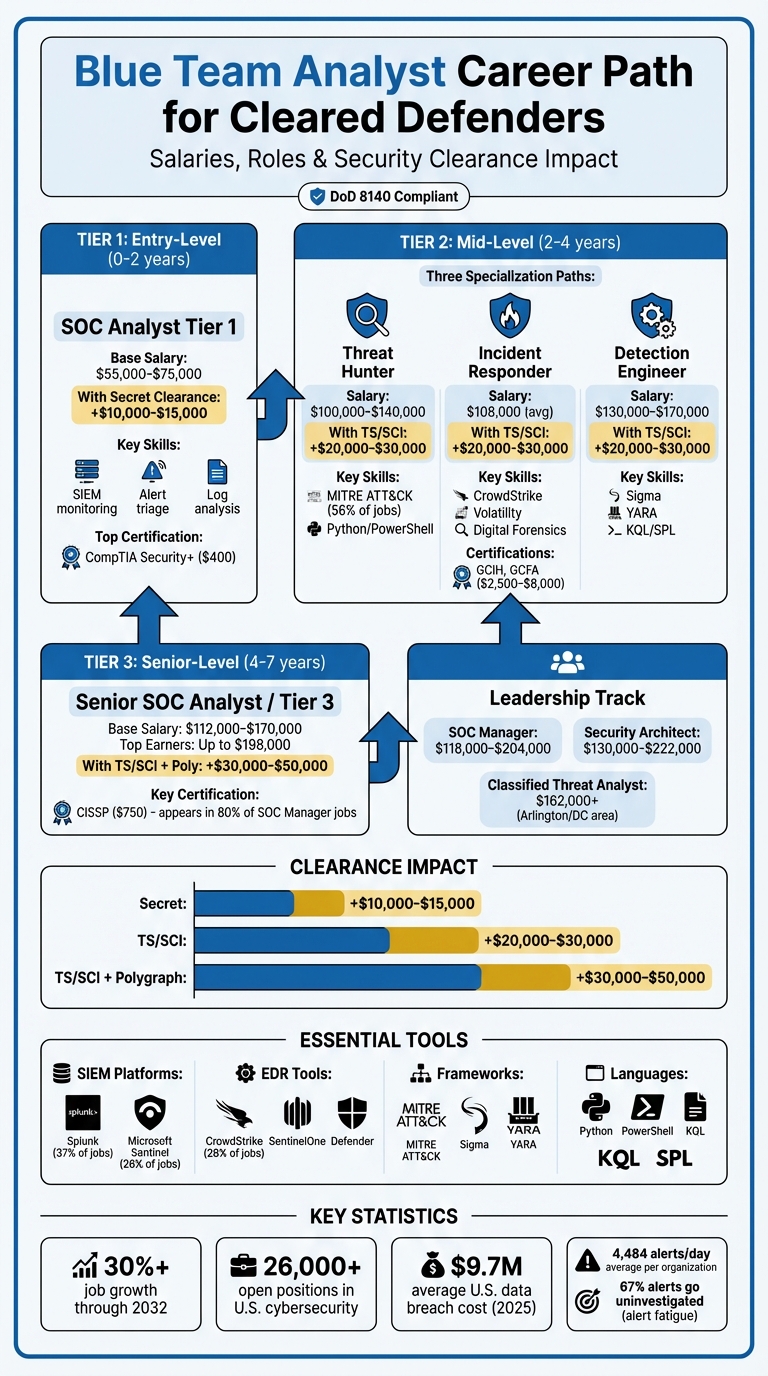
Looking to excel in cybersecurity? Blue Team Analysts play a vital role in protecting digital systems by monitoring networks, detecting threats, and responding to incidents. With over 26,000 open cybersecurity jobs in the U.S. and a 30% projected job growth through 2032, this field offers abundant opportunities – especially for those with a U.S. government security clearance.
Key takeaways:
- Entry roles like SOC Analyst start at $55,000–$75,000, while senior roles like Security Architect can exceed $150,000.
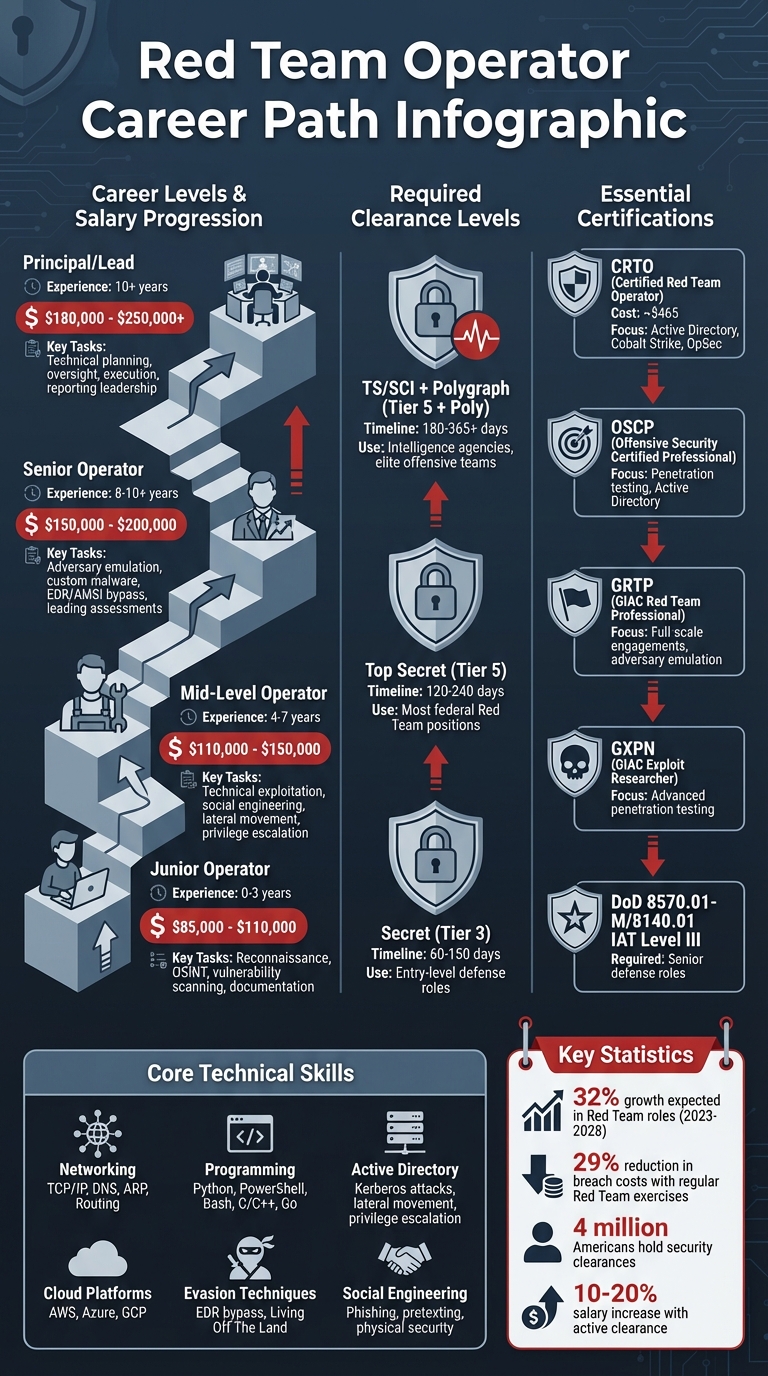
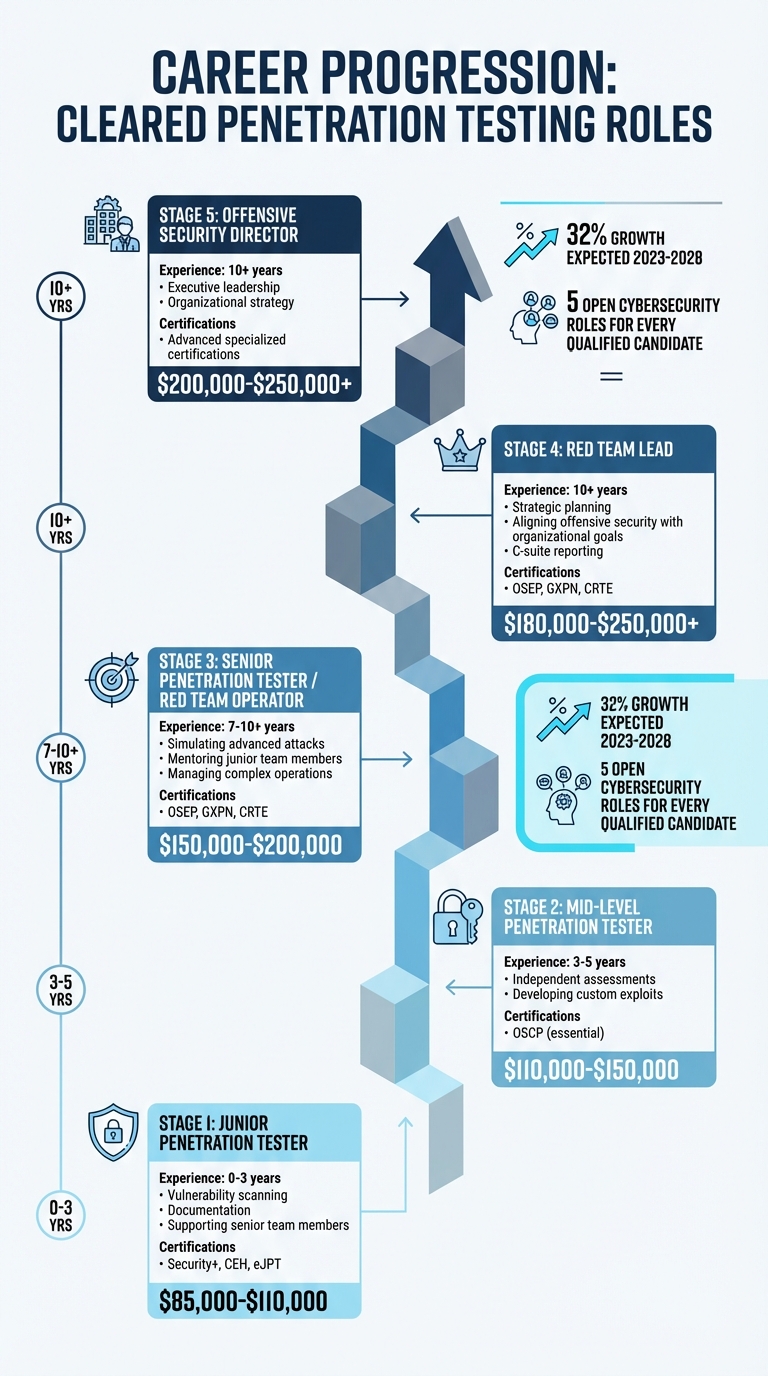
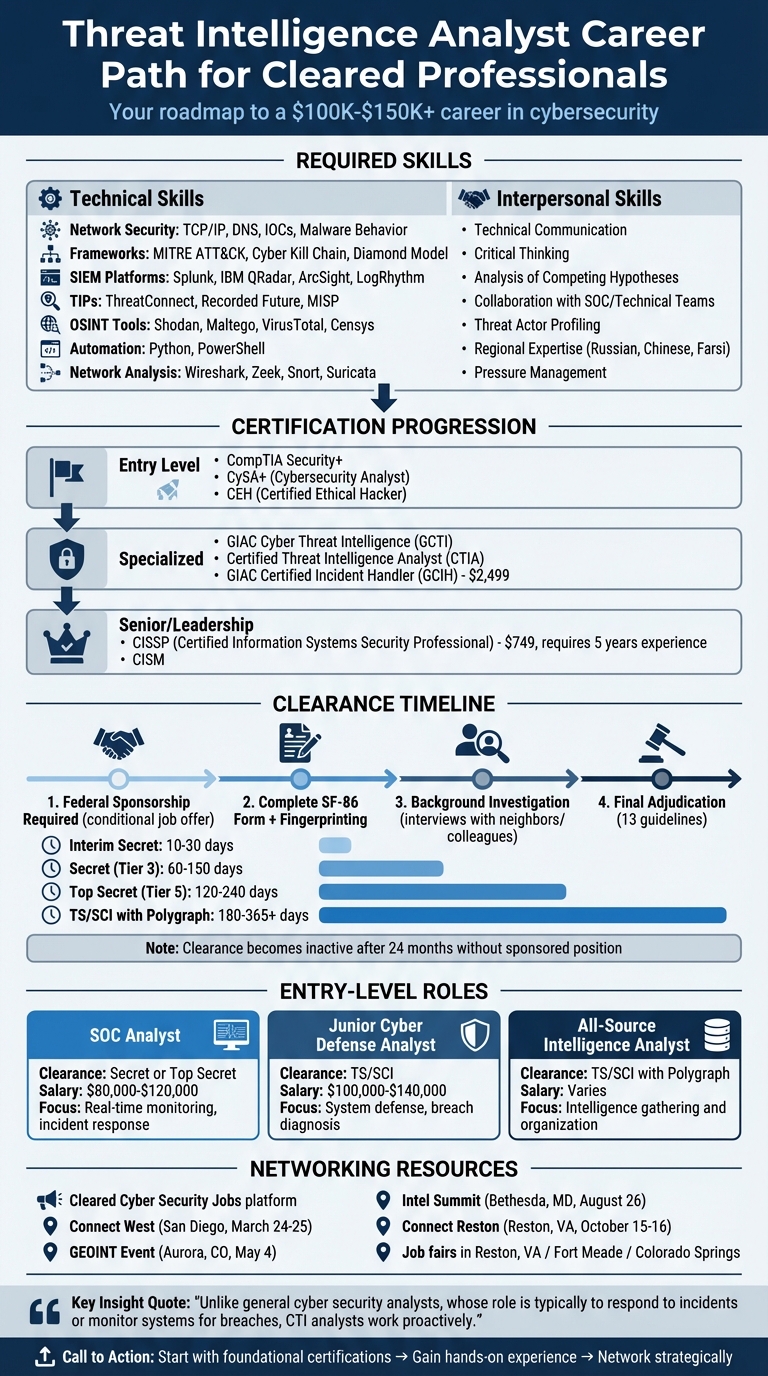
- A security clearance boosts salaries by $10,000–$50,000 depending on clearance type (Secret, TS/SCI, or TS/SCI with polygraph).
- Essential skills include SIEM tools (Splunk, Sentinel), scripting (Python, PowerShell), and frameworks like MITRE ATT&CK.
- Certifications like CompTIA Security+, GIAC GCIH, and CISSP are highly valued in cleared environments.
- Specialized roles like Threat Hunter, Incident Responder, and Detection Engineer offer salaries from $100,000 to $170,000.
Whether you’re starting as a Tier 1 SOC Analyst or aiming for advanced roles, this guide outlines the skills, tools, and certifications to thrive in the cybersecurity field while safeguarding national security.
Blue Team Career Path: Roles, Salaries, and Clearance Premiums
Blue Team Roles in Cleared Cybersecurity
Core Blue Team Positions and Duties
Blue Team professionals are the defenders of cybersecurity, working to monitor, detect, and respond to threats. Each role within the team contributes to a layered defense strategy, ensuring systems remain secure.
SOC Analysts are at the heart of defensive operations. These analysts are divided into tiers based on their responsibilities:
- Tier 1 analysts focus on monitoring SIEM platforms, conducting initial triage, and escalating incidents as needed.
- Tier 2 analysts dive deeper into escalated incidents, performing more detailed investigations.
- Tier 3 analysts tackle the most complex threats, using advanced forensic tools and creating custom detection logic.
As CyberDefenders Team aptly describes:
"SOC analysts are the digital sentinels who constantly watch over an organization’s IT infrastructure, hunting for signs of malicious activity."
Other key roles include:
- Threat Hunters, who actively search for hidden attackers using hypothesis-driven investigations.
- Incident Responders, responsible for containing breaches, removing threats, and restoring systems to normal operations.
- Detection Engineers, who craft and refine detection rules (e.g., Sigma, YARA), aiming to reduce false positives while improving threat detection.
- Threat Intelligence Analysts, who monitor emerging threats, assess risks, and provide actionable insights.
- Digital Forensics Analysts, who gather and analyze digital evidence for investigations or legal purposes.
In cleared environments, roles like Information Systems Security Managers (ISSMs) and Information Systems Security Officers (ISSOs) oversee the management of accredited systems on classified networks such as SIPRNet.
| Core Blue Team Position | Primary Responsibilities |
|---|---|
| SOC Analyst | Monitors SIEM platforms, investigates security alerts, and performs initial triage |
| Incident Responder | Contains and investigates active breaches, restoring normal operations |
| Threat Hunter | Proactively searches for concealed attackers and advanced threats |
| Detection Engineer | Builds and tunes detection rules (e.g., Sigma, YARA) to minimize false positives |
| Threat Intelligence Analyst | Analyzes the threat landscape to identify risks and deliver actionable insights |
Each of these roles contributes to a well-rounded defense, and in cleared environments, their impact is amplified by access to classified tools and resources.
Why Security Clearance Matters
For Blue Team professionals, a security clearance is more than just a credential – it’s a key that unlocks access to sensitive environments and advanced career opportunities. While technical expertise is essential, a clearance allows defenders to operate in classified spaces, such as SIPRNet, or work within specialized cloud platforms like AWS GovCloud and Microsoft Azure Government.
Cleared roles often come with higher pay, reflecting their critical nature. The Trusted Workforce 2.0 initiative has modernized the clearance process, replacing periodic reinvestigations with Continuous Vetting. This real-time monitoring approach ensures that cleared individuals maintain their eligibility without frequent disruptions. It also introduces a "clear once, trusted everywhere" standard, making it easier for professionals to transition between federal agencies and contractors.
For instance, an Interim Secret clearance can be granted in as little as 10 to 30 days, while a Top Secret/SCI clearance with a polygraph may require 180 to 365+ days to complete [2]. The Defense Counterintelligence and Security Agency (DCSA) oversees most federal background checks, and clearances generally become inactive after 24 months if the individual leaves a sponsoring role [2].
Maintaining a clearance requires strict adherence to reporting requirements. Cleared professionals must self-report significant life events, such as arrests or major financial changes, to their Facility Security Officer. This ensures continued trustworthiness and compliance.
The demand for skilled defenders is growing rapidly. Employment for information security analysts is expected to grow over 30% by 2032. With the average cost of a U.S. data breach projected to surpass $9.7 million by 2025, organizations are prioritizing investments in professionals who can safeguard their most sensitive assets [3].
sbb-itb-bf7aa6b
Blue Team vs Red Team: Become an SOC Analyst [Complete Beginner Guide]
Starting Your Career as a SOC Analyst
The role of a Security Operations Center (SOC) Analyst is often the starting point for those entering the world of Blue Team cybersecurity. In fact, according to ISC2’s 2025 Workforce Study, it’s currently the most sought-after position in the cybersecurity field [7]. For those with security clearances, the opportunities are even better – these professionals can often skip entry-level roles and jump straight into higher-paying positions due to a smaller pool of qualified candidates [7].
Tier 1 SOC Analysts focus on monitoring SIEM (Security Information and Event Management) platforms, validating alerts, and following predefined playbooks to determine whether an event requires escalation. This involves sifting through thousands of alerts daily – on average, organizations face 4,484 alerts per day, with 67% going uninvestigated because of alert fatigue [7]. While the work may feel repetitive at first, it’s a critical step in developing the pattern recognition skills needed to identify threats effectively.
For cleared professionals, career advancement often happens more quickly because of the limited number of eligible candidates [7]. These foundational experiences as a SOC Analyst pave the way for more specialized roles and leadership opportunities. Let’s dive into the skills and tools that are essential for excelling in this role.
Required Skills and Tools for SOC Analysts
SOC Analysts rely on a combination of technical tools and foundational knowledge to detect and respond to threats. Here’s a breakdown of what you need to know:
- SIEM Platforms: These are the backbone of SOC operations. Familiarity with tools like Splunk and Microsoft Sentinel is essential, as they are featured in 37% and 26% of job postings, respectively [7]. Splunk uses Search Processing Language (SPL), while Sentinel relies on Kusto Query Language (KQL). Specializing in a specific platform can also increase your earning potential – Splunk experts, for example, average $125,000 annually compared to generalists who earn between $70,000 and $90,000 [7].
- Log Analysis: This is the bread and butter of SOC work. Analysts must interpret logs from sources like Windows Security Event Logs, Linux Syslog entries, and cloud audit logs (e.g., AWS CloudTrail and Azure Entra ID) [11][12]. Understanding what normal activity looks like in these logs helps you spot anomalies – like a failed logon (Event ID 4625) followed by a successful one (Event ID 4624) from an unusual location, which could point to credential stuffing or password spraying.
- EDR Platforms: Tools such as CrowdStrike Falcon and Microsoft Defender for Endpoint allow analysts to dig deeper into host-level activity. These platforms provide insights into suspicious processes, command-line activity, and malware behavior, making them invaluable for investigating ransomware or lateral movement [11].
- Scripting: Knowledge of Python or PowerShell is a game-changer. Automating repetitive tasks like log parsing or threat intelligence enrichment can save time and demonstrate your readiness for Tier 2 roles [7].
- Networking Basics: A strong grasp of TCP/IP, DNS, and VPNs is crucial, along with experience in packet analysis using tools like Wireshark [12]. This knowledge helps determine whether network traffic is malicious or benign.
- MITRE ATT&CK Framework: This framework is becoming a must-have skill. It helps map adversary tactics and techniques, aiding in threat detection and proactive defense. For instance, recognizing behaviors tied to techniques like T1078 (Valid Accounts) or T1566 (Phishing) can significantly enhance investigations [6][7][9].
To develop these skills, creating a home lab is an excellent strategy. Use free tools like Splunk Free or Elastic SIEM, set up vulnerable virtual machines, and practice analyzing alerts from simulated attacks [8][10]. Documenting your findings in 3–5 case studies can also help showcase your expertise to potential employers [5][10].
Salary Ranges and Career Growth
Mastering these tools and skills doesn’t just prepare you for the job – it can also lead to impressive earning potential. The average salary for a SOC Analyst in the U.S. is about $102,000, with ranges typically falling between $78,000 and $140,000 [3]. Security clearances can significantly boost these figures, adding $10,000–$15,000 for a Secret clearance, $20,000–$30,000 for a TS/SCI clearance, and $30,000–$50,000 for a TS/SCI with a polygraph [7].
SOC career paths generally follow a tiered structure:
- Tier 1 Analysts (0–2 years of experience) earn $55,000–$98,000, with an extra $10,000–$15,000 for Secret clearance.
- Tier 2 Analysts (2–4 years of experience) earn $75,000–$144,000, with an additional $20,000–$30,000 for TS/SCI clearance.
- Tier 3 Analysts (4–7 years of experience) command $112,000–$170,000, with $30,000–$50,000 more for a polygraph [7].
The demand for SOC Analysts is surging, with employment for information security analysts expected to grow by 35% through 2031 [10]. As data breaches in the U.S. now average over $9.7 million in costs, organizations are increasingly investing in skilled professionals to minimize risk and mitigate damages [3].
Certifications are another way to accelerate your career. Start with CompTIA Security+ (about $400), which is often required for DoD 8140 compliance and serves as a baseline credential for most cleared roles [7]. From there, consider the Microsoft SC-200 ($165) if you’re working with Sentinel, or the CompTIA CySA+ ($400) to prepare for Tier 2 roles [7]. Advanced certifications like GIAC’s GCIH or GCFA, while pricier ($2,500–$8,000), are highly respected in government environments and are ideal once you’ve gained some experience [7].
As Cybersecurity Jobs List puts it:
"Generalists get hired. Specialists get promoted." [7]
Mid-Level Specialization Paths
After spending 2–4 years as a SOC Analyst, many cleared professionals opt for specialized technical roles. These roles not only lead to higher salaries but also open doors to exclusive opportunities [7]. With a solid SOC foundation, you can branch into one of three popular mid-level specializations: Threat Hunter, Incident Responder, or Detection Engineer. Each path requires distinct skills and offers its own set of challenges and rewards.
These roles mark a shift from reactive monitoring to proactive defense strategies. Instead of just responding to alerts, you might find yourself hunting for hidden threats, crafting detection rules, or managing responses during security incidents.
Threat Hunter
Threat Hunters work under the assumption that adversaries may already have infiltrated the network. Their job is to proactively investigate and uncover stealthy attackers [4]. Tools like the MITRE ATT&CK framework and its Navigator tool are essential for identifying detection gaps. Notably, 56% of Threat Hunter job postings specifically mention expertise in ATT&CK [7].
To succeed in this role, you’ll need a strong grasp of malware analysis, behavioral analytics, and anomaly detection [4]. Scripting knowledge in languages like Python, PowerShell, Go, or Rust is also critical. For example, Python scripts can help correlate unusual DNS queries with known command-and-control servers, while PowerShell can track lateral movement across endpoints.
Threat Hunters typically earn between $100,000 and $140,000, with cleared positions offering an additional $20,000–$30,000 for TS/SCI clearances [8]. This role is ideal if you thrive on investigative work and want to stay hands-on with security operations. Similarly, the skills developed here can transition seamlessly into roles like Incident Responder.
Incident Responder
Often called the "troubleshooters" of the security world, Incident Responders are the first line of defense during a breach [3]. Their responsibilities include containing the breach, neutralizing threats, and restoring normal operations. This role demands quick decision-making and a methodical approach to forensic investigations.
Daily tasks might involve forensic acquisition, memory analysis with tools like Volatility, and reconstructing attack timelines to understand the sequence of events [4]. Familiarity with Endpoint Detection and Response (EDR) platforms such as CrowdStrike and SentinelOne is critical, as is a solid understanding of network protocols and digital forensics [3]. Certifications like the GIAC Certified Incident Handler (GCIH) or Certified Forensic Analyst (GCFA) are particularly valued in government-focused roles [13][3].
The average salary for Incident Responders in 2026 is projected to be around $108,000, with top earners making up to $142,000 [3]. With the average cost of a data breach in the U.S. exceeding $9.7 million, companies are willing to invest significantly in skilled responders who can minimize damages and speed up recovery efforts [3].
Detection Engineer
Detection Engineers focus on integrating threat intelligence into SOC operations by developing and fine-tuning SIEM detection rules [4]. This role has gained prominence as organizations move toward proactive, automated defense strategies [8].
In this role, you’ll design SIEM correlation rules, YARA signatures, and Sigma rules. Sigma, in particular, allows you to write detection logic once and deploy it across multiple SIEM platforms like Splunk, Sentinel, and Elastic [14]. Mastery of query languages (e.g., SPL, KQL, Lucene) and familiarity with version control and CI/CD practices for detection-as-code are essential [4][15].
Detection Engineers can expect salaries ranging from $130,000 to $170,000 in 2026 [8]. If you enjoy creating systems and seeing the tangible impact of your work, this path might be a perfect fit.
| Role | Primary Focus | Key Tools/Skills | Typical 2026 Salary |
|---|---|---|---|
| Threat Hunter | Proactive threat discovery | MITRE ATT&CK, Behavioral Analytics | $100,000–$140,000 [8] |
| Incident Responder | Containment & forensic investigation | CrowdStrike, Volatility, FTK | $108,000 [3] |
| Detection Engineer | Rule creation & automation | Splunk, Sentinel, SIGMA, YARA | $130,000–$170,000 [8] |
Technical Skills and Certifications
To thrive in a Blue Team career, you need the right mix of tools and certifications. Platforms like Splunk and Microsoft Sentinel are staples in SOC operations, showing up in 37% and 26% of job postings, respectively [7]. Endpoint Detection and Response (EDR) tools, such as CrowdStrike Falcon and SentinelOne, are equally important, with CrowdStrike appearing in 28% of SOC-related roles [7]. On top of that, scripting skills in Python and PowerShell are invaluable for automating routine tasks and improving efficiency.
Understanding threat intelligence platforms like MISP and Recorded Future is another critical skill, as these tools help you interpret alerts by linking them to adversary behaviors. Network analysis tools like Wireshark are indispensable when you need to dig into subtle traffic anomalies. For those working in cleared environments, maintaining strict operational security (OPSEC) and precise documentation during forensic investigations is a must.
Key Tools and Platforms
Your technical toolkit should cover several key areas. Here are some of the essential tools and skills to focus on:
- SIEM Platforms: Splunk, Microsoft Sentinel, Elastic, QRadar, and Wazuh [7].
- EDR Tools: CrowdStrike Falcon, SentinelOne, Microsoft Defender for Endpoint, and Carbon Black [7].
- Scripting and Query Languages: Python, PowerShell, Bash, KQL (Kusto Query Language), and SPL (Search Processing Language) [7].
- Threat Intelligence Tools: MISP, Recorded Future, ThreatConnect, VirusTotal, and the MITRE ATT&CK framework [7].
- Forensic Tools: EnCase, FTK, Autopsy, Volatility, and Wireshark [1].
- Detection Rule Frameworks: Sigma and YARA for crafting custom detection logic [7].
Specializing in specific platforms can make you stand out. For example, mastering KQL for Microsoft Sentinel or SPL for Splunk can give you an edge. Building a GitHub portfolio showcasing automation scripts, like a Python tool that pulls indicators of compromise from threat intelligence platforms, is another way to highlight your practical skills.
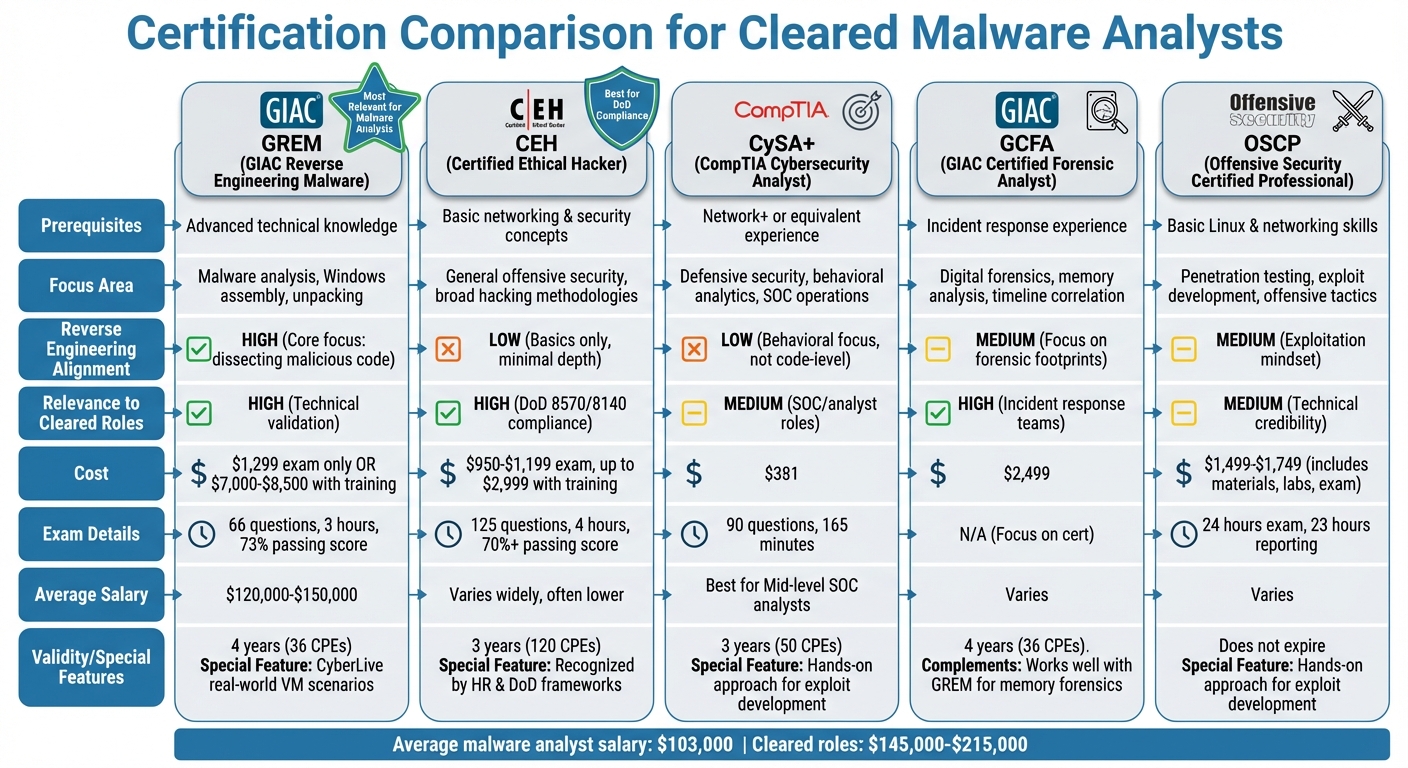
Certification Roadmap
Certifications are a powerful way to validate your skills and meet the requirements for clearance-based roles. Your certification path should align with your experience level and the Department of Defense (DoD) 8140 compliance standards for cleared environments.
- Entry-Level: Begin with the CompTIA Security+ certification (about $400), which lays the foundation for security roles in DoD settings. For those focusing on Microsoft Sentinel, the Microsoft SC-200 certification (around $165) is a great addition.
- Mid-Level: As you advance, consider certifications like CompTIA CySA+ (around $400) for behavioral analytics or GIAC certifications such as GCIH (Incident Handling) and GCFA (Digital Forensics). GIAC certifications are highly respected in government and high-assurance roles, though they come with a hefty price tag ranging from $2,500 to $8,000.
- Senior/Leadership Roles: For higher-level positions, the CISSP (Certified Information Systems Security Professional, approximately $750) is often a requirement. It appears in 80% of SOC Manager job postings and 47% of security management roles [7]. For specialized tracks, certifications like GIAC Cyber Threat Intelligence (GCTI) for threat hunting or the EnCase Certified Examiner (EnCE) for advanced forensic work are excellent choices.
| Career Stage | Primary Focus | Key Certifications | Typical Cost |
|---|---|---|---|
| Entry-Level | Baseline Security & Compliance | CompTIA Security+, Microsoft SC-200 | $165–$400 |
| Mid-Level | Detection & Response | CompTIA CySA+, GIAC GCIH, GIAC GCFA | $400–$8,000 |
| Senior/Leadership | Architecture & Management | CISSP, GIAC GDSA | $750+ |
Strategically pursuing these certifications not only validates your expertise but also positions you for growth in high-demand, clearance-driven roles.
Senior Roles and Leadership Positions
Once you’ve honed your expertise at the mid-level, senior roles call for a shift in focus toward proactive defense and leadership. Instead of just reacting to threats, you’ll be crafting detection strategies, leading threat hunts, and mentoring less-experienced analysts. Having a security clearance at this stage can significantly boost your earning potential. For example, a Secret clearance can add $10,000–$15,000 to your salary, while a TS/SCI clearance bumps that up by $20,000–$30,000. If you hold a TS/SCI with a polygraph, you could see an additional premium of $30,000–$50,000 [7].
Senior positions generally split into two main paths: management and technical specialization. Management roles, such as SOC Manager or Director of SecOps, focus on leading teams, managing budgets, and aligning security efforts with business goals. On the other hand, technical roles like Security Architect or Detection Engineer involve designing advanced security systems and creating custom detection rules using frameworks like MITRE ATT&CK. While both tracks are well-compensated, technical roles tend to offer higher salaries. For instance, Security Architects typically earn between $130,000 and $222,000, whereas SOC Managers see salaries ranging from $118,000 to $204,000 [7]. This split allows professionals to choose between leadership and technical mastery, depending on their interests and strengths.
Leadership and Management Roles
Leadership roles require a different skill set compared to technical, hands-on positions. As a SOC Manager, you’ll oversee alert workflows, manage team operations, and communicate critical security updates to executives. Certifications like the CISSP are highly sought after in these roles, appearing in 80% of SOC Manager job postings and 47% of broader security management listings [7]. If you’re aiming for governance-focused roles, the CISM certification is another valuable credential, showing up in 35% of management job postings and costing around $600 to obtain [7].
For those staying in senior technical roles, positions like Tier 3 Analyst or Threat Intelligence Lead emphasize deep expertise with platforms and tools. Proficiency in query languages such as KQL for Microsoft Sentinel or SPL for Splunk can set you apart. Senior SOC analysts with 4–7 years of experience and a solid grasp of MITRE ATT&CK typically earn between $112,000 and $170,000, with top earners reaching $198,000 [7]. Employers like Leidos offer salaries ranging from $122,000 to $221,000 for similar roles, while Booz Allen Hamilton pays between $88,000 and $201,000 [7]. These roles highlight the value of technical depth, especially in organizations requiring advanced security expertise.
Clearance-Only Opportunities
Holding an active security clearance unlocks access to roles that are unavailable in the commercial sector. These include positions like classified threat analyst, where you track advanced persistent threats targeting government systems, or Information Systems Security Manager (ISSM) roles, which focus on securing classified networks such as SIPRNet. Defense-focused operations centers handling sensitive intelligence often require TS/SCI clearances, and these positions command some of the highest salaries in the field. In areas like Arlington, VA, or Washington, D.C., top salaries for these roles can exceed $162,000 [7].
To maintain your clearance and eligibility for these roles, you’ll need to comply with Continuous Vetting requirements. This includes reporting life events like arrests, significant debt, or foreign contacts promptly. Keeping your digital hygiene in check ensures the trust needed to retain these exclusive opportunities [2].
Conclusion
A career as a cleared Blue Team Analyst hinges on three key factors: obtaining a security clearance, keeping your skills sharp, and strategically pursuing certifications. Security clearance plays a major role in boosting salaries, with bonuses ranging from $10,000–$15,000 for Secret clearance, $20,000–$30,000 for TS/SCI, and as much as $30,000–$50,000 for TS/SCI with polygraph. It also opens doors to work on classified networks like SIPRNet and specialized environments such as AWS GovCloud [2][7].
Advancing in this field requires moving beyond basic playbooks to embrace automation. Skills in Python and PowerShell can elevate you from Tier 1 to Tier 2 roles, while expertise in the MITRE ATT&CK framework and creating custom detection logic with tools like Sigma or YARA is often necessary for Tier 3 positions [7]. Begin with certifications aligned with DoD 8140 requirements, then focus on specialized and advanced certifications to prepare for leadership roles [7]. These technical skills, combined with your clearance, form the backbone of a successful career in this dynamic field.
Maintaining your clearance under Continuous Vetting involves actively reporting major life events – such as arrests, significant debt, or foreign connections – to your Facility Security Officer. Instead of the traditional 5- or 10-year reinvestigation cycles, the system now relies on real-time monitoring of criminal, financial, and travel records [2]. Any technical foreign contacts must be carefully documented, as they are closely examined under "Foreign Influence" guidelines [2].
The cleared Blue Team field is expected to grow by over 30% through 2032 [3], with SOC analysts topping the list of most in-demand cybersecurity roles in ISC2’s 2025 Workforce Study [7]. Whether starting as a Tier 1 analyst with a salary range of $66,000–$102,000 or aiming for senior roles that pay $112,000–$170,000 or more, combining clearance, technical skills, and targeted certifications creates a clear path to success. Plus, your clearance remains active for 24 months after leaving a position, providing a valuable window to transition without undergoing a full reinvestigation [2].
FAQs
Can I start a SOC job without a clearance?
Yes, you can start a SOC job without a security clearance, but your options might be restricted to specific entry-level roles. Obtaining a clearance can significantly boost your career opportunities and open doors to more advanced positions in the field.
Which clearance level boosts my salary the most?
The TS/SCI clearance level stands out as the top-tier option for salary potential, with professionals earning an average of $131,907. When paired with additional certifications, that number can climb to $148,314. This clearance offers a 40% pay premium compared to lower clearance levels, making it a game-changer for those looking to boost their earnings.
What should my first 90 days of SOC learning include?
To get started as a SOC analyst, focus on building core skills, gaining hands-on experience, and earning relevant certifications. Begin by understanding the key responsibilities of a SOC analyst, such as monitoring SIEM tools and analyzing security alerts.
Dive into the basics of cybersecurity, including threat detection and incident response, by taking advantage of free online courses. Boost your practical knowledge through labs and simulations, which allow you to practice in real-world-like environments.
Certifications can provide a competitive edge. Consider pursuing credentials like Blue Team Level 1 (BTL1) to validate your skills. To further enhance your expertise, study real-world SOC scenarios. This will help you learn how to prioritize risks and implement effective containment strategies. With consistent practice, you’ll build confidence and establish a strong foundation for a successful career in cybersecurity.