The Certified Red Team Operator (CRTO) certification is a practical, hands-on credential from Zero-Point Security, designed for professionals in offensive cybersecurity, particularly those in government and defense roles. Here’s what you need to know:
- Focus: Covert operations in Windows and Active Directory environments using Cobalt Strike, covering reconnaissance, credential theft, lateral movement, persistence, and detection evasion.
- Relevance: Tailored for cleared professionals, it aligns with the needs of government and defense sectors where stealth and precision are critical.
- Exam: A 48-hour practical test spread over four days, requiring at least 70% to pass. The new format emphasizes performance and stealth, with penalties for triggering defenses.
- Skills Gained: Active Directory attacks (e.g., Kerberos, ADCS exploitation), OPSEC strategies, and mastering Cobalt Strike for adversary simulation.
- Career Impact: Recognized by CREST, it helps professionals transition into or excel in cleared red team roles, showcasing expertise in advanced tactics and operational security.
The CRTO certification is a stepping stone for professionals aiming to excel in red teaming, offering practical skills and industry recognition. Whether you’re transitioning from penetration testing or advancing within cleared environments, this credential prepares you for the challenges of modern cybersecurity operations.
Is the CRTO Worth It?
sbb-itb-bf7aa6b
Why CRTO Matters for Cleared Red Team Professionals
Cleared red team roles demand expertise that goes far beyond basic penetration testing. The Certified Red Team Operator (CRTO) certification addresses the specific needs of government and defense sector roles by focusing on adversary simulation rather than just identifying vulnerabilities. While penetration testing often involves short, noisy engagements to uncover as many weaknesses as possible, red teaming requires a covert, long-term approach to evaluate an organization’s detection and response capabilities. In cleared environments, stealth and mission success are non-negotiable.
The certification’s emphasis on Active Directory (AD) and Kerberos attacks is particularly relevant to government agency infrastructures. Techniques like Golden Ticket attacks, Kerberos delegation abuse, and ADCS exploitation are covered, reflecting the tactics used by sophisticated adversaries. Candidates are trained to start with minimal access and navigate through complex environments to meet specific operational goals, mirroring the challenges faced by cleared organizations in combating modern cyber threats.
How CRTO Skills Match Cleared Job Requirements
The CRTO certification directly aligns with the responsibilities of cleared red team operators. It provides hands-on experience with Cobalt Strike, a widely used command-and-control platform favored by professional red teams and real-world adversaries alike. Through this training, candidates learn to execute covert operations in realistic Windows enterprise environments, emphasizing AD-focused techniques that are critical for nearly all cleared engagements.
A key aspect of the certification is its focus on Operational Security (OPSEC). In the updated exam format, 50% of the total score is tied to OPSEC performance[6]. Points are deducted for triggering antivirus systems, being detected by security controls, or creating unnecessary activity on the network. Soham, a Security Consultant at Cognisys Group Labs, highlights this importance:
"If your OPSEC score falls below a certain threshold, failing the exam is inevitable, irrespective of objective completion"[6].
This mirrors real-world cleared operations, where detection can jeopardize an entire mission and expose sensitive methodologies.
The exam itself is a 48-hour practical challenge that evaluates candidates on outcome-based objectives. Participants must achieve goals like gaining domain dominance, establishing persistence, and exfiltrating data – all while avoiding detection. Success requires maintaining access, pivoting through networks effectively, and completing the mission under pressure. This realistic assessment ensures that certified professionals are well-equipped for the challenges of cleared red team roles.
Career Opportunities with CRTO
The skills developed through the CRTO certification open doors to specialized roles in cleared environments. By proving the ability to operate responsibly in sensitive Windows environments with industry-standard tools, the certification provides a competitive edge in the cleared job market. FlashGenius, a security professional, underscores its value:
"CRTO tells employers you can run a Windows/AD operation with Cobalt Strike and achieve objectives responsibly. It’s an excellent ‘first real operator’ certification"[4].
The certification’s CREST recognition further enhances its credibility, particularly for professionals working with U.S. government agencies and international defense organizations[4][6]. Zero-Point Security’s status as a CREST-approved training provider and its involvement in co-authoring official Cobalt Strike training materials add significant weight to the certification in the eyes of hiring managers.
For penetration testers looking to transition into red team roles, CRTO serves as a stepping stone by teaching the evasion techniques and stealth-focused methods that set red teaming apart from traditional security assessments[6]. It demonstrates an understanding of not just finding vulnerabilities, but effectively simulating advanced adversaries – an essential distinction in environments where detecting and responding to sophisticated threats is a top priority.
How to Prepare for the CRTO Certification
CRTO Certification Path: Prerequisites, Study Timeline, and Exam Format
Technical Prerequisites for CRTO
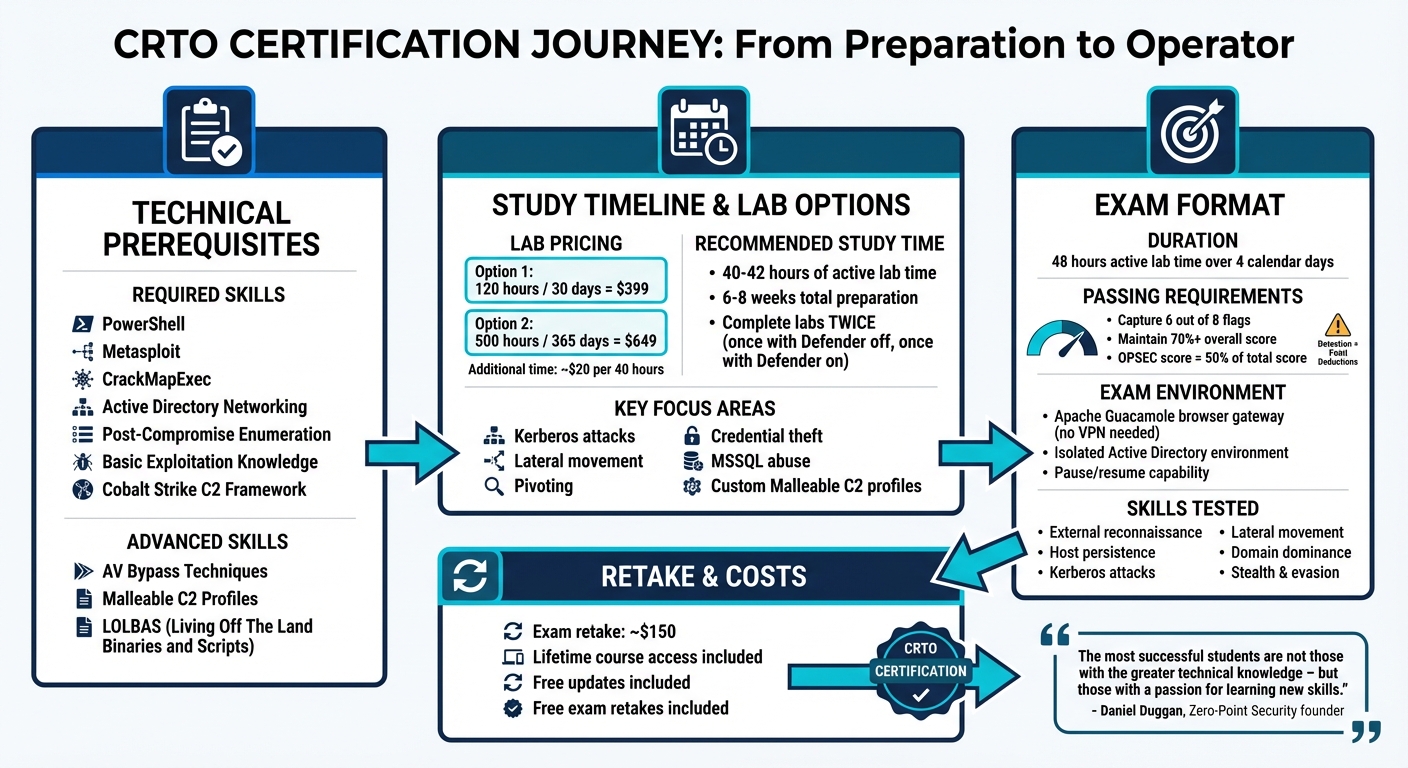
To succeed in the CRTO certification, having a solid technical foundation is crucial. You’ll need hands-on experience with tools like PowerShell, Metasploit, CrackMapExec, and a deep understanding of Active Directory networking. Proficiency in post-compromise enumeration and basic exploitation techniques is also essential [7]. Since the certification heavily focuses on the Cobalt Strike C2 framework, you should be comfortable with command-and-control concepts and lateral movement techniques, such as PsExec, WMI, and WinRM [7][8].
While not mandatory, prior exposure to Active Directory attack scenarios – like those covered in Pentester Academy‘s Attacking and Defending Active Directory course – can give you a head start [5].
John J., a Security Researcher, provides a helpful breakdown of the baseline skills:
"You don’t need to have the OSCP certification to take this course… you should probably have a working knowledge or understanding of: PowerShell, Metasploit, CrackMapExec, Active Directory Networking, Post-Compromise Enumeration, [and] Basic Exploitation/Compromise Knowledge." [7]
For the more advanced portions of the certification, you’ll need to be familiar with AV bypass techniques, Malleable C2 profiles, and Living Off The Land Binaries and Scripts (LOLBAS) [7][5]. Once these technical skills are in place, it’s time to focus on effective study strategies to ensure success.
Study Strategies for Cleared Professionals
The CRTO course offers a flexible pay-and-pause lab model, which means lab time is only consumed when you’re actively working [9]. Pricing options include 120 hours/30 days for $399 or 500 hours/365 days for $649, with additional lab time available at approximately $20 per 40 hours [5][11][13]. This setup is particularly helpful for professionals juggling shift work or classified project deadlines.
A great approach is to complete the labs twice: first with Microsoft Defender disabled to understand the techniques, and then with Defender enabled to practice evasion and operational security. With lifetime access and free updates, you can pace your learning over several months [11]. Most students dedicate around 40 to 42 hours of active lab time to prepare for the exam [12].
Concentrate on key topics like Kerberos attacks, lateral movement, pivoting, credential theft, and MSSQL abuse [14]. Pay special attention to mastering custom Malleable C2 profiles using the c2lint validation tool, which is critical for maintaining stealth during the exam [7]. To save time during the test, create a cheat sheet with commonly used Cobalt Strike and PowerShell commands [11]. For additional support, the Zero-Point Security Discord community is an excellent resource for troubleshooting [11].
Daniel Duggan (RastaMouse), the founder of Zero-Point Security, highlights the importance of mindset:
"The most successful students are not those with the greater technical knowledge – but those with a passion for learning new skills." [13]
For seasoned professionals, the External Route option allows you to take the exam without purchasing the full course [13]. The exam itself spans 48 hours of active lab time over four calendar days, offering flexibility to accommodate work schedules [11][14]. By combining these strategies with your technical expertise, you’ll be well-prepared to tackle the CRTO’s demanding 48-hour exam.
CRTO Exam Format and How to Pass
What to Expect in the CRTO Exam
The CRTO exam is a hands-on practical test where your mission is to infiltrate an Active Directory environment using Cobalt Strike [9]. You’ll have 48 hours of active lab time, which can be paused and resumed within a 4-day calendar window. This setup offers much more flexibility compared to traditional 24-hour penetration testing exams [9].
To succeed, you need to locate and capture 6 out of 8 flags hidden in the environment [9]. The exam is accessed through an Apache Guacamole browser gateway, eliminating the need for VPN software or local tool configuration [9]. The entire environment runs in isolation [9].
This exam isn’t your usual CTF-style challenge. The CRTO puts heavy emphasis on OPSEC and stealth tactics. You’ll be assessed on skills like external reconnaissance, host persistence, Kerberos attacks, lateral movement, and achieving domain dominance – all while keeping your detection footprint minimal [9][8]. The scenarios closely align with the 26 training modules from the course, but you’ll need to adapt and think critically to tackle variations [9].
Let’s break down some preparation strategies to help you excel.
Exam Preparation Tips for Cleared Professionals
When you gain access to a system, establish multiple beacons immediately. As John J., a Security Researcher, suggests:
"Work smarter, not harder. The first thing you should be doing when you gain access to a system is pulling all of the relevant information that will help you maintain persistence" [7].
Choose distinct SMB beacon names to avoid conflicts with tools like PsExec during lateral movement [5].
Keep a detailed runbook, documenting every command and its results. This will help you quickly re-establish lost beacons if needed [7][4]. Plan to spend 2–3 hours per pivot or escalation. If you hit a roadblock, take a break and explore alternate Kerberos paths or lateral movement techniques [4]. Be sure to refresh the SnapLabs dashboard regularly to avoid automatic shutdowns that could interrupt complex attack chains [9].
Make use of Artifact and Resource kits to disguise executables effectively, and leverage the ELK stack to monitor logs [9][5]. If retaking the exam becomes necessary, the cost for additional attempts is around $150 [9].
Using CRTO in Cleared Red Team Roles
Applying CRTO Skills in Cleared Environments
The skills gained through the CRTO certification translate seamlessly to operations within cleared environments. With its emphasis on the Cobalt Strike C2 framework, the course offers hands-on experience with a widely-used commercial tool, often associated with advanced threat groups [11][15][17]. A key takeaway is learning to create custom Malleable C2 profiles that replicate the tactics of real-world adversaries, a skill particularly useful in government agency settings [8][1].
The course’s focus on the assume-breach methodology is especially relevant in classified operations. Instead of prioritizing initial access, you’ll concentrate on post-exploitation tasks like internal reconnaissance, lateral movement through segmented networks, and covert data exfiltration [11]. These techniques are critical for navigating complex environments, such as multi-forest Active Directory setups and networks resembling SIPR/NIPR configurations [8][1].
Mastering the ability to bypass modern security measures – like Microsoft Defender Antivirus, AMSI, and AppLocker – is another essential skill in highly regulated environments [11][16]. The CRTO approach prioritizes maintaining access even against advanced defenses. For instance, the course teaches how to utilize Living Off The Land Binaries (LOLBAS), such as MSBuild, to execute payloads using native Microsoft tools, which often comply with application whitelisting policies. As RedTeaming.org explains:
"Because they are Microsoft owned they allow us to bypass AppLocker since they’re allowed to be executed under the normal ‘allow’ criteria" [5].
When reporting findings, map your techniques to the MITRE ATT&CK framework to provide clear and actionable insights.
Finding Cleared Red Team Jobs with CRTO
The technical skills developed through CRTO can position you as a strong candidate for cleared red team roles. On your resume, make sure to highlight your CRTO certification and expertise in areas like Cobalt Strike, Kerberos attacks, DCSync, and advanced persistence techniques [8][16].
In interviews, emphasize your operational security (OPSEC) and stealth capabilities [16][17]. Cleared employers value operators who understand the principle of "Primum non nocere" (first, do no harm), as testing sensitive systems without causing disruption is a top priority [8][10]. Share specific examples from your CRTO exam, such as deploying multiple beacons for redundancy or using pivot listeners to navigate restricted network segments. These examples can showcase your practical experience and strategic thinking [8][2].
To find opportunities, consider using platforms like Cleared Cyber Security Jobs, which offer tools like job search filters, resume uploads, job alerts, and job fairs. These resources can help you connect with red team roles where your CRTO certification is highly respected, advancing your career in cleared offensive security.
Conclusion
The CRTO certification provides red team professionals with a skills-focused credential that demonstrates their ability to conduct full-scale internal operations within Windows and Active Directory environments. Unlike certifications centered on theoretical knowledge, this one proves you can effectively use Cobalt Strike, simulate Advanced Persistent Threats, and maintain operational security under pressure.
Your next steps depend on where you are in your career. If you’re working on building core skills, dedicate 6–8 weeks to a study plan that emphasizes hands-on practice in a fully licensed Cobalt Strike environment. With lifetime course access, labs that don’t expire, and free exam retakes, the platform minimizes financial risks [4]. As FlashGenius puts it:
"If you want a cert that proves you can actually operate in a Windows enterprise like a real operator – not just memorize facts – ZPS is designed for you" [4].
Once you’ve built a solid foundation, focus on applying these strategies in real-world cleared environments. For those who already hold the CRTO certification, leverage your skills in practical operations. Add achievements like bypassing Defender with custom loaders to your resume to highlight your expertise [4]. To take your career further, consider pursuing RTO II (CRTO II), which focuses on advanced techniques like EDR evasion and custom tooling. This step can prepare you for roles such as senior operator or red team lead [4].
The exam’s 48-hour format allows for a steady, marathon-like approach rather than a rushed experience [3]. Use this time to refine your operator runbook, practice sustained OPSEC, and perfect attack chains from reconnaissance to domain dominance.
FAQs
Is CRTO worth it for cleared red team jobs?
The CRTO certification holds strong value for professionals aiming for cleared red team roles. It showcases hands-on skills in red teaming, particularly with tools like Cobalt Strike, and has earned notable recognition within the cybersecurity field. For those specializing in offensive security and adversary tradecraft, this certification serves as a significant credential for career advancement in cleared environments.
What should I know before starting CRTO?
Before diving into the CRTO certification, it’s important to have a solid grasp of red teaming concepts. This includes understanding adversarial tactics, command and control (C2) frameworks like Cobalt Strike, and Active Directory environments. Having experience with penetration testing techniques – such as lateral movement, persistence, and defense evasion – can also give you an edge.
Since the exam involves a 48-hour hands-on challenge, preparation is key. Spend time reviewing study materials, practicing simulated attack scenarios, and sharpening your skills in offensive security fundamentals. This groundwork will boost your confidence and improve your chances of success.
How do I avoid failing the CRTO exam on OPSEC?
To succeed in the CRTO exam, paying close attention to operational security (OPSEC) is critical. Common missteps can jeopardize your efforts, so staying disciplined in your approach is key. Here are some pitfalls to watch out for:
- Reusing IP addresses: This can make your activities easier to trace and compromise your anonymity.
- Leaving default certificates unchanged: Default settings are a red flag for defenders and can quickly expose your operations.
- Overlooking document metadata: Metadata often contains sensitive details that can reveal your methods or identity.
Additionally, focus on cleaning up your environment thoroughly after activities to avoid leaving behind clues. Avoid falling into predictable patterns, as defenders often look for recurring behaviors. Understanding how blue teams detect red team actions is another essential skill to sharpen.
Finally, studying real-world OPSEC failures can provide valuable lessons. These examples can highlight vulnerabilities you might not have considered and help you refine your tactics effectively.
