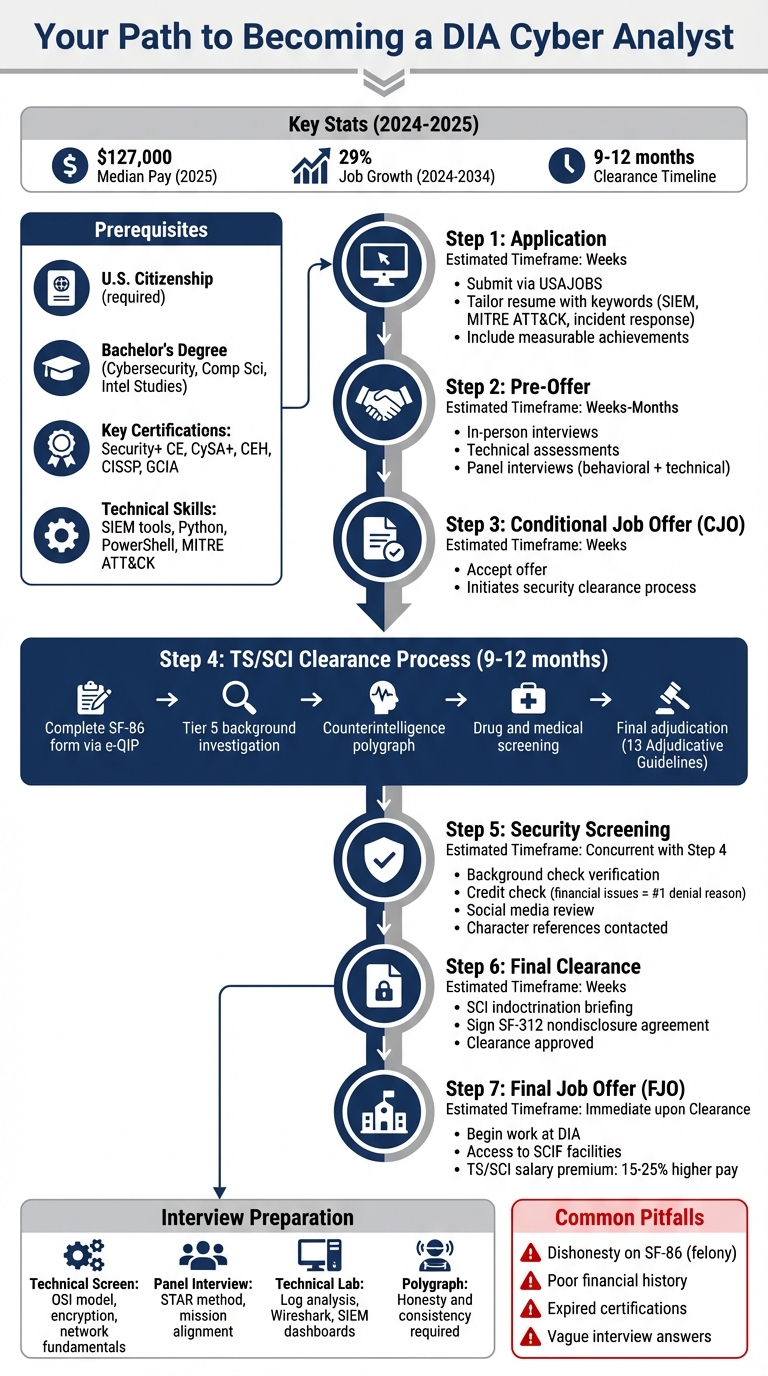
Looking to join the Defense Intelligence Agency (DIA) as a cyber analyst? Here’s what you need to know:
- Role Overview: Cyber analysts protect classified networks, monitor for breaches, and mitigate vulnerabilities using tools like Splunk and CrowdStrike.
- Pay and Demand: Median pay as of 2025 was $127,000, with demand for cybersecurity analysts projected to grow by 29% from 2024 to 2034.
- Security Clearance: A TS/SCI clearance is mandatory, requiring a detailed background check, polygraph, and adjudication process (9–12 months on average).
- Qualifications: A bachelor’s degree (e.g., Cybersecurity, Computer Science) and certifications like Security+ or CISSP are often required.
- Application Process: Apply via USAJOBS with a tailored resume highlighting technical skills and measurable achievements.
- Interview Prep: Expect technical assessments, scenario-based tasks, and behavioral questions. Familiarity with frameworks like MITRE ATT&CK is key.
This guide outlines everything from clearance requirements to interview tips to help you secure a DIA cyber analyst role. Ready to start your journey? Let’s dive into the details.
DIA Cyber Analyst Application Process Timeline and Requirements
What Cyber Analysts Do at DIA
Main Job Duties
Cyber analysts at the Defense Intelligence Agency (DIA) play a critical role in protecting classified networks. They monitor network traffic using SIEM tools like Splunk, IBM QRadar, and Elastic SIEM to detect unusual activity. When anomalies arise, they investigate and prepare detailed incident response reports to document their findings and actions taken [1]. Their responsibilities also include installing and managing security tools such as firewalls and encryption software, addressing vulnerabilities before they can be exploited, and conducting regular risk assessments and penetration tests to uncover potential weaknesses in the system [1]. These efforts are vital to securing national intelligence data.
Another key aspect of their work involves transforming technical intelligence into reports that are useful for both technical teams and decision-makers [11]. To do this, they rely on threat intelligence platforms like Recorded Future, which processes billions of data points daily. Using frameworks like MITRE ATT&CK, CVE data, and the Diamond Model, analysts contextualize threats and recommend mitigation strategies [5][11]. Additionally, they develop and test disaster recovery plans to ensure the agency can bounce back after a cyberattack [10].
Work Environment at DIA
The work environment for cyber analysts at the DIA goes beyond technical tasks, emphasizing teamwork and ongoing learning. Analysts collaborate with intelligence professionals, subject matter experts, and external partners to ensure the accuracy and reliability of intelligence products [11]. They often work in blue teams, analyzing logs to distinguish between normal network activity and potential threats [10].
The DIA is also embracing advanced technology to strengthen its cybersecurity efforts. The agency is adopting an "AI-first" approach, using artificial intelligence tools to enhance threat analysis and ensure dependable cybersecurity outcomes [6]. Analysts have access to cutting-edge tools across different security domains and classification levels. These include endpoint detection and response platforms like CrowdStrike Falcon and SentinelOne, network traffic analysis tools like Wireshark and Zeek, and automation solutions such as Palo Alto Cortex XSOAR [7].
Next, we’ll explore the security clearance requirements needed for these roles.
sbb-itb-bf7aa6b
Security Clearance Requirements
What TS/SCI Clearance Means
TS/SCI, or Top Secret/Sensitive Compartmented Information, combines a Top Secret clearance with additional access authorization to highly compartmented intelligence, strictly restricted to those with a "need-to-know" basis [12][13][14]. This clearance is a must for cyber analyst roles at the Defense Intelligence Agency (DIA), as these roles involve working with intelligence that, if leaked, could cause "exceptionally grave damage" to national security [12][13]. Since the DIA is part of the 18-agency Intelligence Community, it handles classified sources, methods, and analysis processes that demand this level of security. Most of this work occurs in a Sensitive Compartmented Information Facility (SCIF), where electronic devices are strictly forbidden [12][14].
"SCI (Sensitive Compartmented Information) is not a clearance level – it is an access authorization applied on top of a Top Secret clearance." – ClearedJobs.Net [12]
U.S. citizenship is a non-negotiable requirement for TS/SCI roles at the DIA [14]. While the Department of Defense might occasionally allow non-citizens access to Secret-level information under rare circumstances, TS/SCI positions require full U.S. citizenship [14]. Additionally, individuals holding TS/SCI clearance often earn 15–25% more than their counterparts without clearance [12][13].
Understanding these requirements is crucial before diving into the clearance process.
How the Clearance Process Works
The clearance process kicks off once you accept a conditional job offer from the DIA. On average, the process takes between 9 to 12 months to complete [4][12][13].
The first step is completing the SF-86 form through the e-QIP system. This detailed questionnaire covers the past decade of your life, including addresses, employment, education, foreign contacts, and financial history [14][16]. Having all your documentation ready beforehand can help speed things along [14][16].
"Your character, conduct and discretion must be above reproach and you must have unquestioned loyalty to the United States." – Defense Intelligence Agency [2]
Next comes the Tier 5 background investigation. Investigators will verify your character and history by reaching out to friends, neighbors, former colleagues, and employers [13][14]. They may also review publicly available social media, following SEAD 5 guidelines [15]. Financial issues are the most common cause of clearance denials, so keeping your credit report clean and ensuring all taxes are filed and paid is critical [15][16].
A counterintelligence-scope polygraph examination is also required. This test focuses on topics like espionage, sabotage, terrorism, and unauthorized disclosures of classified information [14]. To perform well during the polygraph, stick to your normal routine. As Teresa Tennyson, a journalist and retired Army officer, advises, "The best way to pass any lie detector test is to not lie" [14].
After passing drug and medical screenings, your case goes to final adjudication. An adjudicator reviews all findings against the 13 Adjudicative Guidelines outlined in SEAD 4 to determine your eligibility [15]. Once approved, you’ll attend an indoctrination briefing for SCI access and sign a nondisclosure agreement (SF-312) [12]. It’s important to note that dishonesty or omission of information on the SF-86 is a felony and a common reason for clearance disqualification [14][15]. This thorough process ensures that only those who meet the highest standards of trustworthiness are granted access to the nation’s most sensitive intelligence.
Once your clearance is finalized, the next step is preparing your application and interview for a DIA cyber analyst position.
Required Qualifications, Skills, and Certifications
Education and Experience Requirements
For roles as a DIA cyber analyst, a bachelor’s degree in fields like Cybersecurity, Computer Science, Intelligence Studies, or Technology is typically required [8][9]. However, the agency also values non-traditional career paths and unique experiences [17]. Highlighting how your background – whether conventional or unconventional – equips you to tackle advanced threats can make your application stand out. According to the U.S. Bureau of Labor Statistics, the demand for cybersecurity professionals is anticipated to grow by 33% through 2030 [17].
Besides academic qualifications, technical expertise plays a critical role in distinguishing candidates.
Technical Skills You Need
While a degree is important, technical know-how is what truly sets candidates apart. DIA cyber analysts must excel in several key areas, including coding, intrusion detection and prevention systems, understanding attack methods, security operations, and incident response technologies [17]. Building hands-on experience with tools like Wireshark, Splunk, and scripting languages such as Python and PowerShell is highly recommended [19][21].
"Cyber threat intelligence analysts play an indispensable role in helping organizations understand their threat landscape and protect themselves from risk." – Flashpoint [17]
To succeed, you’ll need to master strategic, operational, and tactical skills to analyze threat actor tactics, techniques, and procedures (TTPs) [17]. Given the constantly shifting nature of cyber threats, continual skill development is a must.
Top Certifications for DIA Roles
DIA cyber analysts must comply with the Department of Defense Directive (DoDD) 8140, which outlines mandatory certifications for individuals with privileged access to DoD information systems [18][20]. These certifications are categorized by job functions, including Information Assurance Technical (IAT), Information Assurance Management (IAM), and Cybersecurity Service Provider (CSSP) [18][20].
| Certification | Issuing Body | Focus Areas | Experience Level | DIA/DoD Relevance |
|---|---|---|---|---|
| Security+ CE | CompTIA | Foundational security, troubleshooting | Entry/Mid | Standard for IAT Level II roles |
| CySA+ | CompTIA | Threat hunting, incident response | Mid | Approved for CSSP Analyst & Incident Responder |
| CEH | EC-Council | Offensive tactics, vulnerability scanning | Mid | Core requirement for CSSP Analyst roles |
| CISSP | ISC2 | Security engineering, risk management | Senior | Required for IAM Level III (Management) |
| GCIA | GIAC | Intrusion analysis, network traffic | Intermediate | Specialized for CSSP Analyst roles |
If you’re just starting, focus on earning the CompTIA Security+ certification, as it’s often required for IAT Level II roles [20]. For analyst-specific positions, certifications like CEH, CySA+, or GCIA – under the CSSP Analyst category – are highly relevant [18][20]. Keep in mind, certifications must remain active. Expired certifications can disqualify candidates from working on cleared federal projects. For instance, CompTIA certifications like Security+ need renewal every three years [20].
"Certifications aren’t just ‘nice to have’ – they’re often mandatory. Cyber threats are growing, and hiring someone without the right skills and credentials can delay projects or even put national security at risk." – CCS Global Tech [20]
How to Apply for DIA Cyber Analyst Jobs
Applying Through USAJOBS
To land a DIA cyber analyst position, start with USAJOBS, the main platform for federal job applications. Create a detailed profile and craft a resume tailored to the job posting. Use specific keywords like "SIEM," "MITRE ATT&CK," and "incident response" to ensure your resume passes Applicant Tracking Systems (ATS) [23].
Focus on showcasing measurable accomplishments instead of listing generic responsibilities. For instance, replace "responsible for incident response" with specifics like "reduced incident response times by 20%" or "mitigated over 200 phishing attempts monthly" [23]. Highlight expertise in government frameworks such as NIST 800-53 and DISA STIGs. Use clean, professional formatting – fonts like Calibri or Arial – and save your resume as a PDF to ensure it looks polished [23].
Once your application is submitted, the hiring process follows several structured steps.
Security Screening and Hiring Steps
After receiving a Conditional Job Offer (CJO), you’ll undergo a multi-stage security screening process, including a background check, polygraph, drug testing, and medical exams. These steps are in place to ensure candidates meet strict qualifications for handling sensitive national security information.
| Hiring Stage | Key Components |
|---|---|
| Application | Submit via USAJOBS, tailor your resume, and pass the initial screening. |
| Pre-Offer | Participate in in-person interviews and technical assessments. |
| Conditional Offer | Accept the CJO, which initiates the security clearance process. |
| Security Screening | Undergo a background investigation, TS/SCI adjudication, and polygraph. |
| Medical & Suitability | Complete drug testing, medical exams, and credit checks. |
| Final Decision | Receive either a Final Job Offer (FJO) or a negative determination. |
Be prepared for potential delays, especially during the adjudication phase. Some candidates report waiting five to six months after the initial investigation for SCI access [3]. As one applicant, Wombat_in_Combat, shared:
"The security office does not communicate where you are in the process with the hiring staff or managers, their current workload, or timelines" [3].
If you encounter delays, reach out to DIA Personnel Security (PERSEC) or the ODNI Scattered Castles hotline to check your clearance status [3].
Using Cleared Cyber Security Jobs to Find Opportunities
In addition to USAJOBS, consider using platforms like Cleared Cyber Security Jobs to simplify your search for DIA roles. This site offers filters tailored to clearance levels such as "TS/SCI + CI Poly," which are essential for DIA cyber analyst positions [22]. You can set up job alerts to receive notifications about relevant openings and upload your resume to make it easily accessible to recruiters [24]. Since the platform focuses solely on positions requiring security clearances, it eliminates irrelevant listings and connects you directly with employers hiring for these specialized roles.
Next, we’ll dive into how to prepare for the DIA interview process.
Preparing for DIA Interviews
What to Expect in Interviews
Once you’ve made it through the application process, it’s time to prepare for the DIA interviews. These interviews are designed to evaluate both your technical expertise and your ability to communicate effectively. You’ll face questions on network fundamentals – think firewall types, segmentation strategies, and practical applications of the OSI model. Be ready to clearly explain the steps of the incident response lifecycle, covering everything from preparation and detection to containment, eradication, recovery, and post-incident review.
You’ll also encounter questions on the MITRE ATT&CK framework and need to distinguish between tactical and strategic threat intelligence. Familiarity with tools like SIEM platforms (e.g., Splunk or Microsoft Sentinel), EDR solutions (like CrowdStrike or Carbon Black), and network analysis tools (such as Wireshark or Snort) is essential. Additionally, you should be able to explain encryption methods, hashing, and their appropriate use cases.
Real-world examples are key. Grace Abrams, a hiring manager, highlights the importance of layered defense strategies:
"A secure network architecture consists of several key components that work together… I like to think of it as a multi-layered approach that ensures a robust defense against potential threats."
Prepare specific examples of times you’ve identified vulnerabilities, reduced incident response times, or simplified technical issues for non-technical leadership. If you’re unsure of an answer during the interview, admit it honestly and explain how you’d research the solution instead of making guesses.
You may also face tabletop exercises where you’ll walk through hypothetical scenarios like a DDoS attack, phishing campaign, or zero-day exploit. These exercises test your ability to prioritize actions, contain threats without disrupting operations, and conduct root cause analysis. A solid understanding of the CIA triad – confidentiality, integrity, and availability – is crucial, as this framework underpins information security decisions across the intelligence community.
Interview Stages and Preparation Tips
DIA interviews are structured to assess different competencies at each stage. Here’s a breakdown of what to expect:
| Interview Stage | Focus | Preparation Tip | Common Pitfall |
|---|---|---|---|
| Technical Screen | Core knowledge (OSI model, encryption, tools) | Review basics like common port numbers and key definitions. | Giving vague or overly "textbook" answers without context. |
| Panel Interview | Behavioral fit and communication | Use the STAR method (Situation, Task, Action, Result) to frame responses. | Failing to show how your work aligns with the agency’s mission. |
| Technical Lab/Scenario | Hands-on skills (log analysis, packet capture) | Practice with tools like Wireshark and SIEM dashboards. Document your process clearly. | Rushing through tasks without showing your thought process. |
| Polygraph Exam | Integrity and security clearance | Be honest and consistent throughout the exam. | Trying to "outsmart" the exam or being evasive. |
During the technical screen, you’ll need to explain foundational concepts like network protocols, the differences between IDS and IPS, and attack vectors such as Man-in-the-Middle, Cross-Site Scripting, and brute-force attacks. Focus on explaining these ideas clearly, not just reciting definitions.
The panel interview will dive into behavioral scenarios, emphasizing how your experience supports the DIA’s mission. Practice discussing situations where you communicated technical issues to leadership, resolved team conflicts, or handled sensitive information under pressure. The ability to translate technical jargon into plain language for non-technical stakeholders is highly valued. Tailor your responses to reflect the agency’s role in national security.
In the technical lab or scenario, you’ll be expected to analyze logs, investigate network traffic, or respond to a simulated incident. Take your time documenting your methodology as you work – interviewers want to see how you approach problems, not just whether you arrive at the correct answer.
Finally, the polygraph exam is all about integrity. Be truthful and consistent, as this stage is designed to confirm your suitability for handling classified information, not to trip you up.
Final Thoughts
Achieving a role as a cleared cyber analyst at the DIA requires careful planning and dedication. From meeting stringent clearance standards to honing technical skills, every step plays a crucial part in your preparation.
Obtaining a TS/SCI clearance is a critical component. This clearance mandates a spotless background, which includes maintaining clean credit records and demonstrating financial responsibility. The process itself is thorough, involving polygraph exams, drug tests, and in-depth background checks. Be ready for a lengthy and meticulous vetting process that can take several months to complete.
On the technical side, earning certifications like CompTIA Security+, GIAC GSEC, or CISSP can validate your expertise and help fill any gaps in experience. While 61% of cybersecurity analysts hold a bachelor’s degree [1], certifications ensure your skills remain sharp and up to date. Additionally, proficiency in programming languages such as Python, JavaScript, or C/C++ can set you apart in technical roles [1].
The application process and interviews are equally demanding. Expect multiple evaluation rounds designed to test your technical knowledge and communication skills. Clear, confident communication is just as important as technical expertise during these stages.
Platforms like Cleared Cyber Security Jobs simplify the job search for professionals with security clearances. Instead of combing through generic job boards, you can focus on positions specifically requiring clearances, such as those at the DIA. This platform offers free tools like job alerts, resume uploads, and career resources tailored to the cleared community. By using these resources, you can streamline your journey from obtaining certifications to landing your dream role at the DIA.
FAQs
Can I apply if I don’t already have TS/SCI?
To qualify for a cleared cyber analyst position at the DIA, you must already hold a TS/SCI clearance. This clearance is a fundamental requirement for these roles and is non-negotiable.
What issues most often delay or derail TS/SCI approval?
The delays in obtaining TS/SCI approval often arise from the intricate nature of the adjudication process. Common issues include cases with past drug use, financial complications, or incomplete and inconsistent submissions. Additionally, external events, such as public security incidents or high-profile cases, can lead to heightened scrutiny and create backlogs. When deeper investigations or additional clarifications are required, the process can extend to a year or even longer.
How can I build DIA-relevant experience without prior intel work?
To prepare for a role at the Defense Intelligence Agency (DIA), focus on building transferable cybersecurity skills and earning certifications that are highly regarded in the intelligence community. Key areas to prioritize include collection management, tradecraft, and fundamental cybersecurity principles like auditing and analysis.
By pursuing certifications and training relevant to the field, you not only demonstrate your commitment but also make up for any lack of direct intelligence experience. Developing expertise in defense-oriented skills is a critical step toward being ready for DIA opportunities.
