Cleared penetration testers specialize in authorized hacking of classified government systems to identify vulnerabilities. This career offers high demand, competitive salaries, and opportunities with top defense contractors, but requires U.S. citizenship, security clearance, and advanced technical skills. Here’s what you need to know:
- Salaries: Entry-level roles start at $85,000–$110,000, with senior positions exceeding $150,000.
- Security Clearance: Essential for accessing classified systems; requires sponsorship, background checks, and adherence to Trusted Workforce 2.0 guidelines.
- Technical Skills: Proficiency in networking, Linux, Active Directory, scripting (Python, PowerShell), and tools like Nmap, Burp Suite, and Metasploit.
- Certifications: Start with CEH or Security+, then advance with OSCP or GPEN for hands-on expertise.
- Career Growth: Progression includes roles from Junior Tester to Red Team Lead, with salaries up to $250,000 for leadership positions.
- Networking: Engage with industry professionals at events like DEF CON or through cleared job platforms.
This field requires both technical expertise and the ability to communicate findings effectively. With cybersecurity jobs growing 33–35% through 2033, cleared penetration testers are well-positioned for success.
Prerequisites for a Career in Cleared Penetration Testing
Security Clearance and Citizenship Requirements
If you’re aiming for a career in cleared penetration testing, U.S. citizenship is non-negotiable. With fewer than 1.3% of U.S. citizens holding a security clearance [5], this career path is highly exclusive. However, you can’t apply for a clearance on your own. Instead, a federal agency or an authorized defense contractor must sponsor you after offering a conditional job position [2].
Most roles in penetration testing require either a Secret (Tier 3) or Top Secret (Tier 5) clearance. Processing times vary: Secret clearances typically take 60 to 150 days, while Top Secret clearances can take 120 to 240 days [2]. If the role involves Sensitive Compartmented Information (SCI) and a polygraph, be prepared for a longer wait – 180 to 365+ days due to appointment backlogs [2]. On the bright side, interim Secret clearances may be issued in as little as 10 to 30 days, allowing you to start work sooner [2].
The Defense Counterintelligence and Security Agency (DCSA) handles over 95% of federal background investigations [2], evaluating candidates based on 13 adjudicative guidelines. These include factors like financial stability, foreign contacts, drug use (marijuana remains federally illegal), and personal conduct. To prepare, gather a detailed 10-year history of your residences, jobs, education, and foreign travel before you receive your eApp link. It’s also a good idea to check your credit reports and resolve any delinquencies, as financial issues are the leading reason for clearance denials [2].
With the introduction of Trusted Workforce 2.0 (TW 2.0), the clearance process has shifted to a “clear once, trusted everywhere” model, streamlining reciprocity between agencies [2]. Continuous Vetting (CV) now replaces periodic reinvestigations, offering real-time monitoring of criminal records, credit activity, and foreign travel [2]. If you experience a major life event – like an arrest, significant debt, or new foreign contacts – report it to your Facility Security Officer (FSO) immediately, as CV will flag these changes.
This rigorous clearance process isn’t just about meeting technical qualifications; it’s a test of your integrity and reliability. Once you’ve cleared this hurdle, it’s time to focus on building the technical expertise that defines success in this field.
Building Technical Foundations
A strong technical foundation is essential for cleared penetration testing. Many professionals begin their careers in roles like helpdesk technician, system administrator, or network administrator [1]. These positions help you understand how systems operate – knowledge you’ll need before you learn how to exploit them. From there, transitioning into security-focused roles such as SOC Analyst, Junior Security Analyst, or Vulnerability Management Specialist is a logical next step [3][1].
One certification you can’t skip is CompTIA Security+. It’s a basic requirement for many government-related positions and helps you pass automated HR filters [3][5]. Beyond certifications, hands-on experience is critical. Key areas to focus on include:
- Networking fundamentals: Understand TCP/IP, DNS, and HTTP.
- Linux proficiency: Around 90% of security tools are Linux-based [3].
- Windows/Active Directory environments: Learn about Kerberos, LDAP, and NTLM. Experts note that Active Directory exploitation is in high demand and offers some of the best salaries in enterprise security [3].
If you see job postings mentioning "ability to obtain a security clearance" or "ability to maintain a security clearance," these roles often offer sponsorship opportunities [5]. Starting in an unclassified technical role with defense contractors like Booz Allen Hamilton, Leidos, or Northrop Grumman is a great way to get your foot in the door. Once you secure a clearance, you could see a 10% to 20% salary bump [4], with average cleared professionals earning $119,131 by 2025 [5].
To stand out, consider setting up a home lab using VirtualBox or VMware to simulate environments like Domain Controllers and Windows Server [3]. Share your expertise by publishing walkthroughs on platforms like Medium or LinkedIn, or participate in bug bounty programs through HackerOne. Even finding a low-severity vulnerability allows you to list "Freelance Security Researcher" on your resume [3].
These technical skills and proactive efforts are the building blocks of a strong career in cleared offensive security.
sbb-itb-bf7aa6b
Core Skills and Tools for Cleared Penetration Testers
Technical Skills for Offensive Security
Once you’ve got a solid technical foundation, it’s time to dive into specialized offensive security skills. One of the first steps is mastering vulnerability assessment – spotting weaknesses in systems. But identifying flaws isn’t enough; manual exploitation is what proves the real-world impact. While automated scanners can help flag potential issues, the testers who stand out are those who can creatively chain smaller vulnerabilities into a major business risk [3].
Scripting and automation are non-negotiable skills. Knowing languages like Python, Bash, and PowerShell lets you tweak exploits, automate repetitive tasks, and bypass specific security controls [3][1]. On top of that, Open Source Intelligence (OSINT) is key for reconnaissance. Before ever touching a target system, you’ll be gathering useful data from publicly available sources [3][1].
In today’s penetration testing landscape, expertise in privilege escalation on both Linux and Windows systems is a must, along with a strong grasp of Active Directory attack methods like Kerberoasting and NTLM hashing. Web application security, particularly the vulnerabilities outlined in the OWASP Top 10, is another critical area to focus on [3][7][1]. Active Directory exploitation, in particular, is highly relevant in cleared environments, where Windows domains are often the focal point of breaches [3]. To sharpen these skills, consider building a home lab with VMware or VirtualBox, where you can simulate Domain Controllers and practice on victim machines [3][1]. Platforms like TryHackMe and Hack The Box are excellent resources for guided and advanced simulations [3][7].
These technical skills come to life when paired with the right tools, which we’ll cover next.
Key Tools for Penetration Testing
The tools you use can make or break your effectiveness as a penetration tester. One of the first tools you’ll need is Nmap, the go-to for network discovery and service identification. It’s essential for mapping out what’s running on a target network. For web application testing, Burp Suite Professional is indispensable. This tool intercepts and manipulates web traffic, helping you uncover vulnerabilities like SQL injection and cross-site scripting (XSS) [3][1]. For beginners, OWASP ZAP offers a great open-source alternative.
As you move deeper into penetration testing, tools like Metasploit, Cobalt Strike, Empire, and Sliver become essential for moving from initial access to post-exploitation. Utilities such as Mimikatz, BloodHound, and PowerSploit are invaluable for credential harvesting and lateral movement [1]. When it comes to password auditing, both John the Ripper and Hashcat are industry favorites for testing credential strength using brute-force and dictionary attacks, often with GPU acceleration.
It’s important to verify the results from these tools. Automated scanners can miss subtle vulnerabilities or flag false positives, so manual inspection is always necessary. Beyond technical expertise, your ability to work well with others and communicate findings effectively is what sets you apart in this field.
Soft Skills for Cleared Professionals
While technical skills and tools are crucial, soft skills often determine how much of an impact you’ll have. Translating technical findings into actionable insights requires diplomacy and clear communication. This is especially important when presenting critical vulnerabilities to stakeholders [8][9]. Practicing formal reporting during Capture The Flag challenges can help. Include both an "Executive Summary" for decision-makers and detailed "Technical Findings" for technical teams [3].
For example, using professional terms like "identified a remote code execution vulnerability" instead of informal language like "pwned" helps maintain credibility in cleared environments [3]. Empathy is another essential skill. Developers often face tight deadlines and resource constraints, so understanding their challenges can help you prioritize vulnerabilities that need immediate attention [10][11].
Finally, persistence and curiosity are what drive top-tier testers. Exploring unconventional scenarios often reveals edge-case vulnerabilities that automated tools might miss [9][10]. With a global cybersecurity talent shortage nearing 4 million professionals [3], problem solvers who understand both system architecture and business risks are becoming increasingly valuable [3].
Top Certifications for Cleared Penetration Testers
Recommended Certifications
Certifications play a dual role in the world of cleared offensive security: they help you meet HR screening requirements and showcase your technical skills to hiring managers. For those aiming for government or defense contractor roles, it’s essential to obtain certifications that align with DoD 8140/8570.01-M baseline requirements while proving your ability to perform hands-on exploitation tasks. These credentials are critical for navigating HR filters and demonstrating expertise in security-cleared environments.
CEH (Certified Ethical Hacker) and GPEN (GIAC Penetration Tester) are widely recognized for meeting DoD baseline requirements for Information Assurance Technical (IAT) roles [13]. CEH, in particular, is designed to satisfy mandatory HR criteria. The CEH exam consists of 125 multiple-choice questions over four hours, with a pass rate reported at 85–90% [17]. The exam voucher costs about $1,199, while official training ranges from $850 to $3,600 [15].
For those looking to prove technical mastery, the OSCP (Offensive Security Certified Professional) stands out [17]. Unlike CEH’s multiple-choice format, OSCP requires candidates to compromise live machines in a 24-hour hands-on exam, followed by a detailed penetration test report. The pass rate for first attempts is around 30–40%, and preparation often demands 300–600 hours of hands-on practice [12]. The certification is available as a 90-day bundle, including one exam attempt, for roughly $1,649. Although OSCP isn’t specifically mapped to the DoD framework, it frequently appears in agency-specific procurement solicitations. As ITRise Editorial aptly noted:
CEH gets your resume past HR. OSCP proves to technical managers that you can actually hack.
For compliance-focused certifications, LPT (Licensed Penetration Tester) by EC-Council is tailored to meet federal requirements, emphasizing classified assessment techniques used by defense agencies [18]. Meanwhile, CISSP (Certified Information Systems Security Professional) is often required for senior cleared positions. While CISSP focuses more on governance and risk management than offensive skills, it remains a key credential for leadership roles. The CISSP exam costs $749, with an additional $125 annual fee, and requires five years of experience in at least two security domains [21].
These certifications not only add credibility but also lead to higher salaries. Certified penetration testers typically earn 15–25% more than their non-certified peers [12]. For example, OSCP holders in the U.S. earn an average of $120,000 annually, with some roles offering up to $168,000 [14]. Offensive Security recently introduced OSCP+, requiring renewal every three years to ensure practitioners stay updated on evolving attack methods. Additionally, new certifications like OSAI+ (OffSec AI Red Teamer) are emerging to address offensive operations involving AI [6].
Certification Comparison
The table below outlines key details of these certifications for easy reference:
| Certification | Cost | Format | DoD 8570/8140 | Prerequisites | Renewal |
|---|---|---|---|---|---|
| CEH | ~$1,199 exam + $850–$3,600 training [15] | 4-hour multiple-choice (125 questions) [17] | Yes (IAT II, IAM I) | 2 years info sec experience or official training [21] | 120 ECE credits every 3 years [13] |
| OSCP | ~$1,649–$1,749 (90-day bundle + exam) [12] | 24-hour hands-on lab + report [17] | Often accepted as equivalent [13] | None (TCP/IP and Linux knowledge recommended [21]) | 3 years (for OSCP+) [16] |
| GPEN | ~$949–$999 exam; ~$7,500 with SANS training [15] | 3-hour proctored (open book) [20] | Yes [13] | None (SANS SEC560 training recommended [20]) | 36 CPE credits every 4 years [13] |
| CISSP | ~$749 exam + $125 annual fee [19] | CAT multiple-choice (3 hours) [19] | Yes (IAT III, IAM II/III) [19] | 5 years of work experience in 2+ domains [21] | 120 CPEs every 3 years [19] |
| PNPT | ~$400 (training + exam) [15] | 5-day practical + briefing [15] | No | None | No renewal required |
For cleared roles, starting with CEH or GPEN is recommended to meet mandatory DoD compliance. Once you’ve secured an entry-level position, pursuing OSCP can validate your hands-on skills and open doors to senior red team roles. Many government contractors and consulting firms also offer full tuition reimbursement for high-cost certifications like OSCP and GPEN, making these investments more accessible. Choosing the right certification path is a key step toward advancing in cleared offensive security.
Career Progression in Cleared Penetration Testing
Penetration Tester Career Path: From Entry-Level to Red Team Lead
From Junior Pentester to Red Team Lead
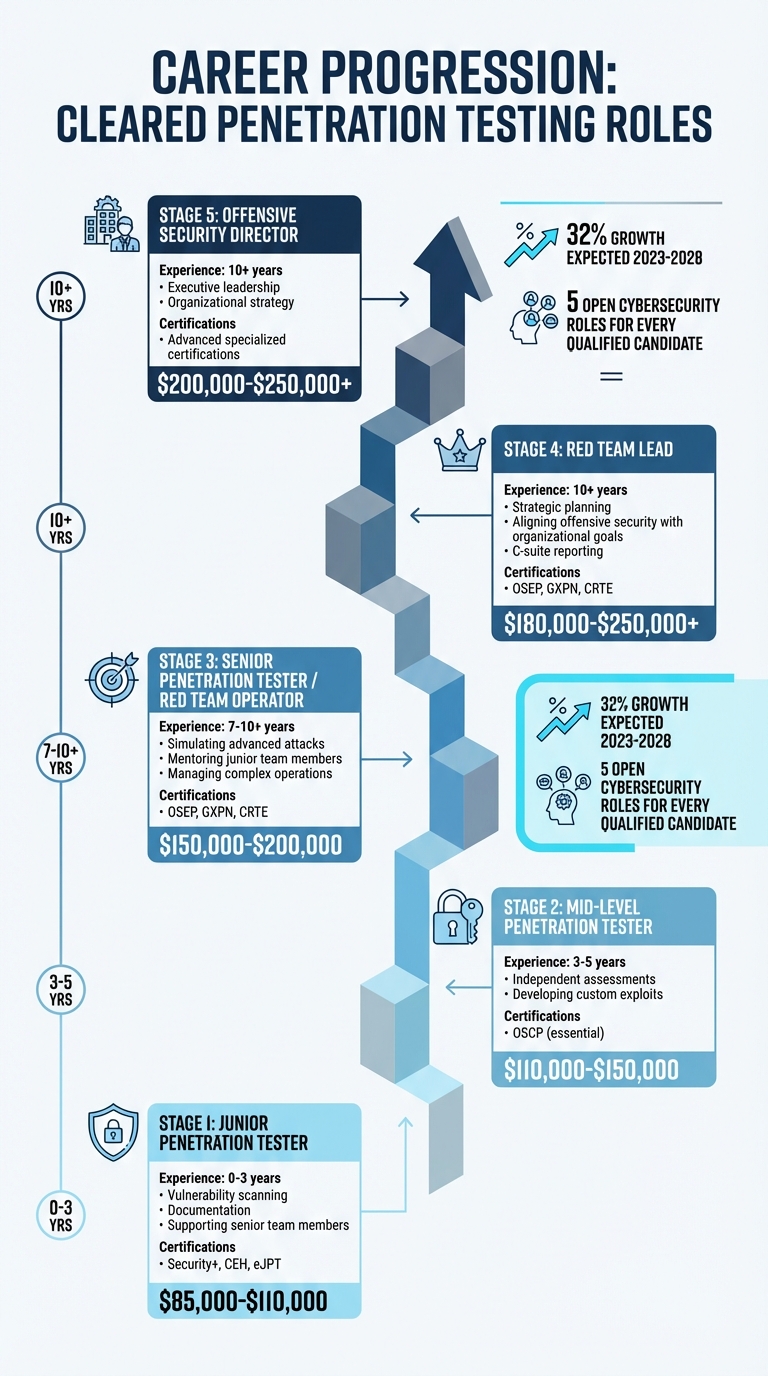
Cleared offensive security careers typically follow a structured path, spanning five stages over a decade or more[1]. It all starts with Junior Penetration Testers, who have 0–3 years of experience. At this stage, professionals focus on tasks like vulnerability scanning, documentation, and supporting senior team members. Foundational certifications such as Security+, CEH, or eJPT are often key for entry into the field.
After gaining 3–5 years of experience, individuals move up to the role of Mid-Level Penetration Tester. These professionals handle independent assessments and work on developing custom exploits. Certifications like the OSCP become essential at this level, and salaries typically range from $110,000 to $150,000[1].
The next step is becoming a Senior Penetration Tester or Red Team Operator, a role that usually requires 7–10+ years of experience. Responsibilities include simulating advanced attacks, mentoring junior team members, and managing more complex operations. Salaries for senior roles range from $150,000 to $200,000, and certifications such as OSEP, GXPN, or CRTE often set top performers apart[1].
At the leadership level, positions like Red Team Lead or Offensive Security Director are typically filled by those with over 10 years of experience. These leaders handle strategic planning, align offensive security efforts with organizational goals, and report directly to C-suite executives. Specialized certifications like OSEP, GXPN, or CRTE remain important, and salaries range from $180,000 to over $250,000[1]. David Kennedy, Founder of TrustedSec, sums up the mindset required for this progression:
Red Teaming is about thinking like the adversary and understanding how they operate. It’s not just about finding vulnerabilities – it’s about exploiting them in ways that mimic real-world attackers to demonstrate actual business impact[1].
The demand for Red Team expertise is expected to grow by 32% between 2023 and 2028[1]. As you move through these stages, using specialized job platforms can help you identify and seize the right opportunities.
Using Cleared Cyber Security Jobs
As you navigate your career in cleared offensive security, specialized job platforms can simplify the process of finding relevant roles. One such platform is Cleared Cyber Security Jobs, which connects U.S. citizens with active security clearances to employers in government and defense contracting. Unlike general job boards, this veteran-founded platform focuses exclusively on security-cleared professionals, eliminating irrelevant postings and saving time.
The platform offers job search filters based on clearance levels (Secret, Top Secret, TS/SCI), making it easier to find roles that match your qualifications. Job seekers can upload their resumes to a searchable database, allowing hiring managers to reach out directly. Alerts for new job postings ensure you don’t miss time-sensitive opportunities, while virtual and in-person job fairs provide a chance to connect with employers without the usual application hurdles.
Beyond job listings, the platform offers resources to support your career growth. These include guidance on maintaining clearances, understanding polygraph requirements, and navigating agency-specific language. For those advancing from junior to senior roles, the site provides insights into salary benchmarks and certification expectations, helping you track your progress and stay competitive in the market.
How to Secure Cleared Penetration Testing Jobs
Resume Building for Cleared Roles
When applying for cleared penetration testing jobs, make sure your resume immediately highlights your security clearance. Include the clearance level (e.g., Secret, Top Secret, or TS/SCI) prominently in your resume header or summary. This instantly lets recruiters know you’re ready to work without additional vetting.
Dedicate a section to your technical skills, listing tools like Metasploit and Burp Suite, along with programming languages such as Python. Certifications like OSCP, CEH, or Security+ should be front and center. If you’re working toward a certification, include the expected completion date. Use the STAR method (Situation, Task, Action, Result) to describe your achievements, and back them up with measurable results. For example, mention how you reduced security risks by 35% through proactive monitoring.
Be mindful of operational security. While you can list your clearance level, avoid including classified details like project names, office locations, or budget specifics. If your clearance is inactive but was held within the last two years, note it as "Inactive, Eligible for Reinstatement" to show you’re still a viable candidate.
Bill Branstetter of 9th Way Insignia offers this advice:
Keep subjective self-descriptions out of your summary section. I’m looking at you, Results-Oriented Team Players.
Finally, tailor your resume for each job by integrating keywords from the job description. Keep it concise – one to two pages with a clean format works best. Once your resume is polished, expand your reach by connecting with others in the industry.
Networking in the Cleared Community
A strong resume is only part of the equation. Networking is critical to finding opportunities in the cleared community. Engaging with current penetration testers at your target companies can open doors through employee referrals, which often carry more weight than standard applications. Bryan Acton, Military & Veterans Program Leader at Peraton, explains:
Most people in talent acquisition would love to have the time to call all 3,000 people a week… but it’s just not possible. Reach out to your peer network.
Attending cybersecurity conferences like BSides, Black Hat, or DEF CON can provide valuable connections. Don’t overlook the informal "hallway" networking that happens between sessions – it’s where many meaningful conversations take place. Volunteering at these events or for local non-profits can also help you meet industry professionals while boosting your portfolio.
After meeting someone, follow up with a short thank-you email or LinkedIn message. If you’ve applied for a role, a timely follow-up with the recruiter can make a difference. Stay active on cleared job boards by logging in regularly to improve your visibility in employer searches. Joining local OWASP chapters or online security communities can also connect you with mentors and hidden job opportunities.
Gaining Hands-On Experience
Practical experience is essential to complement your resume and network. Building a home lab is a great way to sharpen your skills. Use tools like VirtualBox or VMware to run vulnerable machines such as Metasploitable or Windows Evaluation ISOs. Pair these with Kali Linux or Parrot OS to practice penetration testing. Since many organizations rely on Active Directory, setting up a Domain Controller and practicing Kerberos or LDAP exploitation can be especially useful.
Platforms like TryHackMe offer guided learning paths, while Hack The Box provides more challenging, self-directed scenarios. Participating in bug bounty programs through sites like HackerOne or Bugcrowd gives you real-world experience – finding even one valid bug can significantly boost your resume. To stand out further, create and host custom scripts (using Python, Bash, or PowerShell) on GitHub.
Document your work by writing detailed walkthroughs and publishing them on platforms like Medium or LinkedIn. Build a portfolio that includes sanitized penetration testing reports. These should feature an Executive Summary for leadership and detailed technical findings for engineers. When discussing your cleared work, keep descriptions general and focus on your technical contributions without revealing classified information.
Conclusion
Your path in cleared penetration testing hinges on a mix of technical skills, certifications, and consistent networking efforts. Securing sponsorship for a security clearance – whether through a federal agency or a cleared contractor – is a critical first step. From there, building a strong foundation in core skills prepares you to tackle advanced exploitation techniques.
The demand today goes beyond simply running automated scans. Employers value professionals who can identify chained vulnerabilities that expose real business risks, making your ability to think critically and creatively a key asset.
Earning practical certifications like OSCP or PNPT is a smart move. These credentials not only validate your hands-on expertise but also help you stand out in the hiring process. To further showcase your capabilities, build a public portfolio with examples like CTF walkthroughs, GitHub projects, or verified bug bounty reports.
Remember, your technical work is only part of the equation. The ability to translate complex findings into actionable insights for stakeholders is just as important. As CyberPhiLearn aptly states:
You are not paid to hack; you are paid to write a report.
Focus on creating reports that are both clear and impactful. Include executive summaries for decision-makers and detailed technical explanations for engineering teams.
Networking is another cornerstone of success. Engage with local OWASP chapters, attend cybersecurity events like BSides or DEF CON, and connect with experienced penetration testers. With about five open cybersecurity roles for every qualified candidate [1] and an expected 32% growth in information security analyst positions by 2032 [22], the opportunities are vast for those who prepare thoughtfully.
Stay sharp by keeping an eye on emerging trends, such as Active Directory exploitation, cloud security, and AI-driven penetration testing, which can complement your existing expertise. Under the Trusted Workforce 2.0 framework, maintaining your clearance means adhering to continuous vetting processes and promptly reporting any adverse life events. Long-term success in this field comes down to preparation, transparency, and an unwavering commitment to trust.
FAQs
How do I get a security clearance sponsor?
To secure a security clearance sponsor, you generally need to be employed by a government agency or a contractor involved in classified work. Companies and organizations in fields like defense, intelligence, or government contracting are common sponsors. After you’re hired, your employer works with a Facility Security Officer (FSO) to start the background check and clearance process. Whether you’re sponsored depends on whether your job requires access to classified information.
What can block me from getting cleared?
When applying for clearance, several factors can stand in your way. These include dishonesty or leaving out important details on security forms, criminal behavior, substance abuse (drugs or alcohol), financial troubles, mental health concerns, or connections to individuals or groups that raise red flags. It’s crucial to be honest and provide complete information in your application to steer clear of these potential obstacles.
Which cert should I get first for cleared pentesting?
The OSCP (Offensive Security Certified Professional) is often recommended as the first certification for those pursuing cleared penetration testing roles. It’s highly regarded in the industry because it emphasizes practical, hands-on skills through realistic scenarios. While certifications like CEH or CRTP also hold value, OSCP is considered the ideal starting point. Its focus on real-world applications and strong reputation make it an excellent foundation for building expertise in offensive security.
Related Blog Posts
- OSCP Certification Career Guide for Cleared Offensive Security
- PenTest Plus Certification Career Guide for Cleared Pen Testers
- LPT Certification Career Guide for Cleared Pen Test Leads
- eJPT Certification Career Guide for Cleared Junior Pen Testers
