When cyberattacks hit government or defense networks, Incident Response Analysts are the first line of defense. These cybersecurity experts detect, investigate, and neutralize threats to protect sensitive systems. For cleared professionals, this role offers high demand, competitive pay ($80,000–$138,000 annually, with some earning $200,000), and career stability.
Key takeaways:
- Role Overview: Analysts monitor systems, respond to alerts, perform forensic investigations, and secure classified data.
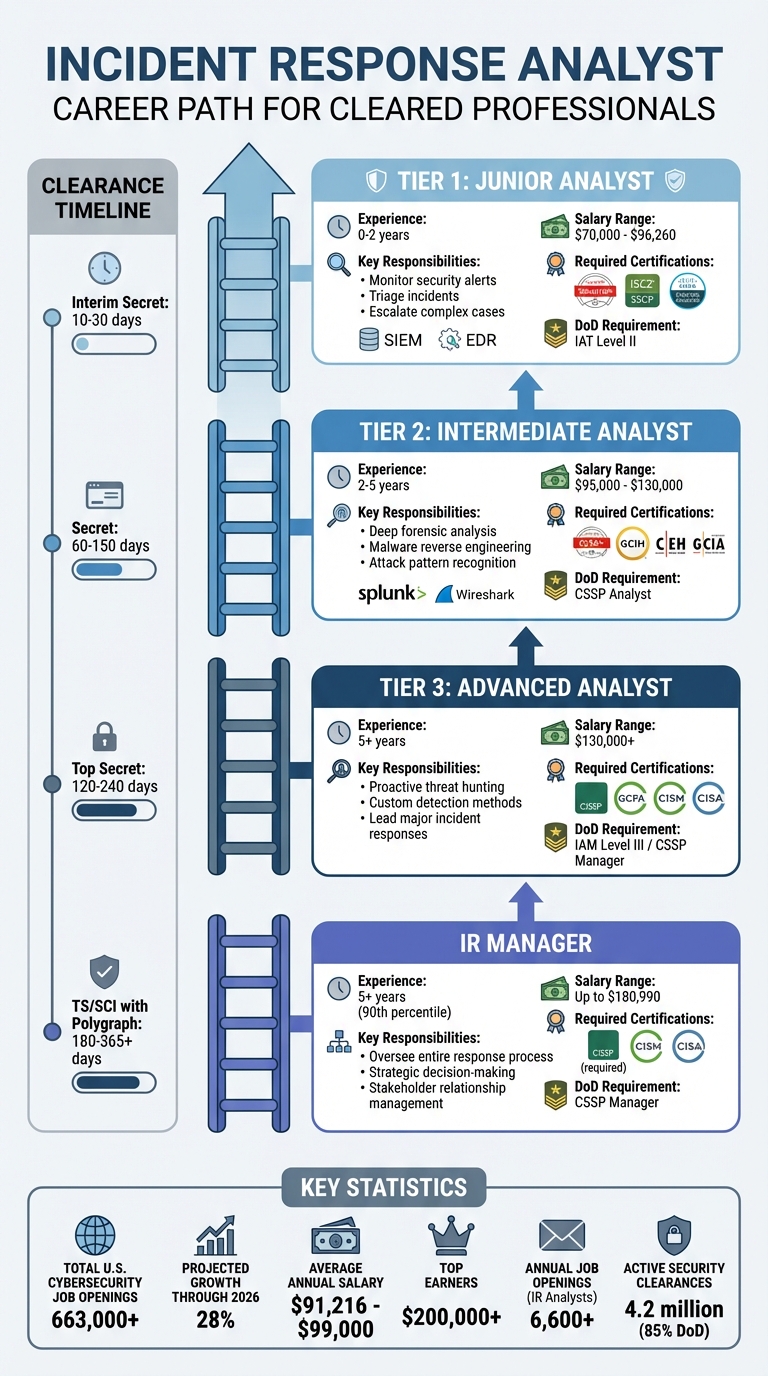
- Career Path: Progression includes Tier 1 (entry-level), Tier 2 (intermediate), Tier 3 (advanced), and management roles, with salaries increasing at each level.
- Skills & Certifications: Proficiency with tools like Splunk and EDR, strong communication skills, and certifications (e.g., CompTIA Security+, CISSP) are essential.
- Security Clearance: Secret or Top Secret clearance is often required, with a rigorous background check process.
- Job Market: The U.S. has over 663,000 cybersecurity job openings, with a projected 28% growth through 2026.
This career combines technical expertise, clearances, and certifications to protect critical systems while offering lucrative opportunities for growth.
Incident Response Analyst Career Path: Tiers, Salaries, and Certifications
Main Duties of a Cleared Incident Response Analyst
Daily Tasks and Responsibilities
Cleared Incident Response Analysts are on the front line, monitoring classified networks with tools like Security Information and Event Management (SIEM) and Endpoint Detection and Response (EDR). Their goal? Spot unusual activity that might signal a breach [8, 10, 11]. When an alert pops up, they dig into its origins, pinpoint vulnerabilities, and act fast – whether that means isolating a compromised system or disabling an affected account [9, 11]. These steps are crucial for maintaining the integrity of classified environments.
Forensic analysis is another key part of the job. Analysts sift through system data, log files, and network traffic to piece together what happened during a breach and figure out what information was exposed [9, 10]. Collaboration is also essential. They work closely with IT teams, legal departments, and even law enforcement to ensure a coordinated response that meets regulatory standards [5]. In classified settings, every finding is meticulously documented to comply with frameworks like SOC 2 and ISO 27001 and to support post-incident reviews [8, 10]. The best Security Operations Centers aim to detect threats in under 15 minutes and respond to critical alerts within an hour [6].
Working With Classified Information
Handling classified data adds another layer of complexity. Analysts must follow strict Chain of Custody protocols, carefully documenting every step of evidence collection, transfer, and analysis to ensure it holds up in legal or governmental settings [8]. Tools like write-blockers are used to prevent accidental changes during data collection, and forensic images are verified with cryptographic hashes to maintain accuracy [8]. Organizations with advanced data classification systems report 68% fewer unauthorized data exposures, highlighting the importance of these processes [7].
Beyond technical work, analysts must communicate findings clearly to stakeholders. This involves translating complex technical details into straightforward explanations while adhering to notification rules based on the classification level of the data [14, 16]. As the field evolves, so do the skills and responsibilities required at different experience levels.
Job Levels in Cleared Incident Response
Careers in cleared incident response follow a structured path, with increasing responsibilities tied to technical expertise and the management of classified data.
- Tier 1 (Junior) analysts: With 0–2 years of experience, these analysts handle initial tasks like monitoring alerts, triaging incidents, and escalating more complex cases. Salaries for this level range from $74,390 to $96,260 [10, 11].
- Tier 2 (Intermediate) analysts: With 2–5 years under their belts, these professionals take on deeper forensic analysis, malware reverse engineering, and pattern recognition to identify attack methods [6].
- Tier 3 (Advanced) analysts: With over 5 years of experience, these analysts focus on proactive threat hunting, crafting custom detection methods, and leading major incident responses [6].
- IR Managers: At the senior level, managers oversee the entire response process, make strategic decisions, and maintain relationships with stakeholders. Those at the 90th percentile of experience can earn around $180,990 [8, 9, 10].
Each tier reflects a blend of technical skill and the ability to handle increasingly sensitive and complex responsibilities.
Required Skills, Education, and Certifications
Technical and Soft Skills
To excel as a cleared Incident Response Analyst, a blend of technical expertise and strong communication skills is essential. Analysts must have a solid grasp of network security and traffic analysis, including TCP/IP, networking ports, protocols, and the OSI model. Tools like Wireshark, Zeek (Bro), and Suricata are critical for identifying malicious traffic. Familiarity with SIEM platforms such as Splunk, IBM QRadar, ArcSight, and ELK Stack is also a must for real-time monitoring and correlating security events. Additionally, proficiency with endpoint detection and response tools strengthens analytical capabilities.
Digital forensics skills are another cornerstone of the role. Analysts rely on tools like Autopsy, FTK Imager, and Volatility to investigate compromised systems, recover evidence, and trace attacker activity. For advanced roles, knowledge of malware analysis becomes critical. This involves understanding malware behavior and reverse engineering it using tools like IDA Pro, Ghidra, or Cuckoo Sandbox. Command-line expertise in Unix/Linux and Windows system administration is also key for navigating large log files and connecting data points efficiently.
Beyond technical abilities, soft skills play a vital role. Critical thinking helps analysts break down complex attack scenarios, especially under classified conditions. Clear communication is equally important for creating reports that both technical and non-technical audiences can understand. These skills ensure that analysts can navigate the strict protocols tied to security clearances [9][2].
Education Options for Cleared Professionals
Most employers (70%) require a bachelor’s degree in Computer Science, Cybersecurity, or a related field [10]. Advanced degrees are often seen as an advantage. For cleared professionals, military service or federal government experience can provide an alternative pathway, offering both technical training and the necessary security clearances. This combination not only simplifies the clearance process but also builds a strong foundation in cybersecurity.
Practical, hands-on experience is equally important. Building a home lab to practice forensic techniques, participating in Capture the Flag (CTF) competitions on platforms like TryHackMe and Hack The Box, and contributing to open-source projects like TheHive, Wazuh, or Cortex are excellent ways to gain real-world skills. Many professionals begin their careers in entry-level roles such as Network Administrator or SOC Analyst (Tier 1), often spending 2–3 years in these positions before transitioning into Incident Response Analyst roles. With the cybersecurity field expected to grow by 28% through 2026 and an average annual salary for incident analysts around $99,000, the time and effort invested in education and training are well worth it [10].
Certifications for Each Career Stage
Certifications are a critical stepping stone, especially for those without traditional degrees. In fact, 70% of hiring managers prioritize certifications that validate job-specific skills [10][1].
- Entry-level professionals (0–2 years, earning $70,000 to $95,000) should focus on certifications like CompTIA Security+, ISC2 SSCP, or Cisco CyberOps Associate, which align with IAT Level II under DoD 8570/8140 requirements.
- Mid-level analysts (3–5 years, earning $95,000 to $130,000) benefit from certifications such as CySA+, GCIH, CEH, or GCIA, which emphasize incident detection and response. These map to CSSP Analyst roles.
- Senior analysts (5+ years, earning $130,000 or more) are expected to pursue advanced certifications like CISSP, GCFA, GCFE, CISM, or CISA, which focus on forensic investigation and leadership. These certifications align with IAM Level III or CSSP Manager positions [9][10][1][2].
For Department of Defense (DoD) roles, candidates often start with a baseline certification but must achieve a CSSP-A level certification within 180 days of hire [2].
Additionally, scripting proficiency and familiarity with the NIST SP 800-61 guide are crucial for career advancement [11]. Combining certifications with practical experience and formal education creates a strong foundation for navigating the rigorous clearance process, which will be explored in the next section.
Getting and Maintaining Security Clearance
Clearance Levels and What They Mean
Security clearance isn’t just about access – it’s a cornerstone of many careers in government and defense. It’s required for roles that deal with classified networks and sensitive intelligence, and the level of clearance you hold dictates what systems you can use and which incidents you can investigate [13].
Here’s a breakdown of the main clearance levels:
- Secret (Tier 3): Grants access to information that could cause serious harm to national security if disclosed. This level, common among Department of Defense (DoD) contractors, involves a National Agency Check with Law and Credit (NACLC) review.
- Top Secret (Tier 5): Opens the door to information that could cause "exceptionally grave damage" to national security. It requires a Single Scope Background Investigation (SSBI), covering a detailed 10-year history.
- Top Secret/Sensitive Compartmented Information (TS/SCI): The highest level, often required for intelligence and cyber threat roles. This clearance may include a polygraph and grants access to highly sensitive sources [13].
Currently, around 4.2 million government and contractor employees hold security clearances, with 85% of them working for the DoD [15][12]. Next, let’s dive into how these clearances are vetted and approved.
The Background Investigation Process
To get started, you’ll need a government agency or authorized contractor to sponsor your application after offering a conditional job based on a "need-to-know" basis [13][14]. Once sponsored, you’ll fill out the Standard Form 86 (SF-86) using the eApp platform, which replaced the older e-QIP system in 2026. This form requires extensive details about your last 10 years, including residences, jobs, foreign contacts, and financial history [13][18].
The Defense Counterintelligence and Security Agency (DCSA) handles the bulk – 95% – of federal background checks [13][16]. During the investigation, they’ll verify your employment, credit history, and criminal records, and they’ll interview references. For Top Secret clearances, the process goes deeper, with investigators speaking to neighbors, coworkers, and personal contacts.
Here’s how long it typically takes:
- Interim Secret: 10 to 30 days
- Secret: 60 to 150 days
- Top Secret: 120 to 240 days
- TS/SCI with polygraph: 180 to over 365 days [13]
"The SF-86 application process creates more problems when candidates hide information than the actual issues they try to conceal." – JOBSwithDOD [17]
Clearance denials happen most often due to financial issues (40%), followed by criminal conduct (24%) and dishonesty (15%) [17][18]. Certain factors will disqualify you outright, such as non-U.S. citizenship, illegal drug use (including marijuana, which remains federally illegal), dishonorable military discharge, or being declared mentally incapacitated [12][13].
This rigorous process directly ties into the career options available to you, as outlined below.
How Clearance Affects Your Career Options
Your clearance level doesn’t just define what you can access – it shapes your career path. High-level roles like Information Systems Security Officer (ISSO), Cyber Threat Intelligence Analyst, and Network Defense Forensics Analyst require active clearances [13]. If you leave a cleared position, your clearance becomes inactive after 24 months, but a new sponsor can reactivate it within that time [13].
Since 2026, the Trusted Workforce 2.0 (TW 2.0) framework has replaced periodic reinvestigations with Continuous Vetting (CV). This system keeps tabs on criminal records, credit issues, and foreign travel in real-time. It also requires you to self-report significant events like arrests, major debts, or financial changes. Not reporting such events is often seen as a bigger violation than the issue itself.
"A security clearance is a privilege, not a right. Mishandling classified documents can lead to criminal charges, job loss, and fines." – US Federal Contractor Registration (USFCR) [14]
Adjudicators also check publicly available information like social media, GitHub contributions, and other online activity to assess your judgment and operational security awareness [13][15]. Before applying, it’s wise to:
- Pull your credit report and address any issues.
- Review your social media privacy settings.
- Compile a complete list of foreign contacts, including names and nationalities.
Honesty is critical on your SF-86. Disclosing past issues, like financial troubles or minor drug use, is often viewed more favorably under the "whole-person concept" than trying to hide them [13][15].
| Clearance Level | Investigation Tier | Typical Scope | 2026 Avg. Timeline |
|---|---|---|---|
| Secret | Tier 3 | 5-10 year record verification; some interviews | 60 – 150 Days |
| Top Secret | Tier 5 | 10-year scope; in-person interviews | 120 – 240 Days |
| TS/SCI | Tier 5 + Polygraph | Tier 5 scope plus specialized polygraph exam | 180 – 365+ Days |
| Interim Secret | N/A | Initial fingerprint and database checks | 10 – 30 Days |
Finding Jobs and Building Your Network
Writing a Resume for Cleared Positions
When crafting a resume for cleared incident response roles, it’s crucial to balance showcasing your skills with maintaining operational security. Start with a clear and concise summary at the top. Highlight your years of experience, certifications, and specific incident response expertise. Skip the buzzwords and keep it factual – this isn’t the place for subjective self-praise [19][20].
Include a technical skills section that lists tools you’ve worked with, like SIEM platforms, intrusion detection systems, forensics software, and vulnerability scanners [21]. For your work history, use the STAR method (Situation, Task, Action, Result) to frame your accomplishments in measurable terms. For example, instead of saying "Handled security incidents", you could write, "Reduced detection time by 35% through automated SIEM correlation rules across 12 classified networks" [21].
Operational security is non-negotiable. Clearly state your clearance level and issuing agency at the top of your resume, but avoid mentioning classified project names, colleague identities, or sensitive budget details [19][20]. Also, be mindful of how much experience you highlight. Surprisingly, listing "30+ years of experience" can sometimes deter recruiters, who may interpret it as a sign of inflexibility or high salary expectations. Many cleared positions cap requirements at 10 years [19][20].
Keep your resume simple and streamlined – 1-2 pages max, with no graphics or shading that might confuse applicant tracking systems [19][20]. If you’re working toward certifications like CISSP or CEH, include them along with expected completion dates. This can sometimes satisfy a job requirement and prompt a recruiter to reach out [21].
"Your security-cleared resume is not a biography or a mere list of qualifications. It’s an ad designed to help you land that coveted cleared job interview…" – Ashley Jones, Editor, ClearedJobs.Net [19]
One more thing: don’t list your clearance on public LinkedIn profiles. While it’s essential for specialized job boards, displaying it publicly can be a red flag for some contractors [19][20]. Once your resume is polished, focus on connecting with recruiters through dedicated cleared job platforms.
Using Cleared Cyber Security Jobs for Your Search
For those in the cleared community, using platforms tailored to your field can make job searching more efficient. Cleared Cyber Security Jobs is a veteran-founded job board designed exclusively for professionals like you. It connects incident response experts directly with employers offering cleared positions, cutting out staffing firms and third-party recruiters.
Upload your resume to the platform’s database so employers can find you directly. Set up job alerts to have relevant postings sent straight to your inbox. Use search filters to narrow results by clearance level (Secret, Top Secret, TS/SCI), location, and specific roles like "SOC analyst", "threat hunter", or "digital forensics."
Here’s a pro tip: stay active on the platform. Many cleared job boards prioritize the most recently active profiles in search results. Even if you’re not actively job hunting, logging in weekly keeps your profile visible to recruiters [23]. The platform also offers job fairs, providing a rare chance to meet employers face-to-face – a crucial advantage in the often discreet world of cleared hiring.
Networking in the Cleared Community
Building a network in the cleared world takes effort and strategy. Attending conferences like BSides, Black Hat, DEF CON, and RSA is a great way to meet peers and hiring managers. But the real magic often happens during "HallwayCon" – those informal chats between sessions [22]. If the cost of attending is a barrier, consider volunteering. Not only will you gain free access to sessions, but you’ll also build trust within the community and get valuable face time with industry leaders [22].
Another underused strategy is conducting informational interviews. Reach out to professionals whose careers you admire and ask for a brief conversation about their journey. These chats can lead to learning about job openings that never make it to public listings [22].
The secret to networking is staying engaged. It’s not a one-and-done activity. Keep in touch with your contacts, share articles they might find useful, and offer assistance when you can. An active approach to maintaining relationships ensures your network remains a valuable resource throughout your career. If your efforts seem to stall, it’s often because you’ve let those connections fade after the initial meeting [22].
"In the competitive field of cyber security, networking can be the key to unlocking new opportunities." – CyberSecJobs.com [22]
sbb-itb-bf7aa6b
Advancing Your Career in Cleared Incident Response
Choosing a Specialty Area
Once you’ve established a solid foundation in incident response, diving into a specialty can open doors to higher earnings and career growth. One intriguing path is malware analysis – breaking down malicious code to uncover its purpose, origin, and potential impact [26]. If you’re drawn to proactive measures, threat hunting lets you uncover hidden dangers before they escalate. Alternatively, incident readiness and resilience focuses on creating response plans, crafting playbooks, and running tabletop exercises to strengthen an organization’s defenses [25].
Your choice of specialty should align with your interests and long-term goals. For instance, if you enjoy unraveling complex technical puzzles, areas like malware analysis or digital forensics might be a great fit. On the other hand, if you’re inclined toward leadership, moving into incident response management could be the right move. This role involves overseeing teams, delivering threat assessments, and leading responses to major incidents [27]. For those who prefer staying hands-on, becoming a subject matter expert (SME) or engineer allows you to master advanced tools and techniques while avoiding management responsibilities [26].
Some specialized roles, such as Cyber Incident Response Analysts working in OT/ICS/SCADA environments, may involve travel – up to 25% in some cases [24]. Meanwhile, emerging fields like cloud incident response and AI security are gaining traction, supported by certifications like the AI Red Teamer (OSAI+) [26]. Companies like LevelBlue, which has handled over 9,000 incidents and conducted more than 1,000 tabletop exercises, are shifting focus from reactive responses to proactive readiness with offerings like "Resilience Retainers" [25].
Continuing Education and Skill Development
After narrowing down your specialty, staying ahead of the curve is crucial. The cybersecurity landscape evolves rapidly, so continuous learning is non-negotiable. Advanced certifications can help you maintain your edge. For example, the GIAC Certified Incident Handler (GCIH) is highly regarded for managing security events, while the Computer Hacking Forensic Investigator (CHFI) certifies expertise in evidence collection and maintaining a legal chain of custody [3][28]. For leadership roles, the CISSP is often a must-have for positions like Intrusion Detection Specialist or Incident Manager [27].
Certifications like the CHFI need to be renewed every three years, requiring EC-Council Continuing Education credits to stay valid [28]. But formal credentials are just one piece of the puzzle. Hands-on experience is equally important. Setting up a home lab with virtual environments lets you practice critical skills like monitoring, reverse engineering, and forensics without risking production systems [3]. You can also participate in Capture The Flag challenges or contribute to open-source projects to sharpen your abilities and build your professional reputation [3][26].
The field is expanding into areas like IoT forensics, cloud forensics, and mobile device encryption countermeasures [28]. With AI becoming integral to faster case triage and hybrid environments – spanning cloud, mobile, and operational technology – being the new norm [1][28], staying updated through webinars, industry publications, and community forums is essential.
Salary and Job Stability
Specializing and keeping your skills sharp naturally leads to better pay and job security. Cleared incident response roles are known for their strong financial rewards. As of September 21, 2023, the average annual salary for an Incident Responder in the U.S. was $91,216, with most professionals earning between $56,000 and $118,000 [26]. Top earners can take home over $136,000, while mid-level professionals with certifications like CHFI typically earn $70,000 to $120,000 [26][28]. Senior or highly specialized roles often command salaries ranging from $75,000 to over $130,000 [11].
Location plays a big role in compensation. For instance, jobs in the Washington, D.C. metro area often come with higher pay to offset the region’s higher cost of living. Transitioning from an entry-level role, such as Cybersecurity Specialist, to a mid-level role like Incident Response Analyst typically takes 2–3 years, with each step up bringing a noticeable salary bump [1].
Job stability in this field is exceptional. Cybersecurity threats are constant across industries like finance, healthcare, and government, ensuring that skilled professionals remain in demand [26]. Unlike some tech roles that can be outsourced or automated, incident response relies heavily on human expertise – especially when dealing with classified information. This makes it a reliable and resilient career path, highlighting the importance of specialization and lifelong learning for sustained success.
From NOC Analyst to Incident Response Analyst
Conclusion
Building a successful career as a cleared Incident Response Analyst requires a combination of technical expertise, strategic certifications, and effective networking. Mastering tools like SIEM and EDR is just the start – you also need the ability to explain complex findings clearly and calmly under pressure. As Hemant Patkar, CISSP, emphasizes:
Maintaining a calm demeanor is essential, ensuring clear and timely communication with all stakeholders who need to be informed [29].
Certifications play a crucial role in validating your skills and advancing your career. Start with beginner-level certifications like CompTIA Security+ or Cisco CyberOps Associate. As you gain experience, move on to intermediate options such as the Certified Ethical Hacker (CEH) and then pursue advanced credentials like GIAC GCIH or CISSP. These certifications not only demonstrate expertise but also pave the way to higher-paying roles [3][4].
With rapid changes in the cybersecurity landscape – highlighted by over 69% of professionals noting significant industry shifts [29] – staying ahead is critical. Hands-on practice through home labs, Capture the Flag challenges, and open-source projects can help sharpen your skills [3]. As Louis Eriakha from Techloy points out:
Incident response is one of the most in-demand roles in cybersecurity right now – and it’s only growing [4].
Networking is equally important. Platforms like Cleared Cyber Security Jobs connect you with employers who understand the unique requirements of cleared positions. With more than 6,600 incident analyst job openings annually and a projected 28% growth in cybersecurity roles [10], the field offers immense opportunities for those who continually invest in their skills and maintain their clearances.
Climbing the ladder from SOC Analyst to Senior Incident Response Lead demands dedication, but the rewards – both financial and professional – are well worth it. By staying curious, documenting your processes, and honing your ability to detect, contain, and recover from cyber threats, you position yourself as an indispensable asset in safeguarding national security.
FAQs
How do I move from SOC Tier 1 into incident response?
To move from a SOC Tier 1 position into incident response, you’ll need to strengthen your technical skills and expand your knowledge base. Start by earning certifications such as CySA+ or CISSP, which are highly regarded in the field. Focus on mastering areas like log analysis, threat detection, and digital forensics – these are core components of incident response work.
Practical experience is equally important. Get hands-on with tools like SIEM and EDR platforms, as these are essential for monitoring and responding to security incidents. Networking within your organization can also open doors; connect with colleagues in the incident response team to learn from their expertise. Finally, seek out specialized training programs to further hone your skills and prepare for the more advanced challenges of incident response.
What clearance issues most often delay or derail hiring?
Lengthy processing times are one of the biggest hurdles in hiring for security-cleared roles, with investigations often stretching out for 6–12 months or even longer. Backlogs in cases add to the delays, particularly when the investigations are more complex. Issues like drug use or financial concerns can make the process even slower, creating significant challenges for meeting hiring timelines.
Which certification should I get next for my tier?
The next certification that’s right for you depends on your career path and goals. If you’re aiming to grow in incident response or cybersecurity, the CISSP is a strong choice, especially for senior-level roles. For those looking to sharpen technical skills in threat detection, CySA+ is a great option. If you want to dive deeper, certifications like Security+ or CISSP can help you access higher-level opportunities. Choose certifications that align closely with your professional aspirations and current expertise.
