Cyber threat hunting is an active cybersecurity role where professionals search for hidden threats that bypass automated systems. For those with security clearances, this career offers high responsibility, protecting sensitive government and defense data from advanced threats like state-sponsored hackers and insider risks. Average salaries start at $159,500, with senior roles reaching $181,500. Demand is growing by 15% annually, driven by increasing cyber breaches.
Key Takeaways:
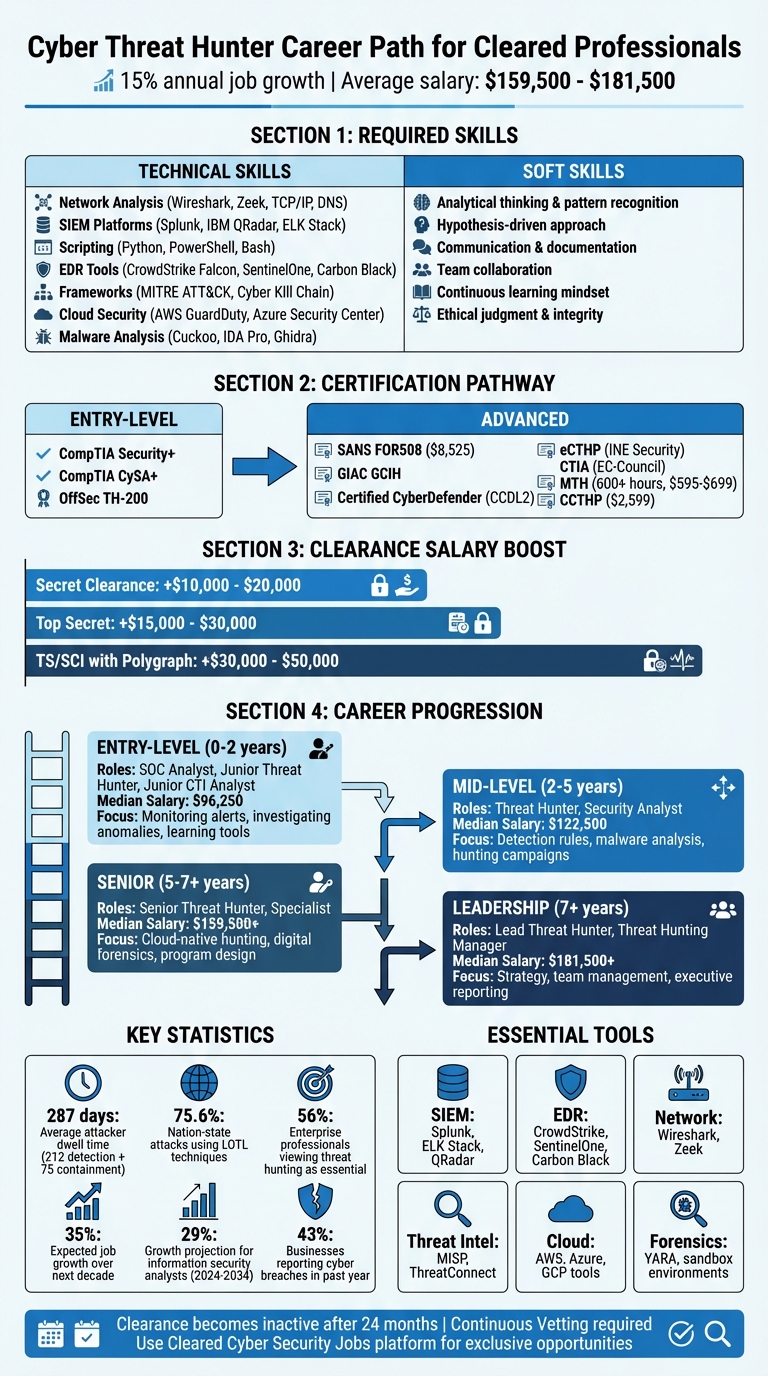
- Skills Needed: Master tools like Splunk, Wireshark, and EDR platforms (e.g., CrowdStrike). Learn scripting (Python, PowerShell) and frameworks like MITRE ATT&CK.
- Certifications: Start with CompTIA Security+ or CySA+, then pursue advanced options like SANS FOR508 or GIAC GCIH.
- Clearance Advantage: A security clearance can boost salaries by $10,000–$50,000 and unlock exclusive roles.
- Job Search Tips: Network at cleared job fairs, use platforms like Cleared Cyber Security Jobs, and highlight your clearance on your resume.
This field offers a clear progression path, starting with SOC Analyst roles and leading to leadership positions. Cyber threat hunting is a lucrative, growing career for cleared professionals with the right skills and certifications.
Cyber Threat Hunter Career Path: Skills, Certifications, and Salary Progression
Required Skills for Cleared Cyber Threat Hunters
Technical Skills
Cleared professionals need a robust set of technical skills to excel in cyber threat hunting. For starters, tools like Wireshark and Zeek are essential for analyzing network traffic, including protocols like TCP/IP, DNS, and HTTP/s. These tools help identify hidden command-and-control channels attackers use to communicate with compromised systems [1][2].
Proficiency with log investigation and Security Information and Event Management (SIEM) platforms is another must. Tools like Splunk, IBM QRadar, or the ELK Stack allow threat hunters to sift through massive datasets. Advanced querying languages, such as SPL (Splunk Processing Language) or KQL (Kusto Query Language), are key to uncovering threats buried in logs [1][2]. Additionally, scripting skills in Python, PowerShell, or Bash are invaluable for automating repetitive tasks and creating custom detection scripts tailored to specific environments [1][2].
Endpoint Detection and Response (EDR) tools, such as CrowdStrike Falcon, SentinelOne, or Carbon Black, provide detailed insights into individual systems. These tools are critical for spotting lateral movement, persistence techniques, and other signs of an attacker’s presence [1][2]. Understanding malware behavior is equally important, whether through sandbox testing with tools like Cuckoo or reverse engineering with IDA Pro and Ghidra. These skills help identify adversary tactics and strengthen defenses [1][2].
Nation-state adversaries often employ "Living off the Land" (LOTL) techniques, which involve using legitimate system tools to blend into normal network activity. This makes detection particularly challenging, as LOTL techniques account for 75.6% of nation-state attacks [7]. To counter these threats, deep knowledge of Windows and Linux internals – especially persistence mechanisms and privilege escalation methods – is critical [6].
Threat hunters also rely on frameworks like MITRE ATT&CK and the Cyber Kill Chain to map adversary tactics, techniques, and procedures (TTPs). These frameworks help predict and counter attackers’ next moves, especially in cleared environments [1][3]. With the growing reliance on cloud infrastructure, expertise in cloud-native security tools like AWS GuardDuty, Azure Security Center, and Google Chronicle is becoming increasingly important for identifying threats in dynamic cloud environments [2].
While technical skills form the backbone of threat hunting, success also depends heavily on sharp analytical and interpersonal abilities.
Soft Skills
Being a proficient threat hunter requires more than technical know-how. Analytical thinking is at the core of the job – you need to recognize patterns, work with incomplete information, and uncover adversaries that evade automated defenses. A hypothesis-driven approach sets threat hunters apart, as you’ll proactively form and test theories about potential compromises rather than relying solely on alerts [4].
Communication skills are equally critical. You must translate complex technical findings into actionable intelligence for both technical teams (like SOCs or Incident Response) and non-technical stakeholders, such as executives. Clear and detailed documentation is also essential for creating repeatable playbooks and ensuring auditability of your findings [4].
Collaboration is another cornerstone of effective threat hunting. You’ll frequently work with detection engineers, SOC analysts, and risk teams to turn your discoveries into automated defenses. A curious mindset and a commitment to continuous learning are vital, as you’ll need to stay ahead of evolving TTPs by thinking like an attacker. Finally, given the sensitive nature of your work, ethical judgment and integrity are non-negotiable – you must handle classified information responsibly and use your access solely for defensive purposes [1][3].
sbb-itb-bf7aa6b
Certifications for Cyber Threat Hunters
Entry-Level Certifications
To kickstart a career in cyber threat hunting, entry-level certifications provide a solid foundation in security principles and practices.
- CompTIA Security+: This certification covers the essentials, such as threat management, vulnerabilities, and security operations. It also meets baseline requirements for professionals working in Department of Defense (DoD) roles.
- CompTIA CySA+ (Cybersecurity Analyst): Designed for those focusing on proactive threat detection, this certification emphasizes behavioral analytics, trend identification, and anomaly detection – key skills for threat hunters.
- OffSec TH-200: This program dives into indicators of compromise (IOCs) and adversarial tactics. It introduces structured methodologies for conducting threat hunts and analyzing network traffic.
Once you’ve built a foundation with these certifications, you’re ready to explore advanced options to deepen your expertise.
Advanced Certifications
For seasoned professionals, advanced certifications provide the tools to combat sophisticated cyber threats. These programs are particularly valuable for those with security clearances or roles in highly sensitive environments.
- SANS FOR508: Widely regarded as the gold standard, this 54-hour course focuses on advanced incident response and threat hunting. Priced at $8,525 (excluding exam and renewal fees), it covers persistent threats, memory forensics, and investigative techniques critical for high-level security operations [10].
- GIAC Certified Incident Handler (GCIH): This certification highlights expertise in detecting and resolving security incidents. Its alignment with both DoD and NICE frameworks makes it a strong choice for professionals in government-related roles.
- Certified CyberDefender (CCDL2): Featuring a 48-hour practical exam, this certification tests real-world investigation skills. It has been praised by professionals from companies like Microsoft, IBM, and Accenture for its vendor-neutral, high-quality lab content [12].
- eCTHP (INE Security): This hands-on certification includes a practical exam based on real-world malware scenarios. It requires a VPN connection and hardware with at least 8GB of RAM for virtualization [9].
- Certified Threat Intelligence Analyst (CTIA): Offered by EC-Council, this certification integrates threat intelligence with automated hunting and SOC operations. It’s listed in U.S. Army and Navy COOL programs, making it particularly relevant for military and defense contractors [14].
- Mosse Certified Threat Hunter (MTH): With over 600 hours of training and lifetime access for $595–$699, this certification focuses on Windows internals like the Registry, Event Logs, and Services [10].
- Infosec Cyber Threat Hunting Boot Camp: Priced at $2,599, this program includes the Certified Cyber Threat Hunting Professional (CCTHP) credential. It aligns with DoD, NICE, and NIST frameworks and has received a 4.6/5 rating from 738 reviews. With information security analyst roles projected to grow 29% between 2024 and 2034 [8] and the threat hunting field expected to expand by 5% [11], this certification can set you apart in a competitive job market.
These certifications not only enhance your technical skills but also position you for long-term success in the evolving field of cyber threat hunting.
Daily Responsibilities and Tools
Primary Job Duties
Cyber threat hunters working in cleared environments operate with the mindset that attackers are already inside the network. Instead of waiting for automated systems to flag issues, they actively search for signs of compromise, assuming defenses have already been breached. Their mission is to uncover hidden adversaries before automated detection tools even raise an alert.
On a typical day, these professionals analyze massive datasets from endpoints, cloud environments, and network logs. They’re looking for patterns and anomalies that automated systems might miss. This proactive approach is critical in cleared environments, where state-sponsored attackers and advanced persistent threats often target sensitive national security interests. Hunters map their discoveries to known adversary tactics and procedures. When they identify unusual activity, they trace indicators, conduct host acquisitions, and analyze malware behavior. The ultimate goal? To minimize "dwell time", or the period attackers remain undetected. Right now, the average dwell time across organizations is 287 days – 212 days for detection and 75 days for containment [13].
Collaboration is another key part of the role. Threat hunters work closely with engineering teams to create automated detection rules and develop playbooks tailored for both technical teams and executive decision-makers. With 56% of enterprise-level cybersecurity professionals viewing threat hunting as essential for improving security [13], the demand for these roles is expected to grow by 35% over the next decade [5].
To tackle these challenges, threat hunters depend on a robust set of tools to turn raw data into actionable insights.
Common Tools and Technologies
The tools of a threat hunter are designed to handle and analyze security data on a large scale. Security Information and Event Management (SIEM) platforms like Splunk, ELK Stack, and QRadar allow hunters to query logs using languages such as KQL, SQL, or regex. For endpoint visibility, tools like CrowdStrike Falcon, SentinelOne, and Carbon Black provide insights into process creation, registry changes, and potential lateral movement within machines.
When it comes to network analysis, tools like Wireshark and Zeek help hunters inspect packets and identify command-and-control traffic. Threat intelligence platforms such as MISP and ThreatConnect are also essential for managing indicators of compromise and profiling threat actors’ tactics. As more organizations adopt cloud-native environments, expertise in analyzing logs from platforms like AWS, Azure, and GCP – along with familiarity with Kubernetes signals and eBPF telemetry – has become increasingly important.
Automation plays a huge role in this field. Skills in Python, PowerShell, and Bash allow hunters to automate repetitive tasks and create custom detection scripts. For forensics and malware analysis, tools like YARA scanners, sandbox environments, and binary triage software help reconstruct attack timelines and examine malicious code. These specialized skills are highly valued and reflected in the competitive salaries offered for these roles.
Using Your Security Clearance for Career Growth
Clearance Advantages
If you’re a cyber threat hunter with an active security clearance, you’re holding one of the most powerful tools for career advancement in the cybersecurity world. A clearance unlocks opportunities that are off-limits to most, such as defending classified networks like SIPRNet, analyzing sensitive threat indicators, or securing government-specific cloud environments like AWS GovCloud and Microsoft Azure Government [16]. Beyond technical qualifications, your clearance signals loyalty, reliability, and sound judgment – qualities that are essential for success in this field [3][16]. It also gives employers a huge hiring advantage by cutting down the lengthy background check process [17].
The financial perks are just as compelling. For instance, a Secret clearance can bump your salary by $10,000–$20,000, while a Top Secret clearance might add $15,000–$30,000. If you hold a TS/SCI clearance with a polygraph, that premium can soar to $30,000–$50,000 over similar roles without clearance [20]. Thanks to the Trusted Workforce 2.0 initiative, clearance reciprocity across federal agencies is improving, making it easier to transition between departments or contractors without starting from scratch [16].
Brad Tachi, the Founder of Best Military Resume, offers a valuable perspective:
"When I transitioned out of the Navy, I did not fully appreciate what my clearance was worth. I spent time applying for jobs that did not require one – which meant I was competing with the entire civilian workforce instead of a much smaller pool of cleared candidates. That is a strategic mistake." [20]
These benefits highlight why your clearance is not just a credential but a powerful career asset.
Highlighting Your Clearance
To maximize these advantages, your resume needs to showcase your clearance effectively. Make it one of the first details recruiters see by listing it prominently at the top of your resume. Be specific about your clearance level – for example, "Top Secret/SCI (Active)" or "Secret (Tier 3)" – as many high-level roles require an active clearance [18].
While being clear is important, protect sensitive information. Mention your clearance level and, if relevant, note that you’ve completed a polygraph. However, avoid revealing classified program names, code words, or any other sensitive details [20]. To further stand out, highlight certifications like GIAC Cyber Threat Intelligence (GCTI) and your expertise in frameworks such as MITRE ATT&CK [19]. Setting up job alerts on platforms like Cleared Cyber Security Jobs can also help you stay ahead of new opportunities tailored to your skills and clearance level.
Keep in mind that clearances become inactive 24 months after leaving a cleared role, although there are proposals to extend this to five years by 2026 [16]. Under the Continuous Vetting system, maintaining your clearance requires proactive steps. Report any significant life changes – like arrests, major financial issues, or foreign contacts – to your Facility Security Officer. Additionally, regularly review your social media privacy settings, as adjudicators increasingly check public-facing online activity for signs of operational security awareness [16].
Networking and Job Search for Cleared Professionals
Building Connections in the Cleared Community
Landing a cyber threat hunter role in the cleared space takes more than just submitting your resume online. Networking plays a huge role, and the cleared community has its own unique way of operating. To get started, connect directly with professionals working in your target roles at respected defense contractors like Peraton. As Bryan Acton, Military & Veterans Program Leader at Peraton, explains:
"Engage your peers and get an employee referral. That’s something I can’t give you as a recruiter." [21]
Referrals not only lead to better hires but also improve retention rates. [23]
Attending cleared job fairs is another excellent way to build connections. Events like Connect Reston (happening October 15–16, 2026, in Reston, VA) and Connect Colorado (scheduled for July 23, 2026, in Colorado Springs, CO) allow you to meet hiring managers from defense and government agencies face-to-face. [25] These events are designed exclusively for cleared professionals, and some are even limited to those with polygraphs. Kirsten Renner, VP of Talent Strategy at SilverEdge Government Solutions, highlights the importance of these events:
"Sometimes what you see posted is just a glimpse into what’s possible." [21]
Many opportunities never appear on public job boards, making these in-person interactions invaluable.
Outside of formal events, you can expand your network by joining online communities like Reddit’s r/netsec or contributing to open-source security projects on GitHub to showcase your skills. After meeting someone, send a brief thank-you email to stay on their radar. Volunteering your cybersecurity skills at conferences or with local non-profits is another way to grow your network while gaining relevant experience to enhance your resume. [22]
These networking efforts work hand-in-hand with the tools available on Cleared Cyber Security Jobs, streamlining your job search.
Finding Jobs on Cleared Cyber Security Jobs
Once you’ve built your network, Cleared Cyber Security Jobs can help you find exclusive opportunities tailored to your clearance level and expertise. This platform is specifically designed for security-cleared cyber threat hunters, so you’ll face less competition compared to general job boards. By uploading your resume, recruiters can find you directly through the platform’s database. You can also set up job alerts with keywords like "Cyber Threat Hunter", "CTI Analyst", or "Insider Threat" to get instant notifications when new roles are posted. [15][24]
The platform’s search filters make it easy to narrow down roles based on your specific clearance level, whether it’s Secret, Top Secret, or TS/SCI. Since many threat hunter roles require active clearances, this feature ensures you’re focusing on the right opportunities. Remember to keep your profile updated and respond quickly, as hiring in the cleared space often moves fast. Additionally, the platform offers access to career resources and specialized job fairs, giving you even more ways to connect with employers actively looking for your skills.
Career Progression from Entry-Level to Leadership
Starting Positions
After building the foundational skills and earning the certifications discussed earlier, your career in threat hunting often begins with roles like SOC Analyst, Security Analyst, Junior Threat Hunter, or Junior Cyber Threat Intelligence (CTI) Analyst. These roles are all about supporting incident response by keeping an eye on alerts and investigating anomalies. You’ll get hands-on experience with tools used in enterprise security, learn to parse logs, and apply frameworks like MITRE ATT&CK. [2][3]
The median salary for entry-level Threat Hunters in the US is around $96,250. [2] To qualify for these positions, a bachelor’s degree in Cybersecurity, Computer Science, or Information Technology is typically required. You’ll also need to be proficient in scripting languages like Python, PowerShell, or Bash, which are essential for automating tasks and developing custom tools. [2] For those just starting out (0-2 years of experience), building a portfolio is key. Platforms like GitHub, participating in Capture The Flag (CTF) challenges, and using lab environments such as TryHackMe or Hack The Box can showcase your skills. [2]
As you gain experience, your responsibilities will transition from operational tasks to more strategic oversight.
Moving into Leadership Roles
With a solid foundation in analysis and communication, experienced threat hunters can step into more strategic positions. Mid-level professionals (2-5 years of experience) take on tasks like designing detection rules, conducting malware reverse engineering, and leading threat-hunting campaigns. These roles come with median salaries of $122,500. [2] Senior threat hunters (5+ years) often specialize in areas such as cloud-native threat hunting or advanced digital forensics. They also define enterprise-wide programs and provide guidance to executives. [1][2]
Leadership roles, such as Lead Threat Hunter or Threat Hunting Manager, typically require 7+ years of experience and shift the focus from technical execution to strategy, team management, and risk oversight. These positions involve allocating resources effectively, staying ahead of emerging threats through AI and automation, and translating technical findings into actionable insights for company executives. Salaries for these roles can exceed $181,500. [1][2] Holding a security clearance can significantly accelerate your career trajectory and unlock leadership opportunities in sensitive environments.
To prepare for leadership, consider pursuing management-focused certifications like the CISSP, mentoring junior team members, and leading collaborative projects that involve IT, engineering, and legal teams. [1][2]
Success in threat hunting demands continuous practice, exposure to real-world attack scenarios, and the ability to learn from both your successes and setbacks. [1]
How to Become a Threat Hunter | Lumen’s Danny Adamitis Interview
Conclusion
Stepping into the world of cyber threat hunting as a cleared professional gives you a distinct edge. Your security clearance – be it Secret, TS/SCI, or Polygraph – opens doors to sought-after roles within government agencies, defense contractors, and critical infrastructure sectors that are often out of reach for others. With the job market for threat hunters expanding at a rate of 15% and nearly 43% of businesses reporting cyber breaches in the past year, the need for proactive threat detection has never been more urgent [2].
Your journey starts with building the right technical skills and earning key certifications. Begin with foundational credentials like CompTIA Security+ or CySA+, and then aim for advanced certifications such as GIAC Cyber Threat Intelligence (GCTI) or SANS FOR508. Learn scripting languages like Python, PowerShell, and Bash to automate processes, and gain hands-on experience with the MITRE ATT&CK framework and tools like Splunk, CrowdStrike, and Wireshark – these will be your everyday arsenal for identifying hidden threats [2].
Networking within the cleared professional community can also accelerate your career. Platforms like Cleared Cyber Security Jobs offer tailored job search tools, resume databases, and job alerts specifically for security-cleared professionals. Additionally, upcoming cleared job fairs in locations such as Falls Church, VA (April 16, 2026), Hanover, MD (May 14, 2026), and Herndon, VA (June 3 and August 27, 2026) provide an excellent opportunity to connect directly with recruiters from top defense contractors [26].
As you gain experience, the financial rewards grow alongside your responsibilities. From entry-level roles to senior and leadership positions, showcasing your skills is essential. Use platforms like GitHub, participate in Capture The Flag events, and engage with lab environments to demonstrate your practical expertise. This field requires continuous practice and exposure to real-world attack scenarios to stay sharp.
FAQs
How do I move from SOC Analyst to Threat Hunter?
Transitioning from a SOC Analyst to a Threat Hunter means diving deeper into understanding adversary tactics, behavioral patterns, and operating system internals. To make this shift, focus on gaining hands-on experience with hunting techniques and methodologies. Developing expertise in cloud-native environments is also becoming increasingly important. Certifications such as CySA+ can help validate your skills and knowledge.
Use your SOC role as a foundation by prioritizing proactive hunting and hypothesis-driven investigations. Building practical experience and documenting your methods will not only help you refine your skills but also demonstrate your readiness for this specialized role.
Which tools should I learn first for threat hunting?
Threat hunting starts with the right tools. Platforms like Microsoft Azure Sentinel and IBM Security QRadar are essential for managing and analyzing security information and events. To bolster your efforts, threat intelligence tools such as Pulsedive and AlienVault OTX can provide valuable insights into emerging threats.
Additionally, understanding query languages like KQL (Kusto Query Language) is crucial. Pairing this knowledge with behavioral analytics will help you monitor network traffic, dive into logs, and investigate any suspicious activity with greater precision.
Do I need an active clearance to get hired?
Yes, most cyber threat hunter positions in the cleared cybersecurity field require an active security clearance. Employers generally prefer candidates who already hold a current clearance to fulfill the unique requirements of these roles.
