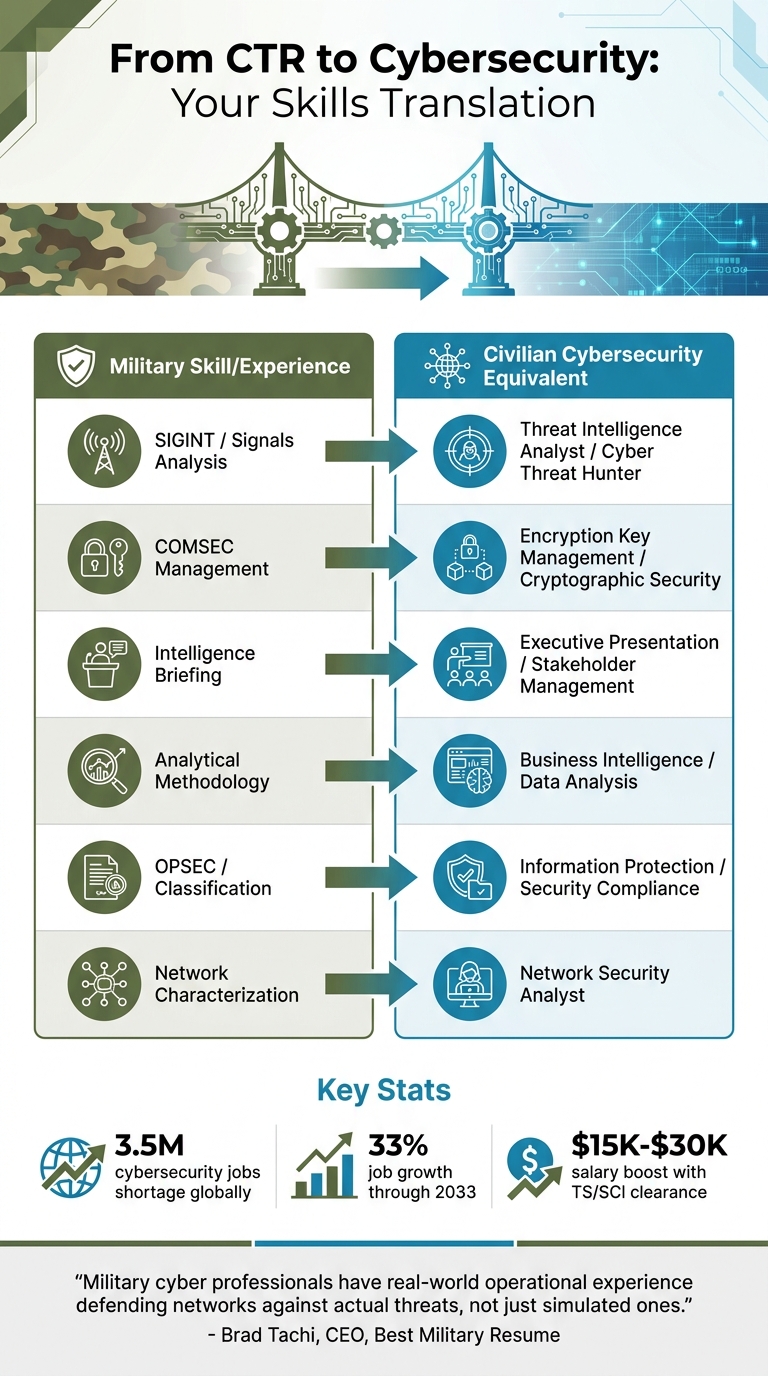
Navy CTR veterans are uniquely positioned to transition into high-demand cybersecurity roles. With expertise in signals intelligence (SIGINT), classified network operations, and analytical methods, you already have the skills for jobs like Threat Intelligence Analyst, SOC Analyst, and Cyber Threat Hunter. Here’s why this career path works for you:
- Skills Match: SIGINT, COMSEC management, and intelligence briefing align with cybersecurity tasks like threat analysis, encryption key management, and compliance.
- High Demand: There’s a global shortage of 3.5 million cybersecurity professionals, with roles like Information Security Analyst growing by 33% through 2033.
- Clearance Advantage: A TS/SCI clearance can add $15,000–$30,000 to your salary and make you a top candidate for cleared roles.
- Certifications to Start: CompTIA Security+ (around $400) meets DoD 8140/8570 requirements and is a baseline for many positions. Follow up with CySA+, CEH, or CISSP for advanced roles.
Use programs like SkillBridge, DoD COOL, and VET TEC to fund certifications and gain civilian experience before separating. Tailor your resume to highlight your clearance and translate military terms into civilian language to stand out. With the right steps, you can secure a cybersecurity job paying $55,000–$70,000 to start, with potential to earn $130,000–$200,000+ as you gain experience.
Veteran to 100K in Cybersecurity – Your Roadmap to Success
sbb-itb-bf7aa6b
CTR Role: Building Blocks for Cybersecurity
CTR Military Skills to Cybersecurity Career Translation Guide
What CTRs Do: Core Responsibilities
As a Navy Cryptologic Technician (Collection) (CTR), your primary focus is on signals intelligence (SIGINT) – intercepting and analyzing communications to uncover patterns, understand networks, and generate intelligence reports that guide operational decisions. But it doesn’t stop there. You also integrate data from multiple sources to identify anomalies, investigate threat actors, and examine attack methods. This process culminates in delivering concise, actionable briefings to leadership. These responsibilities align closely with roles like Threat Intelligence Analyst and SOC Analyst, forming a solid base for the cybersecurity expertise detailed below.
Skills You Gain as a CTR
The technical foundation you develop as a CTR translates seamlessly into critical cybersecurity skills. Your expertise in network characterization and signals collection directly applies to network security analysis and threat hunting in the civilian world. You’re trained to detect network anomalies, understand adversary tactics, and identify vulnerabilities – abilities that are essential for protecting systems from modern cyber threats.
But it’s not just about technical know-how. Your ability to transform raw data into actionable intelligence is a skill that sets you apart. The Navy’s rigorous training sharpens your efficiency, precision, and methodical problem-solving. Additionally, your experience with cryptographic security and enforcing strict information protection policies gives you an edge in roles requiring a deep understanding of data security and compliance standards. Below is a breakdown of how your military skills map to civilian cybersecurity roles:
| Military Skill/Experience | Civilian Cybersecurity Equivalent |
|---|---|
| SIGINT / Signals Analysis | Threat Intelligence Analyst / Cyber Threat Hunter |
| COMSEC Management | Encryption Key Management / Cryptographic Security |
| Intelligence Briefing | Executive Presentation / Stakeholder Management |
| Analytical Methodology | Business Intelligence / Data Analysis |
| OPSEC / Classification | Information Protection / Security Compliance |
| Network Characterization | Network Security Analyst |
These transferable skills make you a strong candidate for high-demand cybersecurity roles, particularly in cleared environments.
"Military cyber professionals have something that most civilian cybersecurity candidates don’t: real-world operational experience defending networks against actual threats, not just simulated ones."
– Brad Tachi, CEO, Best Military Resume
How CTR Skills Apply to Cybersecurity Jobs
Skills That Transfer to Cybersecurity
Your experience as a Cryptologic Technician (CTR) directly connects to roles like Threat Intelligence Analyst and SOC Analyst, thanks to your expertise in researching adversaries, analyzing attack patterns, and producing actionable intelligence [3].
For SOC Analyst positions, your background in vigilant monitoring is a natural fit. You’ve already honed skills like analyzing alerts, following escalation procedures, and maintaining focus under pressure – key elements of being the "first line of defense" in Security Operations Centers [1][3]. Additionally, your ability to make critical decisions during high-stakes situations, such as system breaches, sets you apart in operational environments.
Your experience managing classified systems also aligns with risk management and compliance roles. Tasks like enforcing information security policies and handling sensitive data parallel civilian responsibilities tied to frameworks like NIST 800-53. When crafting your resume, translate military-specific terms into civilian equivalents: for example, use "encryption key management" instead of "COMSEC" and "vulnerability scanning" instead of "ACAS" to ensure Applicant Tracking Systems recognize your qualifications [1].
"If you have a CompTIA Security+, a TS/SCI clearance, and two years of hands-on network experience from your military service, you’re already more qualified than half the applicants with a bachelor’s degree and zero practical experience." – Brad Tachi, Best Military Resume [1]
These technical skills, combined with your active clearance, make you a highly competitive candidate.
Your Security Clearance Gives You an Edge
Beyond your transferable skills, your active TS/SCI clearance gives you a distinct advantage. This clearance not only increases your earning potential – adding $15,000 to $30,000 to your salary – but also allows you to start working immediately. Employers save $5,000 to $15,000 in processing costs and avoid delays associated with reinvestigation [1][2][4][5].
The demand for cleared professionals creates a highly favorable job market for you. Many high-paying roles in defense, intelligence, and federal contracting are restricted to individuals with active clearances, significantly reducing civilian competition [2].
Timing matters. Begin your job search at least six months before leaving the service to ensure a seamless transition of your clearance to a new employer [6]. Even if the first role isn’t ideal, taking a job that requires a clearance keeps it active and preserves its value [1].
"A candidate with an active clearance gets an interview. A candidate who needs a reinvestigation gets a waitlist." – Brad Tachi, CEO, Best Military Resume [5]
Make your clearance a focal point on your resume. Place it prominently in your header (e.g., "TS/SCI with CI Poly") alongside your contact information. This ensures you pass initial recruiter screenings and automated systems. Your clearance is a powerful asset – treat it as a cornerstone of your career transition strategy.
Certifications That Help CTRs Move to Cybersecurity
Best Certifications for Cleared Cyber Jobs
Start with CompTIA Security+ (around $400), which satisfies DoD 8570/8140 IAT Level II requirements. This is a must-have for many defense-related positions [4].
After earning Security+, consider CompTIA CySA+ as your next step. Also priced at around $400, this certification emphasizes skills in security analytics and threat detection – perfectly complementing a background in collection and analysis [4]. For those aiming for SOC Analyst roles, CySA+ proves your ability to handle the analytical challenges of monitoring and responding to security incidents.
For senior or management-level roles, CISSP (Certified Information Systems Security Professional) is the top credential. The exam costs between $699 and $749 and requires five years of experience across at least two security domains – experience that military service often fulfills [4]. With CISSP, professionals frequently earn median salaries above $120,000, making it a worthwhile investment for long-term career growth.
If offensive security is your goal, the Certified Ethical Hacker (CEH) is an excellent choice. Costing between $950 and $1,199, it qualifies you for roles like penetration testing, vulnerability analysis, and incident response. CEH also meets DoD 8140 requirements for CSSP Auditor and Incident Responder positions [4].
For those interested in securing cloud infrastructure, cloud security certifications like AWS Certified Security Specialty and Azure Security Engineer are valuable. These certifications prepare you for roles focused on safeguarding classified cloud environments, especially as defense agencies increasingly adopt AWS and Azure platforms.
| Certification | Cost | Best For | DoD 8570/8140 Level |
|---|---|---|---|
| Security+ | ~$400 | Entry-level baseline | IAT II |
| CySA+ | ~$400 | SOC Analyst / Threat Hunting | CSSP Analyst |
| CEH | $950–$1,199 | Penetration Testing / Incident Response | CSSP Auditor/Incident Responder |
| CISSP | $699–$749 | Management / Security Architecture | IAM III / IASAE II |
"One of our Army Signal NCOs went from E-6 to a $115K SOC analyst role in eight months. Security+ got him in the door. CySA+ got him the offer over other candidates. The clearance sealed it." – Brad Tachi, Navy Veteran & BMR Founder [4]
Military funding programs can help cover the cost of these certifications, making them more accessible.
How to Use Military Training Credits
Your military training and funding programs are powerful tools to streamline your cybersecurity transition.
Navy COOL is an essential resource while you’re still on active duty. Use it to cover exam fees and study materials, allowing you to save your GI Bill for more advanced training. Similarly, Air Force COOL provides up to $4,500 per fiscal year for certification exams, prep courses, and study resources [7].
Training from CTR "A" and "C" schools can often count toward prerequisites or CISSP experience requirements. When applying for certifications, list specific unclassified tools you’ve worked with – such as Wireshark, Splunk, or Nessus – to showcase your technical skills [4].
Post-separation, VET TEC is a great funding option. It covers the cost of cybersecurity bootcamps and provides a housing allowance without using up your GI Bill benefits. Additionally, programs like Onward to Opportunity (O2O) through Syracuse University offer free training and exam vouchers for certifications like CompTIA and AWS [4][8].
To maximize these resources, plan your certification timeline 12–18 months in advance. Completing exams before starting terminal leave ensures you can meet active-duty funding requirements [7].
"The military taught you the skill. COOL gives you the credential that proves it to civilian employers. Do not separate without getting that paperwork done." – Brad Tachi, Navy Veteran & BMR Founder [7]
These certifications, paired with military training and funding programs, set you up for success in high-demand cleared cybersecurity roles.
Finding and Landing Cleared Cybersecurity Jobs
Writing Resumes for Cleared Positions
If you have CTR expertise and an active security clearance, tailoring your resume for the cleared defense sector is essential. These strategies can help you stand out in a competitive market.
Start by placing your clearance level – like TS/SCI – right at the top of your resume, next to your name and contact details. Recruiters often filter applicants by clearance level first.
"I’ve talked to defense contractor recruiters who told me they literally search their ATS for ‘TS/SCI’ as their first filter before looking at anything else." – Brad Tachi, CEO and Founder, Best Military Resume
Translate military terms into civilian-friendly language and include unclassified tools to optimize your resume for keyword searches. For example, replace "COMSEC" with "cryptographic security" or "ACAS" with "vulnerability scanning using Nessus/Tenable." Highlight tools like Palantir, DCGS-A, Splunk, and Wireshark to make your expertise clear.
When describing your experience, focus on measurable achievements without revealing classified information. For instance, you could say, "Analyzed 200+ intelligence reports monthly" or "Managed collection requirements across a large-scale network." Use the STAR method (Situation, Task, Action, Result) to craft compelling accomplishment statements instead of listing duties. Keep your resume concise – ideally one or two pages – and tailor it for each job to ensure it passes Applicant Tracking Systems.
Avoid including classified project names, sensitive locations, or budget details. Your active clearance alone is a major advantage in the cleared job market, so make sure it’s prominently featured.
Once your resume is polished and emphasizes your military-translated skills and clearance, the next step is to focus on targeted job platforms and networking opportunities.
Where and How to Search for Defense Sector Jobs
With a well-crafted resume and your clearance highlighted, it’s time to focus on the job search. Specialized platforms and networking are key in the cleared community.
Use job boards designed specifically for cleared professionals. General job sites often don’t filter for clearance requirements, which means your application could get lost. Platforms like Cleared Cyber Security Jobs, a veteran-founded job board, connect cleared cybersecurity experts directly with employers, ensuring you find roles tailored to your qualifications.
Networking is just as important. Many careers in the defense sector progress through connections and reputation. Attend cleared job fairs hosted by platforms like Cleared Cyber Security Jobs, where you can meet recruiters from leading defense contractors like Booz Allen Hamilton, SAIC, Leidos, Northrop Grumman, and Raytheon.
Make sure your clearance status is visible on all profiles and applications. Clearly indicate if your clearance is Active, Inactive, or Eligible and include polygraph status if applicable. This information is critical for recruiters. Additionally, use MOS translators to find civilian equivalents for your CTR background, such as Threat Intelligence Analyst or SOC Analyst.
If you’re still on active duty, consider applying for SkillBridge internships with defense contractors. These programs allow you to gain civilian experience while maintaining your clearance, often leading to direct job offers after separation. Start your job search 12 to 18 months before leaving the military to maximize opportunities and ensure your clearance remains active.
Military Programs That Support Your Transition
SkillBridge, GI Bill, and DoD COOL Programs
If you’re transitioning to a cleared cybersecurity career, leveraging military funding and training programs can make the process smoother. These programs not only cover your training costs but also help you strategically preserve your benefits for future use.
DoD COOL (Credentialing Opportunities On-Line) is a great resource for funding industry certifications while you’re still on active duty. For example, Navy COOL supports credentials tied to your rating, such as Security⁺, CEH, and CISSP, while Air Force COOL provides up to $4,500 per fiscal year for certifications [7]. It’s smart to use COOL before separating from service, so you can save your GI Bill for larger educational goals, like a degree.
"The military taught you the skill. COOL gives you the credential that proves it to civilian employers. Do not separate without getting that paperwork done." – Brad Tachi, Navy Veteran & BMR Founder [7]
DoD SkillBridge opens doors to civilian internships or apprenticeships during your final 180 days of service – all while you continue to receive full military pay and benefits [9][12]. Surprisingly, only about 10–11% of eligible service members take advantage of this program, often because they don’t know about it [12]. Programs like NPower’s 10-week cybersecurity bootcamp, which boasts a 97% graduation rate, offer industry-recognized credentials and are worth exploring [10][11]. Early planning is crucial to secure SkillBridge approval.
VET TEC, a VA initiative, covers tuition for cybersecurity bootcamps and provides a housing allowance without tapping into your GI Bill benefits [4]. Similarly, Army Credentialing Assistance (CA) offers up to $4,000 per fiscal year for certifications [12]. Another option, Onward to Opportunity (O2O) from Syracuse University’s IVMF, provides free certification training and exam vouchers for certifications like CompTIA, Cisco, and AWS [4][12].
Timing is everything. Apply for COOL funding and complete your exams while still on active duty, as access to COOL typically ends once your terminal leave begins [7]. You can also combine programs strategically. For instance, use Tuition Assistance for a prep course and COOL to cover the exam fee [7].
Once you’ve secured funding, focus on training programs that emphasize hands-on experience and align with DoD requirements. This will help you translate your military expertise into skills that are in demand in the civilian job market.
Picking the Right Training Programs
With military funding in hand, it’s time to choose training providers that meet DoD 8140 standards and offer certifications valued by cleared employers.
For certifications like CompTIA Security⁺ or CySA⁺, look for programs that include hands-on labs and practice exams, rather than just video lectures. Security⁺, which costs around $400, is often the baseline requirement for DoD cybersecurity roles [4][1]. Advanced certifications like CISSP ($749) and CEH (approximately $1,199) can significantly boost your earning potential. If penetration testing is your goal, the OSCP exam, priced at about $1,599, is highly respected [4][2].
When exploring SkillBridge opportunities, prioritize providers with strong post-service employment rates – DoD guidelines recommend at least 75% [13]. The official DoD SkillBridge portal (skillbridge.osd.mil) is a reliable place to find approved partners and apply directly.
Many defense contractors actively participate in SkillBridge programs and value the expertise of CTRs for roles in threat analysis and security operations.
Be cautious of programs that promise quick results but lack sufficient instructor-led training. For example, ACT Now Education CERT2SUCCESS offers three weeks of guided training for IT and cybersecurity certifications [12]. Additionally, the USO Transition Program offers one-on-one career coaching and free certifications through platforms like Coursera and Skillsoft [12].
Once you’ve completed your training, update your military records and add your new certifications to your resume promptly [7]. With over 500,000 open cybersecurity jobs in the U.S. and information security analyst roles expected to grow by 33% through 2033, the demand for cleared professionals with the right credentials is strong [10][11][1].
Conclusion
Your CTR background equips you with hands-on network defense experience, intelligence tradecraft, and a current TS/SCI clearance – advantages that can translate into a salary boost of $15,000–$30,000 [1]. With the cybersecurity industry expected to add approximately 17,300 new positions annually through 2033, you already possess expertise that many civilian candidates take years to acquire [1]. This positions you perfectly to build on your skills, earn certifications, and create a standout resume.
Start by obtaining the CompTIA Security+ certification, which costs around $400 and satisfies DoD 8140 requirements. If you’re still on active duty, consider using DoD COOL funding to cover costs. Afterward, pursue certifications such as CySA+ or CEH, depending on your career goals. Keep in mind that your clearance remains active for 24 months post-separation, so securing a cleared position within that timeframe is critical [1].
When crafting your resume, ensure military terminology is translated into civilian-friendly language. For example, replace "COMSEC custodian" with "encryption key management" and quantify your accomplishments, such as "defended a 15,000-node enterprise network" [1][2]. Your watch-standing experience in a Combat Information Center aligns well with 24/7 SOC analyst roles.
Focus on employers like Booz Allen Hamilton, Leidos, Raytheon, or federal GS-2210 roles on USAJOBS. Your active clearance and military expertise provide a significant advantage. If you’re still on active duty, leverage programs like SkillBridge during your final 180 days to gain civilian experience while maintaining full pay and benefits. As Brad Tachi, Founder of Best Military Resume, emphasizes:
"Military cyber professionals have something that most civilian cybersecurity candidates don’t: real-world operational experience defending networks against actual threats, not just simulated ones." – Brad Tachi [2]
Your CTR experience opens doors to roles such as Threat Intelligence Analyst, Cyber Threat Hunter, or SOC Analyst, with starting salaries between $55,000–$70,000. With experience and advanced certifications, earnings can climb to $130,000–$200,000+ [3]. By following these steps, you can confidently transition from military service to a thriving career in cybersecurity. The demand is high, and you’ve already laid the groundwork for success.
FAQs
How do I keep my TS/SCI clearance active after separating?
Your TS/SCI clearance stays inactive but can be reinstated for up to 24 months after leaving your position. To reactivate it, you’ll need to find a job or contract with an employer willing to sponsor your clearance within this timeframe. If no sponsorship happens within those 24 months, your clearance will expire, and you’ll have to undergo a new investigation – a process that typically takes 6 to 18 months.
Which cybersecurity certification should I get first as a CTR?
The Security+ certification is an excellent starting point for CTRs making the leap into cybersecurity. As one of the most recognized certifications for entry-level positions, it helps veterans translate their military skills into the civilian workforce. Many who pursue Security+ find it instrumental in landing roles with salaries between $55,000 and $75,000, often within six months of leaving military service. Additionally, it lays a solid foundation for pursuing more advanced certifications and career opportunities in cybersecurity.
How do I write a resume with CTR experience without sharing classified details?
When presenting your skills, accomplishments, and security clearance, it’s crucial to strike a balance between showcasing your expertise and maintaining confidentiality. Use civilian-friendly terms to describe transferable skills like signals intelligence, data analysis, or technical troubleshooting. For example, instead of mentioning classified programs, you could say, "Analyzed and interpreted large datasets to identify trends and actionable insights, improving operational efficiency by 20%."
Quantify your achievements wherever possible to demonstrate impact. For instance, highlight outcomes like, "Streamlined workflow processes, reducing analysis time by 30%", or "Collaborated with cross-functional teams to enhance data accuracy by 15%."
Avoid including sensitive details such as specific program names or polygraph results. If you’re uncertain about what can be disclosed, consult your Facility Security Officer (FSO) to ensure compliance with security protocols. This careful approach allows you to effectively communicate your CTR experience while safeguarding classified information.
