Cleared red team jobs involve simulating sophisticated cyberattacks to identify vulnerabilities in sensitive, classified environments. These roles are critical for government agencies and defense contractors to protect against advanced threats. Here’s what you need to know:
- Skills Required: Expertise in Windows, Linux, macOS, network protocols, scripting (Python, PowerShell), penetration testing, and adversary emulation.
- Soft Skills: Clear communication, teamwork, and compliance with strict security clearance guidelines.
- Certifications: OSCP, GRTP, CRTP, GPEN, and CISSP are highly valued.
- Security Clearance: U.S. citizenship is mandatory, and clearances (Secret, Top Secret, TS/SCI) require thorough background checks.
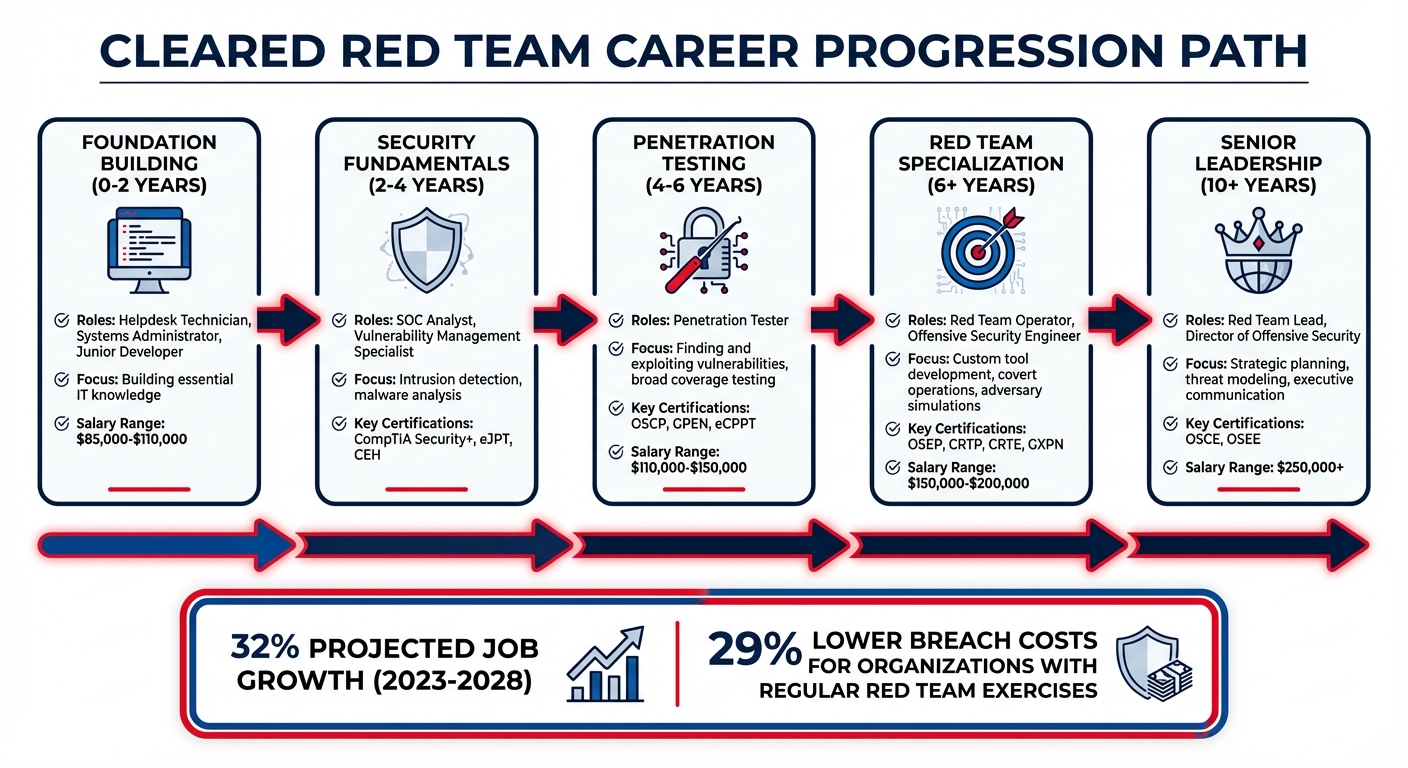
- Career Path: Typically spans 6+ years, starting in IT roles, progressing to penetration testing, and advancing to red team leadership.
- Salary Range: $85,000–$250,000+ annually, depending on experience and role.
Demand for red team professionals is growing rapidly, with a 32% projected increase between 2023 and 2028. This guide covers everything from skills and certifications to job search strategies and career progression, helping you excel in this high-stakes field.
Skills and Qualifications for Cleared Red Team Jobs
Technical Skills for Red Teaming
To succeed in red teaming, you’ll need a strong command of Windows, Linux, and macOS, along with a deep understanding of network protocols like TCP/UDP, DNS, HTTP/S, and SSH. Proficiency in programming and scripting languages such as Python, PowerShell, Bash, and C/C++ is essential for tasks like automation and developing custom exploits.
You should also be skilled in penetration testing across web, network, and cloud environments. Other critical areas include exploit development, social engineering (like phishing and physical security bypasses), and malware reverse engineering. Cloud security expertise – spanning platforms like AWS, Azure, and GCP, including container security – is increasingly important.
Adversary emulation is another cornerstone skill. This involves mimicking real-world threats using frameworks like MITRE ATT&CK to simulate how attackers operate.
Many red team professionals start in foundational IT roles such as systems administration or software engineering, which provide a solid base for transitioning to offensive security. Virtual labs and Capture The Flag (CTF) competitions are excellent ways to fast-track your skill development. Alongside these technical abilities, you’ll need to cultivate soft skills that are just as critical to your success.
Soft Skills for Success
Technical expertise alone won’t cut it in a cleared red team role – you’ll also need strong soft skills. Adopting an adversarial mindset is crucial for spotting unconventional attack routes and identifying security gaps.
Clear and effective communication is another must-have. After completing an engagement, you’ll need to translate your complex findings into concise, actionable recommendations that non-technical stakeholders can easily understand. Teamwork is just as important; collaborating with Blue Teams and Purple Teams ensures that your insights lead to meaningful security improvements.
In cleared environments, traits like sound judgment and reliability are non-negotiable. Adjudicators evaluate candidates based on the 13 Adjudicative Guidelines, which emphasize qualities such as loyalty, honesty, and operational security. Being completely transparent during the clearance process – and throughout your career – is critical. Any dishonesty, even on minor matters, can result in clearance denial.
Clearance Requirements
Cleared red team roles demand not only technical and interpersonal skills but also compliance with strict clearance requirements. Security clearance is granted after being initiated by a federal agency or contractor, usually following a conditional job offer. The process evaluates your overall suitability, taking into account factors like financial responsibility, foreign influence, and personal conduct. Keep in mind that U.S. citizenship is a mandatory requirement for all cleared positions.
The clearance process follows a three-tier system:
- Secret clearances (Tier 3): Typically processed in 60 to 150 days.
- Top Secret clearances (Tier 5): Usually take 120 to 240 days.
- TS/SCI positions with polygraph: Processing can range from 180 days to over a year. [3]
Under the Trusted Workforce 2.0 standard, fully implemented by 2026, the older e-QIP system has been replaced with eApp, a digital platform that uses logic-based questions and real-time error detection. [3] Periodic reinvestigations have also been replaced with Continuous Vetting, which monitors criminal records, credit reports, and foreign travel in real time. [3]
Adjudicators now review your online presence – including GitHub contributions, participation in gaming communities, and social media activity – to assess your judgment and operational security awareness. It’s a good idea to audit your social media privacy settings and thoroughly document any foreign contacts or financial issues on your SF-86 form. [3]
Financial problems are one of the top reasons for clearance denial. To avoid issues, check your credit reports and resolve any delinquencies. If you’ve had financial troubles in the past, providing proof of resolution – such as maintaining a consistent payment plan for 24 months – can help. [3] Additionally, remember that marijuana use remains federally illegal, and repeated use will disqualify you from obtaining clearance. [3]
sbb-itb-bf7aa6b
Certifications for Red Team Professionals
Top Red Team Certifications
The Offensive Security Certified Professional (OSCP) is widely regarded as a benchmark for penetration testers and red team professionals. It challenges candidates with a demanding 24-hour practical exam that not only tests exploitation skills but also evaluates their ability to create a detailed penetration testing report. The PEN-200 course bundle, priced at $1,749, includes 90 days of lab access and one exam attempt. On average, OSCP-certified professionals in the U.S. earn around $120,000 annually, with top earners making up to $168,000 [4].
The GIAC Red Team Professional (GRTP), introduced in January 2024, emphasizes comprehensive adversary emulation. This certification demonstrates expertise in building command-and-control infrastructure, executing Active Directory attacks, and evading modern defense mechanisms. Jean-Francois Maes, a Certified SANS Instructor, highlights its practical focus:
"With this course we provide students with a blueprint they can use to set up a realistic Red Team operation against a client environment… This course consolidates real-world practitioner expertise."
GIAC courses generally cost between $7,000 and $8,000, covering both training and the exam [4].
Other certifications, such as the Certified Red Team Professional (CRTP), concentrate on Windows and Active Directory security, while the GIAC Penetration Tester (GPEN) validates a structured approach to professional penetration testing. Starting July 12, 2025, the GPEN exam requires a passing score of 73% [5]. Many candidates find the practical exam challenging – not necessarily due to technical shortcomings but because of insufficient documentation skills. Practicing report writing during lab preparation is key [4].
Security Clearance-Related Certifications
For professionals working in high-security environments, certifications need to reflect both technical skills and clearance-specific expertise. The Certified Information Systems Security Professional (CISSP) is a globally recognized certification that focuses on security management and governance. While it leans more toward theory than hands-on skills like the OSCP, the CISSP aligns with the strategic demands of cleared environments and senior-level roles. The exam costs approximately $749 and covers critical enterprise security frameworks, including NIST, making it essential for leadership positions in government contracting [4].
Certifications such as OSCP and Certified Ethical Hacker (CEH) are also gaining recognition under DoD 8570/8140 mandates, which define baseline requirements for cybersecurity roles within the Department of Defense. This recognition makes them valuable for securing contracts in cleared roles. Additionally, many government contractors and consultancies offer full or partial tuition reimbursement for these certifications, so it’s worth checking with your employer before covering the cost yourself. For newcomers to the field, starting with foundational certifications like CompTIA Security+ is a smart move before advancing to more intensive options such as OSCP or GIAC certifications [4][1].
Finding Cleared Red Team Jobs
Using Cleared Cyber Security Jobs for Your Job Search
Landing a role in the cleared job market takes a different strategy than applying for commercial cybersecurity positions. Platforms like Cleared Cyber Security Jobs specialize in roles that require an active security clearance. To stand out, make sure your profile is fully completed and emphasizes your red team skills. Highlight specific abilities tied to red team operations – this can make a big difference in matching with the right job postings.
When searching, refine your approach with Boolean techniques. For example, use quotation marks for exact phrases like "red team" and combine similar roles with OR (e.g., "Red Team" OR "Penetration Tester" OR "Ethical Hacker"). Expand your search by including all clearance levels you’re eligible for – even if you hold a Top Secret clearance, selecting Secret can reveal additional opportunities. Use Zip Code-based searches with a mileage radius instead of relying on city names, which can sometimes be inconsistent. Regularly logging in keeps your profile active and visible to recruiters, while saving your search settings as a Job Alert ensures you’re notified about new openings. For added privacy, consider using anonymous modes or blocking specific employers from viewing your profile.
Once you’ve identified potential roles, the next step is crafting a resume tailored to the clearance job market.
Building a Clearance-Focused Resume
Your resume should immediately highlight your valid security clearance – place this detail at the top near your contact information. Follow it with a concise professional summary that showcases your red team expertise, certifications like OSCP or GPEN, and your hands-on experience with critical tools.
Focus on accomplishments rather than generic job responsibilities by using STAR-based bullet points (Situation, Task, Action, Result). For instance, instead of saying you "managed penetration testing operations", describe measurable outcomes that demonstrate your impact. Customize your technical skills section with keywords from the job description to improve your chances of passing Applicant Tracking Systems (ATS).
To maintain operational security, avoid including classified project names, specific office details, or budget figures. Keep your resume clean and concise – stick to one or two pages with a simple, text-based layout for easy electronic scanning. As Bill Branstetter from 9th Way Insignia advises, "Keep subjective self-descriptions out of your summary section. I’m looking at you, Results-Oriented Team Players." Lastly, never list your security clearance on public platforms like LinkedIn, as this could be considered a security risk by some contractors.
With your resume ready, focus on building professional connections to uncover exclusive job leads.
Networking Opportunities
Networking plays a critical role in finding cleared red team positions. Attend industry events like BSides, Black Hat, DEF CON, and RSA to meet professionals face-to-face. Many of these conferences also offer volunteer roles, which can provide direct access to organizers and keynote speakers.
Another valuable way to connect is by participating in Capture the Flag (CTF) events. These not only help you sharpen your technical skills but also allow you to meet other security professionals. As red team expert Ty Anderson puts it, "Capture the Flag events… are another good way to practice your skills in a fun community… It’s also an opportunity to network with other security professionals who may be looking for new hires."
You can also showcase your expertise by maintaining a public portfolio. Document your progress in CTF events, share HackTheBox walkthroughs, or upload security research to a GitHub repository – these efforts demonstrate both your passion and technical ability. Beyond technical activities, consider scheduling informational interviews with seasoned professionals and attending security-cleared job fairs, where you can interact directly with recruiters looking for cleared talent.
Red Team Tools and Methods in Cleared Environments
Common Red Team Tools
Operating within classified networks requires specialized tools that simulate real-world threats while maintaining strict operational security. Among these, Cobalt Strike is a go-to framework for command and control (C2) operations. Its "Beacon" implants are designed to blend seamlessly with regular network traffic, making it a favorite for both red teams and adversaries [6][7]. Beyond Cobalt Strike, alternatives like Sliver (cross-platform and open-source), Nighthawk (focused on high evasion), and Mythic (built for collaborative use) are gaining traction in cleared environments [6].
For targeting Active Directory, BloodHound and its data collector SharpHound are essential tools. They help map privilege escalation paths across intricate network structures [6]. The GhostPack suite, including tools like Rubeus and Seatbelt, is widely used for credential harvesting and system reconnaissance. Meanwhile, Impacket enables manipulation of low-level network protocols, providing red teams with significant flexibility [6]. As Bishop Fox explains:
"Effective Red Teaming is far more about methodology, experience, and strategic thinking than any particular tool – but having the right instruments certainly helps experts deliver results" [6].
Stealth is a top priority in these operations. Tools that avoid triggering suspicious processes are critical. For example, Intel 471 highlights how:
"Cobalt Strike (amongst many others) have found a clever method to bypass [security controls] by loading PowerShell directly into memory… without spawning powershell.exe" [7].
This memory-resident execution technique bypasses advanced Endpoint Detection and Response (EDR) systems often found in classified networks. Similarly, operators use "Living Off the Land Binaries" (LOLBins), such as certutil.exe, to download files, reducing the chances of triggering alerts [7]. These stealth tactics are essential for maintaining operational integrity in sensitive environments.
While tools play a pivotal role, effective red teaming also relies heavily on structured methodologies to guide operations.
Methods for Cleared Networks
In addition to specialized tools, red teams operating in classified networks follow established frameworks to ensure their efforts are both systematic and effective. One such framework, the MITRE ATT&CK framework, breaks down adversary behavior into three key components: tactical objectives (Tactics), specific actions (Techniques), and technical steps (Procedures) [9]. This framework provides a foundation for proactive defense strategies and helps red teams build actionable threat profiles using tools like the ATT&CK Navigator [9]. In cleared networks, it’s also used to verify that security patches effectively guard against known "N-Day" vulnerabilities [8].
The emphasis in these operations shifts from merely identifying vulnerabilities to adversary emulation. This involves mimicking the tactics, techniques, and procedures (TTPs) of nation-state actors relevant to the organization’s risk profile [10]. Red teams often collaborate with blue teams to evaluate how defenses respond to these simulated threats, creating scorecards to measure performance. These operations typically last between two and six weeks, with about 22% involving social engineering to test human-related vulnerabilities [9][10][11][12]. Increasingly, organizations in cleared environments are adopting "always-on" red teaming, where continuous testing helps identify risks before they can be exploited by actual adversaries [8].
Top 5 Red Team Skills for 2025 with Mike Saunders
Career Progression in Cleared Red Teaming
Cleared Red Team Career Path: Timeline from Entry to Leadership
Entry-Level to Senior Roles
Breaking into cleared red teaming takes time, with a career path that typically spans several years and involves progressing through increasingly specialized roles. It’s a journey that starts with foundational IT positions and moves toward advanced offensive security roles.
Most professionals begin in the Foundation Building phase (0–2 years), taking on roles like helpdesk technician, systems administrator, or junior developer. These positions lay the groundwork by building essential IT knowledge. From there, they move into the Security Fundamentals stage (2–4 years), working as SOC analysts or vulnerability management specialists. During this time, they develop critical skills like intrusion detection and malware analysis.
The Penetration Testing phase (around 4–6 years) is often the first step into offensive security. Here, the focus shifts from defending systems to actively finding and exploiting vulnerabilities. This stage is crucial because penetration testing emphasizes broad coverage – identifying as many vulnerabilities as possible – while red teaming is more targeted, aiming to mimic specific adversary tactics to achieve defined goals, such as data theft.
With penetration testing experience under their belt, professionals move into Red Team Specialization (6+ years), taking on roles like Red Team Operator or Offensive Security Engineer. At this level, the work becomes more sophisticated, involving custom tool development, covert operations, and advanced adversary simulations. Finally, the Senior Leadership phase (10+ years) includes positions like Red Team Lead or Director of Offensive Security. These roles demand not only technical expertise but also strategic planning, threat modeling, and the ability to communicate effectively with executives.
Salaries reflect this progression. Entry-level red team roles typically range from $85,000 to $110,000 annually, while mid-level operators earn between $110,000 and $150,000. Senior specialists can command $150,000 to $200,000, and Red Team Leads often earn over $250,000 [1]. With demand for red team professionals expected to grow by 32% between 2023 and 2028 [1], building expertise and keeping certifications up to date are key to advancing in this field.
Professional Development Strategies
Success in cleared red teaming isn’t just about technical skills; it also requires the ability to connect technical exploits to real-world business impacts. Senior roles, in particular, demand clear communication and persuasive reporting to help organizations turn red team findings into actionable strategies.
Creating a public portfolio can help you stand out in the job market. A well-organized GitHub repository showcasing your security research and projects can demonstrate your expertise. Similarly, participating in bug bounty programs is a great way to sharpen your skills while earning extra income.
Proficiency in programming languages like Python, PowerShell, and Golang is essential for automating tasks and developing custom tools. You can further hone your skills by practicing on cyber ranges like TryHackMe, HackTheBox, or SANS CyberRanges, which provide realistic environments for testing your abilities.
Certifications are another critical component of career growth. Entry-level professionals often start with credentials like CompTIA Security+, eJPT, and CEH. Intermediate-level operators pursue certifications such as OSCP, GPEN, and eCPPT, while advanced specialists aim for OSEP, CRTP, CRTE, and GXPN. Expert-level certifications like OSCE and OSEE represent the pinnacle of achievement in the field. Notably, organizations that regularly conduct red team exercises report 29% lower breach costs, highlighting the importance of staying certified [1].
Many red teamers eventually transition to roles in purple teaming or defensive positions. This shift can help mitigate burnout, a common challenge in offensive security. Purple teaming, which involves collaboration between red and blue teams, provides immediate feedback and actionable insights during simulations. Whether you choose to remain in offensive security or move into a defensive role, continuous learning and hands-on practice are the cornerstones of a successful career in cleared red teaming.
Preparing for Cleared Red Team Interviews and Assignments
Technical Interview Preparation
When preparing for a cleared red team interview, technical expertise is key. You’ll need a strong grasp of Windows internals, Active Directory (AD) attacks, and offensive .NET (C#) development. A common starting point is understanding the difference between penetration testing and red teaming. As cybersecurity expert Tim MalcomVetter emphasizes:
"If you cannot articulate the difference between a penetration test and red team, go figure that out first" [13].
Expect to review C# code, discuss leveraging Windows APIs for code execution, and explain your experience with Command and Control (C2) infrastructure – including building custom implants and redirectors. Since phishing is a common technique (given the rarity of remote code execution bugs on external networks [13]), be ready to talk about bypassing Secure Email Gateways (SEGs), handling link crawlers, and circumventing multi-factor authentication (MFA). Familiarity with the MITRE ATT&CK framework, specific Advanced Persistent Threat (APT) tactics, and the cyber kill chain is also critical. To sharpen these skills, consider building a lab using resources like RastaMouse, Adam Chester’s blog, or the "ired.team" site [14].
MalcomVetter also provides a key insight:
"A novice red teamer thinks like an attacker, but a journeyman thinks about the attacker and defender" [13].
This means you’ll need to demonstrate an understanding of Endpoint Detection and Response (EDR) evasion and Windows Filtering Platform (WFP) callout drivers. Proficiency in scripting languages like Python or PowerShell is essential, but candidates with the ability to build implants in C or C++ stand out [13].
Additionally, be prepared to discuss your security clearance status during the interview.
Handling Clearance Verification
Talking about your security clearance is a standard part of the process. Remember, you cannot apply for a clearance on your own – it must be sponsored by a federal agency or an authorized contractor after a conditional job offer [3]. Be ready to provide details about your current clearance level, the dates of your background investigation, and any potential issues related to the 13 adjudicative guidelines [15].
Clearance processing times can vary depending on the level. For roles requiring TS/SCI clearance, understand the difference between Counterintelligence (CI) polygraphs, which focus on espionage and sabotage, and Full Scope polygraphs, which delve into personal conduct and lifestyle [15].
It’s critical to be open and truthful about your background. Do not attempt to alter any information on your SF-86 form. If there are potential disqualifiers – such as financial issues or prior drug use – disclose them along with evidence of how you’ve addressed them [3]. As MalcomVetter warns:
"Your tenure will be a non-starter or short lived if your host organization perceives any form of untrustworthiness. You’re getting paid to break into companies, so your employer needs to know that you will behave responsibly" [13].
Once you’ve prepared for the interview, focus on excelling in practical assignments.
Completing Practical Assignments
Practical assignments in cleared environments require strict compliance with the Rules of Engagement (RoE). Show professionalism by adhering to these rules and following escalation protocols [2]. These assignments often involve working with a "Control Team" – a trusted group within the organization – and maintaining clear communication to ensure operational integrity [2].
Use the MITRE ATT&CK framework to guide your approach, structuring your work around the stages of the cyber kill chain: Reconnaissance, Weaponization, Delivery, Exploitation, Installation, Command and Control (C2), and Actions on Objectives [2][16]. Focus on operational security (OPSEC) and evasion techniques to simulate Advanced Persistent Threats (APTs) effectively while avoiding detection by the Blue Team [2][16]. Your final report should include clear descriptions of identified issues, severity ratings, Proof of Concept (PoC) evidence, and actionable remediation recommendations [2].
Ensure your activities align with established standards like NIST SP 800-115 (Technical Guide to Information Security Testing) and NIST SP 800-53 (Security and Privacy Controls) [2]. Always verify legal compliance before starting any task [2]. Keep in mind that some assignments may take place in a Sensitive Compartmented Information Facility (SCIF), where electronic devices are not allowed [15].
Conclusion
Breaking into cleared red team roles is no small feat – it demands years of dedication to honing technical skills and building professional credibility. On average, this journey spans over six years, often starting in foundational defensive roles like SOC Analyst before transitioning into offensive operations. But red teaming isn’t just about finding vulnerabilities; it’s about simulating real-world threats to test an organization’s people, processes, and technology – all while adhering to strict ethical standards that separate professionals from malicious actors.
The demand for skilled red teamers is immense. In the United States, there are approximately five open cybersecurity positions for every qualified candidate, and red team roles are expected to grow by 32% between 2023 and 2028. Organizations that regularly conduct red team exercises report about 29% lower breach costs, making these professionals invaluable. Salaries reflect this demand, ranging from $85,000 for entry-level roles to over $250,000 for Red Team Leads [1].
To succeed in cleared red teaming, focus on three critical areas: technical expertise, certifications, and strategic job hunting. Build a strong foundation in key areas like Windows internals, Active Directory attacks, and offensive development with tools such as Python and PowerShell. Follow a structured certification path, starting with Security+ and advancing to OSCP, CRTP, and OSEP. Use platforms like Cleared Cyber Security Jobs to identify roles that align with your clearance level. Finally, craft a resume that emphasizes your adversarial thinking skills and ability to translate technical findings into actionable business insights.
As Jayson E. Street aptly puts it: "The difference between a Red Teamer and a criminal is permission. That permission comes with tremendous responsibility." [1]
Keep this perspective front and center as you navigate your career. Dedicate time to practice labs and Capture The Flag competitions to sharpen your skills. While the road to becoming a cleared red teamer can be demanding, the intellectual challenges, career security, and financial rewards make it one of the most rewarding paths in cybersecurity.
FAQs
Can I get a security clearance without a job offer?
You can’t get a security clearance without a conditional job offer. Why? Because the process requires an employer to sponsor you for a position that needs clearance. Without a specific job offer tied to a role requiring clearance, you can’t even start the application process.
What can disqualify me from a clearance for red team work?
Security clearance disqualifiers for red team roles include several critical factors. These include not being a U.S. citizen, illegal drug use, criminal convictions resulting in over a year of imprisonment, dishonorable military discharge, mental incompetency, or serious financial problems. Each of these raises concerns about an individual’s reliability, trustworthiness, or vulnerability to coercion – key considerations for safeguarding sensitive national security information.
How do I prove red team skills without sharing classified details?
If you’re looking to highlight your red team skills, there are plenty of ways to do so publicly while keeping sensitive information secure. Here are some effective approaches:
- Earn Certifications: Certifications like the Offensive Security Certified Professional (OSCP) are highly regarded in the cybersecurity field. They demonstrate your technical knowledge and hands-on abilities.
- Create Open-Source Projects: Building and sharing tools or scripts on platforms like GitHub can help establish your expertise. Whether it’s a custom script for penetration testing or a unique automation tool, open-source contributions speak volumes about your skills.
- Participate in Capture The Flag (CTF) Competitions: Joining CTF events allows you to practice and showcase your problem-solving abilities in real-world scenarios. Plus, they’re a great way to network with other professionals.
- Contribute to Cybersecurity Communities or Blogs: Sharing insights, tutorials, or case studies on forums, blogs, or social media can help you build a reputation as a knowledgeable and active member of the cybersecurity community.
These activities not only highlight your proficiency with tools like Nmap, Metasploit, and Gophish, but they also demonstrate your commitment to the field – all without revealing any classified or sensitive information.
