Cleared malware analysts play a critical role in national security, focusing on identifying, analyzing, and mitigating malware threats targeting government systems. These positions require a security clearance (Secret, Top Secret, or TS/SCI) and technical expertise in reverse engineering, programming, and operating system internals. Salaries range from $60,751 for entry-level roles to over $195,750 for senior positions. The field is growing rapidly, with demand expected to increase by 35% by 2030, driven by rising cyber threats.
Key Takeaways:
- Education: A bachelor’s degree in Computer Science, Cybersecurity, or related fields is standard; experience can sometimes substitute for formal education.
- Skills: Proficiency in tools like IDA Pro, Ghidra, and programming languages (C, C++, Python) is essential.
- Certifications: GIAC Reverse Engineering Malware (GREM) and CISSP are highly valued.
- Clearance Process: U.S. citizenship and sponsorship by a federal agency or contractor are required; clearance levels vary by role.
- Job Market: Over 56,500 new roles are expected by 2030, with salaries reflecting the high demand for cleared professionals.
This guide outlines the steps to enter this field, from education and certifications to job search strategies, helping you build a career in malware analysis.
Education and Security Clearance Requirements
Degree Requirements and Educational Background
For malware analyst roles requiring security clearance, a Bachelor’s degree in fields like Computer Science, Computer Engineering, Information Technology, or Cybersecurity is essential. These programs provide a solid foundation in areas such as programming, operating systems, and network architecture [5].
If you’re aiming for leadership or highly specialized positions, a Master’s degree in Cybersecurity, Information Assurance, or a related discipline can give you an edge [5].
However, if you don’t have a degree, there’s still a path forward. Two years of experience in roles like System Administrator, Network Administrator, or Software Programmer can often serve as an alternative qualification [5].
In addition to academic or professional experience, obtaining the appropriate security clearance is a key requirement for these roles.
Security Clearance Levels and Eligibility
Cleared positions require one of three security clearance levels: Secret, Top Secret, or TS/SCI. Each level corresponds to the sensitivity of information you’ll handle:
- Secret clearance: Grants access to information that could cause serious damage if disclosed.
- Top Secret clearance: Covers access to information that could cause exceptionally grave harm.
- TS/SCI clearance: Requires a Single Scope Background Investigation (SSBI) along with special adjudication [4].
The need for clearance is tied to the sensitivity of the information you’ll work with, not the specific job description [4].
By 2026, the Trusted Workforce 2.0 initiative will replace periodic clearance reinvestigations with Continuous Vetting. This system monitors factors like criminal records and credit activity in real time [6]. Clearance processing times vary widely, ranging from 10–30 days for an Interim Secret clearance to over 365 days for TS/SCI with a polygraph, often due to appointment backlogs [6].
To be eligible for clearance, you must meet these requirements:
- Be a U.S. citizen.
- Secure sponsorship from a federal agency or cleared contractor, typically after receiving a conditional job offer.
The adjudication process evaluates candidates across 13 guidelines, with financial issues being the most common reason for denial [4][6]. To prepare, gather 10 years of records covering your residence, employment, and foreign contacts. Reviewing your credit report early can help you address any potential red flags [6].
| Clearance Level | Investigation Type | Average Processing Time | Vetting Frequency |
|---|---|---|---|
| Secret (Tier 3) | NACLC & Credit Investigation | 60–150 days | Continuous Vetting |
| Top Secret (Tier 5) | Single Scope Background Investigation | 120–240 days | Continuous Vetting |
| TS/SCI with Polygraph | SSBI + Special Adjudication | 180–365+ days | Continuous Vetting + Polygraph |
sbb-itb-bf7aa6b
Technical Skills and Analysis Tools
Core Technical Skills
Reverse engineering lies at the heart of malware analysis. This involves breaking down binaries to understand how they operate, using tools like IDA Pro, Ghidra, and Radare2. To excel here, you’ll need a strong command of x86/x64 and ARM assembly languages, which help you decode the low-level instructions malware relies on.
Proficiency in programming languages like C, C++, and scripting languages such as Python, Perl, or Go is equally important. These skills allow you to automate repetitive tasks and create custom tools. With the cybersecurity industry projected to hit $273.6 billion by 2028, these technical abilities are more in demand than ever [1].
A thorough understanding of operating system internals – spanning Windows, Linux, and macOS – is crucial. Knowing how processes are initiated, how memory is allocated, and how file systems operate gives you the ability to spot malware’s manipulative techniques. You’ll also need expertise in sandboxing, which involves setting up isolated environments to safely analyze malicious code without risking broader contamination.
Your analytical approach will blend static analysis (reviewing code without running it) and dynamic analysis (observing how it behaves when executed). Tools like Wireshark and Process Hacker are invaluable for dynamic analysis, while you’ll also work on developing YARA or Snort signatures to detect and mitigate threats across networks.
With these foundational skills in place, the next step is mastering the tools that support a comprehensive analysis workflow.
Software Tools and Platforms
A well-equipped malware analysis setup starts with pre-configured virtual machines like REMnux and FlareVM. REMnux is a Linux distribution packed with over 100 security tools, while FlareVM offers a Windows-based environment loaded with resources like IDA Free and x64dbg [8]. These virtual machines provide a safe space to execute and study malware.
For disassembly and debugging, tools such as IDA Pro, Ghidra, x64dbg, WinDbg, and OllyDbg are indispensable. Static analysis tools like PEStudio, BinText, and PE-bear help you inspect file structures, while dynamic analysis tools like Process Monitor, Process Explorer, and Regshot allow you to track system and registry changes during execution [8][9].
Network monitoring tools are another key part of your arsenal. Programs like Wireshark, tcpdump, and Fiddler let you observe external traffic, while tools such as FakeNet-NG and INetSim create simulated network environments for testing. Automated sandboxes, including Cuckoo Sandbox, Any.Run, and Joe Sandbox, enable you to safely analyze malware behavior. Depending on the complexity, a complete analysis can take anywhere from 5 to 15 hours, though investigating Advanced Persistent Threats (APTs) may stretch into weeks [8].
To complement your findings, threat intelligence platforms like VirusTotal, Hybrid Analysis, and MalwareBazaar provide additional detection and behavioral insights. Tools like Microsoft Defender and SIEM platforms help you craft detection rules and monitor for threats across enterprise networks.
"SOC analysts who excel at malware analysis are the last line of defense, capable of stopping attacks before they spiral out of control."
- CyberDefenders Team [9]
| Category | Common Tools | Primary Purpose |
|---|---|---|
| Reverse Engineering | Ghidra, IDA Pro, Radare2, x64dbg | Disassembling and decompiling binaries |
| Analysis Platforms | FlareVM (Windows), REMnux (Linux) | Pre-configured environments with security tools |
| Dynamic Analysis | Wireshark, Process Hacker, Procmon | Monitoring network traffic and system behavior |
| Sandboxing | Cuckoo Sandbox, Any.Run, Joe Sandbox | Automated execution in safe environments |
| Static Analysis | PEStudio, Exeinfo PE, BinText | Examining file structures without execution |
Professional Certifications
Industry-Recognized Certifications
If you’re diving into malware analysis, the GIAC Reverse Engineering Malware (GREM) certification is a must-have. It’s widely regarded as the top credential for proving your ability to reverse-engineer malicious software targeting Windows systems and web browsers. This certification focuses on areas like assembly language, memory forensics, and identifying Advanced Persistent Threats (APTs) [11][12]. To earn it, you’ll face a challenging exam with 66–75 questions over three hours, requiring a minimum score of 73% [11][13]. What sets GREM apart is its CyberLive component – a hands-on test environment where you tackle real-world tasks using actual code and virtual machines [12][13].
On the broader side of security, the Certified Information Systems Security Professional (CISSP) certification is a staple for roles in security architecture, engineering, and management [3]. While it’s not as specialized as GREM, CISSP often serves as a prerequisite for senior-level or management positions, especially in environments requiring security clearances. Another key certification is the Certified Ethical Hacker (CEH), which introduces you to offensive techniques, giving you a solid understanding of the tools and methods attackers use [3].
For those aiming to work in Department of Defense (DoD) or government contracting roles, certifications like GREM, CISSP, and CEH are essential because they comply with DoD 8570/8140 requirements.
However, these credentials come with a financial commitment. The GREM exam alone costs about $1,299, and if you include the recommended SANS FOR610 training course, the total investment can climb to around $7,000 [12]. Practice exams, priced at approximately $399 each, add to the expense [12]. That said, the payoff is substantial – GREM-certified professionals in the U.S. earn an average salary of $124,000 annually, significantly higher than the $86,474 average for general malware analysts [12][3].
These certifications not only validate your skills but also position you for faster career advancement.
How Certifications Advance Your Career
Certifications do more than just verify your skills – they serve as a badge of credibility, boosting your career prospects and professional growth. They offer tangible proof of your technical expertise, which is especially critical for cleared roles. Hands-on components, like GREM’s CyberLive, ensure you’re prepared to handle real-world challenges [12][13].
Specialized certifications can set you apart from general security professionals. While broad credentials like CISSP can lead to management opportunities, niche certifications such as GREM make you highly desirable for roles in threat hunting and APT detection. This level of expertise can translate into higher salaries, with top malware analysts earning over $150,000 annually and some specialized positions offering up to $198,160 [12].
Staying certified is just as important as earning the credential. For instance, GREM requires recertification every four years, which involves earning 36 Continuing Professional Education (CPE) credits [12]. Letting certifications lapse could jeopardize your eligibility for certain roles, so maintaining them is crucial. Employers value certified professionals for their proven ability to protect critical infrastructure and secure classified systems.
| Certification | Focus Area | Average Salary Impact | DoD 8570/8140 Approved |
|---|---|---|---|
| GREM | Reverse Engineering & APT Analysis | $124,000/year [12] | Yes [11] |
| CISSP | Security Architecture & Management | Required for senior roles [3] | Yes [11] |
| CEH | Offensive Tactics & Attack Vectors | Foundation for advancement [3] | Yes [11] |
These certifications equip cleared malware analysts with the expertise needed to excel in high-stakes national security roles.
What is a Malware Analyst and How do you get a Junior Malware Analyst Role | TJ Nelson Interview
Job Duties and Career Growth
Cleared Malware Analyst Career Progression: Salary, Experience & Clearance Levels
Daily Work Responsibilities
As a cleared malware analyst, your day kicks off with incident response and triage. Using automated tools, you quickly evaluate suspicious files to identify which ones need further scrutiny. This initial step is critical because thousands of new malware samples surface daily, and your ability to separate false alarms from real threats keeps systems secure.
When a legitimate threat is flagged, you dive into both static and dynamic analysis. Static analysis involves examining file properties, while dynamic analysis uses isolated sandboxes to observe how the malware behaves in action. For particularly complex threats, you take it a step further with reverse engineering, employing tools like WinDbg, OllyDbg, and IDA Pro to uncover hidden functions and encryption methods.
After completing your analysis, you document your findings, create detection signatures, and collaborate with response teams. This job requires not only technical accuracy but also the ability to explain intricate details to people who may not have a technical background. These responsibilities lay a solid foundation for advancing in the field of malware analysis.
Career Advancement Paths
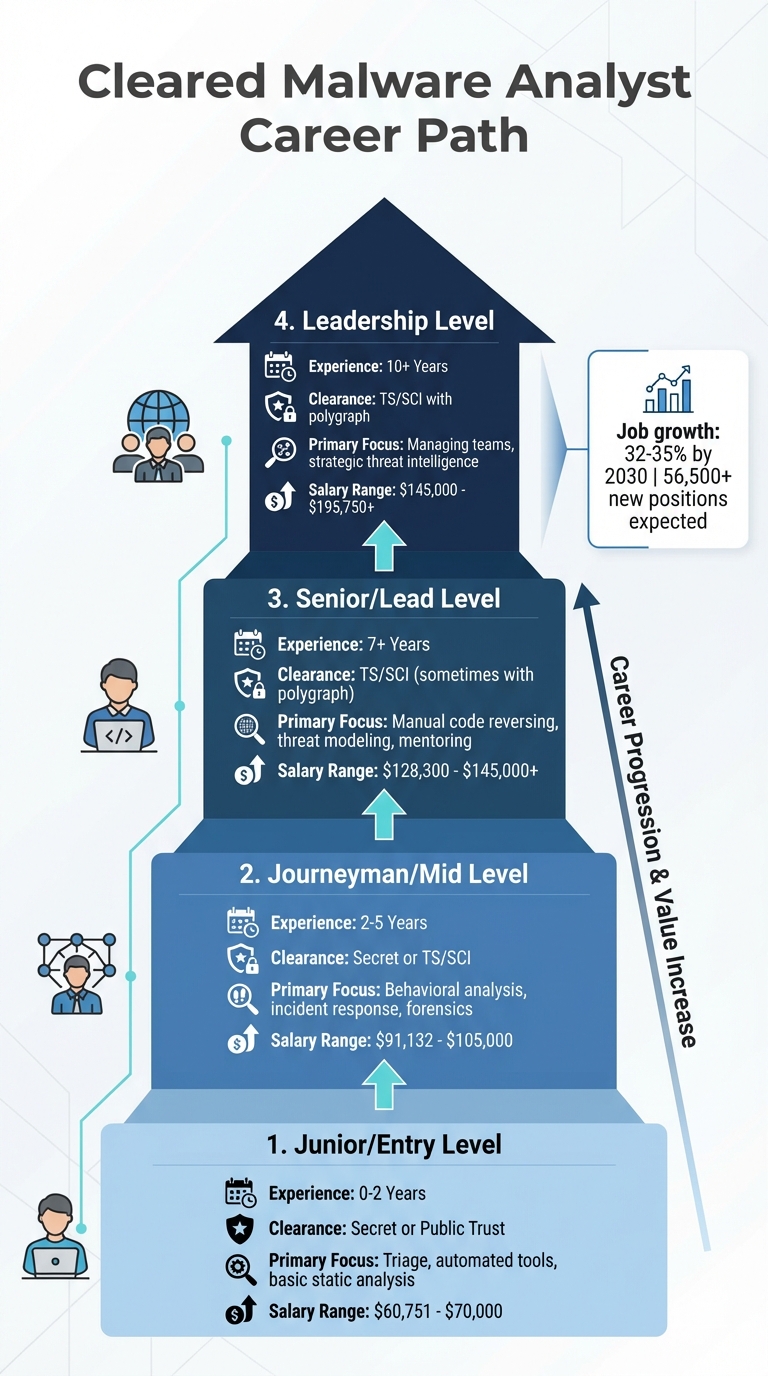
The journey to career growth in malware analysis builds on your technical skills and security clearance levels. At the entry level (0–2 years of experience), you’ll focus on triage, automated tools, and basic static analysis. Most entry-level roles require a Secret or Public Trust clearance. After gaining 2–5 years of experience, you can move into mid-level positions, where responsibilities expand to include behavioral analysis, incident response, and forensics. These roles often require a Secret or TS/SCI clearance.
Senior roles, typically achieved after 7+ years of experience, demand expertise in low-level assembly languages like x86/x64 and ARM. You’ll tackle advanced tasks such as identifying and mitigating zero-day malware, leading investigations, mentoring junior analysts, and even developing custom detection tools. These positions usually require a TS/SCI clearance, sometimes with a polygraph. Strong communication and leadership skills are essential for standing out at this level.
| Career Level | Typical Experience | Primary Focus | Annual Salary Range |
|---|---|---|---|
| Junior / Entry | 0–2 Years | Triage, automated tools, basic static analysis | $60,751 – $70,000 |
| Journeyman / Mid | 2–5 Years | Behavioral analysis, incident response, forensics | $91,132 – $105,000 |
| Senior / Lead | 7+ Years | Manual code reversing, threat modeling, mentoring | $128,300 – $145,000+ |
| Leadership | 10+ Years | Managing teams, strategic threat intelligence | $145,000 – $195,750+ |
The demand for malware analysts is on the rise. According to the U.S. Bureau of Labor Statistics, information security analyst roles are expected to grow by 32% from 2022 to 2032 [7]. Globally, malware analysis positions have seen about 22% annual growth [2]. Skills in programming can further enhance your ability to dissect and understand malicious code. Pursuing certifications, contributing to open-source projects like MalwareBazaar, and gaining hands-on experience with tools like REMnux or FLARE VM can accelerate your path to leadership roles in this thriving field.
Salary Ranges and Job Market Trends
After exploring career paths and responsibilities, it’s time to dive into the compensation and market trends shaping the field of cleared malware analysis.
Salary Expectations by Experience Level
Salaries for cleared malware analysts depend on factors like experience, security clearance level, and location. For those just starting out, salaries begin around $60,751 per year, with an average of $86,474 annually[3]. Mid-level professionals typically earn between $91,132 and $145,500, while seasoned analysts working on advanced threat intelligence and zero-day malware can earn $195,750 or more[1]. Government agencies and defense contractors are known for offering competitive pay.
In regions like the Washington, D.C. metro area, Northern Virginia, and Maryland, salaries tend to be higher due to the concentration of federal agencies and contractors. Remote positions are becoming more common as well, though they often require occasional on-site work for handling classified systems. These salary figures not only highlight earning potential but also reflect the demand in these key hubs.
Current Job Market Demand
The demand for cleared malware analysts is on the rise. According to the U.S. Bureau of Labor Statistics, roles for information security analysts are expected to grow by 32% to 35% from now until 2030–2032, adding approximately 56,500 new positions[7]. This surge is fueled by the increasing complexity of cyber threats – 560,000 new malware samples are detected daily, adding to an already staggering total of over 1 billion[1].
Ransomware attacks in the U.S. saw a 74% increase between 2022 and 2023[7]. At the same time, a global shortage in cybersecurity professionals is creating opportunities for those transitioning from programming or related fields into security roles.
Looking ahead, the cybersecurity market is projected to reach $273.6 billion by 2028, growing at an annual rate of 10.56%. Government contracting remains the largest employer of cleared malware analysts, with many roles requiring TS/SCI clearances for sensitive work. Beyond government, industries like healthcare and finance are ramping up hiring as they face increasingly sophisticated attacks on private data. Meanwhile, the rise of generative AI in malicious activities is pushing analysts to continually refine their skills, emphasizing the importance of staying ahead in this evolving field.
How to Find and Land Cleared Malware Analyst Jobs
Landing a cleared malware analyst job involves a focused strategy that blends technical expertise with an active security clearance.
Job Search Methods for Cleared Positions
Start by leveraging specialized job boards that cater exclusively to cleared positions. These platforms allow you to set up daily alerts based on your clearance level, location, and technical focus. Plus, they connect you directly with hiring managers. Make sure your profile is up-to-date with your resume, certifications, and current clearance status to increase your visibility for new opportunities.
Another effective method is attending cleared job fairs, whether virtual or in-person. These events give you the chance to network with recruiters from top defense contractors and intelligence agencies. They’re a great way to showcase your technical skills and clearance credentials face-to-face, often speeding up the hiring process.
Once you have job leads, it’s time to focus on acing both technical and clearance interviews.
Preparing for Technical and Clearance Interviews
Technical interviews test your practical expertise, so be ready for detailed questions on topics like x86 assembly, C/C++, Windows API, and operating system internals[3][10]. Employers will likely ask you to explain the four key stages of malware analysis: fully-automated analysis, static properties examination, interactive behavioral analysis, and manual code reversing[14]. Structuring your answers around these stages shows your methodical approach and depth of knowledge.
"The closer you get to the top [of the analysis pyramid], the more burdensome the effort and the less common the skill set." – Lenny Zeltser, Cybersecurity Executive[14]
Expect in-depth discussions about Indicators of Compromise (IOCs), such as file-based hashes, network-based command-and-control (C2) domains, host-based registry changes, and email-based spoofed headers[15][16]. If presented with active infection scenarios, emphasize the importance of immediate isolation before moving to triage[15][16].
To stand out, prepare to walk interviewers through workflows and troubleshooting steps using industry-standard tools. Building a home lab with virtual machines and tools like REMnux can give you hands-on experience. Use your lab work to create concrete examples that demonstrate your skills and problem-solving abilities during interviews[10][14].
Conclusion
Breaking into the field of cleared malware analysis requires a mix of education, technical expertise, and certifications. A bachelor’s degree in Computer Science or Cybersecurity provides a solid starting point. From there, honing your skills with tools like IDA Pro and Ghidra, along with gaining proficiency in x86/x64 assembly and C/C++, helps set you apart in this competitive field [2]. These skills not only prepare you for advanced roles but also position you for attractive salaries. With the job market expected to grow by 35% by 2030, your expertise will remain highly sought after [1].
Certifications such as GIAC Reverse Engineering Malware (GREM) and Certified Reverse Engineering Analyst (CREA) are excellent ways to showcase your dedication and expertise. Entry-level roles in this field often start at around $70,000 annually, while senior positions can command salaries ranging from $145,000 to $195,750 [1][2].
Building practical experience is essential. Setting up a home lab allows you to practice and refine your skills. For those just starting out, gaining experience in a Security Operations Center (SOC) or in system administration can provide a strong foundation before moving into malware analysis [1][2]. Staying active in open-source communities like MalwareBazaar and contributing to platforms such as VirusTotal Intelligence can also help you stay updated on the latest threats [2].
A career as a cleared malware analyst not only offers job security but also the chance to tackle the challenges of safeguarding national security. As AI-driven cyber threats continue to emerge [1], organizations need skilled analysts to counter these evolving risks. Update your resume with relevant certifications and clearance status, and use cleared cyber security job boards to connect with potential employers.
Whether you’re signing up for a new certification, building your analysis lab, or applying for your first cleared role, every step brings you closer to joining the mission of protecting critical systems. The demand is there, the growth opportunities are clear, and with determination, you can carve out a successful path in this vital field.
FAQs
How can I get a security clearance if I don’t already have one?
To get a security clearance, you’ll need sponsorship from a qualified employer or government agency. The process involves a few key steps: completing the e-QIP questionnaire, going through a background investigation, and an adjudication phase. During adjudication, factors like your finances, criminal record, and personal conduct are carefully reviewed. It’s crucial to be honest and upfront throughout the process, as it can take months to complete, depending on the level of clearance required and the details of your background.
What should I build in a home malware-analysis lab to prepare for interviews?
To get ready for malware analysis interviews, start by creating a secure, isolated lab environment. Use virtual machines (VMs) to simulate different operating systems, and equip them with tools like FLARE-VM and REMnux. Make sure to configure network containment to block any external communication – this is crucial for safety. Taking snapshots of your VMs is also a smart move, as it lets you quickly restore your setup if needed. This approach ensures you can practice safely and effectively while preparing for your interviews.
What does a cleared malware analyst do differently than a SOC analyst?
A cleared malware analyst works on highly specialized tasks such as reverse engineering malicious software, conducting detailed malware analysis, and performing threat research. These roles often operate in environments that require security clearances, such as Secret or Top Secret levels. Analysts in these positions deal with classified information and focus on addressing nation-state-level threats.
On the other hand, SOC (Security Operations Center) analysts are primarily tasked with monitoring and responding to threats as they happen. They rely heavily on automated tools to identify and mitigate risks. Unlike cleared malware analysts, SOC analysts typically do not require the same level of security clearance. Their work is more centered on real-time threat detection and response rather than deep-dive research or analysis.
