Cleared Information System Security Officers (ISSOs) are critical for safeguarding classified systems in government and defense. They ensure sensitive data remains secure, comply with federal standards like NIST, and manage risks through the Risk Management Framework (RMF). With salaries ranging from $107,500 to over $140,000, these roles demand active security clearances, relevant degrees or experience, and certifications like CISSP or Security+.
Key Highlights:
- Role: Protect classified systems, manage security controls, and ensure compliance.
- Qualifications: U.S. citizenship, active clearance (Secret, TS/SCI), and cybersecurity expertise.
- Certifications: Security+ (entry-level), CISSP (senior roles), CAP (RMF-focused).
- Job Market: High demand with roles growing 12%; Maryland and Virginia are key hubs.
- Salary: Median range $107,500–$140,000; senior roles can exceed $200,000.
To excel, focus on certifications, continuous learning, and leveraging specialized job platforms like Cleared Cyber Security Jobs. Networking at job fairs and maintaining an updated resume with clearance details is essential for success.
Key Responsibilities of Cleared ISSOs
Core Duties of a Cleared ISSO
Cleared ISSOs oversee system security through the Risk Management Framework (RMF), covering everything from system categorization to ongoing monitoring [4]. Their first task is defining system boundaries and assigning impact levels – Low, Moderate, or High – for confidentiality, integrity, and availability, following guidelines from FIPS 199 and NIST 800-60 [4].
"The ISSO plays a pivotal role in bridging technical implementation with organizational risk management." – Babux, Information System Security Officer [4]
They customize baseline controls from NIST SP 800-53, document them in the System Security Plan (SSP), and collaborate with technical teams to validate controls. This process includes compiling the SSP, the Security Assessment Report (SAR), and the Plan of Action and Milestones (POA&M) to secure an Authorization to Operate (ATO) [4]. During assessments, ISSOs interact with assessors, provide necessary documentation, and assist in creating POA&Ms for any identified deficiencies.
Once authorization is granted, their focus shifts to continuous monitoring. This includes tracking vulnerabilities, managing patches, and conducting Security Impact Analyses for proposed system changes [1]. They also oversee Business Impact Analyses and perform annual contingency plan tests, generating After Action Reports if incidents occur [1]. These detailed processes highlight the structured approach required in cleared environments.
Cleared vs. Non-Cleared ISSO Roles
Both cleared and non-cleared ISSOs share the responsibility of managing system security, but cleared ISSOs face stricter standards due to the classified nature of the data they protect. In addition to handling PII, PHI, and FTI, cleared ISSOs must comply with federal standards like NIST SP 800-37 and protocols for High Value Assets [1]. By contrast, non-cleared ISSOs often adhere to industry frameworks such as ISO 27001 [1].
Cleared ISSOs also deal with more stringent documentation requirements. For example, they must fully document all security controls in management systems, even if those controls are inherited from another system [1]. Penetration testing is required every three years or whenever significant system changes occur. These heightened measures reflect the critical importance of safeguarding classified systems, where breaches could jeopardize national security, foreign relations, or the economy [1]. For professionals aiming to excel in this field, mastering these specialized demands is key.
sbb-itb-bf7aa6b
What Does a Government ISSO ACTUALLY Do All Day?
Qualifications and Certifications for Cleared ISSO Roles
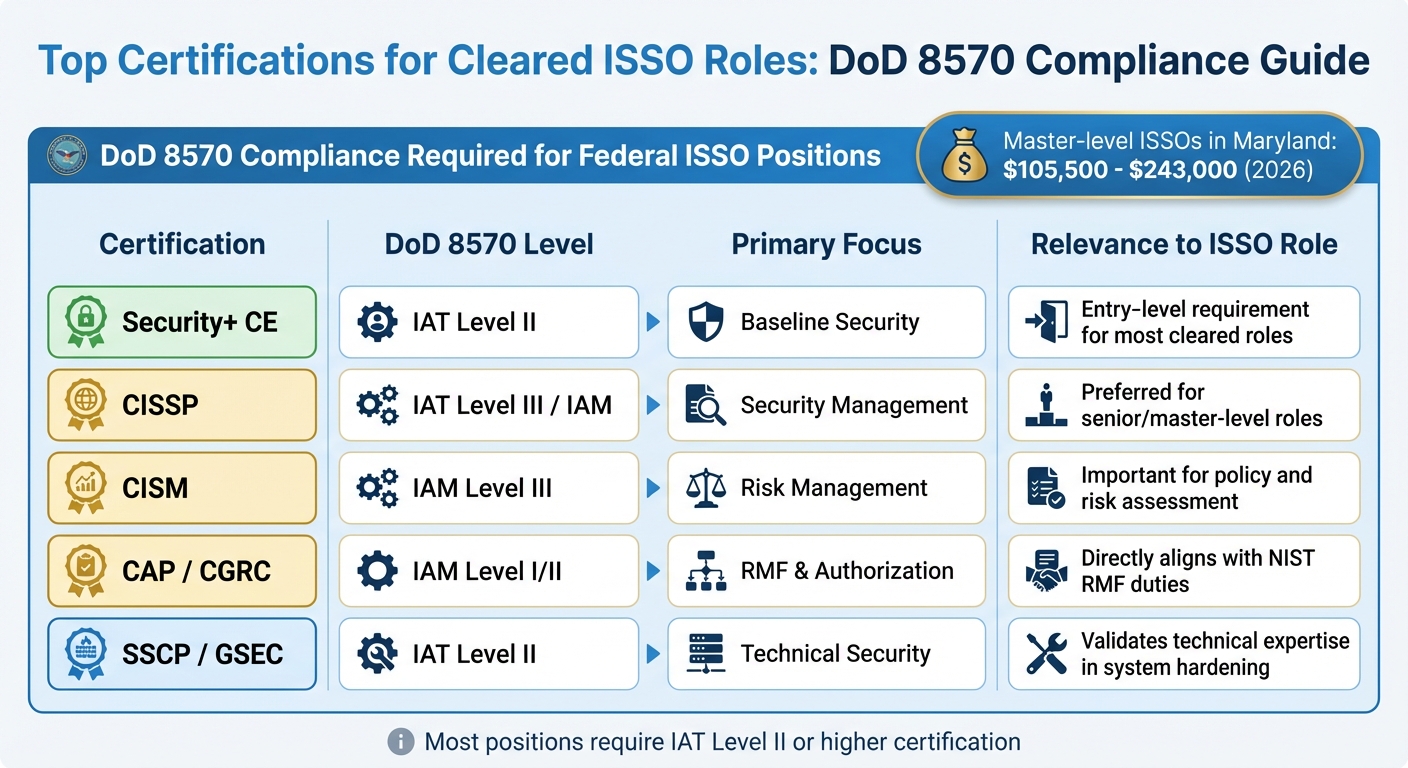
ISSO Certification Requirements and DoD 8570 Compliance Levels
Cleared ISSO positions demand a high level of expertise and strict adherence to federal compliance standards. This is reflected in the rigorous qualifications and certifications required for these roles.
Required Qualifications and Security Clearances
To qualify for a cleared ISSO role, candidates must meet strict criteria, starting with U.S. citizenship and holding an active security clearance (Secret, Top Secret, or TS/SCI with Full Scope Polygraph) [7][8]. Obtaining a clearance involves a detailed background investigation conducted by the Defense Counterintelligence and Security Agency (DCSA). This process examines areas like criminal history, financial records (including credit scores and debts), foreign contacts, and drug use [5]. Since 2025, the submission of the SF-86 form via eApp has become mandatory [5].
"A security clearance is a privilege, not a right. Mishandling classified documents can lead to criminal charges, job loss, and fines." – USFCR [5]
Most roles require a Bachelor’s degree in Computer Science, Cybersecurity, Information Technology, or a related field [2][3][8]. However, candidates without a degree may offset this with additional professional experience. For instance, four years of ISSO experience can substitute for a Bachelor’s degree [7]. Entry-level positions typically require 3–5 years of experience, while senior roles demand over 5 years, including at least 3 years working with Intelligence Community systems [2][3][8].
Candidates must also demonstrate expertise in frameworks and guidelines like RMF (Risk Management Framework), NIST SP 800-37/800-53, and STIGs (Security Technical Implementation Guides) [7][8]. As part of the Trusted Workforce 2.0 initiative, more than 3.8 million cleared personnel now undergo continuous vetting, with automated systems flagging events like foreign travel, major financial changes, or legal issues in real time [5].
Top Certifications for Cleared ISSOs
Cleared ISSO roles must comply with DoD 8570, typically at IAT Level II or higher [7][8]. Among the certifications, the CISSP (Certified Information Systems Security Professional) stands out as the most sought-after by government agencies and defense contractors. It is often listed in job postings for ISSO and ISSM roles and is especially favored for senior and master-level positions [2][6][8]. Additionally, CISM (Certified Information Security Manager) and CISA (Certified Information Systems Auditor) are highly regarded for their focus on policy development and risk assessment [2][3][6].
For those starting out, Security+ CE serves as a foundational certification that meets the IAT Level II standard required for many federal ISSO positions [8]. Specialized certifications like CAP (Certified Authorization Professional) or CGRC (Certified in Governance, Risk and Compliance) are particularly relevant for addressing NIST RMF requirements and accreditation tasks [8]. Compensation reflects the importance of these credentials, with Master-level ISSOs in Maryland earning between $105,500 and $243,000 in 2026 [8].
Here’s a breakdown of certifications and their relevance to ISSO roles:
| Certification | DoD 8570 Level | Primary Focus | Relevance to ISSO Role |
|---|---|---|---|
| Security+ CE | IAT Level II | Baseline Security | Entry-level requirement for most cleared roles |
| CISSP | IAT Level III / IAM | Security Management | Preferred for senior/master-level roles |
| CISM | IAM Level III | Risk Management | Important for policy and risk assessment |
| CAP / CGRC | IAM Level I/II | RMF & Authorization | Directly aligns with NIST RMF duties |
| SSCP / GSEC | IAT Level II | Technical Security | Validates technical expertise in system hardening |
These certifications not only validate technical skills but also demonstrate a candidate’s readiness to meet the demands of cleared ISSO roles.
Job Search Strategies for Cleared ISSO Positions
Finding cleared ISSO (Information Systems Security Officer) roles requires a focused approach, leveraging specialized platforms and intentional networking. The job market for cleared positions is distinct from civilian cybersecurity roles, with approximately 126 active ISSO openings listed on Cleared Cyber Security Jobs as of late March 2026 [10]. These roles often demand high-level clearances like Top Secret/SCI or Top Secret/SCI + Polygraph, with Maryland and Virginia being key hiring hubs [10].
Using Cleared Cyber Security Jobs Effectively
Cleared Cyber Security Jobs provides tools tailored to professionals in the cleared community. To stand out, it’s crucial to optimize your profile since recruiters typically review it before even glancing at your resume. Completing sections like "Key Skills" and "Ideal Work Locations" ensures you appear in relevant recruiter searches. Regularly logging in – whether weekly or monthly – keeps your "last active" date updated, which boosts visibility in employer searches [9].
"Employers’ searches present what’s fresh at the top of their results. So be sure to log in to your ClearedJobs.Net account weekly or monthly to update the date associated with your account." – Ashley Jones, Blog Editor and Cleared Job Search Expert, ClearedJobs.Net [9]
When searching, use Boolean logic to broaden your results. For example, searching for "Information Systems Security Officer" OR "ISSO" OR "Information Assurance Officer" helps you find jobs listed under different titles. Use quotation marks for exact phrases to refine your results. If filtering by clearance level, select all levels you’re eligible for – if you hold a Top Secret clearance, include Secret in your search to avoid missing opportunities. You can also set up Job Agents to receive email alerts for new job postings that match your criteria. For geographic searches, using a zip code with a mileage radius ensures you capture jobs listed under nearby cities [9].
Major employers hiring for cleared ISSO positions include General Dynamics – IT, Peraton, Leidos, CACI, and Amentum [10]. Additionally, the platform allows you to block specific employers from viewing your profile or set your status to "Anonymous" for added privacy [9].
These online tactics should complement your broader career-building efforts.
Networking and Professional Development
Personal connections are just as important as online tools when searching for cleared ISSO roles. Cleared job fairs – both virtual and in-person – offer direct interaction with defense contractors and federal agencies actively seeking cleared talent [9]. These events allow you to engage directly with hiring managers who are familiar with the nuances of security clearance requirements.
Your LinkedIn profile can also be a powerful tool. Clearly indicate your clearance level (within security guidelines) and emphasize your ISSO-related skills. Engage with industry leaders by joining discussions and posting thoughtful insights, positioning yourself as a knowledgeable professional. Informational interviews with experienced ISSOs or security managers can provide insider knowledge about specific agencies or contractor environments.
Attending major cybersecurity conferences like BSides, Black Hat, DEF CON, or RSA keeps you updated on industry trends while offering informal networking opportunities. For more localized connections, consider joining cybersecurity meetups through platforms like Meetup.com or LinkedIn. If you’re working toward certifications like CISSP or CISM, take advantage of the networking opportunities with instructors and peers. Additionally, contributing to open-source security projects on GitHub or participating in technical forums like Reddit’s r/netsec can help you showcase your technical skills to both peers and potential employers.
How to Excel in a Cleared ISSO Career
Resume and Interview Tips for Cleared ISSOs
To stand out as a cleared ISSO, start by tailoring your resume for recruiters and Applicant Tracking Systems (ATS). Place your security clearance prominently in the header and list it again under core competencies. Use precise, industry-recognized terms like "Active TS/SCI Clearance – Current" since recruiters often rely on these keywords to filter candidates.
"I’ve talked to defense contractor recruiters who told me they literally search their ATS for ‘TS/SCI’ as their first filter before looking at anything else. If your clearance isn’t in a searchable text field… you’re invisible." – Brad Tachi, CEO, Best Military Resume [11]
When listing accomplishments, focus on measurable results using the STAR method (Situation, Task, Action, Result). For example, highlight successful RMF authorizations or specific reductions in security risks. Avoid including classified details or sensitive identifiers – this can lead to disqualification. Additionally, align your resume with job descriptions by using relevant terminology, such as NIST 800-53, STIGs, or FedRAMP, to ensure it passes ATS filters.
During interviews, be prepared to explain your incident response process in detail. Discuss how you handle compliance tasks, including gap analyses and action plan development. When covering disaster recovery, emphasize key elements like identifying critical systems, setting Recovery-Time Objectives (RTO), and implementing backup strategies. Show your commitment to staying informed by mentioning resources you use, such as government advisories or professional organizations like ISACA or (ISC)².
A polished resume and confident interview performance will lay the groundwork for advancing your career.
Advancing Your ISSO Career
To move from mid-level ISSO roles to senior positions like ISSM, focus on earning advanced certifications and expanding your technical skill set. Certifications such as CISSP or CISM are often required for senior roles, while credentials like CISSP-ISSMP or PMP can open doors to management tracks.
Deepen your expertise in areas like cloud security, SIEM, and vulnerability assessments. Stay updated on federal regulations, including NISPOM and Intelligence Community Directives, as mastery of these frameworks is crucial in cleared environments. Resources like Cleared Cyber Security Jobs can provide tailored career tools and guidance, helping you identify opportunities to grow and stay competitive in this specialized field.
Conclusion
Building a strong career as a cleared ISSO depends on a few key pillars: maintaining active security clearances, earning respected certifications, and focusing your job search on roles that align with your qualifications. Without an active clearance, many opportunities in this field simply won’t be accessible.
Certifications like CISSP are highly regarded, showcasing your expertise and meeting the expectations of employers, especially if you have over six years of experience. Military veterans often have an edge in this field, thanks to their existing clearances and skills that seamlessly transfer to civilian roles.
Equally important is taking steps to protect and manage your clearance. This includes self-reporting any significant changes, understanding how the background investigation process works, and being prepared to navigate appeals if necessary. If your investigation was handled by the Department of Defense, you can request a copy of your background investigation records through a privacy act request to the Defense Counterintelligence and Security Agency (DCSA). These proactive measures, combined with leveraging specialized career tools, can help you stay on track.
Speaking of resources, platforms like Cleared Cyber Security Jobs are designed for professionals in the cleared community. They offer tools like resume templates, access to virtual career fairs, and direct connections with recruiters and employers who value your clearance and technical skills.
Pursuing a career as a cleared ISSO offers stability, competitive earnings, and the chance to contribute to national security. By earning the right certifications, safeguarding your clearance, and using focused job search strategies, you can set yourself up for long-term success in this specialized and impactful field.
FAQs
Do I need an active clearance to get hired as an ISSO?
Yes, most ISSO positions require an active security clearance, often at the Top Secret level. Employers usually favor candidates who already hold the required clearance, as it’s critical for managing sensitive information and fulfilling the role’s responsibilities.
Which ISSO certification should I get first – Security+ or CISSP?
If you’re beginning your journey as an Information Systems Security Officer (ISSO), Security+ is often the go-to starting point. This entry-level certification introduces fundamental security concepts, making it perfect for those new to the field or transitioning into cybersecurity.
In contrast, CISSP is a more advanced certification. It requires a minimum of five years of relevant experience, making it better suited for seasoned professionals. Starting with Security+ not only helps you grasp the basics but also lays the groundwork for tackling the CISSP later in your career.
What experience should I highlight to prove I can support RMF and ATO work?
Managing system compliance within the Risk Management Framework (RMF) involves a mix of technical expertise, meticulous documentation, and thorough inspections. Here’s what that looks like in practice:
- Preparing and Updating Accreditation Packages: Crafting and maintaining detailed accreditation documents is a key part of ensuring systems meet compliance standards. This includes gathering the necessary evidence, addressing security controls, and keeping documentation up to date.
- Conducting Security Surveys and Self-Inspections: Regular security surveys and self-inspections help identify potential weaknesses in a system. These activities ensure that vulnerabilities are caught early and addressed effectively.
- Reviewing RMF, JSIG, and AIS Documentation: Familiarity with key documentation like RMF guidelines, Joint Special Access Program Implementation Guide (JSIG), and Automated Information Systems (AIS) policies is essential. This involves scrutinizing these documents to ensure alignment with security requirements.
- Coordinating Inspections and Maintaining Security Records: Collaborating with inspection teams and maintaining accurate security records ensures a streamlined compliance process. These records serve as a critical reference point during audits and reviews.
- Identifying Vulnerabilities and Implementing Countermeasures: Spotting security gaps and applying effective countermeasures is vital for protecting systems. This process often involves a mix of technical solutions and procedural changes to minimize risks.
- Supporting System Authorization and Certification Requirements: A deep understanding of authorization and certification processes, including the steps needed to achieve an Authority to Operate (ATO), is crucial. This includes addressing all necessary security controls and ensuring systems meet the required standards.
By combining these skills and practices, compliance professionals play a pivotal role in maintaining secure and certified systems within the RMF framework.
