If you’re looking for a cybersecurity role that blends risk management, compliance, and business strategy – without heavy coding – a cleared GRC analyst job could be your ideal fit. These roles focus on aligning security frameworks with business goals, managing risks, and ensuring compliance with government standards like NIST SP 800-53 and FedRAMP. A security clearance is essential for these positions, as they often involve handling classified information in defense or government sectors.
Key Takeaways:
- What They Do: Cleared GRC analysts create security policies, conduct risk assessments, coordinate audits, and ensure compliance with federal regulations.
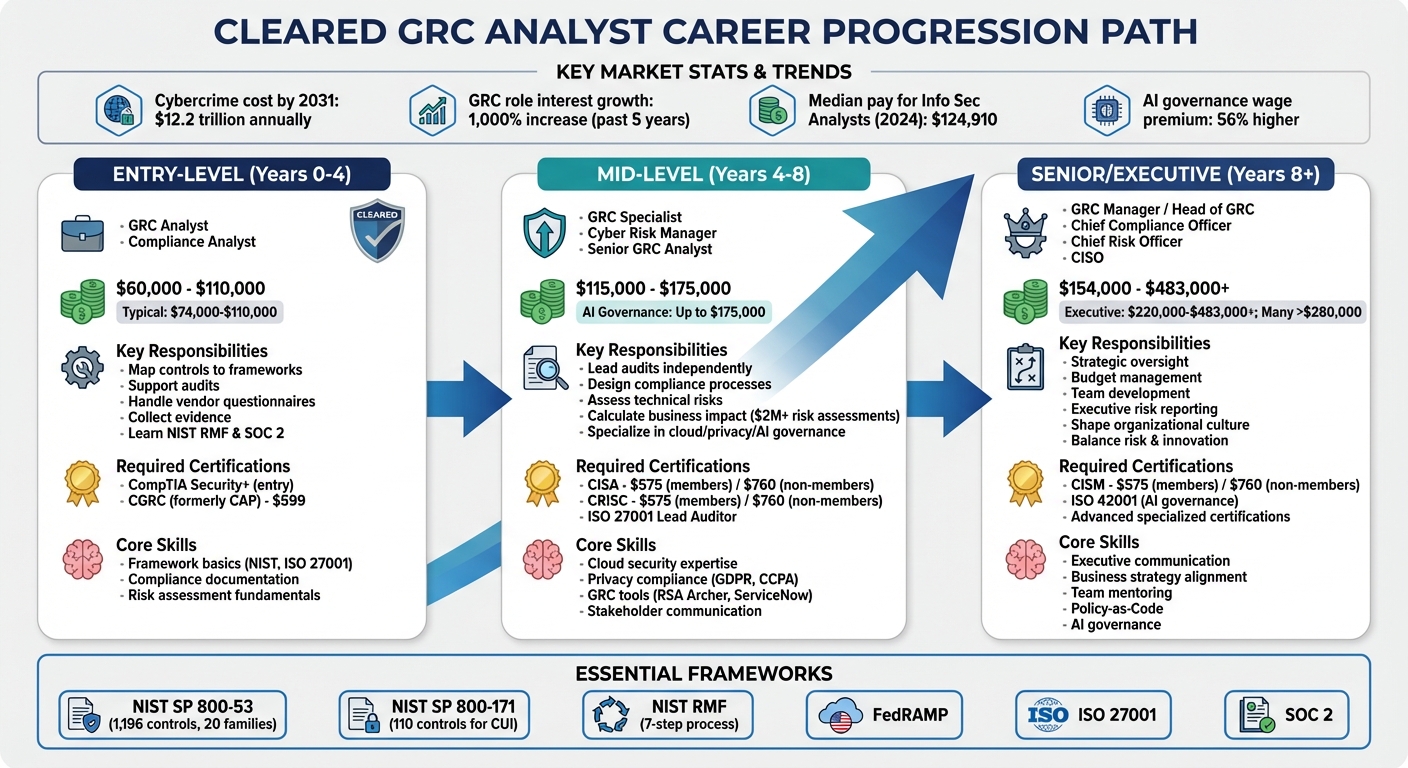
- Salary Insights: Entry-level roles start at $60,000–$80,000, while senior positions can exceed $234,000 annually.
- Required Skills: Proficiency in frameworks (e.g., NIST RMF), risk analysis, compliance tools like RSA Archer, and strong communication abilities.
- Top Certifications: CISA, CRISC, CGRC (formerly CAP), and CompTIA Security+ are highly valued.
- Career Path: Start with foundational roles, gain expertise in frameworks, and advance to leadership positions like Chief Compliance Officer or CISO.
This guide outlines everything from entry-level tips to senior leadership strategies, helping you navigate the growing demand for cleared GRC professionals.
Cleared GRC Analyst Career Path: Salaries, Skills, and Certifications by Level
What Cleared GRC Analysts Do
GRC Analyst Core Responsibilities
Cleared GRC analysts play a critical role in maintaining compliance with federal standards like NIST SP 800-53 and NIST SP 800-171. They develop and update security policies, conduct risk assessments on classified systems, and prioritize mitigation efforts using frameworks such as the NIST Risk Management Framework. Part of the job involves identifying vulnerabilities, evaluating threats, and ensuring the organization meets the stringent standards required for government contracts.
Another key responsibility is audit coordination. Analysts manage evidence collection for both internal and external audits, ensuring documentation is always audit-ready for frameworks like ISO 27001, SOC 2, and FedRAMP. The stakes are high, with tight deadlines and the potential loss of certifications adding pressure. As a senior GRC analyst with experience at Equifax and UPS put it:
"If your analysts can’t do their job, business stops." [5]
Cleared GRC analysts also assess third-party vendors and contractors to reduce supply chain risks – an especially important task in government and defense environments. They oversee Disaster Recovery (DR) and Business Continuity Plans (BCP), ensuring critical government services can quickly recover from disruptions through regular testing and validation. On top of that, they launch security awareness programs to educate cleared personnel on safeguarding sensitive information while meeting compliance requirements.
Strategic communication is another essential aspect of the role. Analysts translate complex regulatory requirements into actionable insights, bridging the gap between IT teams and executive leadership. Adam Ipsen, Lead Content Strategist at Pluralsight, aptly described this dynamic:
"GRC isn’t just a profession, it’s something that you are long before you even get the job – governance, risk, and compliance are already part of your DNA." [3]
This highlights the importance of empathy in the role. By understanding the challenges faced by both engineers and business leaders, GRC analysts foster collaboration and alignment between technical and organizational priorities.
Why Security Clearance Is Required
Security clearance is a non-negotiable requirement for GRC roles in federal agencies and defense contracting. These positions involve managing classified data and overseeing access controls for sensitive systems. The clearance ensures analysts can handle information that, if improperly disclosed, could jeopardize national security. From conducting risk assessments on classified IT infrastructure to reviewing security controls for critical systems, clearance grants the access needed to perform these tasks responsibly.
This requirement also shapes the focus of cleared GRC roles. While commercial GRC positions may center on standards like ISO 27001 or SOC 2, cleared roles are deeply rooted in federal frameworks such as NIST SP 800-53, NIST SP 800-171, and FedRAMP. Maintaining compliance with these frameworks is critical – not just for operational security but also for retaining government contracts, where even a single compliance lapse could result in termination.
sbb-itb-bf7aa6b
Required Skills and Certifications
Skills You Need for GRC Work
If you’re diving into GRC (Governance, Risk, and Compliance) work, risk management and analysis will be at the heart of what you do. You’ll need to pinpoint system vulnerabilities, assess threats, and translate cybersecurity risks into business terms. This means connecting technical issues to real-world consequences, such as lost contracts or revenue hits.
A strong grasp of frameworks is essential. Daily tasks often involve navigating standards like NIST RMF, NIST CSF, ISO/IEC 27001, and COBIT [6][10][2]. Instead of trying to memorize every detail, focus on mastering one framework – say, NIST CSF – and use it as a foundation to understand others. This lets you identify recurring themes, such as access governance and incident response, across various compliance requirements [1].
You’ll also need solid compliance and auditing skills. This includes conducting internal audits, reviewing evidence, and ensuring adherence to regulations like GDPR, HIPAA, PCI DSS, and SOX [6][2]. Familiarity with GRC software tools – such as MetricStream, RSA Archer, and Compliance.ai – can make you more attractive to employers [2].
Don’t underestimate the importance of soft skills. Explaining complex vulnerabilities to non-technical stakeholders is a critical part of the job. You’ll also need diplomacy to advocate for security changes, strong writing skills for creating clear policies, and the ability to stay calm during high-stakes audits. As Gerald Auger, PhD, from Simply Cyber explains:
"The best risk analysis means nothing if you can’t explain it to executives in terms they understand and care about." [11]
Certifications can help validate these skills and make your profile stand out in the competitive world of cleared GRC roles.
Certifications That Employers Want
When it comes to certifications, CISA (Certified Information Systems Auditor) and CRISC (Certified in Risk and Information Systems Control) are highly sought after for cleared GRC roles [4][2]. Both certifications validate your expertise in auditing and enterprise risk management. For ISACA members, these certifications cost $575; for non-members, they’re $760 [9].
For roles tied to U.S. government work, the CGRC (Certified in Governance, Risk and Compliance) – previously known as CAP – is especially relevant. Approved under DoDM 8140.03 for Department of Defense roles, it’s priced at $599 [8][9]. For those eyeing leadership positions, consider CISM (Certified Information Security Manager), which focuses on security management and strategy. Like CISA and CRISC, it costs $575 for ISACA members and $760 for non-members [4][9].
If you’re just starting out, CompTIA Security+ is a great entry-level certification to establish foundational security knowledge before moving on to more specialized GRC credentials [4][2]. For those interested in international standards, the ISO 27001 Lead Auditor certification is a valuable addition to your skillset [4].
While earning certifications, build a portfolio to showcase your skills. For example, create a mock control matrix, draft sample policies, or develop risk register entries based on public breach cases. This practical work can set you apart when applying for jobs. Interestingly, 94% of candidates who pass the GRC Professional (GRCP) exam on their first attempt credit preparatory courses for their success [7].
GRC Tools and Frameworks
Software Tools for GRC Work
A good GRC platform simplifies audits and makes gathering evidence much easier. ServiceNow GRC stands out for IT-focused environments, as it integrates seamlessly with IT Service Management (ITSM) and Security Operations (SecOps). This allows risk management to become a natural part of daily workflows. Archer is another top choice, widely recognized for its detailed risk taxonomy and flexible use cases. It’s particularly well-suited for large organizations dealing with complex operational risks.
For those leaning into automation powered by AI, MetricStream offers a platform designed to unify risk, compliance, and audit processes. Its AI-driven features help organizations gain a complete view of risks and streamline workflows. In fact, Zurich Insurance adopted MetricStream’s Connected GRC products in 2025 to modernize its risk management processes. This implementation created a centralized system for compliance and improved efficiency across its operations in 210 countries and territories [14]. The IDC MarketScape Worldwide GRC Software 2025 Vendor Assessment noted:
"MetricStream has a strong strategic direction and roadmap that will consistently deliver value to customers. The company’s AI capability will see an accelerated increase in customer productivity and outcomes, further enhancing the ROI of the platform." [14]
Federal agencies often turn to Isora GRC for meeting NIST SP 800-53 requirements, as it simplifies risk assessments and control tracking. Meanwhile, Varonis is a go-to solution for organizations managing sensitive data. It automatically classifies critical information and addresses excessive permissions, making it a key tool for safeguarding classified data.
Costs for GRC platforms can vary significantly. Small to mid-sized businesses might spend between $20,000 and $100,000 annually, while enterprise-level solutions can cost around $180,000 for a 36-month contract [15]. When choosing a platform, focus on how well it integrates with your existing tools – like AWS, Azure, Okta, SIEM, or Jira. This allows for automated, continuous evidence collection, reducing the need for manual effort during audits [15]. These tools work hand-in-hand with established compliance frameworks, streamlining risk management across your organization.
Compliance Frameworks and Standards
Compliance frameworks set the standards that GRC tools help enforce, connecting daily operations with regulatory requirements. NIST SP 800-53 is one of the most commonly used catalogs, detailing 1,196 controls across 20 families [16]. Federal agencies must comply with this standard under FISMA, and cloud providers need it for FedRAMP authorization. NIST SP 800-53 offers three baselines – Low (149 controls), Moderate (287 controls), and High (370 controls). Most federal systems operate at the Moderate level, which can take over two years to fully implement [16].
For contractors working with the Department of Defense, NIST SP 800-171 is critical. This framework, derived from NIST SP 800-53, focuses on 110 controls tailored for handling Controlled Unclassified Information (CUI) [16]. Additionally, the Risk Management Framework (RMF), outlined in NIST SP 800-37, provides a seven-step process for managing risk and achieving an Authority to Operate (ATO). The steps include Prepare, Categorize, Select, Implement, Assess, Authorize, and Monitor [16].
On a global scale, ISO 27001 is widely used for managing information security systems (ISMS). It’s particularly helpful for defense and tech contractors operating internationally [17]. Modern GRC platforms often come with pre-built control mappings between frameworks, such as linking NIST SP 800-53 to ISO 27001 or HIPAA. This approach, often called "map once, comply many", allows organizations to collect evidence once and meet multiple compliance requirements simultaneously [15]. It’s a practical way to reduce duplicate work and stay prepared for audits throughout the year.
How to Get Hired as a Cleared GRC Analyst
Writing Your Resume for GRC Positions
Your resume is your first chance to make an impression, so ensure it highlights the essentials. Place your security clearance level and key certifications – like CISA, CRISC, or CompTIA Security+ – prominently near your name or in your professional summary. Recruiters often use these details as initial filters. A chronological format works well to showcase recent experience, but if you want to emphasize specific GRC skills, consider a combination format that blends skills and work history.
Include a dedicated technical skills section tailored to the job description. Mention tools like RSA Archer, ServiceNow GRC, OneTrust, or MetricStream, as well as data tools like Excel and Power BI. Also, list relevant frameworks, as these keywords help your resume pass automated screenings.
Quantify your achievements wherever possible. Instead of saying "conducted risk assessments", specify results: for instance, "monitored 1,000+ transactions monthly" or "coordinated audits across five business units." If you have transferable experience – like auditing, IT support, or even volunteer projects – highlight it to show versatility.
Attention to detail is critical in GRC roles, so any errors in grammar or formatting could hurt your chances. Proofread your resume thoroughly before submitting it.
Consider uploading your resume to Cleared Cyber Security Jobs, where you can set up tailored job alerts based on your clearance level and GRC specialization. Customize each application by mirroring keywords from the job description, such as "governance frameworks", "gap analysis", or "vendor risk management." A concise, focused resume will set you up for the next step: interview preparation.
Preparing for GRC Interviews
With your tailored resume in hand, shift your focus to interview preparation. Strong candidates demonstrate their ability to go beyond "checkbox" compliance by showing a deep understanding of risk analysis – evaluating both the likelihood and impact of control failures.
For cleared positions, be ready to discuss frameworks commonly used in government and defense settings, such as NIST SP 800-53, NIST RMF (800-37), FedRAMP, and CMMC. Bring sanitized examples to illustrate your skills, like a risk register, a mock Plan of Action & Milestones (POA&M), or a gap analysis. Show how you turn theoretical concepts into actionable steps, and be prepared to discuss risk assessments for modern technologies like containers, serverless functions, and APIs.
"Hiring managers can separate solid candidates from great ones by focusing on how they think about risk, communicate with stakeholders, and use automation rather than just reciting frameworks."
Use the STAR method (Situation, Task, Action, Result) to answer behavioral questions, especially when explaining how you handled challenges like pushback from technical teams. Highlight your ability to automate processes by mentioning tools like ServiceNow GRC, Vanta, or Wiz for Gov, which reduce manual work. Discuss current ransomware threats or common access methods to show how threat intelligence shapes your risk assessments.
Practice explaining control mapping across multiple frameworks. For example, describe how a logging standard can meet requirements under NIST, ISO 27001, and SOC 2, streamlining compliance efforts. Be ready to distinguish between strong evidence (e.g., system-generated logs or AWS Config states) and weaker evidence (e.g., manual screenshots or self-attestation) to demonstrate your understanding of audit quality.
Building Your Professional Network
A strong network can open doors in the GRC field, especially for high-trust roles. Joining organizations like ISACA or the International Association of Privacy Professionals (IAPP) gives you access to local events, job postings, and connections with recruiters.
"GRC roles are considered high-trust, cross-functional roles. Employers expect a level of maturity, judgment, and professionalism, even at mid-junior levels."
- Abhijith Soman [12]
Participate in online communities like LinkedIn groups and Reddit forums to discover job opportunities and find mentors. If you’re currently employed, volunteer for internal or vendor audits to gain hands-on experience and increase your visibility with GRC leaders.
Showcase your certifications by displaying digital badges from platforms like Credly on your LinkedIn profile. Stay on top of industry news by following sources like Dark Reading, ISACA SmartBrief, and CPO Magazine. When networking, highlight transferable skills like policy writing, risk analysis, and stakeholder collaboration instead of focusing solely on technical tools. Personal referrals and a solid professional reputation carry significant weight in this field, so building strong connections is key.
Career Advancement in Cleared GRC
Moving from Entry-Level to Mid-Level Roles
In entry-level GRC roles, the focus is on grasping core frameworks like NIST RMF and SOC 2, mapping controls, and supporting audits. Your tasks might include handling vendor questionnaires, collecting evidence, and gaining hands-on experience with compliance processes. Salaries for these roles typically fall between $74,000 and $110,000 [13].
Once you’ve built a solid foundation, you can shift from executing tasks to taking on more strategic responsibilities. This transition to mid-level roles often happens around the four-year mark. At this stage, you’ll lead audits, design compliance processes, and assess technical risks in terms of their business impact. For example, as a GRC Specialist or Cyber Risk Manager, instead of simply documenting a cloud misconfiguration, you might calculate its potential cost as a $2 million risk, helping executives make informed decisions [20]. Salaries for mid-level positions generally range from $115,000 to $153,000, with specialized roles in areas like AI governance reaching up to $175,000 [13].
"Stop being the expert. Start building other experts."
- Harry West, grcmana [20]
To accelerate your growth, consider specializing in high-demand areas such as cloud security, privacy compliance (e.g., GDPR, CCPA), or AI governance. Certifications like CISA (for audit roles) or CRISC (for risk management) can also boost your qualifications. Building a portfolio with mock control matrices or policy samples based on real-world breach cases can showcase your expertise. Professionals skilled in AI governance tools, for instance, can earn up to a 56% higher wage premium compared to their peers [13]. Mastering these skills not only positions you for mid-level roles but also sets the stage for senior leadership opportunities.
Senior Leadership Opportunities
After gaining mid-level experience, the next step is preparing for senior management roles. Typically, after about eight years in the field, you’re ready for positions like GRC Manager or Head of GRC, with salaries ranging from $154,000 to $209,000 [13]. At this level, your responsibilities shift from hands-on tasks to strategic oversight. This includes managing budgets, developing teams, and presenting risk trends to executives [20].
For those aiming for executive roles such as CISO, Chief Risk Officer, or Chief Compliance Officer, the focus is on balancing risk and innovation. Salaries for these top-tier positions can range from $220,000 to over $483,000, with many exceeding $280,000 [13]. As of 2024, the median pay for Information Security Analysts reached $124,910, and interest in GRC leadership roles has surged by 1,000% over the past five years [1][20].
"The shift here is from ‘managing programs’ to ‘shaping culture.’ And that takes both courage and clarity."
- Harry West, grcmana [20]
Career growth in GRC isn’t always a straight path. Many professionals take lateral moves between risk, compliance, and audit roles to broaden their expertise before stepping into director-level positions [21]. To stand out, start mentoring junior analysts, identifying process inefficiencies, and volunteering for cross-functional projects. Demonstrating executive-level thinking – by framing decisions in terms of business outcomes rather than technical details – can help you transition into leadership roles [21].
Beginner to GRC Analyst Roadmap That Actually Works in 2026
Conclusion
Cleared GRC roles offer a solid and dependable career path in cybersecurity. This field has grown beyond basic compliance checks to become, as ComplyJet describes, "the brain of the operation, not just the brakes" [13]. With cybercrime expected to cost the global economy $12.2 trillion annually by 2031 and interest in GRC positions increasing by 1,000% over the last five years, the demand for professionals who can connect technical security with business resilience is at an all-time high [13].
A security clearance is more than just a credential – it’s a key to high-trust, mission-critical work involving frameworks like NIST RMF, FISMA, and FedRAMP. This exclusive access brings significant earning potential, ranging from $74,000–$110,000 for entry-level roles to over $483,000 for executive positions [13]. The clearance requirement not only reduces competition but also grants access to work that directly impacts national security.
To excel in cleared GRC, you’ll need what the industry refers to as a "T-shaped skill set." This means combining deep technical expertise in areas like cloud and AI risks with strong communication, structured writing, and quantitative risk analysis [13]. As Gerald Auger, PhD, puts it, "GRC isn’t ‘less technical’ – it’s differently technical" [19]. By 2026, mastering emerging areas like AI governance and Policy-as-Code while staying proficient in traditional compliance frameworks will be essential. This balance is central to success in these roles.
Take proactive steps to build your career by following the 70-20-10 growth model: dedicate 70% of your time to hands-on experience, such as creating mock risk registers or policies, 20% to networking in GRC communities, and 10% to earning formal certifications [13]. Certifications like CISA for auditing, CRISC for risk management, or ISO 42001 for AI governance can help you stand out. Focus on building a portfolio that highlights your practical skills and real-world applications rather than just theoretical knowledge [13].
Ultimately, cleared GRC roles reward those who can bridge the gap between technical risks and strategic business decisions. Whether you’re just starting or aiming for a leadership position, remember this insight from ComplyJet: "AI won’t replace you, but a professional using AI will. It is a Humans + AI power equation" [13]. Your ability to manage autonomous systems, communicate effectively with executives, and uphold the trust associated with your clearance will shape your success in this fast-changing field.
FAQs
Can I get a cleared GRC analyst job without prior GRC experience?
Yes, it’s possible to land a cleared GRC analyst job even if you don’t have direct GRC experience. While prior experience helps, many entry-level roles focus on foundational skills and certifications. Credentials like CompTIA Security+ or CISA can make you a strong candidate, especially if you have a background in cybersecurity or risk management. Employers often look for candidates who demonstrate a solid understanding of governance, risk, and compliance frameworks and show a strong willingness to learn.
What clearance level do most cleared GRC analyst roles require?
Most GRC analyst roles that require security clearance typically demand a Top Secret clearance. This clearance level is crucial for accessing sensitive information and adhering to the strict security protocols these positions entail.
What does the ATO process look like for a GRC analyst day-to-day?
For a GRC analyst, navigating the ATO (Authority to Operate) process means ensuring that systems meet strict security and compliance standards before they can go live. It’s a role that requires precision, collaboration, and constant vigilance.
On a daily basis, analysts focus on tasks like preparing detailed reports, maintaining documentation that’s always audit-ready, and conducting thorough risk assessments to uncover any vulnerabilities. These assessments are critical for identifying weak spots that could jeopardize a system’s security posture.
GRC analysts also work closely with cybersecurity teams to review and refine controls, ensuring they align with compliance requirements. Whenever updates are necessary – whether due to new regulations or system changes – analysts step in to revise and update the documentation accordingly. This repeated cycle of assessment and improvement is essential for keeping systems secure and fully prepared for ATO approval.
