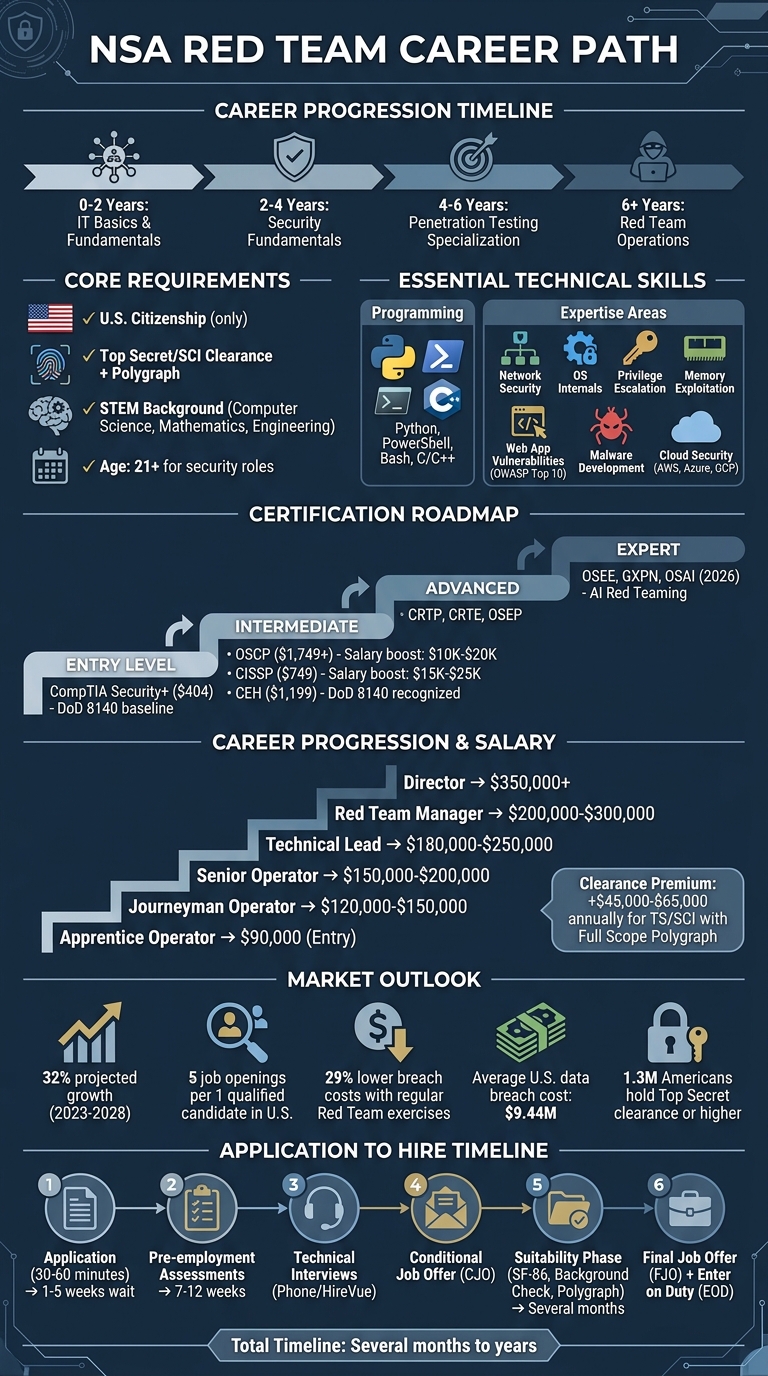
The NSA Red Team is a specialized unit focused on simulating adversary tactics to identify and exploit vulnerabilities within U.S. defense systems. This guide breaks down how to join the team, the skills and certifications required, and the benefits of pursuing a career in this field.
Key Takeaways:
- What They Do: Conduct adversarial assessments across digital, physical, and human security domains, including testing AI systems for vulnerabilities.
- Requirements: Candidates need a Top Secret / SCI clearance with a polygraph, strong technical expertise, and certifications like OSCP or CISSP.
- Salary Range: Entry-level roles start at ~$90,000, while directors can earn $350,000+.
- Career Path: Progression includes roles like Apprentice Operator, Senior Operator, and Red Team Manager, with opportunities to specialize in areas like AI or malware.
- Job Outlook: Offensive security roles are projected to grow by 32% (2023–2028), with high demand due to a shortage of qualified professionals.
To get started, focus on building technical skills (e.g., Python, PowerShell, C/C++), earning certifications, and gaining hands-on experience through labs and platforms like HackTheBox. NSA Red Team careers offer a unique chance to work on critical security challenges while advancing your expertise.
NSA Red Team Career Path: Requirements, Timeline, and Salary Progression
Requirements for Joining the NSA Red Team
Security Clearance Levels
To join the NSA Red Team, you’ll need a Top Secret / Sensitive Compartmented Information (TS/SCI) clearance, often accompanied by a polygraph test – either Counterintelligence or Full Scope [4][5]. This clearance isn’t something you can apply for on your own; it requires NSA sponsorship, which generally comes after receiving a conditional job offer [4]. The process is thorough, involving a detailed background check, a polygraph interview, and physical and psychological evaluations [4]. Additionally, only U.S. citizens are eligible [4].
Holding a TS/SCI clearance with a Full Scope Polygraph can significantly boost your earning potential, adding an annual premium of $45,000–$65,000 [5]. While about 1.3 million Americans hold Top Secret clearance or higher [5], it’s still a select group. Keep in mind, the clearance process can take several months – or even years – so patience is key. If you’re still a student or early in your career, the NSA offers pathways like its Cooperative Education Program or over 20 annual summer internships to help you work toward a cleared position [4].
Once you’ve met the clearance requirements, the next step is to focus on the technical expertise needed for red teaming.
Technical Skills and Experience
Beyond clearance, candidates must bring strong technical skills to the table. Most red teamers build their expertise through a progression: 0–2 years mastering IT basics, 2–4 years working on security fundamentals, and 4–6 years specializing in penetration testing [1]. The NSA places high value on STEM backgrounds, particularly in computer science, mathematics, and engineering [7][8].
Key technical areas include network security, operating system internals, and programming languages such as Python, PowerShell, Bash, and C/C++ [1]. You’ll also need to be well-versed in offensive security techniques like privilege escalation, memory exploitation, web application vulnerabilities (think OWASP Top 10), malware development, and cloud security for platforms like AWS, Azure, and GCP [1]. To showcase your skills, consider building a public GitHub portfolio with custom scripts or walkthroughs from platforms like HackTheBox [6].
Certifications That Help
Certifications play a big role in standing out. Start with CompTIA Security+ ($404), which meets the baseline requirements for DoD 8140 compliance [5]. For offensive roles, the Offensive Security Certified Professional (OSCP) ($1,749+) is often considered a must-have and can boost your salary by $10,000–$20,000 [5]. The Certified Information Systems Security Professional (CISSP) ($749) is another strong option, offering an annual salary increase of $15,000–$25,000 and meeting senior-level job requirements [5]. While the Certified Ethical Hacker (CEH) ($1,199) is less hands-on, it’s still recognized under DoD 8140 for offensive roles [5].
For advanced positions, certifications like Certified Red Team Professional (CRTP), Certified Red Team Expert (CRTE), and Offensive Security Experienced Penetration Tester (OSEP) can help you stand out [1]. At the expert level, consider the Offensive Security Exploitation Expert (OSEE) or GIAC Exploit Researcher and Advanced Penetration Tester (GXPN) [1]. Pair these credentials with real-world practice through platforms like TryHackMe, HackTheBox, and VulnHub to prepare for the NSA’s technical evaluations [1].
Meeting these qualifications not only strengthens your application but also sets you up for success in the challenging hiring process that lies ahead.
sbb-itb-bf7aa6b
The Application and Hiring Process
Where to Find NSA Red Team Jobs
To explore Red Team opportunities at the NSA, start by visiting their official careers portal at nsa.gov/careers. This site is regularly updated with new job postings every few days [11]. The NSA also offers a Job Exploration tool on its website to help you find roles that align with your technical skills [11]. Another resource to consider is Cleared Cyber Security Jobs, which lists positions specifically for security-cleared professionals, including Red Team roles. This can be especially helpful if you already hold a clearance.
Before applying, ensure you meet the basic eligibility criteria: you must be a U.S. citizen and meet the minimum age requirement, typically 21 years old for security roles [11]. While dual citizenship doesn’t automatically disqualify you, it could lead to additional screening [11]. Gather all necessary documents, including a driver’s license, military ID (if applicable), and academic transcripts. Completing the initial application typically takes about 30 to 60 minutes [11].
Once you’ve prepared your materials, follow the structured hiring process outlined below.
Hiring Process Steps
The NSA hiring process involves five key stages. First, you’ll submit your application through their official portal by creating a profile and answering qualification-related questions. Following this, you’ll complete pre-employment aptitude and technical assessments using NSA’s systems [10].
The interview phase includes phone screenings and technical interviews, which may be conducted through platforms like HireVue [10]. If you pass this stage, you’ll receive a conditional job offer (CJO) and move into the suitability phase. This step involves completing the SF-86 form, as well as undergoing extensive background checks, psychological evaluations, and polygraph testing through the Candidate Experience Security Portal (CESP) [9][10]. The process concludes with a Final Job Offer (FJO) and an Enter on Duty (EOD) date during the onboarding phase [10].
After submitting your application, it may take 1 to 5 weeks to hear back, though in some cases, this could extend to 2 months [11]. The transition between the testing and interview stages typically takes 7 to 12 weeks [11]. Unlike the private sector, where hiring often takes 24 to 44 days, federal intelligence jobs require more time due to the extensive suitability checks [10]. If you have urgent questions, calling 1-866-NSA-HIRE (1-866-672-4473) often yields a quicker response than email [11].
Once you’re familiar with the process, focus on crafting a standout application.
How to Strengthen Your Application
Honesty is non-negotiable – any falsehoods about your personal history or minor offenses could lead to immediate disqualification [11]. Beyond meeting the basic requirements, emphasize your technical expertise. Your resume should showcase hands-on experience with Windows Internals, Active Directory attack techniques (like Kerberoasting and Golden Tickets), PowerShell scripting, and exploiting Windows APIs [13]. Highlight proficiency in Python or PowerShell for automation, as well as C/C++ for developing custom implants [12][13].
It’s also essential to demonstrate an understanding of how Red Teaming differs from penetration testing. Cybersecurity expert Tim MalcomVetter explains:
"A novice red teamer thinks like an attacker, but a journeyman thinks about the attacker and defender" [12].
Show that you grasp the Red Team’s role as a collaborative partner for the Blue Team, focusing on improving overall security rather than merely exposing vulnerabilities. As MalcomVetter further notes:
"What they need from their red team is a genuine desire to improve security posture – not a desire to keep vulnerability information secret for a future competitive advantage" [12].
Keep in mind that your personal record matters. Avoid recreational drug use before applying, as the NSA conducts random drug screenings even after hiring [11]. Common reasons for clearance denial include significant debt, substance abuse, questionable foreign ties, or unresolved emotional or psychological issues [11]. For higher-level positions, you may also need to deliver a detailed technical presentation and defend your ideas before a panel [11].
Day-to-Day Responsibilities and Career Path
Daily Job Responsibilities
NSA Red Team professionals immerse themselves in simulating advanced threat actors to rigorously test the agency’s defenses. Their work spans digital, physical, and human security domains – pinpointing vulnerabilities in networks and web applications, evaluating physical security measures, and using social engineering tactics to uncover potential gaps. A typical day might involve reconnaissance through open-source intelligence (OSINT), navigating compromised networks via lateral movement, and escalating privileges to access sensitive systems.
Stealth is a critical aspect of their role. Red Teamers prioritize evasion techniques to bypass antivirus (AV) and Endpoint Detection and Response (EDR) systems. This demands expertise in scripting languages like Python, PowerShell, and Bash to automate attacks or create custom tools. Unlike penetration testers, who focus on identifying vulnerabilities, Red Teamers aim for mission-based objectives, covertly accessing critical data to simulate real-world attack scenarios. This approach not only highlights potential threats but also strengthens an organization’s defenses.
The ultimate goal isn’t just finding weak spots – it’s about helping Blue Teams enhance their detection and response strategies, validating security measures, and testing incident response capabilities. For organizations, the benefits are clear: those that conduct regular Red Team exercises see 29% lower breach costs compared to those that don’t. Considering the average data breach in the U.S. costs $9.44 million, this is no small advantage [1].
Beyond their day-to-day missions, NSA Red Team professionals can look forward to varied career paths that combine technical growth and leadership opportunities.
Career Growth Options
Career progression within the NSA Red Team follows a well-defined path, starting as an Apprentice Operator and advancing through roles like Journeyman Operator, Senior Operator, or Technical Lead. Ultimately, professionals can rise to positions such as Red Team Manager or Director. Depending on their interests, they can choose between a technical specialist track or a leadership-focused path.
On the technical side, specialists may dive into areas like AI Red Teaming, malware development, cloud security, or physical security testing. Senior roles often involve managing complex, multi-phase engagements, conducting architecture reviews, and exploring new attack methods. On the leadership track, roles like Assessment Technical Lead, Red Team Lead, Manager, or Director of Offensive Security involve responsibilities such as overseeing technical plans, managing budgets, and briefing top-level executives.
Advancing in this field requires hitting specific milestones. Many professionals complete programs like the DCART (Defense Cyber Adversarial Red Team) Operator Training Program, which includes courses such as the Red Team Apprentice Course (RTAC) and Red Team Journeyman Course (RTJC). They also need to pass aptitude tests and maintain IAT Level III certifications as per DoDD 8570.01-M. Advanced certifications like OSEE, CRTE, or GXPN can further elevate specialists into expert roles. With Red Team demand projected to grow 32% from 2023 to 2028 and approximately five cybersecurity job openings for every qualified candidate in the U.S., the career outlook is exceptionally strong [1].
Tips for Succeeding in NSA Red Team Roles
Preparing for Assessments and Interviews
Red teaming is all about simulating real-world adversaries with mission-driven objectives, which sets it apart from penetration testing’s focus on simply identifying vulnerabilities. Interviewers will expect you to explain this difference clearly and confidently [12].
Showcase your ability to think like an adversary. This means approaching challenges creatively, identifying unconventional ways to achieve objectives, and understanding that red teaming is a collaborative effort. Your goal isn’t just to "win" engagements but to help the blue team improve their detection and response capabilities.
Before your interview, conduct thorough open-source intelligence (OSINT) on the hiring team. Skipping this step could signal a lack of understanding of basic red team methodologies. Also, emphasize any specialized skills you bring to the table – whether it’s expertise in physical security, web applications, or custom tool development. Larger teams often seek candidates who stand out with unique capabilities rather than generalists.
Keeping Your Skills Current
Focus on mastering a core set of tools like Burp Suite Pro, Cobalt Strike, and BloodHound. Set up your own red team lab using platforms such as VMware or Proxmox to safely practice and refine your techniques [2].
Expand your certifications beyond the basics. While foundational credentials like Security+ are helpful, aim for more advanced offensive certifications like OSEP or CRTP. To stay ahead of evolving threats, consider certifications like the OffSec AI Red Teamer (OSAI), launched in 2026, which addresses vulnerabilities in AI systems and machine learning pipelines. Regularly practice in realistic scenarios through online platforms and stay updated on threat actor tactics by analyzing current threat intelligence. This not only sharpens your skills but also enhances your credibility when networking or applying for roles.
Building Professional Connections
Once you’ve honed your technical skills and interview readiness, networking becomes a critical step for career growth. Attend hiring events tailored to the Department of Defense and intelligence communities, such as AFCEA TechNet or Transition Careers fairs. Events like the Fort Meade hiring fair on June 5, 2026, are especially valuable for cleared professionals with CI or FS Poly clearances, offering direct access to NSA recruiters and hiring managers [14].
Get involved in communities like Red Team Village and participate in Capture the Flag competitions to expand your network. Senior roles often prioritize candidates with experience speaking at conferences or mentoring others, so start building this experience early. Contributing to open-source tools on GitHub is another way to strengthen your professional reputation. Additionally, initiatives like "Trusted Workforce 2.0" simplify transitioning between cleared positions, making it easier to navigate career opportunities as you progress.
Meet the Hacker Who Built NSA’s Elite RED TEAM
Conclusion
Joining the NSA Red Team requires a methodical career path, starting with foundational IT roles, advancing through SOC positions and penetration testing, and eventually specializing in red team operations – a journey that typically spans over six years. To thrive in this role, you’ll need to hone technical skills like Python, PowerShell, and C/C++, while also developing the mindset of an adversary.
Organizations that conduct regular red team exercises see a 29% reduction in breach costs, and the demand for red team experts is projected to grow by 32% between 2023 and 2028[1]. With around five open cybersecurity jobs for every qualified professional in the U.S., individuals who gain the right certifications and hands-on experience are well-positioned for competitive salaries and career growth[1].
To align with the NSA’s mission, adopt an offensive approach to cybersecurity. Success in this field relies on combining technical curiosity with the agency’s goal of fortifying national security. The red teaming community is tight-knit, so every interaction is a chance to build your reputation and expand your network[3].
As outlined earlier, your first steps include setting up a practice lab, earning certifications such as CASP+ or OSCP (IAT Level III), and participating in the red teaming community through CTF competitions and industry events. Take stock of where you are on this career path and focus on acquiring the skills and certifications needed to move forward.
While the journey to an NSA Red Team role requires dedication, the combination of meaningful work and top-tier career opportunities makes it an incredibly rewarding pursuit in the field of cleared cybersecurity.
FAQs
How long does TS/SCI clearance take?
TS/SCI clearance typically takes 6 to 18 months for new applicants. The exact timeline depends on several factors, such as the complexity of your background and the priorities of the agency handling your case. Since processing times can fluctuate, it’s crucial to remain patient as the process unfolds.
What should I learn first for NSA red teaming?
To get ready for NSA red teaming, start with the basics of cybersecurity. Dive into key areas such as identifying security vulnerabilities, conducting penetration tests, and simulating attacks. A solid technical foundation is a must before moving on to advanced skills or certifications. Begin by mastering fundamental concepts like cybersecurity principles, network security, and penetration testing methods. These skills will set the stage for excelling in red team roles at the NSA.
How do I prove skills without real-world ops?
Demonstrating your skills in cybersecurity involves more than just listing them on a resume. Get hands-on by tackling simulated exercises, labs, or projects that highlight your technical expertise and ability to solve problems. Joining Capture The Flag (CTF) competitions or participating in cybersecurity challenges is a great way to sharpen your skills while showcasing them to others. Training programs can also provide practical experience.
Earning certifications like CISSP, CEH, or OSCP adds another layer of credibility to your qualifications. These certifications are widely respected and can validate your knowledge in the field. Additionally, building a portfolio of personal or open-source projects can help you stand out.
Engage with cybersecurity communities to network and learn from others in the field. Documenting your problem-solving methods – whether through blogs, case studies, or presentations – can further establish your expertise and make your skills more visible to potential employers or collaborators.
