SCADA Security Engineers protect critical infrastructure like power grids and pipelines from cyber threats. These roles require expertise in industrial systems, cybersecurity, and often a security clearance due to the sensitive nature of the work. Here’s what you need to know:
- Core Skills: Knowledge of SCADA protocols (Modbus, DNP3), hardware (PLCs, RTUs), and cybersecurity practices like network segmentation and OT-specific threat detection.
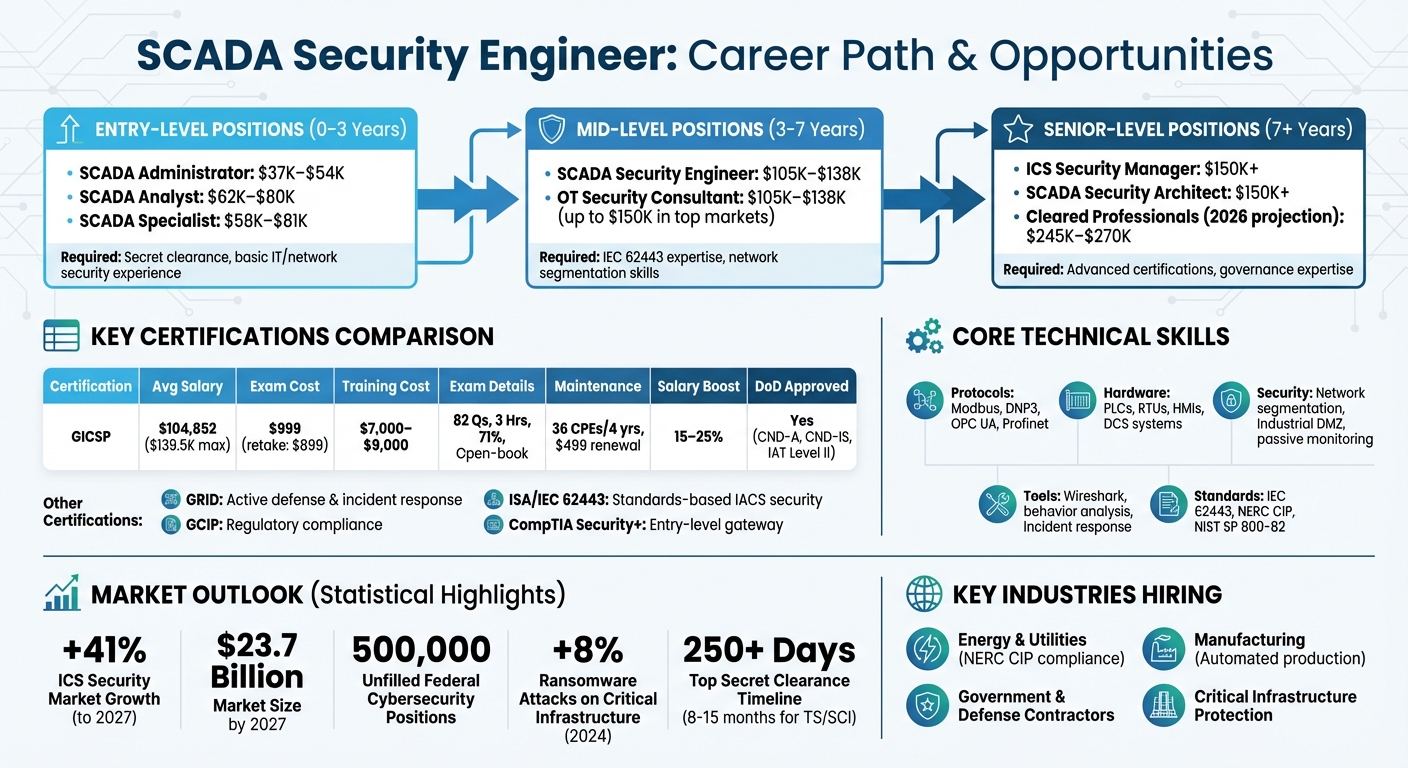
- Certifications: GICSP is highly valued, with average salaries of $104,852 (up to $139,500). Other options include GRID, GCIP, and ISA/IEC 62443.
- Career Path: Start in IT or network security, then transition to SCADA roles like SCADA Analyst ($62K–$80K) or SCADA Specialist ($58K–$81K). Mid-level roles can pay $105K–$138K, while senior positions exceed $150K.
- Demand: By 2026, salaries for cleared SCADA professionals could reach $245K–$270K due to talent shortages and increasing threats to critical infrastructure.
- Key Industries: Energy, government, and manufacturing are major employers, with strong demand for cleared professionals to secure national security assets.
For those with security clearances, this field offers high earning potential and opportunities to work on essential systems. Certifications, hands-on experience, and staying updated on industry standards like IEC 62443 are crucial to advancing in this career.
SCADA Security Engineer Career Path: Salaries, Certifications, and Progression Timeline
Required Skills and Certifications
Technical Skills for SCADA Security Engineers
Working in SCADA security demands a strong grasp of both industrial systems and cybersecurity. Engineers need to understand PERA levels 0–3 and use IEC 62443 Zones and Conduits as a baseline for system design. Familiarity with industrial protocols like Modbus, DNP3, OPC UA, and Profinet is critical, along with the ability to analyze traffic using tools such as Wireshark.
Hands-on knowledge of hardware is equally important. This includes managing and securing PLCs, RTUs, HMIs, and DCS systems. Network segmentation, particularly creating Industrial DMZs to isolate IT systems from operational technology (OT), is a key strategy to prevent ransomware from spreading across environments.
Unlike traditional IT systems, SCADA environments often rely on passive monitoring due to the fragility of legacy PLCs, which can crash under active scanning. Engineers should develop expertise in OT-specific threat detection, behavior analysis for identifying malware, and incident response strategies that prioritize physical process safety. Hardening legacy systems like Windows XP or Windows 7 and Unix-based platforms requires techniques such as application allowlisting and limiting local admin rights. Secure remote access is another critical area, involving multi-factor authentication (MFA), jump hosts, and encrypted VPNs to ensure safe vendor maintenance.
While these technical skills form the foundation, industry-recognized certifications are essential to demonstrate expertise in this specialized field.
Certifications That Employers Look For
One of the most sought-after certifications in SCADA security is the GICSP (Global Industrial Cyber Security Professional). This certification bridges the knowledge gap between IT, engineering, and cybersecurity [8][10]. The GICSP exam consists of 82 questions, takes three hours to complete, and requires a passing score of 71% [8]. It’s an open-book exam (printed materials only), so having a well-organized reference of technical terms can be incredibly helpful.
From a financial perspective, GICSP certification offers substantial rewards. As of September 2025, the average annual salary for GICSP-certified professionals in the U.S. was about $104,852, with top earners reaching $139,500 [7]. On average, certified individuals earn 15–25% more than their non-certified counterparts, with salaries for many specialists exceeding $120,000 [7]. The certification exam costs around $999, with retakes priced at $899. Official SANS training courses, such as ICS410, typically range between $7,000 and $9,000 or more [7]. To maintain certification, professionals need 36 Continuing Professional Education (CPE) credits over four years and must pay a renewal fee of approximately $499 [7][10].
The GICSP is recognized by the U.S. Department of Defense for roles in categories like CND-A, CND-IS, and IAT Level II [7]. Other certifications worth considering include:
- GRID (GIAC Response and Industrial Defense): Focuses on active defense and incident response.
- GCIP (GIAC Critical Infrastructure Protection): Targets regulatory compliance.
- ISA/IEC 62443 Certification: Emphasizes standards-based IACS security [9][10].
While general certifications like CISSP, CEH, and CISM provide a broad understanding of information security, they lack the specific focus on OT/ICS environments that the GICSP offers [10].
Beyond technical skills and certifications, success in SCADA security also depends on mastering key non-technical abilities.
Non-Technical Skills for Success
In SCADA security, priorities differ from traditional IT. The focus is on Availability → Integrity → Confidentiality, all underpinned by a commitment to safety [6]. This safety-first approach is critical because mistakes in industrial settings can lead to physical harm and costly operational disruptions.
Problem-solving is a must, especially when conventional IT methods don’t work in OT environments. As Francis Cianfrocca, CEO of Insight Cyber Group, explains:
Even if you change an operating system just a little bit to patch it, you’ve invalidated all your safety testing [1].
This means engineers often need to rely on manual behavior analysis and creative solutions to secure outdated systems.
For professionals in cleared SCADA roles, communication and leadership are equally important. Engineers must translate complex cyber risks into actionable safety measures for plant managers and regulatory bodies. Using clear, quantifiable descriptions of achievements – such as "Developed a secure remote access policy ensuring 100% compliance with ISA/IEC 62443 standards" – can effectively convey impact. Working under pressure is a common requirement, especially in critical infrastructure sectors like nuclear energy or power grids, where uptime directly impacts public safety. Collaboration across engineering teams, adapting to manual processes when automation isn’t an option, and leading the development of long-term security strategies are all part of the role.
sbb-itb-bf7aa6b
Career Progression and Growth Opportunities
Entry-Level Positions and Getting Started
If you’re looking to break into SCADA security, your journey will likely begin by leveraging your existing IT or physical security experience. As the Infosec Institute explains:
OT security practitioner roles aren’t typically entry-level positions. Most people get into industrial control systems security after working in network security [1].
This means your background in IT can be a solid foundation – just shift the focus of your expertise. Instead of emphasizing software maintenance, highlight how your skills contribute to risk reduction and operational reliability [6].
For entry-level roles, consider positions like SCADA Administrator (salary range: $37K–$54K), SCADA Analyst ($62K–$80K), or SCADA Specialist ($58K–$81K) [1]. These roles often require knowledge of industrial protocols, basic hardware, and a security clearance – typically at least a Secret level – for work in government or critical infrastructure.
Emily Miller, Vice President of National Security and Critical Infrastructure at Mocana, advises newcomers to start with foundational certifications:
If you’re new to the field, CompTIA Security+ is an excellent gateway into OT and ICS security [1].
Building on that, you can pursue more specialized certifications like the GICSP or Industrial Control Security Practitioner (ICSP). Setting up a home lab is another great way to stand out. Use Modbus simulators, open-source HMI tools, and software like pfSense to demonstrate your practical skills to potential employers [6]. Over time, you’ll gain the experience needed to move into more advanced roles.
Mid-Level and Senior SCADA Security Positions
As you grow in your career, you’ll find opportunities to specialize in technical or governance-focused roles. Mid-level positions, such as SCADA Security Engineer or OT Security Consultant, offer salaries ranging from $105K to $138K, with top markets reaching as high as $150K [1]. These roles require deep knowledge of frameworks like IEC 62443, particularly in designing secure architectures with zones and conduits for network segmentation.
At the senior level, the focus shifts to broader responsibilities. For instance, ICS Security Managers handle governance, risk, and compliance using standards like NIS2, while SCADA Security Architects focus on technical implementations guided by frameworks such as NIST SP 800-82. These roles often involve balancing IT security measures with the unique demands of operational technology, such as managing patch cycles without disrupting critical processes.
Senior professionals also need to excel at detecting threats through manual behavior analysis and passive network monitoring, as traditional signature-based detection methods often fall short in industrial environments.
How to Advance Your SCADA Security Career
Once you’ve built a solid foundation in entry-level and mid-level roles, advancing your career requires a strategic approach. As Emily Miller points out:
Credentialing yourself is number one [1].
To stand out, consider advanced certifications like the GIAC Critical Infrastructure Protection (GCIP) or the ISA/IEC 62443 Cybersecurity Expert certificate. These credentials demonstrate your expertise in both governance and compliance, which are critical for senior roles.
The ICS security market is growing rapidly, with projections showing a 41% increase through 2027, reaching $23.7 billion [1]. This growth means there’s strong demand for professionals who can navigate both technical and regulatory challenges. Stay ahead by keeping up with CISA ICS alerts, joining organizations like the Industrial Control System Information Sharing and Analysis Center (ICS-ISAC), and participating in OT-specific cyber drills to improve your incident response skills [1][2].
Developing and tracking senior-level metrics is also essential. Focus on KPIs like asset inventory coverage, segmentation progress (e.g., implementing an Industrial DMZ), and backup readiness for critical OT servers. Mastering the "Zones and Conduits" approach from IEC 62443 can help you communicate effectively across engineering, operations, and IT teams.
For professionals with active security clearances, platforms like Cleared Cyber Security Jobs can connect you with specialized roles in defense and national security. These positions often offer unique opportunities to work on critical infrastructure projects that require top-tier expertise.
Job Market and Salary Information
Industries Hiring SCADA Security Engineers
SCADA security engineers are in high demand across several industries. Energy and utilities companies, like Dominion Energy, rely on these professionals to protect industrial control systems and ensure compliance with regulations such as NERC CIP and NIST standards [12]. For instance, in February 2026, Dominion Energy South Carolina sought a Senior/Staff Cyber Security and Control Systems Engineer in Cayce, SC. The role involved supporting power generation facilities, maintaining NERC CIP compliance, and managing industrial control system networks [12].
Outside the energy sector, manufacturing facilities with automated production lines also require SCADA security specialists. These professionals play a crucial role in bridging the gap between IT security and operational technology on the factory floor [12]. Additionally, defense contractors and government agencies are prominent employers in this field, particularly in roles tied to critical infrastructure protection [3].
The increasing need for SCADA security experts highlights the broader challenges of filling cleared cybersecurity positions.
Growing Demand for Cleared SCADA Professionals
The SCADA job market, particularly for cleared professionals, faces a severe talent shortage. Around 500,000 federal cybersecurity positions remain unfilled, with TS/SCI-cleared roles being among the hardest to staff. These positions are crucial to national security, especially as adversaries like Russia, China, and Iran intensify their attacks on IT and OT/SCADA systems [3].
Regulatory requirements are further driving the demand for SCADA professionals. Executive Order 14028 mandates Zero Trust adoption across federal agencies, while FedRAMP-High standards require cleared personnel for cloud migration tasks, including supply-chain vetting and continuous monitoring [3]. However, the process of obtaining Top Secret clearances is lengthy, with investigations taking over 250 days and TS/SCI adjudications requiring 8 to 15 months. This prolonged timeline exacerbates the scarcity of cleared professionals [3].
These challenges, combined with the urgency of addressing cyber threats, have a direct impact on salaries in the SCADA security field.
Salary Ranges and Job Outlook
In the SCADA security sector, security clearances significantly boost earning potential. Employers are prioritizing "verified trust" and the ability to work in sensitive environments over technical skills alone [13]. By 2026, salaries for cleared SCADA security professionals are projected to range from $245,000 to over $270,000. This trend underscores the value of security clearances in a market shaped by increasing cyber threats and stringent regulations [13].
Industry insiders often refer to this situation as the "combined challenges" – a mix of growing nation-state threats, expanding regulatory requirements like CMMC and Zero Trust, and a historic shortage of polygraphed technical experts [13]. A representative from FullScope Staffing explained:
The clearance itself has become a strategic asset, and in 2026 it will be the single strongest determinant of compensation for top technical cybersecurity roles [13].
Federal agencies are also grappling with retention issues. Cleared engineers are frequently drawn to defense contractors offering signing bonuses and salaries that exceed federal pay scales by 10–25% [3].
For those with security clearances looking to enter the SCADA security field, platforms such as Cleared Cyber Security Jobs provide access to high-paying roles in the energy, defense, and government sectors. With ransomware attacks on critical infrastructure rising by 8% as of 2024, the demand for SCADA security expertise is expected to remain strong well into the future [3].
OT Cybersecurity for Beginners: The Complete Guide (ICS, SCADA & PLC)
Next Steps for Your SCADA Security Career
If you’re looking to advance your cleared SCADA security career, here’s a roadmap to help you build on the essential skills and seize new opportunities.
Key Requirements for a SCADA Security Career
A successful SCADA security career demands a mix of certifications, hands-on technical expertise, and an active security clearance. Start with a foundational certification like CompTIA Security+, then move on to specialized credentials such as GICSP or GCIP [1]. As Emily Miller, Vice President of National Security and Critical Infrastructure at Mocana, puts it:
Credentialing is the top priority. [1]
Beyond certifications, consider setting up a lab to practice with protocols and standards like Modbus, DNP3, IEC 62443, and NERC CIP [2]. Developing skills in malware behavioral analysis is also critical. According to Francis Cianfrocca, CEO of Insight Cyber Group:
Implementing IT-style security controls in industrial environments is challenging; much of ICS security requires manual, creative solutions. [1]
Achieving specialized certifications alongside an active clearance can boost your earnings by 15–25% [7]. These steps will lay a strong foundation for leveraging resources and tools to propel your career further.
Resources and Job Search Tools
Once you’ve met the core requirements, take advantage of specialized platforms and training programs to secure your next SCADA security role. Start with Cleared Cyber Security Jobs, a platform that connects professionals to SCADA security positions within defense contractors, government agencies, and critical infrastructure sectors. Features like job alerts, a resume database, and tailored career resources allow you to stay updated on roles such as "ICS/SCADA Cyber Threat Intelligence Analyst" or "Incident Response Analyst (OT/ICS/SCADA)" [4][5].
For training, the SANS ICS410 (ICS/SCADA Security Essentials) course is highly respected for preparing candidates for the GICSP exam. While the course costs between $7,000 and $9,000, it is considered a top-tier investment [7]. Free resources are also available through the Cybersecurity & Infrastructure Security Agency (CISA), which offers training materials and ICS alerts tailored for cleared professionals [1][2]. Additionally, the ISA/IEC 62443 Cybersecurity Certificate Program provides flexible learning formats, including classroom sessions, instructor-led online courses, and self-paced modules. These options make it possible to earn the ISA/IEC 62443 Cybersecurity Fundamentals Specialist certificate while maintaining full-time employment [11].
Keep an eye on hiring opportunities from prominent defense contractors like Leidos, SAIC, Nightwing, and Riverside Research. These companies frequently post cleared SCADA roles in key areas such as Arlington, VA; Reston, VA; Dayton, OH; and Tucson, AZ [4][5]. With the ICS security market expected to grow to $23.7 billion by 2027 and a projected annual growth rate of 41%, now is an excellent time to take the next step in your SCADA security career [1].
FAQs
What clearance level do SCADA security roles usually require?
SCADA security roles often require a Top Secret clearance. In some cases, positions may also necessitate SCI (Sensitive Compartmented Information) access, depending on the specific responsibilities of the job.
How can I get hands-on OT/SCADA experience without access to a plant?
To build experience with OT/SCADA systems, you can dive into virtual labs, simulations, and online training. Start with platforms that create realistic scenarios for critical infrastructure. For example, free resources like CISA’s virtual labs offer hands-on opportunities. Additionally, training courses that focus on ICS security are a great way to deepen your understanding. Tools for penetration testing and simulations also let you practice in controlled environments, giving you the chance to develop skills without requiring physical access to an actual plant.
Which certification should I get first for SCADA security: Security+ or GICSP?
For SCADA security, the GICSP (Global Industrial Cybersecurity Professional) certification is an excellent starting point. It specifically targets the security of industrial control systems (ICS) and operational technology (OT), making it a perfect fit for SCADA-related roles. On the other hand, Security+ offers a general introduction to cybersecurity concepts and is more suited for entry-level professionals. If you’re aiming to show expertise in safeguarding critical infrastructure, GICSP aligns much better with that goal.
