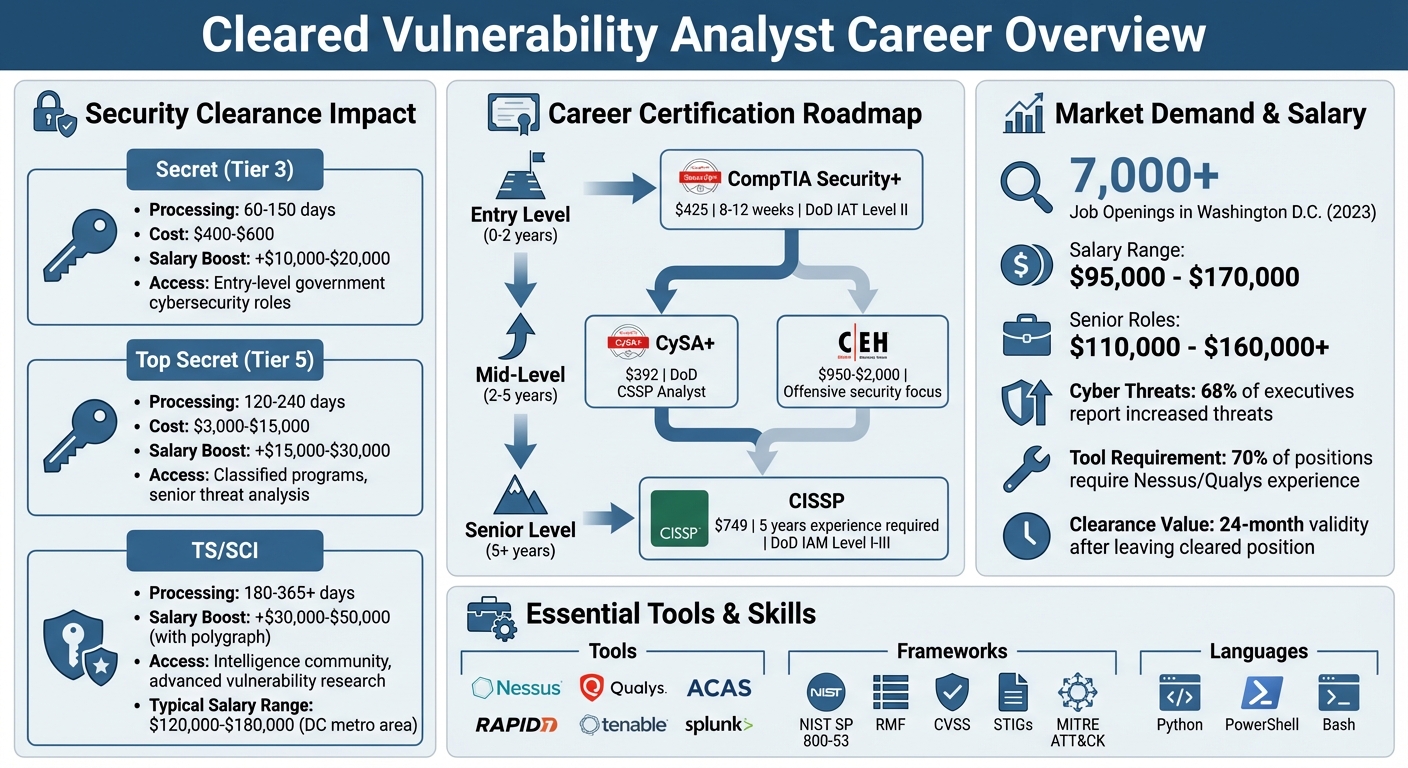
Cleared Vulnerability Analysts are cybersecurity professionals who protect sensitive government and defense systems by identifying and addressing system vulnerabilities. These roles require a mix of technical expertise, certifications, and active security clearances, offering access to high-paying, in-demand positions. Here’s what you need to know:
- Key Responsibilities: Identifying vulnerabilities, conducting risk assessments, ensuring compliance with frameworks like NIST, and collaborating with teams to implement security measures.
- Required Skills: Proficiency in tools like Nessus, Qualys, and ACAS, scripting languages (Python, PowerShell), and frameworks such as RMF and CVSS.
- Certifications: Start with CompTIA Security+ and progress to CEH or CISSP for advanced roles.
- Clearance Impact: Active security clearances (Secret, Top Secret, TS/SCI) significantly boost earning potential and job eligibility.
- Salaries: Ranges from $95,000 to $170,000, with higher pay for advanced clearances and senior roles.
- Job Search Tips: Use specialized job boards, highlight clearances on your resume, and network at industry events.
Demand for these roles is growing, driven by increasing cybersecurity threats and investments in national security. With the right skills and certifications, cleared professionals can secure lucrative and impactful careers in this field.
Security Clearance Levels and Certification Requirements for Vulnerability Analysts
Cyber Security Careers: How to get started in Vulnerability Management
sbb-itb-bf7aa6b
What Does a Cleared Vulnerability Analyst Do?
Cleared Vulnerability Analysts play a critical role in protecting government and defense systems by identifying and addressing vulnerabilities before they can be exploited. These professionals work in secure environments, managing sensitive national security information, and performing advanced technical assessments that go beyond what is typically encountered in corporate settings. Their security clearance gives them access to systems and data that are off-limits to most cybersecurity professionals.
Here’s a closer look at their main duties and responsibilities.
Core Responsibilities
On a daily basis, Cleared Vulnerability Analysts scan systems and networks to uncover vulnerabilities, prioritizing them based on severity and potential impact. To do this, they rely on the Common Vulnerability Scoring System (CVSS) to evaluate which issues pose the highest risk. Their work spans a variety of environments, including Windows, Linux, enterprise networks, cloud platforms, and web applications. Common challenges include addressing SQL injection vulnerabilities and fixing configuration errors.
These analysts also develop cybersecurity risk profiles, conduct threat modeling, and assess how security incidents could disrupt operations. Based on their findings, they recommend cost-effective security measures and remediation strategies. They then track the implementation of these measures, reporting progress and key metrics to organizational leadership.
Compliance and auditing are also central to the role. Analysts ensure adherence to cybersecurity frameworks and standards such as NIST, ISO 27001, and CIS Controls. They prepare detailed audit reports and manage specialized tools to evaluate and strengthen high-security defenses.
Collaboration is another vital aspect. Cleared Vulnerability Analysts work closely with SecOps and DevOps teams to ensure that patches and updates are thoroughly tested and deployed without disrupting operations. They also perform root cause analyses for security incidents and coordinate with external partners for controlled penetration testing and third-party assessments. As CompTIA puts it, "A vulnerability analyst must think like a hacker to protect against them."
How Security Clearance Affects the Role
Security clearance adds another layer of responsibility and influence to this role. Cleared positions involve specialized tasks, such as using tailored audit tools and conducting advanced evaluations of multi-layered defense strategies. As the New York City Office of Technology and Innovation explains, their mission is to "lead and execute an innovative, intelligence-driven, risk-informed cyber defense and response strategy – with the support of key partners and allies – that enables the city government to properly function and provide services."
This elevated responsibility often comes with higher pay. For example, in New York City, Vulnerability Management Analysts typically earn between $86,101 and $101,295, while senior roles can command salaries ranging from $110,000 to $160,000 [4][5].
The demand for cleared professionals is also fueled by a growing talent shortage in cybersecurity. With 68% of business executives reporting an increase in cyber threats against their organizations [5], the need for skilled analysts continues to rise. Employers generally prefer candidates with 2 to 6 years of experience in fields like information systems, infrastructure design, or network security [1]. Holding an active clearance can significantly enhance career prospects, offering opportunities for faster advancement in this high-demand field.
Required Skills and Tools for Cleared Vulnerability Analysts
Becoming a successful Cleared Vulnerability Analyst demands a mix of technical know-how, strategic insight, and the ability to communicate effectively. While technical expertise helps you identify and mitigate risks, soft skills ensure you can translate those findings into actionable steps that resonate across teams and leadership.
Technical Skills
At the core of your technical toolkit is expertise in vulnerability assessment and scanning. Tools like Nessus, Qualys, and Rapid7 are essential for pinpointing security risks and policy violations [2][7]. If you’re working in government settings, proficiency with the Department of Defense’s Assured Compliance Assessment Solution (ACAS) is non-negotiable.
You’ll also need scripting skills to automate tedious tasks and create custom solutions. Languages like Python, PowerShell, and Bash are key here [2][6]. A solid grasp of compliance frameworks such as NIST SP 800-53, the Risk Management Framework (RMF), CVSS scoring, and STIGs is equally important, especially for meeting DoD compliance standards [2][7].
For more specialized roles, familiarity with managing NSA-certified Type 1 encryption devices (like TACLANE) is crucial. Additionally, you’ll rely on the MITRE ATT&CK framework to analyze threats and prioritize risks based on potential attack paths.
Soft Skills
Technical expertise is only part of the equation. A problem-solving mindset and the ability to think like a hacker are critical for anticipating attack vectors and securing systems. Communication skills are equally important – you’ll need to explain vulnerabilities and mitigation strategies in ways that non-technical stakeholders can understand. This includes writing policies, creating training materials, and presenting complex security concepts in simple terms.
Strategic thinking is another must-have. You’ll develop risk-based mitigation plans and measure the effectiveness of security programs to demonstrate their value to leadership. These soft skills ensure that your technical efforts translate into meaningful, actionable outcomes.
Tools and Technologies You’ll Use
Your everyday tools will include vulnerability scanning platforms like Tenable Nessus Professional and Nessus Expert, which help identify risks in web applications and external attack surfaces. These tools use extensive plugin libraries from Tenable Research to uncover vulnerabilities that could impact your organization [8].
For data analysis and reporting, platforms like Splunk are invaluable for incident response and log analysis. Tenable One offers a unified view of IT, OT, and cloud environments, while Power BI helps you present findings in a way that’s easy for leadership to digest.
The field is also embracing AI-driven solutions. Tools like Tenable ExposureAI are designed to reveal hidden risks and provide detailed remediation guidance. Additionally, you’ll work with Cloud-Native Application Protection Platforms (CNAPP) and Cloud Security Posture Management (CSPM) solutions to manage risks in hybrid and cloud environments. Attack path mapping technologies, which visualize cross-domain relationships, are becoming increasingly important for blocking critical attack vectors.
Top Certifications for Cleared Vulnerability Analysts
Certifications play a crucial role in showcasing your expertise and readiness for roles in cleared cybersecurity. For professionals working with national security infrastructure, certifications act as proof of your ability to handle classified networks and sensitive threat data effectively [9]. In fact, many cleared vulnerability analyst positions explicitly require certifications like CEH or CISSP as part of their qualifications [3].
Here’s how certifications are typically categorized and what they offer:
For those just starting out, CompTIA Security+ is an excellent entry point. Priced at $425, it can be earned within 8–12 weeks and meets the Department of Defense (DoD) baseline requirements. It’s widely recognized across government and contractor roles. Once you’ve earned Security+, the CySA+ (Cybersecurity Analyst) certification, costing $392, provides deeper knowledge in vulnerability management and threat hunting, which are core responsibilities for vulnerability analysts [10].
If your focus leans toward offensive security and vulnerability research, the Certified Ethical Hacker (CEH) certification from EC-Council is a strong choice. With costs ranging between $950 and $2,000, CEH emphasizes offensive security strategies and helps you develop the mindset needed for identifying system vulnerabilities [10]. At the senior level, the CISSP (Certified Information Systems Security Professional) from (ISC)² is often considered the top credential. Priced at $749, it requires five years of experience and is frequently mandatory for high-level government contractor roles. A CISSP certification can also open the door to higher salary opportunities [10].
Certification Comparison Table
| Certification | Issuing Body | Focus Area | DoD 8570/8140 Level | Renewal Requirements |
|---|---|---|---|---|
| Security+ | CompTIA | Broad security foundations, DoD entry | IAT Level II | CEUs every 3 years |
| CySA+ | CompTIA | Vulnerability management, threat hunting | IAT Level II, CSSP Analyst | CEUs every 3 years |
| CEH | EC-Council | Offensive methodologies, vulnerability research | IAT/IASAE Level III, CSSP Analyst | Annual renewal fees |
| CISSP | (ISC)² | Security management, architecture | IAM Level I-III, IASAE | Annual fees + CPE credits |
For those new to the field, starting with Security+ is a smart move, especially if you have less than two years of experience. From there, you can build on your skills with CySA+ for more analyst-specific expertise. As you gain experience (around five years or more), pursuing CISSP can help you qualify for higher-level roles.
It’s also worth noting that 70% of vulnerability analyst positions require hands-on experience with tools like Nessus and Qualys. Certifications are most impactful when paired with practical, real-world experience [3]. Combining both will not only enhance your qualifications but also accelerate your career in cleared cybersecurity positions.
Using Your Security Clearance to Find Better Jobs
An active security clearance can be a game-changer for vulnerability analysts. For cybersecurity professionals tasked with safeguarding national security infrastructure, a U.S. government security clearance is essential. It’s a requirement for roles that involve securing classified networks like SIPRNet, analyzing sensitive threat data, or uncovering vulnerabilities in critical systems and infrastructure [9].
Employers actively seek candidates with clearances because obtaining one is both expensive and time-consuming. A Top Secret clearance, for example, can cost between $3,000 and $15,000, with processing times stretching up to a year [11]. As Brad Thompson, Founder of Best Military Resume, points out:
Every month a position sits empty because a clearance investigation is in progress costs the company money. A veteran who walks in the door with an active clearance fills that seat immediately [11].
This demand translates into better opportunities for you. An active clearance not only gives you an edge in salary negotiations but also opens doors to roles requiring specialized skills like vulnerability research [11]. It also grants access to exclusive positions at top defense contractors like Lockheed Martin and Northrop Grumman, as well as intelligence-focused firms such as Palantir and Booz Allen Hamilton [11].
Let’s take a closer look at clearance levels and how they impact job eligibility.
Clearance Levels and Job Eligibility
Knowing the different clearance levels can help you target the right positions. Secret clearance (Tier 3) is the entry-level requirement for most government cybersecurity roles, covering tasks like IT support, network defense, and maintaining government systems. The average processing time for this clearance ranges from 60 to 150 days, with an investigation cost of approximately $400–$600 [9][11].
Top Secret (Tier 5) clearance is required for roles involving classified programs, senior-level threat analysis, and cybersecurity operations. Processing typically takes 120 to 240 days [9]. For even more sensitive positions, TS/SCI (Top Secret/Sensitive Compartmented Information) clearance is needed, particularly for intelligence community roles and advanced vulnerability research. The highest level, TS/SCI with polygraph, is reserved for national intelligence agencies like the NSA, CIA, and NRO. These clearances can take anywhere from 180 to over 365 days to process due to polygraph scheduling delays [9].
It’s important to note that you cannot apply for a clearance on your own; a federal agency or authorized contractor must sponsor you for a specific position [9][11]. This makes having an active clearance a major advantage – you’re ready to step into a role without delay.
These clearance levels not only determine the types of jobs you’re eligible for but also influence salary potential and hiring speed.
Benefits of Security Clearance in Job Applications
Having a clearance boosts both your earning potential and job prospects. A Secret clearance can add $10,000–$20,000 to your annual salary [11]. For Top Secret holders, the premium jumps to $15,000–$30,000. In high-demand markets like the DC metro area, professionals with TS/SCI clearance and technical expertise often earn between $120,000 and $180,000, with senior roles exceeding $200,000 [11]. The highest tier, TS/SCI with polygraph, can command an additional $30,000–$50,000 compared to non-polygraph positions [11].
Beyond higher pay, clearances streamline the hiring process and grant access to exclusive roles that are rarely advertised publicly. Many cleared positions are filled through direct recruitment of professionals who already have active clearances.
Keep in mind the 24-month rule: if you leave a cleared position, your clearance remains valid for two years and can be reactivated without a full reinvestigation [9][11]. Brad Thompson cautions:
Letting a TS/SCI lapse because you took a non-cleared position is one of the most expensive mistakes a transitioning veteran can make [11].
To maximize the value of your clearance, prominently display your clearance level and status (e.g., "Top Secret/SCI (active)") at the top of your resume – recruiters for these roles often look for it first [11]. Under the Continuous Vetting system, you must also promptly report any adverse events, such as arrests or significant financial changes, to your Facility Security Officer to maintain eligibility [9]. Pairing your clearance with in-demand certifications like CISSP or CySA+ can further enhance your appeal in the cleared job market [11].
Job Search Strategies for Cleared Vulnerability Analysts
If you’re a cleared vulnerability analyst, having a focused job search strategy can make all the difference in landing the right role. With your clearances and certifications, you’re already positioned for opportunities in the highly competitive cleared cybersecurity field. Specialized job boards for the cleared community are a great starting point. These platforms compile listings from top defense contractors like Leidos, Peraton, CACI, and SAIC, as well as government agencies, offering roles that specifically require active security clearances [12].
Using Job Search Filters
To make your search more effective, take advantage of filters. Narrow down options by clearance level (Secret, Top Secret, TS/SCI, or TS/SCI with Polygraph) and include technology-specific terms like Tenable, Nessus, Qualys, Nexpose, and ACAS. For example, as of March 26, 2026, searching for "Vulnerability Assessment Analyst" on a cleared job board yielded 276 active listings [12].
Geographic filters are just as important. Many roles are located in defense hotspots like Fort Meade, Maryland; Ashburn and Reston, Virginia; and Tampa, Florida. These areas often require on-site work due to the classified nature of the projects [12]. Once you’ve refined your search, stay organized and proactive with your applications.
Uploading Resumes and Setting Alerts
Your resume should immediately showcase your highest clearance level at the top. When setting up job alerts, avoid broad terms like "Cybersecurity." Instead, use specific titles such as "Vulnerability Assessment Analyst" or "Vulnerability Management" paired with your clearance level. This approach ensures you receive relevant notifications as soon as new positions are posted [12][13].
Make your resume stand out by including measurable achievements, such as:
- "Performed over 100 vulnerability assessments annually, reducing security breaches by 20%" [14]
Setting alerts for immediate updates and tailoring your resume with clear, quantifiable results will help you stay ahead in the application process.
Attending Job Fairs
Job fairs are another excellent way to connect directly with hiring managers from major defense contractors. For instance, SOSi recently sought a Vulnerability Assessment Team Lead in Ashburn, Virginia, requiring a DHS clearance, while Peraton was hiring a Malware Analyst in Fort Meade, Maryland, with TS/SCI with Polygraph requirements [12]. These events allow you to present yourself beyond your resume, often speeding up the hiring process and giving you a chance to make a lasting impression.
How to Optimize Your Resume for Cleared Vulnerability Analyst Roles
Your resume needs to immediately highlight your technical skills and active clearance to get through ATS filters. As Brad Tachi, CEO and Founder of Best Military Resume, explains:
I’ve talked to defense contractor recruiters who told me they literally search their ATS for ‘TS/SCI’ as their first filter before looking at anything else. If your clearance isn’t in a searchable text field on your resume… you’re invisible to these recruiters. [18]
This means your clearance level should be prominently displayed at the very top of your resume, not buried in a paragraph.
Highlighting Technical Expertise and Clearance
For cleared roles, it’s essential to showcase both your clearance and technical expertise clearly. Start by placing your active clearance level directly under your contact information in the header. Use concise, standardized terms like "Active TS/SCI" or "Active Secret Clearance – Current" to ensure recruiters and ATS filters can spot it immediately [18]. Mention your clearance again in your Skills section. If you hold a polygraph, note it explicitly – for example, "CI Polygraph" or "Full-Scope Polygraph" – as these credentials can boost your earning potential by $15,000 to $30,000 in cybersecurity roles [18].
Highlight your technical skills by listing tools like Nessus, ACAS, Nexpose, Qualys, and frameworks such as STIGs, SCAP Compliance Checker, RMF, and NIST SP 800-53. Include scripting languages like Python, PowerShell, and Bash, emphasizing measurable outcomes [15]. Specify the IAT level you meet under DoD 8570/8140 guidelines (e.g., IAT Level II or III) to signal your readiness for government contract roles.
When describing your achievements, use quantifiable results. Replace generic statements like "Conducted vulnerability assessments" with specifics such as "Performed over 100 vulnerability assessments annually, reducing security breaches by 20%" or "Decreased system vulnerabilities by 35% through proactive threat monitoring" [17]. Structuring your accomplishments with the STAR method can help you present them more effectively [19].
Once your clearance and technical expertise are clearly outlined, the next step is to focus on certifications and tool proficiencies.
Emphasizing Certifications and Tools
Certifications are crucial for meeting job requirements and proving your expertise. Highlight DoD 8570-compliant certifications such as CompTIA Security+, CEH, CISSP, CASP+ CE, and CySA+. If you’re pursuing a certification, include it with the expected completion date [15][16]. These credentials not only validate your skills but also show employers your dedication to ongoing professional growth [16].
Organize your technical skills into a dedicated section, grouping tools, frameworks, and languages together. Use the exact wording from job postings (e.g., "penetration testing" or "SIEM solutions") to ensure your resume aligns with ATS filters [19]. Keep the design clean and simple – avoid flashy graphics that might confuse scanning software – and limit your resume to one or two pages, focusing on the last decade of relevant experience [19].
Networking in the Cleared Cybersecurity Community
Boost your job search by focusing on strategic networking to uncover opportunities that aren’t listed online. If you have an active security clearance and technical expertise, expanding your professional network is a must. In the cleared cybersecurity world, many positions are filled through personal connections rather than traditional applications. As CyberSecJobs.com puts it:
"In the security-cleared cyber security community, landing your dream job often requires more than just submitting your resume online. Whether you’re happy to hear it or not, networking is key." [20]
Washington D.C. is a prime location to focus on, with over 7,000 vulnerability analyst openings reported in 2023 [3]. Attending local events in this area can help you connect directly with defense contractors and government agencies. These interactions can lead to introductions to professional groups and online communities that are integral to the cleared cybersecurity field.
Joining Industry Organizations
Associations like (ISC)² and ISACA offer resources specifically tailored to professionals with security clearances. These include government-focused special interest groups and certification programs [21]. Membership in these organizations gives you access to directories that can help you find mentors already working in senior roles within the cleared cybersecurity space. The SANS Institute also caters to cleared professionals by hosting government-focused tracks at its conferences, offering a chance to network in a more specialized setting [21]. If you’re working toward certifications like CISSP-ISSEP or SSCP, these organizations can connect you with seasoned professionals who can guide you.
Engaging in Online Communities
In addition to formal industry groups, online platforms are valuable tools for connecting with experienced professionals. LinkedIn is an excellent place to network with alumni from defense contracting firms, while GitHub allows you to showcase your cybersecurity projects [20]. Make sure your LinkedIn profile highlights your clearance, technical skills, and vulnerability analysis expertise. Participating in forums like Reddit’s r/netsec and Stack Overflow can also help you build your professional reputation.
Conferences such as Black Hat, RSA, and DEF CON are ideal for informal networking. Events often include what’s known as "HallwayCon", where you can meet peers and recruiters in a casual setting [20]. Many conferences also offer volunteer roles, which can provide free access to sessions and direct interaction with industry leaders [20]. After meeting new contacts, follow up with personalized messages within a few days to keep the connection alive [20].
Conclusion
To excel as a cleared Vulnerability Analyst, focus on building a strong foundation of technical skills, earning relevant certifications, and expanding your professional network. Proficiency with tools like Nessus and Qualys is essential, as is validating your expertise through certifications such as CompTIA Security+ or CEH early in your career [1]. The growing demand for cleared professionals, highlighted by specific market trends and job boards, underscores the opportunities in this field.
Your security clearance is a powerful advantage. Use specialized job boards to filter roles by clearance level and set up automated alerts to stay ahead of new opportunities [12]. This approach not only simplifies your job search but also helps you tailor your resume to stand out in a competitive market.
Soft skills and continuous learning are just as important as technical expertise. Develop the ability to communicate technical vulnerabilities in terms of business risks [1], and stay informed about emerging threats, including those related to AI security challenges [2]. Whether your goal is to manage a Security Operations Center or transition into penetration testing, this role provides a solid platform for career growth [1].
Maximize your potential by emphasizing both your clearance and technical skills on your resume. Take advantage of resources like Cleared Cyber Security Jobs to connect with employers, especially in high-demand areas like Washington D.C. With these strategies, you’ll be well-positioned to secure and thrive in top opportunities.
FAQs
Can I get a security clearance without a job offer?
No, you typically can’t get a security clearance without a job offer. Security clearances require sponsorship from an employer or a government agency. This sponsorship is what initiates the process, which includes thorough background checks on your finances, criminal history, and personal conduct. Without a job offer or a sponsoring organization, you won’t be able to begin or obtain a clearance.
What should I do if my clearance is about to lapse?
If your security clearance is nearing expiration, it’s time to gear up for a periodic reinvestigation to keep your clearance active. This review typically involves checks on areas like your finances, criminal record, and personal behavior. To stay ahead of the process, make sure all your required documents are current and work closely with your sponsoring employer or security officer to streamline the steps.
How do I get hands-on experience with Nessus, Qualys, or ACAS?
Gaining hands-on experience with tools like Nessus, Qualys, or ACAS can be as simple as working with them in a lab or test environment. This allows you to explore their features and functionality in a controlled setting. You can also build your skills through training courses, online tutorials, or even simulations designed to mimic real-world applications.
If you’re aiming for practical, on-the-job experience, roles like Junior Vulnerability Analyst often include training or supervised use of these tools. This kind of role not only helps you learn the tools but also gives you exposure to applying them in real-world scenarios.
