A cleared forensic analyst is a digital investigator with government security clearance, specializing in analyzing evidence like file systems, memory dumps, and network traffic to solve cybercrimes or breaches. These roles require a mix of education, certifications, and technical skills, offering competitive salaries and career growth opportunities in government and private sectors.
Key Takeaways:
- Security Clearance: Essential for handling sensitive cases; makes candidates highly sought after.
- Education: Bachelor’s degree in computer science, cybersecurity, or related fields is standard; advanced degrees can provide an edge.
- Certifications: GCFA, GCFE, CCFP, and others validate expertise and align with Department of Defense standards.
- Skills: Proficiency in forensic tools (e.g., EnCase, Autopsy), file system analysis, memory forensics, and network forensics.
- Salary Ranges: Entry-level starts at $60,000-$80,000; senior roles can exceed $145,000 annually.
- Job Market: High demand due to increasing cybercrime; federal agencies and contractors are primary employers.
This guide provides detailed insights into qualifications, certifications, tools, and strategies to excel in this field.
Education and Experience Requirements
Educational Background
For most positions, a bachelor’s degree is the standard requirement. Degrees in fields like computer science, cybersecurity, digital forensics, IT, engineering, or mathematics are often preferred for cleared roles[1]. In laboratory-based positions, degrees in chemistry, biochemistry, biology, or forensic science are typically necessary[5][6].
Federal agencies, such as the FBI, often have specific academic requirements. For example, digital forensic examiners are usually required to complete at least 24 college semester hours in a relevant subject area[1]. The National Institute of Justice emphasizes the importance of academic integrity and suitable educational qualifications:
A model candidate for all forensic science practices possesses personal integrity, holds a baccalaureate degree (at a minimum) in the natural sciences[5].
For those aiming for senior, research, or teaching roles, a master’s degree in digital forensics or a related discipline can offer a competitive edge[7]. When choosing a degree program, it’s wise to look for accreditation by respected organizations such as The Chartered Society of Forensic Sciences[4].
Experience Expectations
Education alone isn’t enough – practical, role-specific experience is essential.
For entry-level forensic science technician roles, prior work experience is often not required beyond holding a bachelor’s degree. However, on-the-job training is common and may last anywhere from six months to three years[5][6].
Mid-level positions usually demand at least two years of relevant experience in areas like forensic science, biology, or chemistry, in addition to a bachelor’s degree[8]. Advanced or specialized roles require even more extensive experience. For instance, the FBI prefers forensic accountants to have three to five years of experience in fields such as public accounting, internal audit, or forensic audit[1]. For Digital Forensic Examiner positions, the FBI may accept four years of full-time professional experience in digital forensics as a substitute for a bachelor’s degree[1].
To stand out, candidates should highlight hands-on investigative skills, such as participating in Capture The Flag challenges on platforms like CyberDefenders[2].
sbb-itb-bf7aa6b
Digital Forensics Analyst Job? | Salary, Certifications, Skills & Tools, Bootcamp, Education, etc.
Required Certifications for Cleared Forensic Analysts
Once you’ve established a strong educational and practical foundation, certifications are the next step to proving your expertise in sensitive investigations. For cleared roles, certain credentials stand out because they align with Department of Defense (DoD) workforce standards and validate your ability to operate in high-stakes scenarios.
GCFA (GIAC Certified Forensic Analyst)
The GCFA is often considered the "gold standard" for advanced digital forensics and incident response [9][10]. It prepares professionals to tackle sophisticated threats and data breaches across both Windows and Linux platforms, with a particular focus on threat hunting.
The exam includes 82 questions, a 3-hour time limit, and requires a passing score of 71% (as of March 18, 2023) [9]. It features a CyberLive environment where candidates perform real-world tasks using programs, code, and virtual machines [9][11]. This hands-on approach ensures that candidates demonstrate both practical and theoretical expertise. Rob Lee from the SANS Institute highlights the critical need for skilled professionals:
We need lethal digital forensics experts who can detect and eradicate advanced threats immediately. A properly trained incident responder could be the only defense your organization has left during a compromise. [9]
The GCFA is recognized by the DoD Credentialing Opportunities On-Line (DoD COOL) and is accredited by the ANSI National Accreditation Board under ISO/IEC 17024 [10][13]. The exam costs $999, with renewal fees of $499 every four years [9][10]. GCFA-certified professionals earn an average base salary of $106,000 per year, with consulting roles reaching up to $130,000 [12].
CCFP (Certified Cyber Forensics Professional)
The (ISC)² CCFP takes a broader approach, covering the entire forensics lifecycle from discovery to reporting [12]. While the GCFA focuses on advanced system-level forensics and incident response, the CCFP emphasizes managing investigations in a way that’s both legally sound and court-defensible. This certification is particularly useful for cleared professionals who need to ensure the integrity of their findings.
Additional Certifications
Other certifications can also help bolster your credentials:
- GIAC Certified Forensic Examiner (GCFE): Specializes in Windows forensic analysis, including areas like the Windows Registry, USB device analysis, and email forensics. It’s tailored for federal agents, media exploitation analysts, and law enforcement officers working with Windows-based systems. A 70% score is required to pass, and GCFE-certified professionals earn between $86,000 and $108,162 annually [10][11].
- Computer Hacking Forensic Investigator (CHFI): Validates expertise in core digital forensics skills like forensic imaging and chain-of-custody procedures [2].
- EnCase Certified Examiner (EnCE): Focuses on proficiency with EnCase, a widely used forensic software tool in government investigations [2].
- CompTIA Security+: Covers cybersecurity fundamentals and incident response basics, making it a great starting point for those new to the field [2].
Before committing to costly certifications, consider gaining experience with open-source tools such as Autopsy, FTK Imager, and Volatility [2]. Document your work on forensic challenges through platforms like CyberDefenders to build a portfolio that demonstrates your practical skills [2]. Since SANS training and GIAC exams can cost between $8,000 and $10,000, look into employer sponsorship or DoD Credentialing Assistance if you’re in the military [10][12]. With the right certifications in hand, you’ll be well-positioned to compete in the job market, as discussed in the next section.
Technical Skills and Tools
To excel as a cleared forensic analyst, technical expertise is a must. While certifications and experience lay the groundwork, hands-on skills set top-tier professionals apart. Proficiency in investigative techniques and specialized tools is essential, spanning everything from traditional hard drives to modern cloud platforms. These capabilities ensure compliance with strict clearance protocols often required in sensitive government investigations.
Core Technical Skills
At the heart of forensic analysis lies data acquisition. Analysts must create exact, forensically sound copies of data using write blockers and validated tools, followed by integrity verification with cryptographic hashes like MD5 or SHA256. Skipping this step can make evidence inadmissible in court or government proceedings.
File system analysis is another cornerstone skill. Analysts need a thorough understanding of file systems such as NTFS, ext4, APFS, and FAT32 to uncover critical artifacts. This includes examining registry hives, event logs, and browser histories. Memory forensics is equally vital, focusing on volatile data in RAM to identify running processes, network activity, and malicious code that might never touch a hard drive. Meanwhile, network forensics involves analyzing packet captures, flow data, and firewall logs to trace intrusions and detect data breaches.
Programming knowledge is increasingly indispensable. As Raymond Musumba, CFE, puts it:
A strong foundation in programming is essential for computer forensic investigators… It helps professionals understand how software and scripts operate, identify suspicious code, and even recover deleted or hidden data [14].
Python stands out as a valuable tool for automating repetitive tasks and creating custom solutions for investigations.
Another critical skill is correlating timestamps from metadata, logs, and other artifacts to establish a clear timeline. This ability is crucial for presenting findings in a way that attorneys, executives, or juries can understand without sacrificing technical accuracy [2]. The Bureau of Labor Statistics anticipates a 13% growth in jobs for forensic science technicians between 2024 and 2034, with around 2,900 openings annually [6].
Mastering these skills sets the stage for effectively leveraging the right tools during investigations.
Forensic Tools
Starting with open-source tools is a great way to build foundational skills before moving on to advanced commercial platforms. For example:
- Autopsy: A free tool for comprehensive file system and artifact analysis.
- FTK Imager: Ideal for forensic imaging and data acquisition.
- Volatility and Volatility Workbench: Widely used for memory forensics.
- KAPE (Kroll Artifact Parser and Extractor): Speeds up triage across large datasets to pinpoint key evidence.
For more advanced needs, commercial tools like EnCase and Magnet AXIOM offer robust capabilities, particularly suited for government and law enforcement work. These platforms, along with tools like Plaso for timeline reconstruction, help analysts meet the stringent standards of cleared environments.
As cloud adoption grows, analysts increasingly deal with APIs and snapshots from services like AWS, Azure, and GCP instead of relying solely on physical imaging. Mobile forensics has also become crucial, requiring expertise in extracting data from iOS and Android devices, including encrypted apps and location histories.
Finally, meticulous documentation is non-negotiable. Real-time notes and screen captures during analysis ensure findings can be reproduced by another examiner. Even a small lapse in the chain of custody can jeopardize an entire investigation.
Job Market and Salary Information
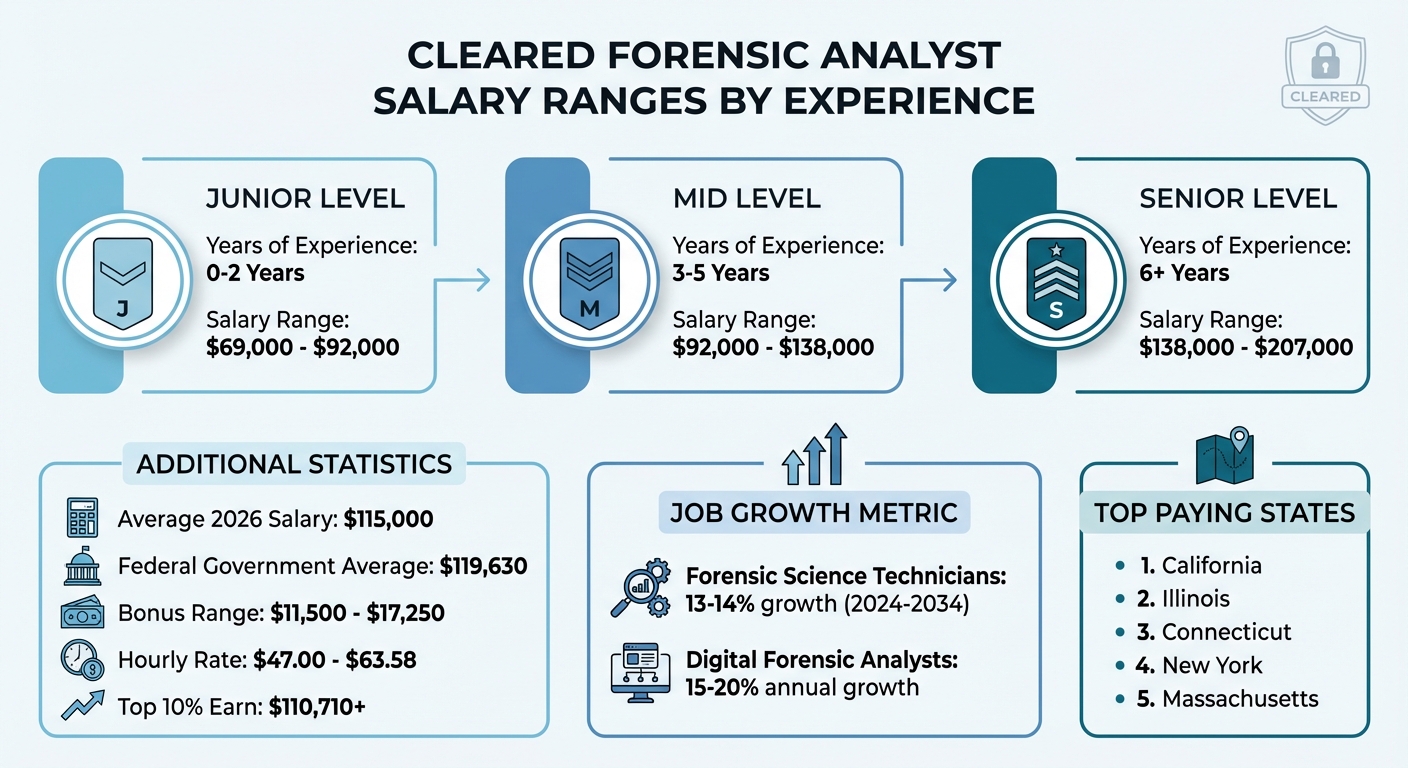
Cleared Forensic Analyst Career Path: Salary Ranges by Experience Level
Demand for Cleared Professionals
Building on the qualifications and certifications mentioned earlier, the job market for cleared forensic analysts is thriving. Employment for forensic science technicians is expected to grow by 13%-14% between 2024 and 2034 [15][6]. Meanwhile, the demand for digital forensic analysts is projected to climb even higher, with annual growth rates of 15%-20% driven by the surge in cybercrime [15][18].
Security clearances are now a baseline requirement for many federal roles, particularly in agencies like the FBI, DEA, and ATF. The process to obtain clearance is rigorous, as highlighted by the UC Davis Master’s Program in Forensic Science, which advises:
If you are seeking employment in forensic science do not use drugs, do not break the law, and do not have bad credit [16].
Geography plays a major role in job availability. California leads the nation with 2,050 forensic technicians employed, followed by Florida (1,420) and Texas (1,100) [15][17]. Virginia and Maryland, with 430 and 420 positions respectively, benefit from their proximity to Washington, D.C., home to numerous federal agencies and contractors [17]. Areas in the Northeast and along the West Coast also offer strong opportunities due to their concentration of federal agencies and specialized forensic labs [15].
This high demand translates into competitive salaries, as detailed below.
Salary Ranges by Experience and Location
The salary landscape for cleared forensic analysts underscores the value of experience and location. By 2026, the average annual salary for a digital forensics analyst in the United States is projected to reach $115,000 [18]. Federal government roles often pay a premium, with an average annual salary of $119,630, compared to $73,860 for local government positions and $69,540 for state government roles [16].
| Experience Level | Years of Experience | Salary Range (Annual) |
|---|---|---|
| Junior | 0-2 Years | $69,000 – $92,000 |
| Middle | 3-5 Years | $92,000 – $138,000 |
| Senior | 6+ Years | $138,000 – $207,000 |
Additional compensation can include bonuses ranging from $11,500 to $17,250, and hourly rates typically fall between $47.00 and $63.58 [18]. Remote work is also widely available in this field [18]. The top 10% of forensic science technicians earn more than $110,710 annually [6], with the highest-paying states being California, Illinois, Connecticut, New York, and Massachusetts [16].
How to Secure Cleared Forensic Analyst Positions
Resume Optimization
Your security clearance is a major advantage when applying for cleared forensic analyst roles. Make sure it stands out by placing it prominently in your resume – either in the summary or a dedicated section. Since recruiters typically spend less than a minute reviewing resumes[19], this visibility can make all the difference.
Be specific about your clearance details: include the level, granting agency, and current status. Trevor Richfield, a Career Coach and Professional Resume Writer, emphasizes:
Putting security clearance on your resume is an important step in making yourself a competitive candidate for positions requiring access to sensitive information.[3]
When describing your experience, focus on measurable achievements rather than generic job duties. For instance, instead of saying "performed digital forensics", highlight results like "identified the root cause of a data breach within 48 hours" or "recovered critical evidence in 20+ investigations." Group your technical skills into clear categories such as:
- Forensic Tools: EnCase, FTK, Autopsy, Volatility
- Operating Systems: Windows, Linux, MacOS
- Programming Languages: Python, C++
Tailor your resume to the job description by incorporating relevant keywords like "incident response", "chain of custody", and "timeline reconstruction." This approach not only strengthens your resume but also helps it pass applicant tracking systems.
If you’re light on professional experience, consider including volunteer work, case studies, or personal projects. Linking to forensic write-ups or contributions to open-source tools like Volatility adds credibility to your skills. Use your clearance to position yourself as ready to handle sensitive and high-stakes investigations.
This solid resume framework will set you up for success in the interview process.
Interview Preparation
Interviews for forensic analyst roles require you to explain complex processes in a way that’s easy to understand. Be ready to discuss the entire digital evidence lifecycle – from identifying and preserving evidence to analyzing and reporting findings.
Thomas W. Adair, a retired Senior Criminalist from the Westminster Police Department, advises:
Your knowledge base must mirror your resume.
He also notes:
Oral boards like to ask questions such as, ‘What can you tell us about our agency?’[20]
Given the competitive nature of forensic science positions, with hundreds of applicants for each role[20], thorough preparation is critical.
Be transparent about your clearance during the interview. As the UC Davis Master’s Program in Forensic Science points out:
Be honest during the application process – some agencies might overlook prior mistakes… but dishonesty during the process will disqualify an applicant.[16]
If you’re stumped by a technical question, admit it rather than guessing. Employers value honesty, especially in roles that require high levels of trust.
Bring a professional portfolio to showcase your expertise. Include redacted forensic reports, investigation methodologies, and technical write-ups. Be ready to explain how you maintain the chain of custody, conduct unbiased analyses, and ensure that your findings are legally admissible. Demonstrating this level of preparation will help you stand out.
Using Cleared Cyber Security Jobs
Cleared Cyber Security Jobs is a platform tailored specifically for professionals with active security clearances. Its tools allow you to filter job listings by clearance level, location, and forensic specialization, ensuring you only see roles you’re qualified for.
Uploading your resume to the platform’s database gives employers direct access to your profile. You can also set up job alerts for new forensic analyst openings. Additionally, the platform hosts job fairs where you can connect with hiring managers from federal agencies and defense contractors, making the hiring process more direct.
Since an active clearance can speed up your job search[3], using a platform dedicated to cleared professionals helps you target roles that align with your expertise and credentials efficiently.
Conclusion
Pursuing a career as a cleared forensic analyst requires a combination of specialized certifications, advanced technical expertise, and an active security clearance. Certifications like GCFE and GCFA, which align with DoD standards, demonstrate your qualifications to potential employers[13]. Mastery of areas such as file systems, memory analysis, and timeline reconstruction is key to excelling in this field. A security clearance further opens doors to impactful roles within organizations like the FBI, Secret Service, and Department of Defense[2]. Together, these elements position you strongly in an ever-growing job market.
The increasing prevalence of cybercrime continues to drive demand for forensic analysts. Having both verified credentials and a security clearance gives you a distinct edge in securing roles that require a high level of trust and expertise.
To thrive in this field, prioritize ongoing education. As technology evolves, so do forensic techniques and tools. Operating systems and applications are constantly updated, introducing new digital artifacts to analyze. Stay ahead by reading DFIR blogs, participating in CTF challenges, and building a portfolio that showcases your hands-on experience[2].
As emphasized throughout this guide, maintaining your clearance, updating certifications, and refining your technical skills are essential for long-term success. The demand for skilled forensic analysts remains strong, and those who commit to continuous growth will find a wealth of opportunities in digital forensics.
FAQs
How do I get a security clearance for forensic analyst roles?
To obtain a security clearance, you’ll need to navigate the U.S. government’s process, which involves several key steps: completing an application, undergoing a thorough background check, and having various factors assessed – such as your criminal history, financial records, and personal conduct. Generally, this process is started by your employer or sponsor if the role you’re pursuing requires clearance. Properly showcasing your clearance on your resume can also boost your prospects for positions that demand heightened security awareness.
Which certification should I get first: Security+, GCFE, or GCFA?
Begin with Security+ to establish a solid understanding of cybersecurity fundamentals. This certification covers the essential principles and practices needed to navigate the cybersecurity landscape effectively. Once you’ve got the basics down, consider advancing to certifications like GCFE or GCFA. These are tailored for professionals aiming to specialize in digital forensic analysis, equipping you with in-depth skills for conducting forensic investigations and handling complex cases.
What projects can I do to prove DFIR skills without job experience?
If you’re looking to showcase your Digital Forensics and Incident Response (DFIR) skills but lack formal work experience, practical projects are a great way to start. For example, you can try building tools like a keylogger, developing a backdoor, or creating a port scanner. These hands-on activities not only teach you technical skills but also demonstrate your ability to tackle real-world challenges.
Platforms like TryHackMe and HackTheBox are excellent for practicing. They offer scenarios where you can analyze filesystems, logs, and memory to uncover forensic details. By diving into these exercises, you’ll strengthen essential skills such as malware analysis and evidence collection.
The best part? These projects and platforms allow you to build a portfolio that highlights your capabilities, even if you haven’t had formal DFIR job experience yet.
