If you’re an IT Information Systems Technician, transitioning into cleared cybersecurity roles can significantly boost your career prospects. Cybersecurity jobs are growing rapidly, with over 514,000 openings projected in the U.S. by 2026, and many remain unfilled. Cleared roles, which require security clearance, offer higher salaries – 20% to 40% more than commercial roles – and unmatched job stability. Here’s what you need to know:
- Key Benefits: Higher pay (up to $1.3M more over a career), mission-focused work tied to national security, and recession-resistant opportunities.
- Skills Transfer: Your IT skills in networking, system administration, and troubleshooting are directly applicable to cybersecurity.
- Certifications: Start with CompTIA Security+ (mandatory for many roles) and consider advanced options like CISSP for higher-level positions.
- Clearance Process: You’ll need sponsorship from a federal agency or contractor to apply for clearance, with levels like Secret and Top Secret offering increasing access and earning potential.
- Job Search Tips: Focus on cleared job boards, network at industry events, and tailor your resume to emphasize security-related experience.
With your IT foundation, certifications, and a security clearance, you’ll be well-positioned to enter this high-demand field.
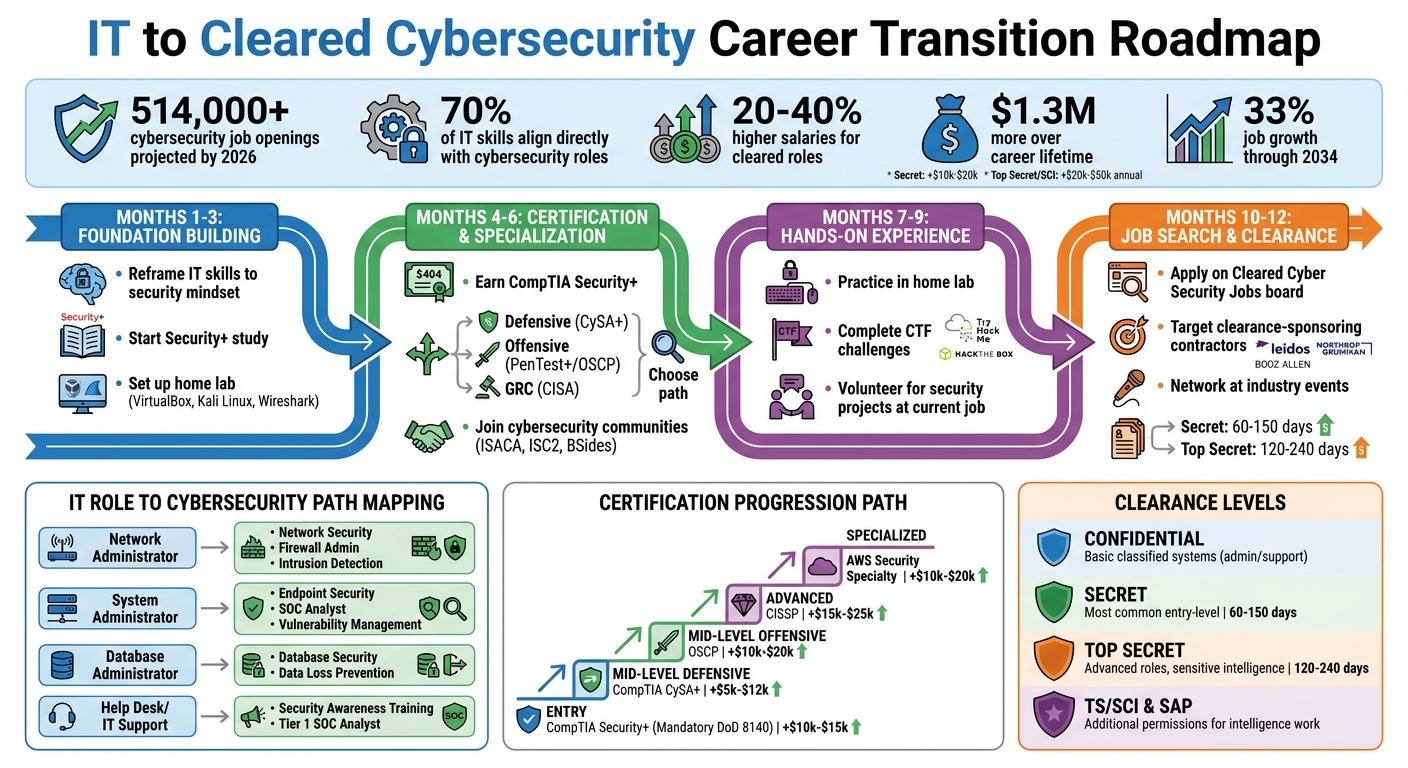
IT to Cleared Cybersecurity Career Transition Roadmap
8570: How Best to Navigate Security Cleared Cybersecurity Certifications
sbb-itb-bf7aa6b
Using Your IT Experience in Cybersecurity
If you have an IT background, you’re already ahead of the game when stepping into cybersecurity. Around 70% of IT skills align directly with cybersecurity roles [9], meaning you’re not starting from scratch – you’re building on a solid foundation.
The shift, however, lies in your mindset. As John Berti, Co-founder of Destination Certification, puts it:
"The most significant shift for many IT professionals is moving from an operational mindset to a security mindset." [1]
In IT, the focus is on uptime and performance. In cybersecurity, while these still matter, you also weigh protection and risk. It’s no longer just about asking, "Does it work?" but also, "Is it secure?"
IT Skills That Transfer to Cybersecurity
Your existing IT expertise can translate seamlessly into cybersecurity. For instance:
- Networking knowledge: Concepts like TCP/IP, the OSI model, routing, switching, and firewalls are directly applicable to roles in network security, intrusion detection, and VPN management. If you’ve configured firewalls or resolved network issues, you already understand data flow and potential vulnerabilities.
- System administration: Experience with Active Directory, Windows/Linux systems, and patch management prepares you for roles in identity and access management (IAM) and endpoint security. Knowing how systems operate gives you the tools to secure them.
Here’s how some common IT roles align with cybersecurity paths:
| Current IT Role | Best-Fit Cybersecurity Path |
|---|---|
| Network Administrator | Network Security, Firewall Admin, Intrusion Detection |
| System Administrator | Endpoint Security, SOC Analyst, Vulnerability Management |
| Database Administrator | Database Security, Data Loss Prevention |
| Help Desk / IT Support | Security Awareness Training, Tier 1 SOC Analyst |
To stand out, reframe your IT experience in security terms. For example, instead of saying "managed Active Directory", describe it as "maintained Identity and Access Management (IAM) systems." Replace "performed system updates" with "executed vulnerability and patch management processes."
Adding Cybersecurity-Specific Knowledge
Once you’ve identified your transferable skills, the next step is to build on them with cybersecurity-specific tools and techniques. This includes:
- Mastering tools: Gain hands-on experience with SIEM tools (e.g., Splunk, Elastic), vulnerability scanners (e.g., Nessus), and packet analysis tools like Wireshark.
- Learning scripting languages: Python, PowerShell, or Bash can help you automate repetitive tasks and improve efficiency.
- Exploring security frameworks: Familiarize yourself with NIST CSF, ISO 27001, and other frameworks to understand industry standards.
Setting up a home lab is a great way to practice. Use VirtualBox or VMware to install tools like Kali Linux for penetration testing or Security Onion for intrusion detection. Platforms like TryHackMe, Hack The Box, and PicoCTF offer practical challenges to sharpen your skills.
In your current IT role, look for opportunities to get involved in security-related projects. Tasks like implementing multi-factor authentication (MFA), hardening servers, monitoring network traffic, or leading phishing awareness initiatives not only build experience but also show initiative to potential employers.
Finally, connect with the cybersecurity community. Join organizations like ISACA or (ISC)², and attend BSides events to network with seasoned professionals and gain valuable insights.
With IT professionals who understand both technology and security in high demand, your background gives you an edge. And with entry-level roles like Incident and Intrusion Analysts offering an average salary of $101,130 [7], diving into cybersecurity is a move that can pay off significantly.
How to Get a Security Clearance
You can only apply for a security clearance if you’re sponsored by a federal agency or a cleared contractor after receiving a conditional job offer [11]. In other words, securing the right job is your first step toward entering the world of cleared cybersecurity.
The Department of Defense (DoD) oversees more than 80% of all U.S. government security clearances [13]. For most IT professionals, this means navigating DoD-related processes. Once sponsored, you’ll complete your application through eApp, the online system that replaced the older e-QIP platform in 2026 [5]. Let’s break down the clearance levels and the steps involved in the process.
Security Clearance Levels Explained
There are three primary clearance levels, each linked to the level of risk unauthorized disclosure poses to national security:
- Confidential: The lowest level, covering information that could cause "damage" to national security. This is often needed for administrative or support IT roles dealing with basic classified systems [10][11].
- Secret: Covers information that could cause "serious damage." It’s the most common level for entry-level cybersecurity roles, especially those involving defense contracts or military networks [10][12].
- Top Secret (TS): Grants access to information that could cause "grave damage" to national security. This is required for advanced roles, such as working with sensitive intelligence or high-security systems [10][12].
In addition, there are Sensitive Compartmented Information (SCI) and Special Access Programs (SAP). These aren’t separate clearance levels but additional permissions for those with Top Secret clearance. SCI relates to intelligence work, while SAP involves covert defense projects – both critical for roles like cyber threat intelligence analysis or research on defense systems [10][5].
A Top Secret clearance can significantly boost your earning potential, with average annual salaries reaching $119,000 compared to $92,000 for those with Secret clearance [13]. However, keep in mind that having clearance doesn’t grant unrestricted access. You’ll also need a specific "need-to-know" for any classified information you handle [11].
The Clearance Application Process
The application process involves a tiered investigation system: Tier 3 for Secret clearances and Tier 5 for Top Secret and SCI [5]. Your employer will start the process and give you access to eApp, where you’ll complete Standard Form 86 (SF-86). This form asks for extensive details about your employment history, residences, foreign contacts, financial records, and personal conduct.
To prepare, gather information like 10 years of residence addresses, contact details for references, and financial records. Financial issues are the leading reason for clearance rejections [11], so check your credit report and address any delinquencies with documented repayment plans [5].
Government processing goals are 40 days for Secret clearances and 75 days for Top Secret [10]. However, in early 2026, actual timelines ranged from 60–150 days for Secret (Tier 3) and 120–240 days for Top Secret (Tier 5). If your clearance involves a polygraph – common for Top Secret/SCI roles – the process could take 180–365+ days due to appointment backlogs [5]. Interim Secret clearances are often issued within 10–30 days based on initial automated checks, allowing you to begin work while the full investigation continues [5].
Adjudicators review your application using the "whole-person concept", which considers 13 guidelines such as financial responsibility, foreign influence, and personal conduct [5][13]. Financial problems account for about 40% of Department of Navy clearance denials, while dishonesty on applications makes up about 15% [13].
"Omitting required information or lying on this form is itself a serious issue… and can lead to clearance denial or even criminal charges if it’s a deliberate false statement."
– National Security Law Firm [14]
Be honest and thorough. If you realize you’ve left something out after submitting your application, notify your investigator or security officer right away. Taking responsibility for mistakes is seen as a positive trait [14]. Once approved, keeping your clearance active is just as important as obtaining it.
How to Keep Your Security Clearance Active
In 2026, the Trusted Workforce 2.0 framework replaced periodic reinvestigations with Continuous Vetting (CV), an automated system that monitors criminal, financial, and public records [10][5]. As of early 2026, more than 3.8 million cleared personnel were enrolled in the CV program [10].
Under Continuous Vetting, you must report significant life events to your Facility Security Officer (FSO) immediately. These include arrests, major debts, foreign contacts, or foreign travel. Arrests or criminal charges, for instance, must be reported within 72 hours, no matter the outcome [13].
Cybersecurity professionals face extra scrutiny. Adjudicators often review publicly available social media, GitHub contributions, and even gaming interactions to evaluate judgment and operational security awareness [5]. Before applying, review your social media privacy settings and clean up old posts or contributions that might raise questions.
Maintaining good credit, avoiding unpaid debt, and filing taxes on time are essential throughout your career. The 2026 National Defense Authorization Act (NDAA) extended the eligibility window for clearance holders from 24 months to five years, making it easier to transition between cleared roles without restarting the process [10].
"A clearance is a privilege, not a right – even once you have one, you must follow strict rules in handling classified materials, or you can lose it."
– National Security Law Firm [14]
Mishandling classified materials can lead to criminal charges, job loss, or fines [10]. Treat your clearance as a critical career asset. It opens doors to roles like managing classified networks (e.g., SIPRNet), analyzing sensitive threat data, and working in secure environments like AWS GovCloud or Microsoft Azure Government [5]. Keeping your clearance active is as crucial as earning it in the first place.
Certifications for Cleared Cybersecurity Jobs
In the world of cleared cybersecurity, certifications aren’t just nice to have – they’re essential. They demonstrate your technical skills and ensure you meet the Department of Defense (DoD) 8140 requirements, which are necessary for many government and contractor roles [6][15]. Among certification providers, ISC2 stands out, covering 85% of the 54 approved DoD work roles – more than any other organization [15]. However, hiring managers often recommend focusing on earning one key certification and gaining hands-on experience instead of collecting multiple credentials without practical application [2].
Starting with Security+
For those breaking into cleared cybersecurity, CompTIA Security+ is the go-to first certification. It’s mandatory for baseline DoD 8140 roles at federal agencies and with cleared contractors [6]. The exam costs $404, but it can increase your salary by an estimated $10,000–$15,000 [6].
If you already have IT experience, you’re likely familiar with core cybersecurity concepts like data transfer, troubleshooting under pressure, access control, and system updates [1]. By reframing your current tasks – such as managing Active Directory as part of Identity and Access Management (IAM) or handling updates as Vulnerability and Patch Management – you can highlight your transferable skills [1].
Security+ is designed to bridge IT operations and cybersecurity basics. If your IT background is limited, consider starting with CompTIA A+ and Network+ to build foundational knowledge in hardware, operating systems, and networking [17][6]. A solid grasp of networking principles, such as TCP/IP and routing, is critical before diving into Security+ [16][6].
For active-duty military personnel and veterans, programs like COOL (for Air Force, Marine Corps, and Navy) or the Post-9/11 GI Bill can help cover exam fees and training costs [15]. Once you obtain Security+, you’ll qualify for roles with cleared contractors, including companies that sponsor security clearances like Leidos, Booz Allen, and Northrop Grumman [6].
Advanced Certifications: CISSP and Others
If you’re aiming for higher-level roles, the Certified Information Systems Security Professional (CISSP) is a standout choice. This certification focuses on management and architecture skills and requires years of operational experience [1][2]. At $749, it’s a significant investment, but it can boost your salary by $15,000–$25,000 [2].
Your next certification should align with your career goals. For defensive roles, such as incident detection and response, CompTIA CySA+ is a solid option at $404 [6][17]. If offensive roles like penetration testing or ethical hacking appeal to you, consider CompTIA PenTest+ ($404) or the Offensive Security Certified Professional (OSCP), which costs $1,499 [2][17]. For those interested in governance, risk, and compliance (GRC), the Certified Information Systems Auditor (CISA) is a must-have [6].
Some certifications come with heftier price tags. The GIAC Security Essentials (GSEC) costs $2,499 and is highly regarded in the Intelligence Community [6]. Similarly, the Certified Ethical Hacker (CEH) is priced at $1,199, while the AWS Security Specialty certification, ideal for AWS GovCloud engineering roles, costs $300 [2].
Looking ahead, the SecAI+ certification is gaining traction for professionals with 3–4 years of experience. This certification focuses on securing AI-enabled tools and is a logical next step for those who already hold Security+ or CySA+ and want to address AI-related threats [17]. With these advanced certifications, you can chart a clear path for career growth.
Certification Roadmap for IT Technicians
Whether you’re just starting out or looking to advance, having a roadmap can simplify your journey. If you’re new to IT, begin with A+ and Network+ to establish a solid foundation [17][6]. Then, move on to Security+, which is essential for DoD 8140 roles [6].
Once you’ve earned your baseline certification, target roles with cleared contractors while specializing in your area of interest. For defensive roles, pursue CySA+; for offensive roles, aim for PenTest+ or OSCP; and for GRC roles, focus on CISA [6]. At the advanced level, CISSP offers the best return on investment for management and high-level engineering roles [2]. Alternatively, SecurityX (formerly CASP+) is ideal for those who prefer hands-on technical architecture roles [17].
| Career Stage | Recommended Certification | Primary Benefit | Salary Impact (Est.) |
|---|---|---|---|
| Entry/Baseline | CompTIA Security+ | DoD 8140 Mandatory | +$10,000–$15,000 [6] |
| Mid (Defensive) | CompTIA CySA+ | SOC/Analyst Roles | +$5,000–$12,000 [2] |
| Mid (Offensive) | OSCP | Penetration Testing | +$10,000–$20,000 [2] |
| Advanced | CISSP | Management/Architecture | +$15,000–$25,000 [2] |
| Specialized | AWS Security | GovCloud Engineering | +$10,000–$20,000 [2] |
To stand out, complement your certifications with hands-on experience in a home lab. Tools like VirtualBox, Splunk Free, and Wireshark allow you to practice in a controlled environment [6]. Running systems like Kali Linux or Security Onion can help you apply your knowledge practically [1][6]. Documenting security-related tasks – such as server hardening or monitoring network traffic – can also serve as compelling evidence of your skills during interviews [1]. Combining certifications with practical experience ensures you’re well-prepared for a thriving career in cleared cybersecurity.
Finding Cleared Cybersecurity Jobs
Making the leap from IT to cleared cybersecurity requires more than just technical know-how; it demands a thoughtful plan for navigating the job market. With your IT and cybersecurity background, the next step is finding the right position in this growing field. The cleared cybersecurity market is thriving, with projections of over 514,000 job postings by 2026 – a 12% increase from previous years. However, about 26% of these positions remain open, offering plenty of opportunities for professionals looking to transition [2].
Finding Jobs on Cleared Cyber Security Jobs
Cleared Cyber Security Jobs is a specialized job board created with security-cleared professionals in mind. Unlike general job sites, it exclusively lists roles that require active clearances, ensuring that every position aligns with your qualifications.
To get started, complete your profile with your key skills and preferred locations. You can set your status to Active or use Anonymous mode for privacy. The platform also allows you to block specific employers from accessing your profile.
Use the site not only to apply for jobs but also to research the market. By browsing thousands of listings, you can identify in-demand skills and discover which contractors are hiring. Setting up Job Agents will automate your search, sending you email alerts when positions matching your criteria become available. When searching, use a ZIP code and mileage radius instead of city names to avoid missing listings with different naming conventions (e.g., "St. Louis" vs. "Scott AFB").
Mastering Boolean search techniques can also improve your results. For example, use quotation marks for exact phrases like "Security Analyst" and connectors like "OR" to include variations (e.g., "SOC Analyst" OR "Cyber Analyst"). If you possess a Top Secret clearance, consider applying for Secret-level roles as well to broaden your options. Don’t forget to log in weekly and update your profile – many employers prioritize recently updated profiles [18].
While job boards are a powerful tool, networking and direct connections can open doors that online applications might not.
Networking and Job Fairs for Cleared Positions
Networking plays a crucial role in finding cleared cybersecurity jobs, as personal connections often lead to interviews and offers. The cleared community is close-knit, making relationships especially valuable. Attending job fairs – both in-person and virtual – can help you connect directly with defense and intelligence contractors. Conferences like BSides, Black Hat, DEF CON, and RSA also provide excellent opportunities to meet industry professionals. Casual conversations at these events can lead to meaningful connections, so make sure to follow up within 24 hours to keep the momentum going.
Smaller government contractors are often more flexible with requirements and may even sponsor initial clearances for promising candidates, so focus your networking efforts there. Also, optimize your LinkedIn profile to showcase your skills and clearance status. Participating in forums like Reddit’s r/netsec or Stack Overflow can further establish your expertise. Informational interviews with professionals already working in cleared roles can provide valuable insights and potential referrals. Volunteering at cybersecurity events or with local non-profits offers additional networking opportunities and practical experience [21].
As you expand your network, ensure your resume is tailored to highlight your clearance and technical skills.
Writing a Resume for Cleared Cyber Roles
Once you’ve refined your job search and networking strategies, your resume needs to clearly emphasize your clearance and technical abilities. Place your clearance level prominently at the top of the first page, either in your contact details or professional summary, to immediately signal your qualifications [19].
"Your security-cleared resume is not a biography or a mere list of qualifications. It’s an ad designed to help you land that coveted cleared job interview."
– Ashley Jones, Editor, ClearedJobs.Net [19]
Use the STAR method (Situation, Task, Action, Result) to turn generic job duties into impactful achievements. For instance, instead of saying you “conducted assessments,” specify the results: “Implemented proactive threat monitoring that reduced system vulnerabilities by 35%” [20].
Reframe your IT experience in security terms and include relevant keywords from job descriptions to ensure your resume passes Applicant Tracking Systems (ATS). Create a dedicated technical skills section, organizing tools, platforms, and certifications by category. Include certifications you’re working on, along with expected completion dates, to show your commitment to growth. Mention your clearance level in job titles or project descriptions when applicable (e.g., "Systems Technician (TS/SCI)").
Keep your resume concise – ideally one to two pages – and use a clean, simple format. Avoid graphics or heavy shading, as these can interfere with electronic scanning. Skip subjective self-descriptions in your summary and practice operational security (OPSEC) by listing only your clearance level on resumes submitted through cleared job boards. Avoid including classified project details, office sizes, or budgets, and don’t list clearance information on public profiles like LinkedIn. Additionally, leave out college graduation years and phrases like “30 years of experience,” which might unintentionally signal inflexibility to recruiters. Focus on showcasing the skills and experience that make you the right fit for the job you’re targeting.
Your Transition Plan
Now that you’ve explored the necessary skills, certifications, and job search strategies, it’s time to craft a plan that works for your life. This step-by-step approach will help you move forward with clarity and purpose.
Creating Your Transition Timeline
For most IT professionals, transitioning into cleared cybersecurity roles takes 6 to 18 months [1][6]. If you’re a network or system administrator, the process might be faster – 3 to 6 months – because your skill set already overlaps with cybersecurity. On the other hand, help desk and IT support professionals typically need 6 to 12 months to make the shift [3][4].
Your timeline should include both skill development and clearance processing. Start by identifying roles that align with your current expertise. For example:
- Network administrators might naturally move into network security or intrusion detection.
- System administrators are well-suited for SOC analyst or vulnerability management roles [1][9].
A 12-month roadmap could look like this:
- Months 1–3: Build your foundational knowledge.
- Months 4–6: Earn your Security+ certification and choose a specialization.
- Months 7–9: Gain hands-on experience through labs and Capture the Flag (CTF) challenges.
- Months 10–12: Start your job search.
Keep in mind that clearance processing will add time to your overall timeline. A Secret clearance typically takes 60 to 150 days, while a Top Secret clearance can take 120 to 240 days [5].
Some defense contractors, like Booz Allen, Leidos, and Northrop Grumman, are known to sponsor clearances for candidates who already hold a Security+ certification [6]. Target these companies early to get the clearance process underway while you continue building your skills.
Once your timeline is in place, the next challenge is balancing your current job with your transition efforts.
Managing Work While Preparing for Your Career Change
Balancing your current job with your transition requires careful time management. Aim to dedicate 10–15 hours per week to studying and practicing [8]. Here are some tips to make the most of your time:
- Use idle moments wisely: Listen to cybersecurity podcasts during your commute or read blogs during breaks [1].
- Study on your schedule: Take advantage of online courses and virtual labs, which are available 24/7 [22].
- Consider a focused study break: If you’re preparing for Security+, a one-week leave for an intensive bootcamp can be incredibly effective [1].
If possible, look for ways to gain security experience in your current role. Volunteer for tasks like:
- Server hardening
- Monitoring network traffic for unusual activity
- Leading phishing awareness campaigns [1][9]
These experiences not only enhance your skills but also give you concrete examples to discuss in interviews. Plus, they help you update your resume with security-focused terminology.
"Your transition from IT to cybersecurity isn’t a career change – it’s a career evolution. You’re not discarding your skills; you’re elevating them."
– John Berti, Destination Certification [1]
Keep practicing in your home lab to sharpen your abilities [1][9]. Document your progress with a personal blog or GitHub portfolio – recruiters in the cleared space value this initiative [9]. Finally, join online communities on platforms like LinkedIn, Discord, or Reddit to connect with mentors who can guide you through challenges [1][9].
Conclusion
Your IT background gives you a strong advantage in the ever-growing cybersecurity field. Transitioning from an IT Information Systems Technician to a cleared cybersecurity professional is a logical next step. Skills like networking, system administration, troubleshooting, and cloud infrastructure already align closely with cybersecurity demands [9]. The key steps ahead include earning your Security+ certification, adopting a security-first mindset, and securing a clearance sponsorship. With these pieces in place, you’ll be well-positioned to meet the market’s high demand for cleared cybersecurity experts.
The numbers speak volumes: over 500,000 cybersecurity roles remain unfilled in the U.S., and the field is expected to grow by 33% through 2034 [6]. Major defense contractors like Leidos, Booz Allen, and Northrop Grumman are actively sponsoring clearances for candidates who showcase initiative with certifications and hands-on experience [6]. On top of that, a Secret clearance can increase your annual salary by $10,000–$20,000, while a TS/SCI clearance can add $20,000–$50,000 [6].
"Your IT background isn’t just relevant – it’s a competitive edge. The cybersecurity field needs professionals who understand both technology and operations, and you’re already fluent in both." – John Berti, Co-founder, Destination Certification [1]
To make the most of your IT experience, reframe it using security-focused language. For example, replace "Managed Active Directory" with "Identity and Access Management (IAM)" on your resume. Building a home lab with tools like Splunk, Wireshark, or Kali Linux can further demonstrate your hands-on expertise. Platforms like Cleared Cyber Security Jobs can connect you with employers that sponsor clearances and value your IT foundation. Take the first step today and set yourself on the path to a rewarding career in cleared cybersecurity.
FAQs
What cleared cyber roles fit my current IT job best?
Your current IT experience can open doors to various cleared cybersecurity roles. For instance, if you’ve worked in system management or network administration, positions like Cleared Security Engineer or Cybersecurity Analyst could be a perfect fit. If your expertise includes managing security tools or performing system updates, you might consider roles such as Vulnerability Researcher or Security Engineer. For those just starting out, entry-level roles like Cybersecurity Technician or ISSO are great options, especially if you hold certifications like Security+ or CISSP.
What can stop me from getting a clearance?
Several things can stand in the way of getting a security clearance. These include unresolved financial problems, criminal behavior, substance abuse, or lying during the background check. The process is all about assessing your trustworthiness, reliability, and whether you pose any risks to national security. Even smaller concerns, like past illegal actions or associations that raise red flags, can affect your chances. Keeping a clean record and being completely honest throughout the process are key to gaining approval.
How do I get hands-on cyber experience before I’m cleared?
Gaining practical cybersecurity experience before obtaining clearance is absolutely possible. Start by creating a home lab – this allows you to practice security tasks in a safe and controlled setting. It’s a great way to tinker with tools, simulate attacks, and understand defensive strategies.
Another smart move is connecting with cybersecurity professionals. Networking can open doors to mentorship, advice, and even collaborative projects that help you build real-world skills.
Finally, consider earning certifications like Security+ or CISSP. These often come with hands-on labs, giving you a chance to develop practical expertise while showcasing your commitment and readiness for cybersecurity roles.
