Cleared Security Architects are highly specialized professionals responsible for designing secure systems that protect classified government data. These roles require security clearances like Secret or Top Secret and involve navigating federal compliance standards such as NIST 800-53 and FISMA.
Key Takeaways:
- Salary: Median pay is $223,000 annually.
- Demand: Information security analyst roles are projected to grow by 29% from 2024 to 2034.
- Clearance Levels: Secret, Top Secret, and TS/SCI are the most common clearance types, with timelines for approval ranging from 2 months to over a year.
- Required Certifications: CISSP is required in 80% of listings, along with others like CISM, TOGAF, and cloud-specific credentials.
- Core Skills: Expertise in Zero Trust Architecture, cloud platforms (AWS GovCloud, Azure Government), and compliance frameworks.
This guide outlines the career path, required skills, certifications, and strategies to secure these high-paying and impactful roles.
Cloud Security Architect Skills: Must-Know Technical Skills for Security Architect Careers
sbb-itb-bf7aa6b
What Cleared Security Architects Do
In the cleared sector, Security Architects play a pivotal role in safeguarding classified government information. Their work goes beyond just building secure systems – they also ensure compliance with strict federal standards. Operating at a strategic level, these professionals design security frameworks that not only protect sensitive data but also guide an organization’s approach to security from initial setup to ongoing operations [1][2].
Cleared Security Architects balance technical expertise with a strategic outlook. They spend about 25% of their time on architecture reviews and design sessions, another 20% in stakeholder meetings to translate technical risks into business terms for executives, and an additional 20% developing documentation and standards [2]. Their responsibilities also include evaluating new security technologies, taking into account integration challenges and long-term costs, all while ensuring alignment with federal compliance guidelines.
In cleared environments, architects must integrate Continuous Vetting (CV) processes – automated systems that track criminal records, credit activity, and foreign travel for cleared personnel in real time [4]. They also build secure infrastructures for classified networks like SIPRNet and use government-specific cloud platforms such as AWS GovCloud and Microsoft Azure Government [4].
Designing Secure Architectures
At the heart of their work is the implementation of Zero Trust Architecture – a model that assumes breaches are inevitable and focuses on continuous verification [2]. This approach includes strategies like micro-segmentation to isolate sensitive systems, continuous monitoring to detect anomalies, and robust identity verification for users and devices. This replaces outdated perimeter-based security models, which are less effective in today’s cloud-driven and remote work environments.
Another key responsibility is Security by Design. Architects embed security into every stage of the system development lifecycle (SDLC), from secure coding practices to early-stage threat modeling [2]. This proactive "shift-left" approach addresses vulnerabilities early, preventing issues from reaching production systems. Additionally, they assess new technologies to determine their operational fit, integration complexity, and long-term costs.
Compliance and Regulatory Responsibilities
Every decision a cleared Security Architect makes is influenced by federal compliance standards. They map system components to NIST controls, document how architectures meet FISMA requirements, and ensure any cloud services used are FedRAMP-authorized. A major focus is supporting the Trusted Workforce 2.0 initiative, which aims for seamless clearance reciprocity across federal agencies under the principle of "clear once, trusted everywhere" [4]. Architects must design systems that uphold this standard while meeting the unique security needs of various agencies.
This compliance-driven approach also shapes how monitoring systems are designed, ensuring they support effective and timely incident responses.
Monitoring and Incident Response
While architects don’t handle daily security operations, they lay the groundwork for effective monitoring and incident handling. They establish continuous monitoring frameworks to provide real-time insights into system health and security. This includes defining what data is logged, how long it is retained, and how alerts are routed to ensure swift action by security teams.
Architects also oversee penetration testing programs, working with red teams to uncover weaknesses before attackers can exploit them. When incidents occur, they analyze root causes to determine if adjustments to the architecture are needed. For example, they may evaluate whether micro-segmentation should be tightened or if identity verification processes require enhancement. These evaluations ensure that incidents lead to long-term architectural improvements, not just short-term fixes.
Clearance Levels and Federal Frameworks
For those in cleared Security Architect roles, understanding security clearances and federal frameworks isn’t just helpful – it’s essential. These elements dictate the systems you can access, the projects you’ll tackle, and the way you design solutions that align with government standards.
Types of Security Clearances
Security clearances are the backbone of compliance in government-related roles, especially when designing systems that meet strict federal requirements. These clearances come in three main levels, each corresponding to different degrees of access:
- Secret: The most common clearance level for defense contractors. It covers information that, if disclosed, could cause "serious damage" to national security. This is often the baseline for IT and engineering roles in defense work [5].
- Top Secret (TS): Required for accessing information that could cause "exceptionally grave damage" to national security. Senior architects working on critical national security programs often need this level [5].
- Sensitive Compartmented Information (SCI): A subset of Top Secret, this clearance deals with intelligence sources and methods. It requires additional screening, which may include polygraph tests [5].
As of 2025, over 4.2 million individuals, including government and contractor employees, hold security clearances across 80 executive branch agencies [5]. The timeline for obtaining a clearance varies by level: Secret clearances typically take 60 to 150 days, Top Secret can take 120 to 240 days, and TS/SCI may require 180 to 365 days or longer [4].
Higher clearance levels come with heightened responsibilities. These include designing systems for classified networks like SIPRNet, managing accredited systems as an ISSM (Information System Security Manager) or ISSO (Information System Security Officer), and working within government-only cloud environments [4].
Under the Trusted Workforce 2.0 initiative, the federal government has adopted Continuous Vetting (CV) as the standard by 2026. CV uses automated, real-time monitoring of criminal, financial, and travel records to replace periodic reinvestigations [4]. This approach, described as "clear once, trusted everywhere", simplifies clearance reciprocity across agencies. Additionally, a clearance remains active for 24 months after leaving a position, allowing for a smooth transition to a new sponsor within that timeframe [4].
Federal Frameworks You Need to Know
Beyond clearances, federal frameworks play a crucial role in shaping every decision Security Architects make. These frameworks ensure that systems meet strict government security and privacy standards:
- NIST 800-53: A comprehensive catalog of security and privacy controls that architects must map to system components [1].
- FISMA (Federal Information Security Management Act): This law mandates that government agencies and contractors implement risk-based security programs aligned with NIST guidelines. Architects must document how their systems meet FISMA requirements and ensure any cloud services used are FedRAMP-authorized, which standardizes security assessments for cloud providers working with federal agencies.
For roles in the intelligence community, ICD 503 (Intelligence Community Directive for Risk Management) is key. It governs how architects approach risk assessment and mitigation [1]. These frameworks influence everything from data classification and storage to monitoring system configurations and incident response strategies.
Mastering these frameworks doesn’t just enhance your technical skills – it positions you as a critical player in high-stakes, clearance-driven roles where precision and compliance are non-negotiable.
Required Skills and Certifications
Landing a cleared Security Architect role requires 7–10 years of experience in security, combining technical expertise, key certifications, and the ability to communicate complex risks to non-technical leaders effectively [2][6]. These roles demand a unique skill set tailored to environments where federal compliance and strategic security design come together.
Core Technical Skills
The technical foundation for this role involves mastering enterprise frameworks like TOGAF, Zachman, and SABSA. These frameworks help structure large-scale IT systems and align business processes with security controls [2]. Expertise in cloud security is critical, especially across platforms like AWS, Azure, and Google Cloud Platform, with a focus on their government-specific environments (e.g., AWS GovCloud, Azure Government) [2][4].
Proficiency in Zero Trust Architecture is essential, emphasizing continuous verification, micro-segmentation, and least privilege access [2]. You’ll also need strong Identity and Access Management (IAM) skills to design scalable identity architectures, including federation, single sign-on (SSO), and privileged access management (PAM) [2][7].
Another key area is Security by Design, which involves secure coding practices, threat modeling, and integrating security into CI/CD pipelines [2][7]. Skills in Python and PowerShell scripting are invaluable for automating tasks and developing custom security tools [7]. In fact, expertise in cloud security alone can boost your salary by over $15,000 [7].
Top Certifications for Cleared Security Architects
Certifications play a critical role in validating your expertise. The CISSP (Certified Information Systems Security Professional) is a staple in nearly 80% of Security Architect job listings, proving broad knowledge of security domains [2]. For those aspiring to management roles, the CISM (Certified Information Security Manager) focuses on governance, risk management, and leadership skills [8].
Specialized certifications like SABSA (Sherwood Applied Business Security Architecture) demonstrate your ability to design enterprise security programs [2]. Similarly, TOGAF (The Open Group Architecture Framework) is vital for understanding how large organizations structure IT systems [2]. Cloud-specific certifications, such as AWS Solutions Architect Professional, Azure Solutions Architect Expert, and Google Professional Cloud Architect, are increasingly important for leading secure cloud transformations [2].
| Certification | Primary Focus | Career Impact |
|---|---|---|
| CISSP | Broad Security Domains | Required for 80% of senior architect roles [2] |
| CISM | Management & Governance | Prepares for leadership positions [8] |
| SABSA | Architecture Methodology | Validates enterprise security design skills [2] |
| TOGAF | Enterprise Architecture | Structures large-scale IT systems [2] |
| Cloud Architect | AWS/Azure/GCP | Essential for secure cloud transformations [2] |
These certifications not only enhance your technical credibility but also position you for leadership opportunities.
Leadership and Communication Skills
Technical expertise is just one part of the equation. To truly excel, you need strong leadership and communication skills to bridge the gap between technical complexities and strategic business goals. Security Architects often spend about 20% of their time in stakeholder meetings and presentations, and another 10% mentoring junior team members [2].
Translating technical vulnerabilities into business terms is crucial. For example, you might need to explain risks in financial or operational terms to justify security investments to CISOs, CTOs, or board members. Stakeholder management is equally important, requiring you to build trust across teams with differing priorities. Rather than simply saying "no", you’ll need to offer secure solutions that align with business objectives.
In cleared environments, integrity and sound judgment are non-negotiable. Continuous Vetting processes require you to self-report events like arrests, significant financial issues, or international contacts to your Facility Security Officer [4]. Adjudicators also evaluate your digital footprint, including GitHub activity and professional networking profiles, to assess your operational security awareness and overall suitability for clearance [4]. Your online presence becomes a reflection of your reliability and adherence to the "grant of trust" that clearance entails.
Career Progression and Advancement
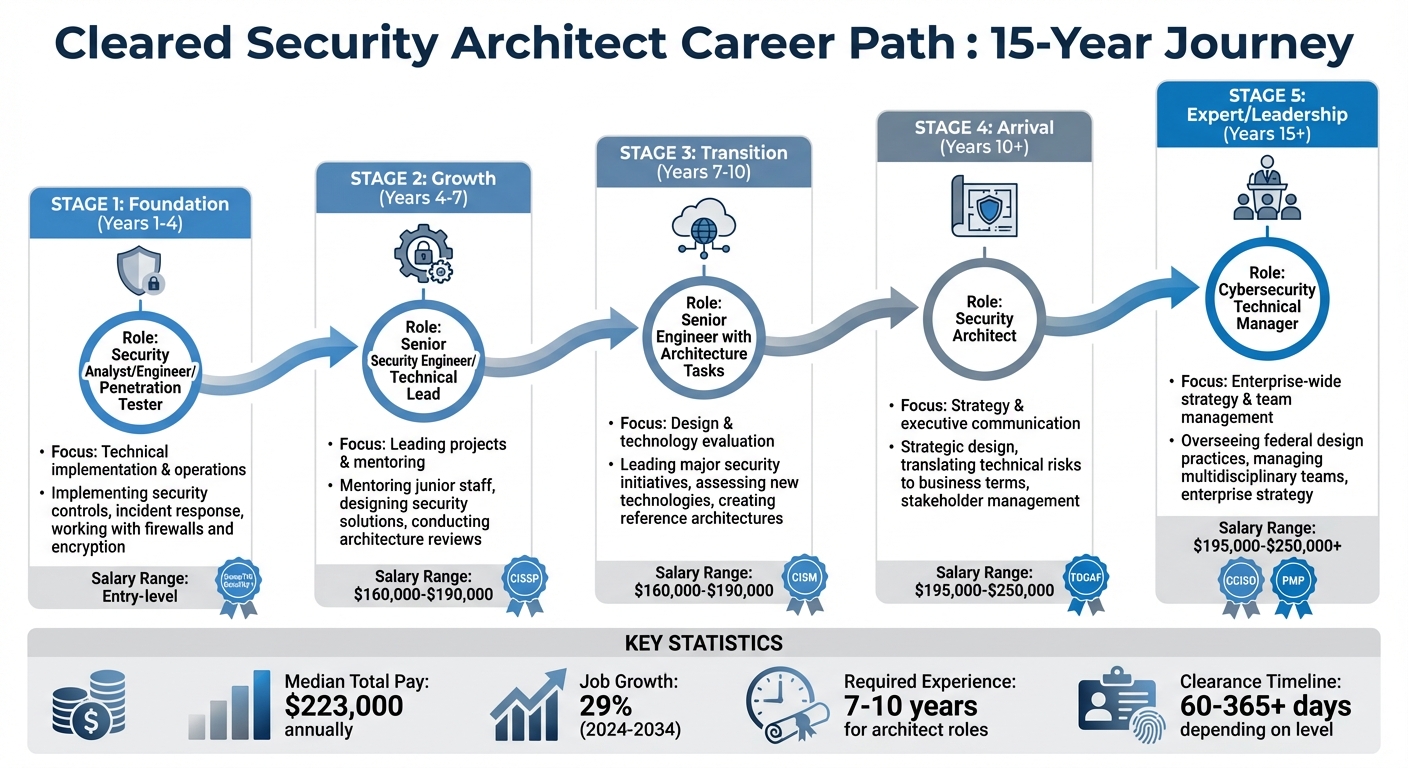
Cleared Security Architect Career Path Timeline and Salary Progression
Typical Career Path
Building a career as a cleared Security Architect is a journey that typically spans 10–15 years, starting with technical roles like Security Analyst, Engineer, or Penetration Tester. Along the way, you’ll develop a mix of technical expertise and federal compliance knowledge, gradually stepping into more strategic roles [2].
In the foundation stage (years 1–4), your focus is on mastering the basics – implementing security controls, responding to incidents, and working with tools like firewalls and encryption systems [2].
From years 4–7, as a Senior Security Engineer or Technical Lead, your responsibilities expand to include mentoring junior staff, designing security solutions, and conducting architecture reviews. This is when you start to shift from just configuring systems to understanding the reasoning behind their design [2].
In the transition stage (years 7–10), you may still hold senior engineering titles but begin taking on architecture-related tasks. These include leading major security initiatives, assessing new technologies, and creating reference architectures to guide teams. By the arrival stage (10+ years), you officially step into a Security Architect role, focusing on strategic design rather than hands-on implementation [2]. After 15+ years, senior roles like Cybersecurity Technical Manager emerge, where you oversee federal design practices and manage multidisciplinary teams [9].
| Career Phase | Typical Years | Key Focus Area | 2026 Salary Range |
|---|---|---|---|
| Foundation | 1–4 | Technical implementation & operations | Entry-level roles |
| Growth | 4–7 | Leading projects & mentoring | $160,000–$190,000 [2] |
| Transition | 7–10 | Design & technology evaluation | $160,000–$190,000 [2] |
| Arrival | 10+ | Strategy & executive communication | $195,000–$250,000 [2] |
| Expert/Leadership | 15+ | Enterprise-wide strategy & team management | $195,000–$250,000+ [2][9] |
At each stage, sharpening your expertise and leadership abilities becomes increasingly important.
Building Your Expertise
To advance in this field, you need a deep understanding of federal frameworks. Proficiency in NIST SP 800-53, NIST SP 800-37 (RMF), and Unified Facilities Criteria (UFC) is essential. These frameworks act as the backbone of cleared security architecture [9].
Creating a portfolio of your work is another critical step. While ensuring all classified or sensitive information is removed, document architecture diagrams, security standards, and frameworks you’ve designed. This sanitized portfolio provides tangible proof of your skills during interviews [2]. Taking on leadership opportunities, such as chairing an Architecture Review Board (ARB) or mentoring junior engineers, adds valuable strategic experience that hiring managers look for in senior candidates [2].
Under the Trusted Workforce 2.0 framework, maintaining your clearance through Continuous Vetting is non-negotiable. Adjudicators may review your online presence, including GitHub activity and professional networking profiles, so practicing strong operational security is crucial [4].
Transitioning from an engineering mindset to an architectural one means focusing on the big picture. Instead of just solving technical issues, you’ll need to align security solutions with business goals and communicate risks in terms that executives can understand. This ability to bridge technical details with strategic objectives is a key skill for leadership roles [8].
How to Find and Land Cleared Security Architect Jobs
Once you’ve built your skills and credentials, the next step is showcasing them effectively during your job search.
How to Write Your Resume for Cleared Roles
Start by listing your clearance level prominently at the top, alongside your name and contact details. In your technical summary, highlight measurable achievements and relevant certifications like CISSP or CISM. Use the STAR method (Situation, Task, Action, Result) to detail your accomplishments. For instance, instead of saying "improved security posture", specify how your redesign reduced incident response times by a certain percentage or helped secure a contract renewal [10].
Avoid vague language – be specific and focus on results.
Operational security is critical. Never include classified information or sensitive names on your resume. While you should list your clearance level on resumes submitted through secure channels, avoid posting it on public platforms like LinkedIn, as this could pose a security risk. Keep your resume concise – one to two pages – and use a simple format that works with Applicant Tracking Systems. Tailor your keywords to match each job description [10].
Once your resume is ready, it’s time to explore platforms tailored for cleared professionals.
Using Cleared Cyber Security Jobs to Find Opportunities
The Cleared Cyber Security Jobs platform is a great resource for finding roles. It allows you to filter job listings by clearance level, location, and specialization, connecting you directly with employers actively seeking cleared Security Architects. Upload your resume to boost visibility with hiring managers, and set up job alerts to stay updated on new opportunities that match your skills.
The platform also hosts job fairs, offering a chance to meet recruiters face-to-face, share your experience, and demonstrate your knowledge of federal frameworks. Beyond job postings, it provides resources for cleared professionals, including advice on maintaining your clearance and navigating transitions between agencies [4].
Once you’ve applied for roles, the next step is preparing for interviews.
Preparing for Interviews
Interviews for cleared Security Architect positions often test your ability to balance strategic vision with tactical execution. Be ready to explain your approach to designing security architectures and anticipating threats, rather than just focusing on tool configurations. Employers want to see that you can differentiate between creating a security framework and implementing it [1].
Showcase your expertise in frameworks like NIST 800-53, ISO/IEC 27001, and GDPR. Use the STAR method to provide examples of how you’ve aligned security strategies with business goals and communicated risks to non-technical stakeholders [1][10].
As AI becomes more integrated into security systems by 2026, expect questions about securing AI-powered tools and using AI for threat detection [3].
Throughout the interview, maintain strict operational security. Avoid mentioning classified projects or sensitive financial details. Instead, articulate your architectural vision in business terms and discuss how you’ve used automation tools like Python or PowerShell to enhance security [1][10].
Conclusion
Becoming a cleared Security Architect requires a mix of technical expertise and strategic insight, often gained over 7–10 years of experience[2]. A security clearance is not a permanent credential but rather a conditional trust tied to specific roles. Under the Trusted Workforce 2.0 framework launched in 2026, Continuous Vetting has replaced periodic reinvestigations, meaning your financial habits and online presence are now monitored in real time[4].
Success in this field goes beyond technical skills. Certifications like CISSP demonstrate your qualifications, while understanding frameworks like Zero Trust helps you communicate risks in terms that resonate with business leaders[2]. With information security analyst roles expected to grow by 29% from 2024 to 2034 and median total pay reaching $223,000 annually, the demand for cleared architects is strong and steady[1]. These qualifications not only open doors to top-tier roles but also highlight the need to protect your clearance throughout your career.
To maintain your clearance, report significant life events promptly and create a sanitized portfolio to showcase your design skills. Focus on states with cybersecurity talent shortages, such as Virginia, Maryland, Texas, and California, to enhance your job prospects[1].
Plan career moves carefully, as clearance becomes inactive 24 months after leaving a sponsored position[4]. Expanding your knowledge in cloud platforms like AWS GovCloud and frameworks such as TOGAF and SABSA can qualify you for senior roles offering salaries between $195,000 and $250,000 annually[2]. While this career path demands ongoing education and strict operational security, it offers strategic influence and highly competitive compensation.
FAQs
Can I get hired as a cleared Security Architect without already having a clearance?
Most of the time, no. Security Architect roles that require a clearance usually expect candidates to already possess one. This is because holding a security clearance is a key qualification for these jobs, and employers often focus on hiring individuals who meet this requirement to align with strict security protocols.
What should I include in a sanitized portfolio for cleared architecture work?
When creating a polished portfolio, ensure it presents a professional image while showcasing your expertise in security architecture. Here’s what to include:
- Name, City, and State: Clearly state your name and location, but avoid listing your full address for privacy.
- Contact Information: Provide your email address and phone number for easy communication.
- Security Clearance Level: Highlight your clearance level prominently, as it’s a critical qualification in the field.
Next, include a concise summary of your experience. For instance, summarize your background in implementing security measures, designing enterprise architecture frameworks, and leading cloud security initiatives. Mention any certifications you hold, such as CISSP (Certified Information Systems Security Professional) or SABSA (Sherwood Applied Business Security Architecture), which validate your expertise.
Don’t forget to list your technical skills. This could include proficiency in zero trust models, cloud platforms, and specific tools or programming languages relevant to security architecture.
Finally, emphasize your key accomplishments. For example, highlight successful projects involving enterprise architecture frameworks, implementing zero trust security models, or optimizing cloud security protocols. Tailor these achievements to align with the skills and qualifications sought in your field.
A well-organized, professional portfolio not only underscores your technical expertise but also draws attention to your qualifications and clearance level, making you stand out in a competitive industry.
How do I protect my clearance under Continuous Vetting (CV)?
To keep your clearance secure under Continuous Vetting (CV), it’s crucial to practice good personal conduct and stick to security guidelines. CV includes regular reviews of your background, financial status, and criminal history. To avoid potential issues, steer clear of actions that might raise red flags, like financial troubles or legal problems. Be upfront about any changes in your circumstances and follow established security protocols to stay compliant and protect your clearance during these ongoing evaluations.
