Blue Team jobs focus on protecting systems, detecting threats, and responding to cyber incidents. For roles requiring security clearances, such as in government or defense, the stakes are higher as they involve safeguarding classified information and critical infrastructure. Entry-level salaries range from $55,000–$75,000, while senior positions can exceed $150,000. These jobs often require on-site presence due to secure facility protocols.
Key roles include:
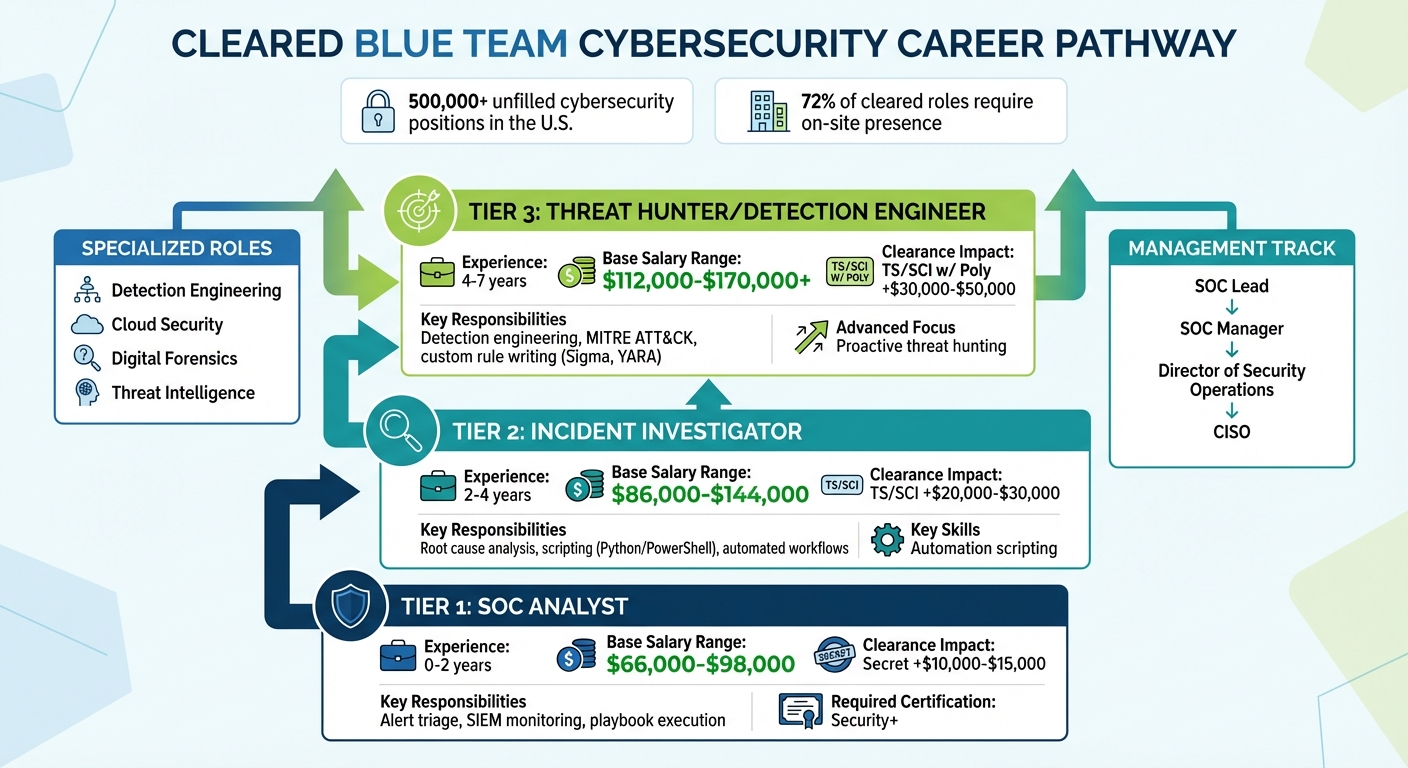
- SOC Analyst: Monitors systems, triages alerts, and escalates threats. Salaries range from $66,000 to $170,000+ depending on experience.
- Incident Responder: Contains and resolves confirmed threats, often requiring expertise in digital forensics and incident response.
- Security Engineer: Builds and maintains security defenses, focusing on tools like SIEM, EDR, and Zero Trust principles.
Skills in scripting (Python, PowerShell), SIEM tools (Splunk, Elastic), and certifications like Blue Team Level 1 (BTL1) or GSEC are highly valued. Security clearances significantly boost salaries and career prospects. With high demand and over 500,000 unfilled cybersecurity roles in the U.S., cleared professionals have strong opportunities for growth.
For job seekers, platforms like Cleared Cyber Security Jobs and practical experience with tools or certifications can help secure roles in this field.
Blue Team vs Red Team: Become an SOC Analyst [Complete Beginner Guide]
sbb-itb-bf7aa6b
What Cleared Blue Team Professionals Do
When classified information is on the line, defending it requires strict clearance protocols that highlight its importance to national security. Cleared Blue Team professionals operate within the structure of the NIST Cybersecurity Framework, following its five key functions: Identify, Protect, Detect, Respond, and Recover. These steps are critical in safeguarding sensitive systems that often support intelligence and national security operations [5]. In such high-stakes environments, the focus shifts to early detection and rapid containment, as breaches are assumed to be inevitable [7].
"Think of the SOC as the nerve center of cybersecurity defense – receiving signals (logs, alerts, telemetry), analyzing them, and deciding the right response." – rootRS7, Cybersecurity Writer [7]
Since 72% of cleared roles require on-site presence due to the need for secure facilities like SCIFs (Sensitive Compartmented Information Facilities), most professionals work in government-secured environments rather than remotely [2]. Here’s a closer look at how three key roles – SOC Analyst, Incident Responder, and Security Engineer – apply these principles in practice.
SOC Analyst
SOC Analysts are the first responders in cybersecurity, constantly monitoring SIEM (Security Information and Event Management) and EDR (Endpoint Detection and Response) platforms. They sift through alerts, separating the false positives from genuine threats, and escalate issues when necessary. Jack Walsh, owner of Cybersecurity Jobs List, describes the role as, "the emergency room of cybersecurity: you’re the first responder when something breaches the perimeter" [2].
Organizations face an overwhelming 4,484 alerts per day, with 67% of them going uninvestigated due to alert fatigue [2]. This makes the SOC Analyst’s ability to prioritize and act – such as blocking malicious IPs or isolating compromised devices – vital in preventing small issues from escalating into major incidents. The role is divided into tiers based on experience:
- Tier 1 analysts ($66,000–$98,000): Handle high volumes of alerts and follow established procedures.
- Tier 2 analysts ($86,000–$144,000): Dive deeper into investigations and write automation scripts.
- Tier 3 analysts ($112,000–$170,000+): Focus on proactive threat hunting and creating custom detection rules using tools like Sigma and YARA [2].
SOC Analysts are in high demand, ranking as the #1 cybersecurity role according to ISC2‘s 2025 Workforce Study [2]. However, hiring for these positions is challenging, with an average time-to-fill of 7 months, and some roles taking up to 2 years [2]. Skills in Python and PowerShell can set Tier 2 analysts apart from Tier 1 [2].
Incident Responder
Once a threat is confirmed by SOC Analysts, Incident Responders step in to contain and resolve it. They focus on identifying the root cause, neutralizing active threats, and ensuring systems return to normal operations [5]. In classified settings, they also manage digital evidence under strict chain-of-custody protocols, supporting legal or intelligence investigations [5].
Key responsibilities include analyzing EDR data to track attacker movements, isolating compromised systems to stop lateral spread, and documenting findings to strengthen future defenses [5]. This role requires expertise in digital forensics and mastery of the NIST Incident Response lifecycle: Preparation, Identification, Containment, Eradication, Recovery, and Lessons Learned [5]. With the average cost of a data breach at $4.45 million [4], the speed and effectiveness of incident response can significantly impact an organization’s resilience.
Incident Responders often collaborate with Security Engineers to patch vulnerabilities and fine-tune detection rules, ensuring similar attacks are less likely in the future. The work is demanding and often requires on-call availability, but it’s critical for minimizing damage and maintaining the Confidentiality, Integrity, and Availability (CIA) of sensitive systems [1].
Security Engineer
Security Engineers take a proactive approach by building defenses to block threats before they occur. Their work includes deploying firewalls, configuring SIEM and EDR platforms, implementing network segmentation, and hardening systems against known vulnerabilities [5]. By fine-tuning these tools, they ensure SOC Analysts receive actionable data rather than overwhelming noise [7].
In classified environments, Security Engineers rely on Zero Trust Architecture principles, such as identity-based security, micro-segmentation, and continuous verification, to protect highly sensitive networks [5]. They also integrate SOAR (Security Orchestration, Automation, and Response) platforms to automate routine tasks like IP reputation checks, reducing alert fatigue – a growing concern as 76% of security professionals reported burnout in 2025 [2].
Additional responsibilities include conducting vulnerability assessments, maintaining asset inventories, and designing risk-based architectures to meet strict compliance standards [5][6]. Employers value specialists in specific tools, with Splunk appearing in 37% of job postings and Microsoft Sentinel in 26% [2]. Mastering these platforms not only strengthens defenses but also accelerates career growth in cleared roles.
Required Skills and Certifications for Cleared Blue Team Roles
Breaking into cleared Blue Team roles demands a mix of technical know-how, recognized certifications, and the ability to communicate effectively under pressure. With over 400,000 learners using platforms like LetsDefend in more than 150 countries [11], competition is tough. That means sharpening your skills strategically is more important than ever.
Technical and Soft Skills
A strong foundation in SIEM operations is non-negotiable. Tools like Splunk and Elastic are at the heart of threat detection, and employers expect you to master tasks like writing queries, creating dashboards, and fine-tuning alerts to reduce unnecessary noise. Familiarity with network traffic analysis using Wireshark and digital forensics to piece together attacker behavior is also critical [3].
For advanced roles, skills like phishing and malware analysis (both static and dynamic) and proactive threat hunting are essential [10]. Add to that vulnerability management, which involves using scanning tools to prioritize and address risks effectively.
But technical skills alone aren’t enough. Clear communication and problem-solving abilities are key when explaining technical findings or conducting root cause analyses [3]. Thinking like an attacker helps too – it’s a valuable way to anticipate tactics and profile potential threats. As Nate Gonzalez, who holds GSEC and GCIH certifications, explains:
"Working in a Managed Detection & Response team, my GSEC gave me the building blocks needed to become a well-rounded defender and has sparked my motivation to continue getting more education and certs" [8].
These skills create a solid base, but certifications are what validate and elevate your expertise.
Recommended Certifications
Certifications play a huge role in proving your skills and advancing your career. The right choice depends on where you are in your journey. For beginners, Blue Team Level 1 (BTL1) is a great starting point. At around $520, it covers phishing, forensics, SIEM, and incident response through a hands-on exam [3]. With over 10,000 students earning this certification in the past five years and a first-time pass rate of 70%, it’s a trusted entry-level option. Tier 2 SOC Analyst Jay Jay reflected on the experience:
"The Exam itself was undoubtedly challenging and took me approximately 18 hours to attain gold, the experience made me a much more confident and well-rounded analyst and has made me qualified for lead roles" [3].
For those with more experience, Blue Team Level 2 (BTL2), priced at about $2,600, dives deeper into areas like malware analysis, threat hunting, and advanced SIEM techniques [10]. Another standout is the Certified CyberDefender (CCD), which boasts a 4.9/5 rating and was recognized as the SANS Team of the Year in 2023. Its rigorous 48-hour practical exam covers threat hunting, forensics, and perimeter defense [9]. Sai Dinesh Kondeti, a Security Engineer at Microsoft, shared:
"I can say that this is some high quality content that I have seen/studied in recent times. Labs are the meat of this course, sometimes, I had to spend several hours just to answer a single question" [9].
Here’s a quick look at some key certifications:
| Certification | Provider | Career Level | Approximate Cost (USD) | Key Focus Areas |
|---|---|---|---|---|
| Blue Team Level 1 (BTL1) | Security Blue Team | Junior (0–2 years) | $520 | Phishing, Forensics, SIEM, Incident Response [3] |
| Blue Team Level 2 (BTL2) | Security Blue Team | Intermediate | $2,600 | Malware Analysis, Threat Hunting, Advanced SIEM [10] |
| Certified CyberDefender (CCD) | CyberDefenders | Intermediate/Advanced | Varies | Threat Hunting, Forensics, Perimeter Defense [9] |
| GIAC Security Essentials (GSEC) | GIAC | Beginner/Intermediate | $2,499 | Security Fundamentals, Defensible Architecture [8] |
| Certified Security Operations Manager (CSOM) | Security Blue Team | Advanced | $2,600 | SOC Planning, Team Building, Maturity Models [10] |
For advanced roles, particularly in SOC leadership, Certified Security Operations Manager (CSOM) is a strong choice. Priced at about $2,600, it focuses on building, planning, and maturing SOC teams [10]. The key is to align your certifications with your career goals – whether you’re aiming to be a SOC Analyst for classified networks, an ISSO/ISSM for accredited systems, or a Cloud Security Engineer working in government cloud environments [12].
Tools and Technologies Used in Cleared Blue Team Operations
The right tools can make or break the effectiveness of cleared Blue Team operations. At the heart of these efforts are SIEM platforms like Splunk Enterprise Security, IBM QRadar, and the ELK Stack (Elasticsearch, Logstash, Kibana). These platforms centralize log aggregation and event correlation, providing a unified view of security events across classified networks. This approach ensures that SOC Analysts can focus on actionable insights instead of being overwhelmed by noise. Of course, strong endpoint protection is just as critical.
For endpoint defense, EDR platforms such as CrowdStrike Falcon, Microsoft Defender for Endpoint, and Carbon Black Endpoint offer deep visibility into endpoint activities. These tools allow teams to perform live forensics and contain threats directly on individual machines, enhancing overall security.
Integrating threat intelligence is what sets apart good defenders from exceptional ones. Tools like MISP, OpenCTI, and VirusTotal enrich security efforts by providing known indicators of compromise and adversary tactics. Specialized platforms like Flare focus on identity exposure monitoring, collecting over 1 million new stealer logs weekly from sources like dark web marketplaces and Telegram. Flare even enables advanced features like automatic employee password resets when compromised credentials are detected [14]. Meanwhile, GreyNoise helps filter out irrelevant internet noise, making it easier to identify targeted attacks. Impressively, it detects vulnerability exploitation attempts 80% faster than CISA KEV updates [14]. For air-gapped environments, Anomali ThreatStream aggregates intelligence feeds while supporting isolated network operations.
Detection engineering also plays a key role, especially when it comes to integrating tools effectively. Sigma, often referred to as "YARA for logs", simplifies detection logic by allowing rules to be written once and then adapted across multiple SIEMs like Splunk or Elastic. For deeper visibility into Windows systems, deploying Sysmon with configurations such as SwiftOnSecurity provides richer telemetry than standard Windows Event Logs. Additionally, Velociraptor is a powerful tool for large-scale forensic triage, enabling queries across thousands of hosts simultaneously.
Automation is another game-changer for Blue Teams. Platforms like TheHive for case management, paired with Cortex as an automation engine, streamline workflows. This setup allows for one-click actions like VirusTotal analysis or automated IP blocking, reducing manual effort and speeding up response times.
As Cybervolt aptly noted:
"The blue team’s job is no longer just monitoring logs or blocking IPs. It’s about visibility, detection engineering, automation, and response at scale." – Cybervolt [13]
The field is evolving at an impressive pace. For example, Cisco Talos processes 800 billion security events daily and prevents 7.2 trillion attacks annually [14]. Staying up to date with these tools and understanding how they fit into your overall security strategy is essential. Mastering them not only bolsters immediate defenses but also ensures your team is prepared to adapt to new challenges as they arise.
Career Paths and How to Find Cleared Blue Team Jobs
Cleared Blue Team Career Progression: Roles, Salaries, and Clearance Impact
Career Progression in Cleared Blue Team Roles
Starting out as a Tier 1 SOC Analyst (0–2 years), you’ll focus on tasks like monitoring SIEM and EDR systems, following established playbooks, and escalating threats when necessary. To land this role, a Security+ certification is typically the minimum requirement.
Next, you can move into Tier 2 as an Incident Investigator (2–4 years) by developing skills in Python and PowerShell to automate responses. Jack Walsh, Owner of Cybersecurity Jobs List, explains:
"The skill gap between Tier 1 and Tier 2 comes down to scripting. Python and PowerShell transform you from a playbook follower into someone who builds automation" [2].
This role involves conducting root cause analysis and forensic triage, requiring deeper technical expertise.
Tier 3 Threat Hunters or Detection Engineers (4–7 years) take on more proactive roles, focusing on detection and response strategies. Responsibilities include writing custom detection rules using tools like Sigma and YARA, leading major incident responses, and mastering frameworks like MITRE ATT&CK. From here, career paths can branch into specialized areas like Detection Engineering, Cloud Security, Digital Forensics, or Threat Intelligence. Alternatively, you might transition into management roles such as SOC Lead, SOC Manager, or even Director of Security Operations, with the ultimate goal of becoming a CISO.
Holding a security clearance can significantly speed up career progression and boost earnings. The salary breakdown below highlights just how impactful clearances can be. With a clear roadmap, the next step is finding the right job.
How to Search for Cleared Blue Team Jobs
For professionals with security clearances, Cleared Cyber Security Jobs is a veteran-founded platform designed to connect you with employers in need of cleared talent. It offers features like tailored job search filters, resume uploads, job alerts, and access to cleared job fairs.
Companies like Booz Allen Hamilton, Leidos, Peraton, GDIT, and CACI frequently hire for junior and mid-level roles in cleared environments. To stand out, showcase your practical experience by documenting alert triage exercises from platforms like TryHackMe or HackTheBox. Building a GitHub portfolio with automation scripts – such as parsing VirusTotal APIs or automating shift reports – can also make a strong impression. Specializing in a SIEM platform like Splunk or Microsoft Sentinel is another way to secure competitive salaries.
Many hiring managers also value candidates with foundational experience in IT helpdesk or systems administration roles, typically requiring 6–12 months of hands-on work. This background is often seen as an asset during the clearance process. Additionally, maintaining strong digital hygiene – such as auditing social media privacy settings and keeping GitHub contributions updated – can help you navigate the hiring process more smoothly.
Salary Expectations for Cleared Blue Team Roles
| Role Level | Experience Required | Salary Range | Clearance Impact | Primary Responsibilities |
|---|---|---|---|---|
| Tier 1 SOC Analyst | 0–2 years | $66,000–$98,000 | Secret: +$10,000–$15,000 | Alert triage, SIEM monitoring, playbook execution |
| Tier 2 Incident Investigator | 2–4 years | $86,000–$144,000 | TS/SCI: +$20,000–$30,000 | Root cause analysis, scripting, automated workflows |
| Tier 3 Threat Hunter | 4–7 years | $112,000–$170,000+ | TS/SCI w/ Poly: +$30,000–$50,000 | Detection engineering, MITRE ATT&CK, custom rule writing |
Security clearances play a significant role in boosting salaries. A Secret clearance can add $10,000–$15,000 to your base salary, while TS/SCI clearances add $20,000–$30,000. TS/SCI with a polygraph provides the largest boost, increasing earnings by $30,000–$50,000.
SOC Analysts remain one of the most sought-after roles in cybersecurity. According to ISC2’s 2025 Workforce Study, there are over 500,000 unfilled cybersecurity positions in the U.S., and information security jobs are expected to grow by 29% through 2034. However, keep in mind that 72% of SOC roles require on-site presence due to classified environment requirements, with only 6% offering fully remote options [2].
Building a Career in Cleared Blue Team Cybersecurity
To carve out a career in cleared Blue Team cybersecurity roles, start by mastering the basics. Focus on understanding the TCP/IP stack, the OSI model, and operating system administration for both Windows Server and Linux. Develop skills in PowerShell, Bash scripting, and key networking protocols like DNS, DHCP, and HTTP [5]. This foundational knowledge is what sets apart effective defenders from those who rely solely on theoretical understanding.
Earning practical certifications can showcase your readiness to operate in cleared environments. Hands-on training, such as BTL1, is particularly valuable for building essential skills and gaining the confidence needed for more advanced roles [3].
As you progress, aim to develop expertise in areas like phishing analysis, digital forensics, threat intelligence, SIEM operations, and incident response. Specialized labs and hands-on experience with industry-standard tools will help solidify your defensive capabilities [3][5]. While having a security clearance is a significant advantage, your ability to perform operationally will ultimately dictate your career trajectory.
A structured plan can help guide your career growth. After building a strong technical foundation, focus on core skills during Year 1, move into intermediate tasks like malware analysis in Year 2, and advance to sophisticated threat detection by Year 3. By Years 4–5, you can work toward leadership roles and expertise in security architecture [5]. With more than 26,000 open Cybersecurity Analyst positions in the U.S. and only enough professionals to fill 85% of them [15], cleared individuals have a clear path to growth and opportunity.
To connect with roles that match your clearance and skills, platforms like Cleared Cyber Security Jobs offer tailored resources. These include job filters, resume uploads, alerts, and access to cleared job fairs. Use these tools to align your advancing expertise with the right opportunities in the field.
FAQs
How do I get a security clearance for Blue Team work?
To secure a security clearance for Blue Team roles, you’ll need to follow a few key steps. First, an employer must sponsor you, as individuals cannot apply on their own. Then, you’ll need to complete the SF-86 form, which collects detailed personal and professional information. After that, you’ll go through a background investigation to assess your eligibility.
The process varies depending on the clearance level – Confidential, Secret, or Top Secret. For higher levels like Top Secret, additional steps such as a polygraph test might be required. Be prepared for the process to take time, ranging from several months to over a year. If you’re aiming for even more specialized clearances, like TS/SCI, expect further vetting and possibly extra training.
What should my first 90 days as a cleared SOC analyst focus on?
Starting out as a cleared SOC analyst? The first three months are all about laying the groundwork, getting comfortable with the tools, and sharpening your ability to spot patterns. Here’s a breakdown of how to make the most of this time:
- Days 0–30: Focus on understanding the essentials. Get familiar with key tools like SIEM and EDR platforms, study your organization’s security policies, and dive into the specifics of its threat landscape.
- Days 30–60: Start prioritizing alerts based on risk levels. This is where you’ll get hands-on experience with monitoring and responding to real-time incidents.
- Days 60–90: Take it up a notch by honing advanced skills. Spend time on digital forensics, incident response techniques, and conducting vulnerability assessments.
By pacing yourself through these steps, you’ll build a solid foundation to excel in your role.
Which SIEM should I learn first for cleared roles?
For those stepping into cleared Blue Team roles, Wazuh is a great starting point. This open-source SIEM platform is well-regarded for its adaptability and feature set, making it a practical choice for beginners while meeting industry requirements.
As you build experience, you might want to dive into commercial tools like Splunk to broaden your skill set. Mastering SIEM platforms is crucial for handling key responsibilities in cleared environments, such as threat detection, incident response, and vulnerability management.
