As a 1721 Cyberspace Officer in the Marine Corps, you’ve gained unmatched hands-on experience in cybersecurity, including threat analysis, incident response, and vulnerability management. With over 700,000 cybersecurity jobs expected to remain unfilled in the U.S. by 2025, your skills, combined with an active TS/SCI clearance, position you as a top candidate for high-paying civilian roles. Transitioning successfully involves:
- Translating military experience into civilian-friendly language (e.g., "classified/unclassified networks" instead of "NIPR/SIPR").
- Earning certifications like CISSP, OSCP, or CCSP to maximize earning potential.
- Highlighting your clearance prominently on your resume, as it can add $15,000-$30,000 to your salary.
- Starting your job search early (12 months before separation) and leveraging programs like SkillBridge.
The cleared job market offers roles such as Threat Intelligence Analyst, Penetration Tester, and Security Architect, with salaries ranging from $95,000 to $250,000 depending on experience and certifications. Protecting your clearance, networking strategically, and tailoring your resume are key steps toward securing a rewarding career in cybersecurity.
What 1721 Cyberspace Officers Do and How It Applies to Civilian Jobs
Main Duties of 1721 Cyberspace Officers
As a 1721 Cyberspace Officer, your work revolves around threat analysis, incident response, and vulnerability management – all of which are crucial in both military and civilian cybersecurity roles. You’re responsible for monitoring security alerts across enterprise networks, investigating breaches, and researching threat actors to create intelligence reports that guide defensive strategies. When a security incident occurs, you take charge of containing the breach, conducting forensic analysis, and preparing detailed after-action reports.
In terms of vulnerability management, you use tools like ACAS (Tenable Nessus) to perform scans, analyze the results, and prioritize fixes according to DISA STIGs. Unlike many civilian professionals who often train in controlled, simulated environments, you’ve worked on live networks where the stakes are higher – failure could compromise national security. As Brad Tachi, CEO of Best Military Resume, explains:
"Military cyber professionals have something that most civilian cybersecurity candidates don’t: real-world operational experience defending networks against actual threats, not just simulated ones." [3]
These responsibilities align closely with core civilian cybersecurity functions.
Converting Military Cybersecurity Skills to Civilian Job Titles
Your experience as a 1721 Cyberspace Officer can translate seamlessly into civilian roles such as Threat Intelligence Analyst, Incident Responder, SOC Manager, Vulnerability Analyst, Cybersecurity Engineer, Penetration Tester, Red Team Lead, Security Architect, or even CISO. These roles align with the operational expertise you’ve developed, making your skills highly relevant in the civilian cybersecurity workforce.
The demand for cybersecurity professionals is booming, with information security analyst roles alone expected to grow by 33% through 2033. This growth will create around 17,300 new positions annually [4]. Your military background – defined by operational discipline, strict adherence to procedures, and accountability – makes you particularly well-suited for high-pressure environments like Security Operations Centers, where uptime for critical systems is non-negotiable.
sbb-itb-bf7aa6b
Certifications That Matter for Civilian Cybersecurity Careers
Certifications You May Already Have from Military Service
If you’ve served as a 1721 Cyberspace Officer, chances are you already hold CompTIA Security+, a baseline requirement for DoD 8570/8140 IAT Level II positions. This certification alone can open doors to most entry-level cleared cybersecurity jobs, with potential salaries ranging from $55,000 to $75,000 within six months of leaving the military [5]. Additionally, some 1721s acquire the Certified Ethical Hacker (CEH) certification through military training programs, which showcases your expertise in offensive cybersecurity.
Your hands-on experience defending networks from real-world threats gives you a significant advantage when tackling advanced certification exams. As Mike McNelis of Training Camp points out:
"A certification cuts through that translation problem. When your resume says CompTIA Security+ or CISSP, a hiring manager immediately understands your knowledge base" [7].
Your familiarity with frameworks like the Risk Management Framework (RMF), NIST guidelines, and DISA STIGs provides a solid foundation for certifications that many civilian candidates find challenging. These qualifications not only validate your expertise but also prepare you for pursuing advanced certifications that can boost your career prospects in the cleared cybersecurity field.
Additional Certifications That Improve Your Job Prospects
For those aiming for senior cybersecurity roles, the CISSP (Certified Information Systems Security Professional) is a standout credential. It requires five years of relevant experience, which your military service often satisfies. The exam costs $749, but programs like Marine Corps COOL can cover this expense [1][6]. CISSP-certified professionals typically earn salaries exceeding $130,000 on average [6].
If you’re targeting cloud security roles, consider the CCSP (Certified Cloud Security Professional). Priced at $599, it’s increasingly important as more organizations shift to cloud-based infrastructures [1]. For those interested in penetration testing or red team positions, the OSCP (Offensive Security Certified Professional) is highly regarded by technical hiring managers. At $1,599, it’s a rigorous certification that includes a 24-hour hands-on hacking exam, making it more respected than the CEH [1][3]. For defensive operations, such as roles in Security Operations Centers, the CompTIA CySA+ ($392) is tailored for SOC Analyst Tier II and Incident Responder positions [1][5].
Combining these certifications with your active TS/SCI clearance significantly increases your value to employers. This clearance spares organizations the $5,000–$15,000 cost and lengthy 6–18 month process of clearance sponsorship [1][3]. In fact, this added value can translate into an annual salary premium of $15,000 to $30,000 [3][2][4].
How Military Cyber Experience Translates to Civilian Careers
How to Write Your Resume for Cleared Cybersecurity Jobs
Your resume is the key to transitioning from military service to a civilian cybersecurity career. The challenge isn’t whether you have the skills – it’s making sure hiring managers can quickly recognize them. With recruiters spending just six seconds on an initial scan [12], your resume needs to be clear, concise, and written in civilian terms.
Replacing Military Terms with Civilian Language
Civilian hiring managers often struggle to interpret military jargon. To stand out, translate your experience into terms they can easily understand.
"A civilian hiring manager cannot decode ‘0311 Sgt, 2/8, 2d MarDiv’ in six seconds. But ‘Operations Team Supervisor managing 13 personnel and $1.2M in equipment’ – that they understand immediately" [12].
Start by converting your job title into a civilian equivalent. For example:
- If you were an O-3 (Captain), use titles like Project Manager or Operations Manager.
- O-4s (Majors) might list roles like Senior Program Manager or Director.
- For 1721 Cyberspace Officers, civilian roles could include Cybersecurity Manager, SOC Director, or Information Security Lead [2][3].
Next, rewrite technical terms to align with civilian language. For example:
- Replace "NIPR/SIPR" with "unclassified and classified network environments."
- Swap "COMSEC" for "encryption management" or "communications security."
- Describe tools like ACAS as "vulnerability assessment tools (Tenable Nessus)" [2].
When listing accomplishments, follow the CAR method (Challenge, Action, Result) [8]. Instead of stating "Executed defensive cyber operations", say: "Reduced incident containment time by 20% by implementing automated threat detection across a 15,000-node enterprise network" [3]. Wherever possible, include metrics like network size, user base, or asset value [2][3].
For classified work, focus on scope and complexity while avoiding sensitive details. Use phrases like "multi-enclave network environment" or "15,000-node enterprise network" to describe scale without disclosing specifics [10][11].
Here’s a quick reference for translating military terms:
| Military Term | Civilian Translation |
|---|---|
| DCO (Defensive Cyber Operations) | Network defense operations |
| ACAS / HBSS | Vulnerability scanners (Nessus) / Endpoint security suites |
| RMF (Risk Management Framework) | Security compliance and authorization |
| DISA STIGs | Security hardening standards |
| Briefed Commander | Presented strategic recommendations to executive leadership |
Once you’ve translated your experience, shift focus to highlighting your clearance and technical expertise.
Showing Your Clearance and Technical Skills
Your security clearance is a major asset, often boosting salaries by $15,000 to $30,000 annually [2][3]. Make it easy for recruiters to spot by listing it in two places:
- Directly under your contact information in the resume header.
- In a dedicated "Clearance" section near the top.
Use precise language like: Active TS/SCI with CI Polygraph – Current. This ensures your resume surfaces in searches [10].
"I’ve talked to defense contractor recruiters who told me they literally search their ATS for ‘TS/SCI’ as their first filter before looking at anything else. If your clearance isn’t in a searchable text field on your resume – or if you’ve buried it on page two – you’re invisible to these recruiters" [10].
For certifications, list high-demand credentials such as CISSP, CASP+, or OSCP prominently in a "Certifications" section immediately after your clearance.
In your technical skills section, include tools and frameworks that match job descriptions. Examples include Splunk, Wireshark, Nessus, and frameworks like NIST and MITRE ATT&CK [2][3].
Finally, format your resume using civilian-friendly conventions:
- Use "City, State" for locations (e.g., "Camp Lejeune, NC").
- List dates as "Month Year to Month Year" (e.g., "March 2018 to June 2022") to ensure compatibility with Applicant Tracking Systems.
- Aim for a two-page maximum when applying for corporate roles [8][9].
Finding and Landing Cleared Cybersecurity Jobs
Having an active security clearance doesn’t just make you eligible for in-demand roles – it also saves employers a lot of time and money. By cutting sponsorship costs by $5,000–$15,000 and bypassing the 6–18 months typically needed for background checks [3][14], your clearance becomes a powerful bargaining tool. To make the most of it, you’ll need to know where to look, who’s hiring, and how to connect with key players. With your polished resume and certifications ready, it’s time to zero in on the right employers and build meaningful connections.
How Security Clearance Affects Your Job Options
If you hold a TS/SCI clearance, you could see a salary bump of $15,000–$30,000, with some roles offering annual pay premiums of $20,000–$60,000 compared to positions without clearance requirements [3][14].
But clearances don’t last forever – they’re time-sensitive. After leaving federal service, they typically stay "active" for just two years [14]. If your clearance expires, contractors face reinvestigation costs ranging from $10,000 to $30,000 [14]. To avoid this, aim to secure a cleared role or participate in a SkillBridge internship within 90 days of leaving the military [14].
When negotiating pay, emphasize the value of your clearance. For example, you might say:
"My active clearance saves your company 12–18 months of waiting and over $20,000 in investigation costs. I believe this benefit should be reflected in my compensation" [14].
Next, focus on identifying the employers actively seeking cleared talent.
Major Employers Hiring for Cleared Cybersecurity Positions
Cleared cybersecurity roles are concentrated within three main types of employers: defense contractors, federal agencies, and commercial tech companies with government contracts.
- Defense contractors are the largest employers of cleared professionals. Big names include Booz Allen Hamilton, Leidos, ManTech, SAIC, Raytheon, and Northrop Grumman [3].
- Federal agencies also hire cleared candidates directly. Use USAJobs.gov for civilian federal roles, and check IntelligenceCareers.gov for positions with agencies like the CIA, DIA, NGA, and NRO [13].
- Commercial tech companies with government contracts – such as Amazon (AWS), Microsoft, Google, CrowdStrike, and Palo Alto Networks – employ cleared professionals. Even financial giants like JPMorgan Chase, Bank of America, and Goldman Sachs maintain cleared cybersecurity teams [3].
Geography can influence your job search. Cleared job hubs include the DC/Maryland/Virginia (DMV) corridor, Tampa, Colorado Springs, San Diego, and Huntsville.
Building Connections in the Cleared Community
Once you’ve identified potential employers, the next step is networking. Building relationships within the cleared community can help you bypass automated hiring systems and connect directly with decision-makers. One effective strategy is reaching out to former military colleagues now employed at defense contractors [14]. A referral from someone inside the company can significantly improve your chances.
Specialized job boards, like ClearanceJobs.com, are an excellent resource for cleared professionals. Unlike general job boards, ClearanceJobs allows recruiters to find you based on your clearance level – even when you’re not actively applying [13][14].
"Your clearance is a golden ticket, but only if you put it where employers can find it. A clearance buried on page two of your resume or missing from your online profile is a clearance that is not working for you."
- Brad Tachi, Navy Veteran & BMR Founder [13]
On LinkedIn, use Boolean search techniques to locate recruiters and hiring managers. For instance, search for "Cybersecurity Manager" + "TS/SCI" or "Secret clearance required" to find professionals actively hiring for cleared roles [13][14]. Engaging with posts from employees at your target companies – like Lockheed Martin or Booz Allen Hamilton – can also boost your visibility.
Joining professional organizations, such as ISSA or (ISC)², can open doors to networking events in major cleared job hubs [13]. Attending cleared job fairs in cities like Northern Virginia, San Diego, or Huntsville is another great way to connect with hiring teams face-to-face [13].
Finally, consider the DoD SkillBridge program, which allows you to intern with a cleared contractor during your last 180 days of military service while still receiving your military pay [14]. This hands-on experience often leads to full-time job offers, giving you a head start before you officially transition out of service.
Salary Expectations and Career Advancement
Security Clearance Salary Premium and Career Progression for Cleared Cybersecurity Professionals
Transitioning from a 1721 Cyberspace Officer role can significantly boost your earning potential compared to entry-level cybersecurity positions. For those in cleared roles, the pay premium ranges between 20–40% [15][16]. Understanding the factors that influence salaries and how to maximize them is vital for building a rewarding and sustainable career.
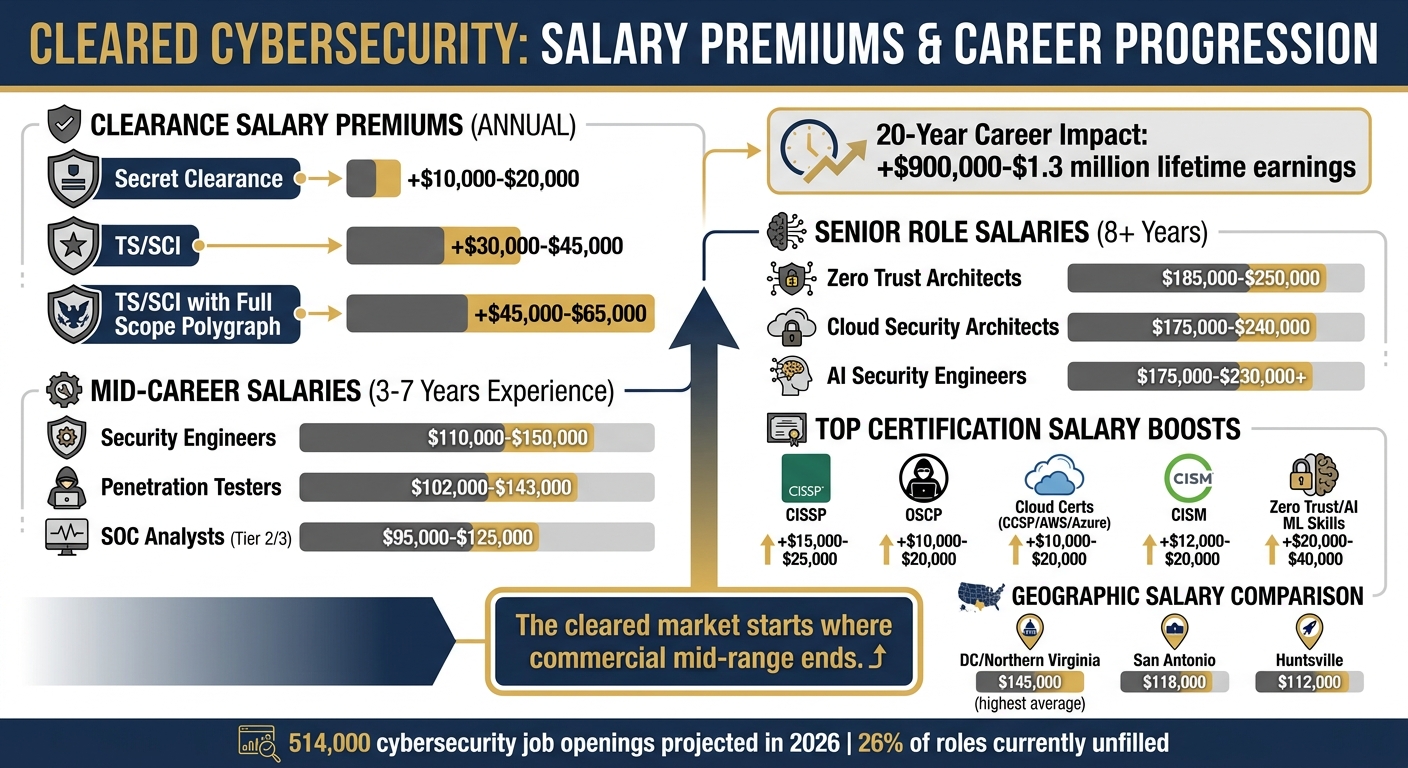
What Cleared Cybersecurity Jobs Pay
In cybersecurity, obtaining a security clearance is one of the biggest factors affecting salary. A Secret clearance typically adds $10,000–$20,000 annually, while a TS/SCI clearance can increase pay by $30,000–$45,000 compared to non-cleared positions [15][16]. For those with a TS/SCI with Full Scope Polygraph, the premium jumps to $45,000–$65,000 per year. Over a 20-year career, this could mean an additional $900,000–$1.3 million in lifetime earnings [15][16].
Here’s a snapshot of mid-career salaries (3–7 years of experience):
- Security Engineers: $110,000–$150,000
- Penetration Testers: $102,000–$143,000
- SOC Analysts (Tier 2/3): $95,000–$125,000 [15]
For senior roles (8+ years), salaries rise dramatically:
- Zero Trust Architects: $185,000–$250,000
- Cloud Security Architects: $175,000–$240,000
- AI Security Engineers: $175,000–$230,000+ [15]
Geography also plays a role. While DC/Northern Virginia offers the highest average salary at $145,000, cities like San Antonio ($118,000) and Huntsville ($112,000) provide better purchasing power due to lower living costs [15][16]. When switching contractors, aim for a 15–20% salary increase – your active clearance gives you a competitive edge [15].
"The cleared market starts where commercial mid-range ends." – CyberSecJobs Editorial [15]
These figures highlight how advanced certifications and specialized skills can significantly enhance earning potential.
Certifications That Lead to Higher Positions and Pay
Certifications are a powerful way to increase your salary. The CISSP is widely recognized as the gold standard for senior roles, security architecture, and management tracks, often adding $15,000–$25,000 to your salary [15]. For penetration testers and technical experts, the OSCP carries a $10,000–$20,000 premium due to its challenging practical exam [15].
Cloud security certifications are increasingly valuable as government agencies migrate to secure cloud environments like GovCloud and IL5-6. Earning certifications such as the CCSP, AWS Certified Security Specialty, or Azure Security Engineer (AZ-500) can add $10,000–$20,000 to your base salary [15]. Meanwhile, the CISM is a strong choice for those pursuing security management roles, with salary boosts ranging from $12,000–$20,000 [15].
Specialized skills in Zero Trust Architecture and AI/ML Security command the highest premiums. Professionals with these skills often earn $20,000–$40,000 above standard roles, as the talent pool in these areas is extremely limited [15]. With federal mandates requiring all agencies to adopt Zero Trust frameworks, architects in this field are among the best-paid individual contributors [15][16].
Planning Your Career Path in Cleared Cybersecurity
Strategic planning is essential for long-term success in cleared cybersecurity roles. One key milestone is the "5-Year Clearance Cliff", a point where salaries increase sharply as you gain mission-specific knowledge and expertise [15]. By this stage, your familiarity with classified systems often outweighs technical skills in value, opening doors to senior roles and leadership opportunities.
Protect your clearance at all costs. An active clearance is critical to advancing your career. If you leave a cleared role, you have 24 months to reactivate your clearance without undergoing a full reinvestigation [17][4]. Allowing a TS/SCI clearance to lapse by taking a non-cleared position is a costly mistake for veterans [17][4].
"Letting a TS/SCI lapse because you took a non-cleared position is one of the most expensive mistakes a transitioning veteran can make." – Brad Tachi, CEO, Best Military Resume [17]
Additionally, use contract recompetes to your advantage. When a new contractor takes over a contract, they often prioritize retaining incumbent staff, giving you leverage to negotiate a 15–20% salary increase [15]. While contractors generally earn 15–40% more in base salary, federal employees at higher levels, like a GS-14 Step 5 in DC ($163,104), can out-earn contractors when factoring in benefits like the FERS pension, TSP matching, and healthcare [15].
Finally, stay on top of emerging skills. Around 10% of cybersecurity job listings now mention AI expertise [15], and major employers like Google, IBM, and the DoD are shifting toward skills-based hiring, placing more emphasis on certifications and technical ability over formal degrees [4]. With 514,000 cybersecurity job openings projected in 2026 and 26% of roles currently unfilled [16], the demand for skilled cleared professionals shows no signs of slowing down.
Conclusion
Your military cyber background gives you a distinct edge when transitioning to cleared civilian roles. The practical experience you’ve gained defending networks against real adversaries holds far greater weight than purely academic credentials[2][3]. Additionally, your active security clearance is a significant advantage that most civilian candidates simply don’t have.
To make the most of your experience, translate your military achievements into civilian-friendly language, and back them up with measurable results. Using the CAR method (Challenge, Action, Result) can help you showcase your accomplishments with specifics like uptime percentages, the number of users supported, or the scale of the networks you managed[8]. Certifications are another key piece: while foundational ones like Security+ can open doors, credentials like CySA+ or CISSP can elevate your profile even further.
This approach has been proven time and again.
"The cyber veterans I’ve seen transition most successfully are the ones who don’t settle for the first SOC analyst job offered to them. Your military experience puts you above entry-level." – Brad Tachi, CEO of Best Military Resume[3]
One critical reminder: protect your clearance. You have a 24-month window to reactivate it after separation, and letting a TS/SCI clearance lapse could be a costly mistake[4]. To set yourself up for success, start planning your transition 12–18 months before separating. Update your online presence, network actively, and focus on connecting with key defense contractors[3][2]. With over 514,000 cybersecurity jobs projected to open by 2026, the demand for skilled professionals like you remains high.
FAQs
Which 1721 skills translate best to civilian cyber jobs?
Key abilities in cybersecurity revolve around offensive and defensive operations, penetration testing, network defense, and malware analysis. Having expertise with tools such as Python, Linux, and SIEM systems is especially important for those pursuing civilian roles in this field.
How do I keep my TS/SCI active after separation?
To maintain your TS/SCI clearance after separation, it can remain inactive for up to 24 months. During this period, you’ll need sponsorship from an employer or contractor to reactivate it. If it isn’t reactivated within those 24 months, the clearance will expire, and you’ll need to undergo a new investigation. Taking action within this timeframe is crucial to avoid restarting the entire process.
What cert should I get next for my target role?
The best certification for you depends on where you are in your career and what role you’re aiming for. If you’re targeting advanced positions like a security engineer, the CISSP is a strong choice. For those just starting out or looking to establish a solid base, Security+ is a great starting point and is often a requirement for government or cleared positions. If penetration testing or offensive security is your goal, the CEH is worth considering. A smart progression might be earning Security+ first, then moving on to CISSP or CEH, depending on your career aspirations.
