SOC analysts are the frontline defenders in cybersecurity, especially in U.S. government and defense sectors. Their work involves monitoring networks, analyzing threats, and responding to incidents in real-time. For professionals with security clearances, SOC roles offer structured career growth and substantial salary boosts – up to $50,000 more for those with a TS/SCI clearance and polygraph.
SOC teams are organized into tiers:
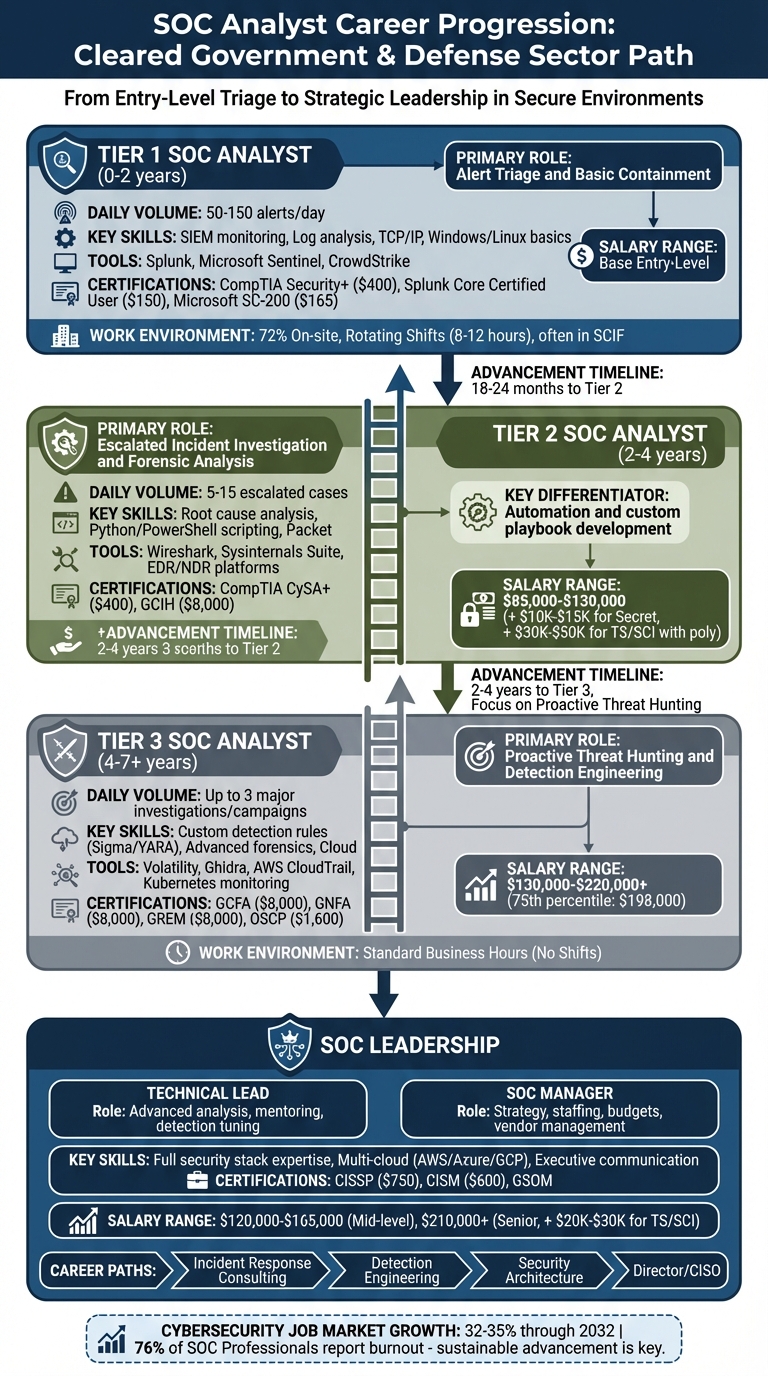
- Tier 1 (0–2 years): Handles alert triage and basic containment.
- Tier 2 (2–4 years): Investigates escalated incidents and performs forensic analysis.
- Tier 3 (4–7+ years): Focuses on threat hunting and detection engineering.
- Leadership roles: Oversee team operations and strategy.
Certifications like CompTIA Security+ (Tier 1), CySA+ (Tier 2), and CISSP (leadership) are critical for career progression. Analysts also benefit from technical skills like scripting (Python, PowerShell) and expertise in tools like Splunk and Microsoft Sentinel.
Key tips for advancing:
- Automate repetitive tasks to showcase initiative.
- Gain hands-on experience with SIEM tools and cloud security.
- Build a portfolio of projects to highlight technical depth.
Cleared SOC roles are in high demand, with salaries ranging from $85,000 for Tier 2 analysts to over $200,000 for Tier 3 and leadership positions. High-performing SOCs aim for rapid detection and response times, making skilled analysts indispensable.
SOC Analyst Career Progression Path from Tier 1 to Leadership
From Beginner to LEVEL 3 SOC Analyst in Cybersecurity
Required Skills and Certifications for Cleared SOC Analysts
To succeed in a cleared SOC (Security Operations Center) role, a combination of security clearance, technical expertise, and specific certifications is essential. Here’s a breakdown of what it takes to thrive in this field.
Understanding Security Clearance Levels
Security clearances are divided into three main categories, each granting access to different levels of sensitive information:
- Confidential: Grants access to information that could harm national security if disclosed improperly[10].
- Secret: Covers information that could cause serious harm and is commonly required for SOC analysts dealing with secure government networks[10][11].
- Top Secret (TS): Protects information that could cause grave damage, requiring a Single Scope Background Investigation (SSBI)[10][11].
For those handling highly classified intelligence, a TS/SCI (Top Secret/Sensitive Compartmented Information) clearance is necessary. This level includes access to compartmented intelligence methods and sources[10].
The clearance process evaluates 13 factors, such as financial stability, foreign influence, and personal conduct[10][11]. In 2026, processing times for clearances varied:
- Secret clearances: 60–150 days
- Top Secret clearances: 120–240 days
- TS/SCI with polygraph: 180–365+ days[11]
Under the Trusted Workforce 2.0 framework, periodic reinvestigations have been replaced by Continuous Vetting. This system monitors criminal records, credit reports, and foreign travel in real time. Applicants must self-report events like arrests, significant debts, or foreign contacts. Before applying through the eApp platform, it’s wise to:
- Conduct a self-audit of financial records.
- Resolve any credit issues.
- Gather documentation for a 10-year history of residences, employment, and foreign contacts for the SF-86 form[11].
Once clearance requirements are met, the focus shifts to acquiring the technical skills needed for SOC roles.
Technical Skills Needed for Entry-Level SOC Work
At the Tier 1 level, analysts handle tasks like triaging alerts, monitoring SIEM (Security Information and Event Management) and EDR (Endpoint Detection and Response) platforms, and following playbooks for incidents like phishing or malware attacks[1][8]. Key skills include:
- Networking basics (e.g., TCP/IP, DNS).
- Familiarity with operating systems like Windows and Linux.
- Log analysis using tools like Splunk, Microsoft Sentinel, and CrowdStrike[1].
Tier 2 analysts take on advanced investigations, such as root cause analysis, and use scripting languages like Python or PowerShell to automate tasks. Scripting expertise is often a stepping stone to higher roles[1][5].
At the Tier 3 level, responsibilities include proactive threat hunting, detection engineering (e.g., writing Sigma and YARA rules), and applying the MITRE ATT&CK framework[1][9].
For hands-on practice, platforms like TryHackMe, LetsDefend, and Security Onion offer simulations of real-world scenarios. Documenting these projects in a professional portfolio can help showcase your skills[6][9]. Additionally, specializing in a major SIEM tool – such as Splunk or Microsoft Sentinel – can boost your expertise and earning potential[1].
Entry-Level Certifications for Cleared SOC Careers
Certifications play a pivotal role in meeting job requirements and advancing your career. Here are some key certifications to consider:
- CompTIA Security+: A must-have for entry-level roles, this certification is required for about 70% of SOC analyst positions and satisfies the DoD 8140/8570 IAT Level II requirement. Cost: approximately $400[1][6][7].
- CompTIA CySA+: Ideal for Tier 2 roles, this certification focuses on behavioral analytics and threat detection. It also fulfills the DoD 8140 CSSP Analyst requirement. Cost: approximately $400[1][7].
- Microsoft SC-200 (Security Operations Analyst): While not DoD 8140-compliant, this certification is highly regarded in organizations using Azure-based security tools, particularly for those working with Microsoft Sentinel. Cost: approximately $165[1].
| Certification | Career Level | DoD 8140/8570 Relevance | Approximate Cost |
|---|---|---|---|
| CompTIA Security+ | Tier 1 / Entry | IAT Level II | $400 |
| CompTIA CySA+ | Tier 2 / Mid | CSSP Analyst | $400 |
| Microsoft SC-200 | Tier 1–2 / Specialist | No (Vendor-Specific) | $165 |
These certifications, combined with technical skills and clearances, form the foundation for a successful career in cleared SOC environments.
Tier 1 SOC Analyst: Entry-Level Cleared SOC Positions
Daily Tasks and Work Environment
As a Tier 1 SOC analyst, you’re the first responder in the world of cybersecurity, acting as the initial line of defense in a SOC (Security Operations Center). Your main job? Monitoring SIEM (Security Information and Event Management) dashboards – tools like Splunk, Microsoft Sentinel, or IBM QRadar – to sift through anywhere from 50 to 150 alerts a day[12]. The tricky part is separating true positives (real threats) from false positives (noise), all while working within tight timelines. High-severity alerts often require action within 15 to 30 minutes.
Every alert you handle gets logged in a ticketing system like ServiceNow or Jira. Your tasks include assessing the "blast radius" of an incident – figuring out which endpoints, user accounts, or networks are affected. Depending on the situation, you might resolve the issue yourself or escalate it to Tier 2. Basic containment steps, like blocking a malicious IP or isolating a compromised device, are carried out using pre-written playbooks.
If you’re working in a cleared environment, expect to be on-site in a SCIF (Sensitive Compartmented Information Facility), where personal devices are strictly off-limits. Shifts usually rotate in 8- or 12-hour blocks and often include nights, weekends, and holidays. Fully remote SOC positions are rare – only 6% of roles offer this flexibility, and for cleared positions, on-site work is even more common at 72%[1]. A typical shift involves a handover from the previous team, continuous alert monitoring, and thorough documentation.
"Tier 1 analysts are the triage nurses who assess every patient walking through the door and determine severity." – Nora Grace, Training Camp[13]
This demanding role sets the foundation for the skills and certifications essential to succeed as a Tier 1 analyst.
Skills and Certifications for Tier 1 Analysts
The CompTIA Security+ certification is often the starting point for Tier 1 analysts, but vendor-specific certifications can make you stand out. For example, the Splunk Core Certified User (costing around $150) highlights your ability to navigate one of the most popular SIEM platforms. Similarly, the Microsoft SC-200 certification (costing $165–$200) demonstrates expertise in Microsoft Sentinel environments[12][1].
Your day-to-day work will involve analyzing logs from firewalls, proxies, and endpoints to detect unusual activity. You’ll need to understand how SIEM correlation rules work, recognize what triggers alerts, and communicate your findings effectively – whether it’s to technical teams or non-technical stakeholders. Writing clear, concise incident summaries (usually five sentences) is just as critical as your technical skills[8].
Modern SOC environments are increasingly focused on cloud-native signals like AWS CloudTrail logs, Azure Activity Logs, and identity-based anomalies such as MFA (multi-factor authentication) issues. Familiarity with the MITRE ATT&CK framework is also crucial for categorizing adversary tactics and techniques during escalations[12][7]. With organizations facing an average of 4,484 alerts daily and 67% of them going uninvestigated due to alert fatigue, your ability to prioritize and triage effectively becomes a key asset[1].
Mastering these skills and certifications lays the groundwork for advancing into more challenging roles, like Tier 2 analyst positions.
How to Move from Tier 1 to Tier 2
Most analysts spend 18 to 24 months in a Tier 1 role before moving up to Tier 2[1]. The key to advancing is shifting from simply following playbooks to building automation tools. Learning Python or PowerShell is a game-changer, enabling you to automate repetitive tasks like creating shift reports or parsing VirusTotal API data. This not only shows initiative but also reduces the manual workload for your team[1][3].
Volunteer to take on escalated incidents to demonstrate your investigative skills. Documenting your approach to root cause analysis can highlight your ability to work independently. Additionally, maintaining a log to fine-tune noisy detection rules showcases leadership potential and your commitment to improving SOC efficiency[8].
"The jump from Tier 1 to Tier 2 is where many analysts stall. It’s not enough to be good at triaging alerts. You need to demonstrate investigative ability and technical depth." – Safwan Azeem, Advanced Cybersecurity & Management Certification[3]
To strengthen your qualifications, consider earning the CompTIA CySA+ certification (around $400) or specializing in areas like network forensics or malware analysis. Participating in incident post-mortems and tracking action items can also help you gain visibility with senior management[5]. High-performing SOCs aim for a Mean Time to Detect (MTTD) of under 15 minutes and a Mean Time to Respond (MTTR) of under 1 hour for critical alerts. Consistently meeting these benchmarks can fast-track your career progression[4].
Tier 2 and Tier 3 SOC Analysts: Mid-Level and Senior Positions
Tier 2: Advanced Analysis and Incident Response
Tier 2 analysts take on escalated incidents, diving deeper into investigations and coordinating containment strategies[2][12]. These analysts typically handle 5–15 escalated cases daily, focusing on detailed analysis rather than sheer volume[12]. A significant part of the job involves working with tools like SIEM, EDR, and NDR to piece together attack timelines and uncover the root cause of incidents. This often means identifying how attackers initially gained access and which systems were affected.
Expect to rely heavily on tools like Wireshark for packet inspection and the Sysinternals Suite for Windows analysis. While malware analysis is part of the role, especially for identifying known threats, more complex samples are usually escalated to Tier 3.
"Tier 2 is the escape hatch. Most burnout concentrates at Tier 1… The 1-2 year push to Tier 2 dramatically improves quality of life." – Cybersecurity Jobs List[1]
In the U.S., Tier 2 analysts earn between $85,000 and $130,000 annually[12]. Holding a Secret clearance can add $10,000–$15,000 to your salary, while a TS/SCI with polygraph may increase it by $30,000–$50,000[1]. Companies like Booz Allen Hamilton and Leidos actively hire for these roles, with Booz Allen offering salaries ranging from $88,000 to $201,000 for senior positions[1].
Tier 2 work serves as a stepping stone to Tier 3, where the focus shifts from reactive incident response to proactive threat hunting and detection engineering.
Tier 3: Threat Hunting and Detection Engineering
Tier 3 analysts take their expertise to the next level, focusing on anticipating and uncovering hidden threats rather than responding to alerts. This role, the highest technical level in a SOC, involves proactive threat hunting. Analysts look for signs of lateral movement or persistence mechanisms that automated systems might miss. Typically, Tier 3 analysts manage up to three major investigations or proactive campaigns daily[12].
Detection engineering is a core responsibility at this level. Analysts create custom detection rules using tools like Sigma or YARA while conducting advanced forensics with platforms such as Volatility and Ghidra[1]. In cloud-native environments, you’ll monitor AWS CloudTrail logs, Kubernetes pod activity, and other cloud-specific signals[4].
Salaries for Tier 3 analysts range from $130,000 to $220,000+, with the 75th percentile reaching $198,000 in total compensation[12][1]. These roles, which are significantly more expensive for organizations than Tier 1 positions, reflect the advanced expertise required. Unlike lower-tier roles, Tier 3 analysts often work standard business hours instead of shifts[12].
Mid-Level and Advanced Certifications
To move into Tier 2 roles, certifications like the CompTIA CySA+ (around $400) focus on behavioral analytics and threat detection[1]. For analysts working with Microsoft Sentinel, the Microsoft SC-200 (approximately $165) is a cost-effective option[1][3]. Another valuable certification is the GCIH (GIAC Certified Incident Handler), priced at about $8,000, which is often employer-sponsored due to its comprehensive approach to incident response frameworks like NIST and SANS PICERL[12].
Tier 3 roles demand more specialized certifications. Options like the GCFA (GIAC Certified Forensic Analyst), GNFA (GIAC Certified Network Forensic Analyst), and GREM (GIAC Certified Reverse Engineering Malware), each costing roughly $8,000, are highly regarded[12]. The OSCP (Offensive Security Certified Professional), priced at around $1,600, is another strong choice for developing an adversary mindset and enhancing threat-hunting skills[12]. Additionally, expertise in specific SIEM tools such as Splunk (featured in 37% of SOC analyst job postings) or Microsoft Sentinel (26% of postings) can command a higher salary premium than being a generalist[1].
sbb-itb-bf7aa6b
SOC Leadership: Lead Analyst and Manager Positions
What SOC Leads and Managers Do
SOC leadership typically splits into two paths: technical leads and managers. Technical leads focus on day-to-day operations, such as managing alert queues, mentoring junior team members, and being the go-to person for high-severity incidents[14]. They stay heavily involved in hands-on investigations, often diving into process trees, logs, and other forensic details during active incidents.
On the other hand, managers concentrate on the bigger picture – strategy and administrative responsibilities. Their work includes hiring, managing budgets, negotiating with vendors, and briefing executives on the organization’s security posture[14]. While technical leads fine-tune the SOC’s response to threats, managers ensure the team has the workforce, tools, and funding needed to thrive.
| Feature | Technical Lead | SOC Manager |
|---|---|---|
| Primary Focus | Advanced analysis & threat hunting | Strategy, people, and budget |
| Daily Task | Tuning detection rules & hunting | Staffing, reporting, & vendor management |
| Primary Metric | Detection coverage & accuracy | MTTA, MTTR, & team retention |
| Stakeholders | Tier 1/2 analysts & engineers | CISO, Legal, HR, & Finance |
A challenge faced by SOC managers is the high burnout rate among analysts. According to Splunk’s 2025 Global State of Security report, 52% of SOC analysts have considered leaving their jobs due to the overwhelming volume of alerts and urgent incidents[14]. To combat this, managers must prioritize sustainable shift schedules and monitor team well-being.
These two leadership roles demand distinct skill sets, paving the way for certifications and expertise that define top-tier SOC leaders.
Leadership Skills and Required Certifications
To excel in SOC leadership, you need a strong grasp of the entire security stack. This includes expertise in SIEM platforms like Splunk or Sentinel, SOAR tools such as Cortex XSOAR, and EDR/XDR solutions like CrowdStrike[14]. As many SOCs now operate in multi-cloud environments, familiarity with AWS, Azure, or GCP is increasingly valuable[14].
But technical skills are only part of the equation. Communication is just as critical. SOC leaders must translate complex incidents into language that executives can understand, focusing on business risks rather than technical jargon[14]. During major breaches, they often act as coordinators, aligning responses across legal, HR, and PR teams – a task sometimes referred to as "escalation diplomacy."
Certifications play a key role in building credibility. The Certified Information Systems Security Professional (CISSP) remains a top credential, costing about $750 and appearing in 47% of security management job postings[1]. The Certified Information Security Manager (CISM), priced at around $600, is particularly valued in governance-heavy roles[1]. For SOC-specific leadership, the GIAC Security Operations Manager (GSOM) certification is another strong option[5].
"Holding CISSP doesn’t guarantee promotion – but not holding any cert often guarantees you’ll be overlooked."
- Safwan Azeem[5]
These certifications also meet DoD 8140/8570 requirements for management roles[15]. In the U.S., mid-level SOC managers with 5–8 years of experience typically earn between $120,000 and $165,000, with senior managers in major metro areas earning upwards of $210,000[14]. A TS/SCI clearance can boost these figures by an additional $20,000–$30,000[1].
Career Options Beyond SOC Operations
SOC leadership is more than just a job – it’s a launching pad for broader opportunities in cybersecurity. Many professionals leverage their experience to transition into specialized roles.
One common option is Incident Response Consulting, where experts help organizations navigate major breaches as external advisors[14]. Others move into Detection Engineering, a growing field focused on creating detection logic rather than reacting to alerts[1].
Another path is Security Architecture, where you can apply your understanding of threats to design stronger defensive systems[14]. For those aiming to climb even higher, SOC leadership can lead to positions like Director of Security Operations or even Chief Information Security Officer (CISO)[14].
At the senior level, success hinges on your ability to link technical work to business outcomes – whether you stay in the SOC or branch out into enterprise security roles.
Planning Your Cleared SOC Career Path
Using Job Listings to Identify Required Skills
Job postings can be a goldmine for understanding the skills needed to climb the SOC career ladder. For instance, SIEM tools appear in a whopping 82% of SOC job listings, while Python shows up in 24% of mid-level roles – hinting that scripting skills are a must for moving from Tier 1 to Tier 2[1]. When browsing job descriptions on Cleared Cyber Security Jobs, don’t just skim the basics. If a Tier 2 role mentions "automation" or "custom playbooks", it’s a signal to focus on automation skills. Similarly, mentions of AWS CloudTrail or Azure Activity Logs highlight the growing importance of cloud security expertise[4].
On top of technical skills, holding a security clearance can significantly boost your earning potential. A Secret clearance might add $10,000–$15,000 to your salary, while a TS/SCI clearance could mean an extra $20,000–$30,000. Combine these advantages with in-demand technical skills, and you’re setting yourself up for success[1].
Developing Skills and Choosing a Specialty
Breaking out of Tier 1 often means shifting from reactive tasks to proactive problem-solving. One of the quickest ways to advance is by automating repetitive tasks like shift reports, VirusTotal lookups, or indicator enrichment. Tools like Python and PowerShell can help you streamline these processes[1]. To showcase your skills, document your automation projects on GitHub – this portfolio can be a game-changer during interviews[8][18].
When it comes to specialization, most SOC career paths branch into three main areas:
- Detection Engineering: Focus on mastering query languages like KQL (for Microsoft Sentinel) or SPL (for Splunk). Learn how to deploy detection rules using APIs and adopt "Detection-as-Code" practices[17].
- Cloud Security: Dive into monitoring Kubernetes, serverless environments, and cloud audit logs to address the growing demand for cloud expertise[4].
- Threat Intelligence: Hone your skills in researching adversary tactics and integrating that knowledge into detection systems[3].
Certifications can also fast-track your progress. For example, CompTIA CySA+ (around $400) is a great investment for moving from Tier 1 to Tier 2[1]. If you’re working with Microsoft Sentinel, the Microsoft SC-200 certification (about $165) is a cost-effective way to deepen your expertise[1][3]. For those aspiring to leadership roles, the CISSP certification (approximately $750) is highly respected, though it requires five years of experience[1].
While building your technical skills is vital, maintaining balance and avoiding burnout is equally important for long-term growth.
Preventing Burnout in SOC Roles
SOC roles can be demanding, with 76% of security professionals reporting burnout in 2025[1]. Transitioning to Tier 2 can often provide relief from the high-pressure environment of Tier 1 work.
Start by looking into shift schedules during interviews. SOCs offering 4×10 schedules (four 10-hour days with three days off) or 3×12 shifts can be more manageable compared to traditional rotating 8-hour shifts[1]. Defense contractors often provide more predictable schedules compared to MSSPs, where burnout tends to be more common[1].
Automation isn’t just a career booster – it can also lighten your mental load by reducing repetitive, mundane tasks[3]. Set aside time for deep, uninterrupted work away from the constant barrage of alerts. Volunteering for tasks like incident retrospectives can also help you build leadership visibility while giving you a break from the alert queue. Seek out mentors who have successfully navigated their way to Tier 3 or management roles – they can offer invaluable guidance[5][16].
If you start feeling burned out, address it early. Open communication can help you manage the situation while maintaining your visibility and keeping your career progression on track[5].
Conclusion: Building a Successful Cleared SOC Career
Climbing the ladder from a Tier 1 SOC Analyst to a leadership role in the SOC world takes more than just time. It’s about consistently sharpening your skills, making smart certification decisions, and fully leveraging the advantages of your security clearance. The typical career path involves excelling at alert triage, moving into incident response, mastering threat hunting, and eventually stepping into leadership positions.
The jump between tiers often hinges on specific skills. For example, developing automation expertise can help you move to Tier 2, while honing threat hunting capabilities is crucial for Tier 3 [1]. Leadership, on the other hand, demands a shift in focus – from hands-on technical tasks to managing teams and overseeing strategic goals [5].
Your security clearance isn’t just a qualification – it’s a major asset that can significantly boost your career and salary. A Secret clearance can add $10,000–$15,000 to your annual pay, while a TS/SCI with polygraph might increase it by $30,000–$50,000 [1]. With the cybersecurity job market expected to grow by 32% to 35% through 2032 [4][19], cleared professionals are well-positioned to secure high-paying, stable roles, especially in government and defense sectors that remain steady even during economic uncertainty.
"Security leadership doesn’t wait for permission. It moves forward when you do." – Safwan Azeem [5]
To stand out, focus on hands-on experience, earn progressively advanced certifications (like Security+, CySA+, and CISSP), and build a strong portfolio [8]. And don’t underestimate the importance of a sustainable work environment – better schedules and reduced repetitive stress are key to thriving in the long run [1].
FAQs
Do I need an active clearance to get hired?
Yes, most SOC analyst positions that require security clearances, like Secret or Top Secret, typically demand an active clearance. This is often a crucial qualification for these roles.
Which certification should I get first for Tier 1?
The CompTIA Security+ certification is an excellent starting point for anyone aiming to become a Tier 1 SOC analyst. It covers the basics of cybersecurity and is widely acknowledged as a standard entry-level credential for many jobs in the industry.
How can I move from Tier 1 to Tier 2 faster?
To move from Tier 1 to Tier 2 more quickly, concentrate on developing essential skills such as understanding systems, automating repetitive tasks, and crafting detection rules that go beyond just handling alerts. Certifications like Security+ or CySA+ can help demonstrate your technical abilities. Alongside this, connect with mentors, build relationships within your organization, and stay informed about cloud-native threats and the latest security tools. These steps can help you stand out and speed up your career progression.
